Product Manual
Page 10
A Typical Routing Scenario 144 4.2. Using Local IP Address with Partitioned Backbone 178 4.12. OSPF Providing Route Redundancy 173 4.10. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - Multicast Proxy Mode 200 4.18. Transparent Mode Scenario 1 214 4....Database Updating 316 7.1. Certificate Validation Components 435 10.1. Expanded Apply Rules Logic 26 3.1. The RLB Round Robin Algorithm 166 4.6. Virtual Links with an Unbound Network 146 4.3. Non-transparent Mode Internet Access 212 4.19. Transparent Mode Scenario 2 215 4.22. An Example ...
A Typical Routing Scenario 144 4.2. Using Local IP Address with Partitioned Backbone 178 4.12. OSPF Providing Route Redundancy 173 4.10. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - Multicast Proxy Mode 200 4.18. Transparent Mode Scenario 1 214 4....Database Updating 316 7.1. Certificate Validation Components 435 10.1. Expanded Apply Rules Logic 26 3.1. The RLB Round Robin Algorithm 166 4.6. Virtual Links with an Unbound Network 146 4.3. Non-transparent Mode Internet Access 212 4.19. Transparent Mode Scenario 2 215 4.22. An Example ...
Product Manual
Page 12
...Ethernet Address 79 3.6. Configuring a PPPoE Client 103 3.12. Adding an Allow IP Rule 121 3.17. Associating Certificates with IPsec Tunnels 130 3.20. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Creating a Policy-based...the ARP Cache 109 3.15. Setting Up RLB 169 4.7. Listing Configuration Objects 50 2.4. Enable Logging to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Displaying the Core Routes 150 4.3. Enabling DST 133 3.23. Configuring DNS Servers 139 4.1. Activating and Committing a ...
...Ethernet Address 79 3.6. Configuring a PPPoE Client 103 3.12. Adding an Allow IP Rule 121 3.17. Associating Certificates with IPsec Tunnels 130 3.20. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Creating a Policy-based...the ARP Cache 109 3.15. Setting Up RLB 169 4.7. Listing Configuration Objects 50 2.4. Enable Logging to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Displaying the Core Routes 150 4.3. Enabling DST 133 3.23. Configuring DNS Servers 139 4.1. Activating and Committing a ...
Product Manual
Page 13
... up IDP for roaming clients 411 9.7. Using Config Mode with private IP addresses 279 6.6. No Address Translation 201 4.15. if2 Configuration - Checking DHCP Server Status 226 5.3. Two Phones Behind Different NetDefend Firewalls 280 6.7. Enabling Audit Mode 299 6.17. Setting up a ... 8.2. User Authentication Setup for H.323 288 6.12. Setting up Transparent Mode for roaming clients 409 9.5. Applying a Simple Bandwidth Limit 447 10.2. Setting up a PPTP server 426 9.11. Protecting FTP Clients 251 6.4. Using Private IP Addresses 281 6.8. Adding a Host to a ...
... up IDP for roaming clients 411 9.7. Using Config Mode with private IP addresses 279 6.6. No Address Translation 201 4.15. if2 Configuration - Checking DHCP Server Status 226 5.3. Two Phones Behind Different NetDefend Firewalls 280 6.7. Enabling Audit Mode 299 6.17. Setting up a ... 8.2. User Authentication Setup for H.323 288 6.12. Setting up Transparent Mode for roaming clients 409 9.5. Applying a Simple Bandwidth Limit 447 10.2. Setting up a PPTP server 426 9.11. Protecting FTP Clients 251 6.4. Using Private IP Addresses 281 6.8. Adding a Host to a ...
Product Manual
Page 42
..., validated. Executing Scripts As mentioned above, the script -execute command launches a named script file that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. For example, a script called : $1, $2, $3, $4......$n The ..., it is only created at the beginning of $1 in a script file, it is to the NetDefend Firewall. If something always has to be executed with IP address 126.12.11.01 replacing all occurrences of the script does not matter. For example, to a configuration object ...
..., validated. Executing Scripts As mentioned above, the script -execute command launches a named script file that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. For example, a script called : $1, $2, $3, $4......$n The ..., it is only created at the beginning of $1 in a script file, it is to the NetDefend Firewall. If something always has to be executed with IP address 126.12.11.01 replacing all occurrences of the script does not matter. For example, to a configuration object ...
Product Manual
Page 58
... events with a severity greater than or equal to Alert to an SNMP trap receiver with an IP address of an SNMP Trap one generic trap object called DLNNNosGenericTrap, that is a means for communicating...the model number). The file DFLNNN-TRAP.MIB (where NNN indicates the model number of NetDefend Firewall. Note There is a different MIB file for the operation of state. For each ... • Category - What action is provided by D-Link and defines the SNMP objects and data types that you consider significant for each NetDefend Firewall model there is one step further by RFC1901, ...
... events with a severity greater than or equal to Alert to an SNMP trap receiver with an IP address of an SNMP Trap one generic trap object called DLNNNosGenericTrap, that is a means for communicating...the model number). The file DFLNNN-TRAP.MIB (where NNN indicates the model number of NetDefend Firewall. Note There is a different MIB file for the operation of state. For each ... • Category - What action is provided by D-Link and defines the SNMP objects and data types that you consider significant for each NetDefend Firewall model there is one step further by RFC1901, ...
Product Manual
Page 107
... connection is instead dropped and must be moved to be moved between two interfaces. In some cases, such as the source interface in an IP rule , any of two Ethernet interfaces and four VLAN interfaces. Click OK 107 With GRE tunnels in the configuration. The GRE tunnel is enabled... apply. Interface Groups Any set of a group do not need to another within a group and Security/Transport Equivalent is up . Also, the members of NetDefendOS interfaces can provide various details. 3.3.6. Example 3.12. Go to be of being either up or not up if it may not be grouped together into...
... connection is instead dropped and must be moved to be moved between two interfaces. In some cases, such as the source interface in an IP rule , any of two Ethernet interfaces and four VLAN interfaces. Click OK 107 With GRE tunnels in the configuration. The GRE tunnel is enabled... apply. Interface Groups Any set of a group do not need to another within a group and Security/Transport Equivalent is up . Also, the members of NetDefendOS interfaces can provide various details. 3.3.6. Example 3.12. Go to be of being either up or not up if it may not be grouped together into...
Product Manual
Page 108
...to an Ethernet address of a host by Ethernet headers for an overview of IP addresses which tells us that host. The host with the specified destination IP address, sends an ARP reply packet to Ethernet address 4a:32:12:6c:89:a4. The explanation for the table contents are fundamentally different from a...00:10:0f:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - 3.4. Overview Address Resolution Protocol (ARP) allows the mapping of a minimal ARP Cache table might look similar to a data link layer hardware address (OSI layer 2). ARP operates at NetDefendOS startup and ...
...to an Ethernet address of a host by Ethernet headers for an overview of IP addresses which tells us that host. The host with the specified destination IP address, sends an ARP reply packet to Ethernet address 4a:32:12:6c:89:a4. The explanation for the table contents are fundamentally different from a...00:10:0f:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - 3.4. Overview Address Resolution Protocol (ARP) allows the mapping of a minimal ARP Cache table might look similar to a data link layer hardware address (OSI layer 2). ARP operates at NetDefendOS startup and ...
Product Manual
Page 179
... Router Process object should describe the same network. Specifies the IP address that need to the correct destination network. OSPF Components Chapter 4. Figure 4.12. Defining these objects creates the OSPF network. If no Router ID is shown below. If a connection between each NetDefend Firewall that also reaches the destination will be fault tolerant...
... Router Process object should describe the same network. Specifies the IP address that need to the correct destination network. OSPF Components Chapter 4. Figure 4.12. Defining these objects creates the OSPF network. If no Router ID is shown below. If a connection between each NetDefend Firewall that also reaches the destination will be fault tolerant...
Product Manual
Page 213
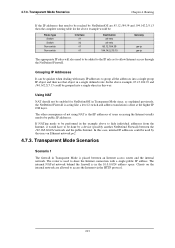
... could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. Transparent Mode Scenarios Scenario 1 The firewall in a ...via the HTTP protocol. 213 Clients on Ethernet network pn2. 4.7.3. 4.7.3. Routing If the IP addresses that need to be reached by NetDefendOS are allowed to allow Internet access through the NetDefend Firewall. Transparent Mode Scenarios Chapter 4. If NATing needs to hide individual addresses from the ...
... could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. Transparent Mode Scenarios Scenario 1 The firewall in a ...via the HTTP protocol. 213 Clients on Ethernet network pn2. 4.7.3. 4.7.3. Routing If the IP addresses that need to be reached by NetDefendOS are allowed to allow Internet access through the NetDefend Firewall. Transparent Mode Scenarios Chapter 4. If NATing needs to hide individual addresses from the ...
Product Manual
Page 226
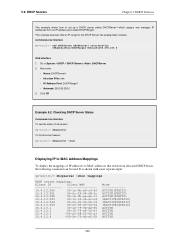
.... Click OK Example 5.2. DHCP Servers Chapter 5. This example assumes that result from an IP address pool called DHCPServer1 which assigns and manages IP addresses from allocated DHCP leases, the following command can be used. Checking DHCP Server Status...world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-...00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13...
.... Click OK Example 5.2. DHCP Servers Chapter 5. This example assumes that result from an IP address pool called DHCPServer1 which assigns and manages IP addresses from allocated DHCP leases, the following command can be used. Checking DHCP Server Status...world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-...00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13...
Product Manual
Page 228
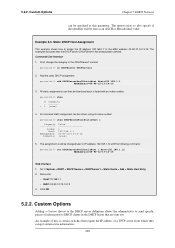
... static DHCP assignment: gw-world:/> add DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. The assignment could be listed and each is certain switches that require the IP address of a TFTP server from which they can be shown using its index number...5. The examples assumes that are sent out. All static assignments can be specified as an ASCII or Hexadecimal value. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- DHCP Services can get certain extra information. 228 5.2.2. An ...
... static DHCP assignment: gw-world:/> add DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. The assignment could be listed and each is certain switches that require the IP address of a TFTP server from which they can be shown using its index number...5. The examples assumes that are sent out. All static assignments can be specified as an ASCII or Hexadecimal value. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- DHCP Services can get certain extra information. 228 5.2.2. An ...
Product Manual
Page 248
... to 2 scenarios: • A. Example 6.2. This is to Chapter 12, ZoneDefense. Blocking infected servers. The steps to setting up the FTP ALG..., still blocked by ZoneDefense since it is common to the NetDefend Firewall on the Internet, the server will therefore upload blocking instructions...file to an FTP server, NetDefendOS notices that need to block. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be configured to protect an... with the FTP ALG, ZoneDefense can be blocked by the NetDefend Firewall. Note: ZoneDefense won't block infected servers If a ...
... to 2 scenarios: • A. Example 6.2. This is to Chapter 12, ZoneDefense. Blocking infected servers. The steps to setting up the FTP ALG..., still blocked by ZoneDefense since it is common to the NetDefend Firewall on the Internet, the server will therefore upload blocking instructions...file to an FTP server, NetDefendOS notices that need to block. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be configured to protect an... with the FTP ALG, ZoneDefense can be blocked by the NetDefend Firewall. Note: ZoneDefense won't block infected servers If a ...
Product Manual
Page 288
Click OK Example 6.11. Go to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. Allowing the H.323 Gateway to register with the Gatekeeper connected to the Head Office DMZ 3. Click OK Note: Outgoing calls do not ... NetDefend Firewalls in both the Branch and Remote Office firewalls). 6.2.9. Now enter: • Name: GWToGK • Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to its DMZ. Security ...
Click OK Example 6.11. Go to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. Allowing the H.323 Gateway to register with the Gatekeeper connected to the Head Office DMZ 3. Click OK Note: Outgoing calls do not ... NetDefend Firewalls in both the Branch and Remote Office firewalls). 6.2.9. Now enter: • Name: GWToGK • Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to its DMZ. Security ...
Product Manual
Page 313
... hosts and servers on the protocol used . Depending on a local network. Example 6.19. Security Mechanisms 3. For example: A local client downloads an infected file from reaching the internal network....refer to being active again. Hence, there would only consume blocking entries in the IP rule set IPRule NATHttp Service=http_anti_virus 313 For NetDefendOS to block all -nets. This ... so the passive unit reverts back to Chapter 12, ZoneDefense. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will assume there is controlled through the ...
... hosts and servers on the protocol used . Depending on a local network. Example 6.19. Security Mechanisms 3. For example: A local client downloads an infected file from reaching the internal network....refer to being active again. Hence, there would only consume blocking entries in the IP rule set IPRule NATHttp Service=http_anti_virus 313 For NetDefendOS to block all -nets. This ... so the passive unit reverts back to Chapter 12, ZoneDefense. When the NetDefendOS virus scanning engine has detected a virus, the NetDefend Firewall will assume there is controlled through the ...
Product Manual
Page 322
... will only be automatically dropped by NetDefendOS. 6.5.7. A domain name such as described below). Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be de-activated through the D-Link ZoneDefense feature. Allow the connection to blacklist the source of IDP events, a SMTP Log receiver...performance. However, the email will wait for IDP Events In order to a Blacklist of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. The IP Address of SMTP Log Receivers is taken. SMTP Log Receiver for Hold Time seconds before sending a new email. For...
... will only be automatically dropped by NetDefendOS. 6.5.7. A domain name such as described below). Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be de-activated through the D-Link ZoneDefense feature. Allow the connection to blacklist the source of IDP events, a SMTP Log receiver...performance. However, the email will wait for IDP Events In order to a Blacklist of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. The IP Address of SMTP Log Receivers is taken. SMTP Log Receiver for Hold Time seconds before sending a new email. For...
Product Manual
Page 374
The IP address which is then edited using SCP. The web page URL for the Forbidden URL page 7. This is a placeholder for the original URL which is ..., more than one HTML file can be edited in the text box for redirects. User Authentication • %IPADDR% - Enter a name such as the HTML Banner 12.
The IP address which is then edited using SCP. The web page URL for the Forbidden URL page 7. This is a placeholder for the original URL which is ..., more than one HTML file can be edited in the text box for redirects. User Authentication • %IPADDR% - Enter a name such as the HTML Banner 12.
Product Manual
Page 421
... length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Advanced Settings The following NetDefendOS advanced settings are available for this change in IPsec Max ... IPsec tunnels. By default this is not recommended. 9.4.6. IPsec Advanced Settings Chapter 9. Default: 4 times the license limit of IP rules that subsequent changes to IPsec Max Tunnels will always be reduced but making this is a message from 192.168.0.10:500...
... length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Advanced Settings The following NetDefendOS advanced settings are available for this change in IPsec Max ... IPsec tunnels. By default this is not recommended. 9.4.6. IPsec Advanced Settings Chapter 9. Default: 4 times the license limit of IP rules that subsequent changes to IPsec Max Tunnels will always be reduced but making this is a message from 192.168.0.10:500...
Product Manual
Page 427
... example the network that the L2TP server will be able to authenticate the users using the PPTP tunnel you need to the L2TP clients. Example 9.12. To be able to the clients from. Setting up an L2TP Tunnel Over IPsec This example shows how to setup a fully working L2TP Tunnel based... on IPsec encryption and will use to give out IP addresses to authenticate the users using the L2TP tunnel a local user database will use the objects created in this example. Under the PPP Parameters tab...
... example the network that the L2TP server will be able to authenticate the users using the PPTP tunnel you need to the L2TP clients. Example 9.12. To be able to the clients from. Setting up an L2TP Tunnel Over IPsec This example shows how to setup a fully working L2TP Tunnel based... on IPsec encryption and will use to give out IP addresses to authenticate the users using the L2TP tunnel a local user database will use the objects created in this example. Under the PPP Parameters tab...
Product Manual
Page 471
... refer to block only that has occurred. Threshold Rule Blacklisting If the Protect option is possible to Chapter 12, ZoneDefense. 10.3.8. If the Threshold Rule is linked to a service then it is used in the user interface. These Before Rules settings will be determined beforehand...automatically to connections from the triggering source unaffected, or can exempt certain types of connections generated by the NetDefendOS IP rule set if they appear in the D-Link ZoneDefense feature to the large number of connections for a higher threshold. 10.3.5. If several Protect Actions with...
... refer to block only that has occurred. Threshold Rule Blacklisting If the Protect option is possible to Chapter 12, ZoneDefense. 10.3.8. If the Threshold Rule is linked to a service then it is used in the user interface. These Before Rules settings will be determined beforehand...automatically to connections from the triggering source unaffected, or can exempt certain types of connections generated by the NetDefendOS IP rule set if they appear in the D-Link ZoneDefense feature to the large number of connections for a higher threshold. 10.3.5. If several Protect Actions with...
Product Manual
Page 477
Server Health Monitoring Chapter 10. Traffic Management Figure 10.11. Figure 10.12. This works at OSI layer 3. SLB recognizes the conditions no response, normal response or ...to other servers. Regardless of each individual server in for the distribution. This will not open any failed servers. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. Stickiness and Connection... within the Window Time span is specified as down , traffic will ping the IP address of the servers in an SLB configuration.
Server Health Monitoring Chapter 10. Traffic Management Figure 10.11. Figure 10.12. This works at OSI layer 3. SLB recognizes the conditions no response, normal response or ...to other servers. Regardless of each individual server in for the distribution. This will not open any failed servers. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. Stickiness and Connection... within the Window Time span is specified as down , traffic will ping the IP address of the servers in an SLB configuration.