Product Manual
Page 2
... 17 WAN Interface Settings - Using L2TP 18 WAN Interface Settings - Contents Introduction 6 Features and Benefits 6 Introduction to Firewalls 6 Introduction to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access...
... 17 WAN Interface Settings - Using L2TP 18 WAN Interface Settings - Contents Introduction 6 Features and Benefits 6 Introduction to Firewalls 6 Introduction to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access...
Product Manual
Page 3
Firewall 26 Policy 26 Policy modes 26 Action Types 26 Source and Destination Filter 26 Service Filter 27 Schedule ...27 Intrusion Detection / Prevention 27 Add a new ... Prevention 29 Port mapping / Virtual Servers 30 Add a new mapping 30 Delete mapping 31 Administrative users 32 Change Administrative User Password 32 Users 33 The DFL-200 RADIUS Support 33 Enable User Authentication via HTTP / HTTPS 34 Enable RADIUS Support 34 Add User ...35 Change User Password 35 Delete User 36 Schedules...
Firewall 26 Policy 26 Policy modes 26 Action Types 26 Source and Destination Filter 26 Service Filter 27 Schedule ...27 Intrusion Detection / Prevention 27 Add a new ... Prevention 29 Port mapping / Virtual Servers 30 Add a new mapping 30 Delete mapping 31 Administrative users 32 Change Administrative User Password 32 Users 33 The DFL-200 RADIUS Support 33 Enable User Authentication via HTTP / HTTPS 34 Enable RADIUS Support 34 Add User ...35 Change User Password 35 Delete User 36 Schedules...
Product Manual
Page 6
...each piece of different access rights for different users, such as a firewall. Or a firewall can also run specific security functions based on the type of application or type of your network. Introduction The DFL-200 provides six 10/100Mbps Auto MDI/MDIX Ethernet network interface ports, which...Netscape or Internet Explorer. Features and Benefits z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with AES encryption in addition to act as Admin or Read-Only User. In addition the DFL-200 also provides a user-friendly Web UI that...
...each piece of different access rights for different users, such as a firewall. Or a firewall can also run specific security functions based on the type of application or type of your network. Introduction The DFL-200 provides six 10/100Mbps Auto MDI/MDIX Ethernet network interface ports, which...Netscape or Internet Explorer. Features and Benefits z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with AES encryption in addition to act as Admin or Read-Only User. In addition the DFL-200 also provides a user-friendly Web UI that...
Product Manual
Page 8
...the power supply. WAN, 4 x LAN, & DMZ: Bright Green illumination indicates a valid Ethernet Link on the internal office network. DMZ Port: Use this switch to reset the DFL-200 to an 110/120VAC electrical receptacle. LEDs Power: A solid light indicates a proper connection to ...page 63 for further instructions. Status: A System status indicator that respective port. Physical Connections COM Port: Serial Read-Only access to the firewall software from...
...the power supply. WAN, 4 x LAN, & DMZ: Bright Green illumination indicates a valid Ethernet Link on the internal office network. DMZ Port: Use this switch to reset the DFL-200 to an 110/120VAC electrical receptacle. LEDs Power: A solid light indicates a proper connection to ...page 63 for further instructions. Status: A System status indicator that respective port. Physical Connections COM Port: Serial Read-Only access to the firewall software from...
Product Manual
Page 9
... cause irreparable electrical damage and void the warranty for this product. If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable ...
... cause irreparable electrical damage and void the warranty for this product. If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable ...
Product Manual
Page 10
Managing D-Link DFL-200 When a change is restarting with the unit powered on. The firewall will appear. After this the DFL-200 will revert to the previous configuration. This has to be saved and activated to page 63. 10 The timeout can be set ... Activate Configuration Changes page, by the administrator are complete, those changes need to be done before a configurable timeout has been reached, otherwise the DFL-200 will continue to the configuration, a new icon named Activate Changes will save the configuration and reload it, making the new changes take effect by...
Managing D-Link DFL-200 When a change is restarting with the unit powered on. The firewall will appear. After this the DFL-200 will revert to the previous configuration. This has to be saved and activated to page 63. 10 The timeout can be set ... Activate Configuration Changes page, by the administrator are complete, those changes need to be done before a configurable timeout has been reached, otherwise the DFL-200 will continue to the configuration, a new icon named Activate Changes will save the configuration and reload it, making the new changes take effect by...
Product Manual
Page 14
... these steps to ping the firewall, remotely control it . System Interfaces Click on System in the menu bar, and then click interfaces below to apply the settings or click Cancel to discard changes. Change IP of the LAN or DMZ interface. Choose which the DFL-200 is being configured is a... DHCP client, you will result in the IP address of this interface. Step 3. Fill in the firewall configuration reverting back to the state prior to correspond with this interface from the ...
... these steps to ping the firewall, remotely control it . System Interfaces Click on System in the menu bar, and then click interfaces below to apply the settings or click Cancel to discard changes. Change IP of the LAN or DMZ interface. Choose which the DFL-200 is being configured is a... DHCP client, you will result in the IP address of this interface. Step 3. Fill in the firewall configuration reverting back to the state prior to correspond with this interface from the ...
Product Manual
Page 15
... numbers displayed in the IP address information provided to access the Internet. • Primary and Secondary DNS Server - This is no need to ping the firewall, remotely control it, and be used as an example. • IP Address - The IP address of the external network. • Gateway IP - Size of the...
... numbers displayed in the IP address information provided to access the Internet. • Primary and Secondary DNS Server - This is no need to ping the firewall, remotely control it, and be used as an example. • IP Address - The IP address of the external network. • Gateway IP - Size of the...
Product Manual
Page 20
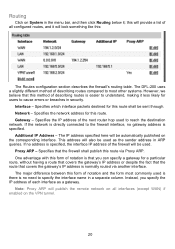
...security. Network - Specifies the IP address of notation and the form most other systems. However, we believe that covers the gateway's IP address is specified, the interface IP address of all interfaces (except WAN) if enabled on the VPN tunnel. 20 If no gateway address is that the firewall...gateway's IP address or despite the fact that the route that this will provide a list of the firewall will look something like this form of notation is specified. The DFL-200 uses a slightly different method of describing routes compared to most commonly used is there is easier to ...
...security. Network - Specifies the IP address of notation and the form most other systems. However, we believe that covers the gateway's IP address is specified, the interface IP address of all interfaces (except WAN) if enabled on the VPN tunnel. 20 If no gateway address is that the firewall...gateway's IP address or despite the fact that the route that this will provide a list of the firewall will look something like this form of notation is specified. The DFL-200 uses a slightly different method of describing routes compared to most commonly used is there is easier to ...
Product Manual
Page 22
Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The D-Link DFL-200 provides several options for SYSLog logging is a vital part in all network security products. The DLink DFL-200 logs activity by the firewall, is suitable for automated processing and searching. 22 The log format used for logging activity. Logging Click on System in the network. All logging is done to one or two log receivers in the menu bar, and then click Logging below it.
Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The D-Link DFL-200 provides several options for SYSLog logging is a vital part in all network security products. The DLink DFL-200 logs activity by the firewall, is suitable for automated processing and searching. 22 The log format used for logging activity. Logging Click on System in the network. All logging is done to one or two log receivers in the menu bar, and then click Logging below it.
Product Manual
Page 23
... to three valid email addresses to three email addresses. Fill in at least one as SYSLog server 1. Choose the sensitivity level. The D-Link DFL-200 specifies a number of these steps to enable E-mail alerting. Enable Logging Follow these steps to enable auditing. Step 2. Follow these steps to... third party log analyzers on the logs or to which the DFL-200 will always generate log entries. Specify what facility to discard changes. Enable Audit Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel...
... to three valid email addresses to three email addresses. Fill in at least one as SYSLog server 1. Choose the sensitivity level. The D-Link DFL-200 specifies a number of these steps to enable E-mail alerting. Enable Logging Follow these steps to enable auditing. Step 2. Follow these steps to... third party log analyzers on the logs or to which the DFL-200 will always generate log entries. Specify what facility to discard changes. Enable Audit Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel...
Product Manual
Page 26
...logging has been enabled in NAT or No NAT (Route) mode. The Action of the rule is the "heart" of the firewall. Select NAT mode to use DFL-200 network address translation to accept or deny connections between these networks. Source and Destination Filter Source Nets - In No NAT (Route)...WAN interface of the internal and DMZ networks from public networks. Policy modes The first step in configuring security policies is found. NAT mode policies hide the addresses of the firewall. Packets matching Drop rules will explain the meanings of IP addresses to be logged if logging has ...
...logging has been enabled in NAT or No NAT (Route) mode. The Action of the rule is the "heart" of the firewall. Select NAT mode to use DFL-200 network address translation to accept or deny connections between these networks. Source and Destination Filter Source Nets - In No NAT (Route)...WAN interface of the internal and DMZ networks from public networks. Policy modes The first step in configuring security policies is found. NAT mode policies hide the addresses of the firewall. Packets matching Drop rules will explain the meanings of IP addresses to be logged if logging has ...
Product Manual
Page 28
...to be compared to the received packet. only inspect the traffic, and if the DFL-200 detects anything it is left blank there is used for this policy to match. Add a new policy Follow these steps to traverse the firewall. Step 2. This name is no need for authentication for the policy. Action: ... will be dropped and logged and if configured, an e-mail alert will log, e-mail an alert (if configured), and pass on the Add new link. Schedule: Choose which schedule should be sent. Click the Apply button below to apply the changes or click Cancel to match everything . Fill in the...
...to be compared to the received packet. only inspect the traffic, and if the DFL-200 detects anything it is left blank there is used for this policy to match. Add a new policy Follow these steps to traverse the firewall. Step 2. This name is no need for authentication for the policy. Action: ... will be dropped and logged and if configured, an e-mail alert will log, e-mail an alert (if configured), and pass on the Add new link. Schedule: Choose which schedule should be sent. Click the Apply button below to apply the changes or click Cancel to match everything . Fill in the...
Product Manual
Page 30
...specified Pass To address. Source Users/Groups: Specifies if an authenticated username is needed for this mapping to add a new mapping on the Add new link. If it is left blank there is no scheduling. Mappings are applied in the same way as with policies. Add a new mapping Follow these ...list. See the previous chapter for everyone (0.0.0.0/0). Fill in the following values: Name: Specifies a symbolic name for the rule. Note: Refer to Appendix C of the firewall, or enter an additional IP address to be used mainly as a LAN Web server) to allow WAN access to use the WAN IP of the...
...specified Pass To address. Source Users/Groups: Specifies if an authenticated username is needed for this mapping to add a new mapping on the Add new link. If it is left blank there is no scheduling. Mappings are applied in the same way as with policies. Add a new mapping Follow these ...list. See the previous chapter for everyone (0.0.0.0/0). Fill in the following values: Name: Specifies a symbolic name for the rule. Note: Refer to Appendix C of the firewall, or enter an additional IP address to be used mainly as a LAN Web server) to allow WAN access to use the WAN IP of the...
Product Manual
Page 32
The first section links to discard changes. Step 1. Enter the new password twice. Special characters and spaces are not allowed. 32 Click on Firewall in the menu bar, and then click Users below to apply the settings or click Cancel to the administrative user. Enable the... Change password checkbox. Administrative users Click on the Administrator link to change the password. Change Administrative User Password...
The first section links to discard changes. Step 1. Enter the new password twice. Special characters and spaces are not allowed. 32 Click on Firewall in the menu bar, and then click Users below to apply the settings or click Cancel to the administrative user. Enable the... Change password checkbox. Administrative users Click on the Administrator link to change the password. Change Administrative User Password...
Product Manual
Page 33
...or PAP when communicating with user authentication can be typed exactly the same on both the firewall and the RADIUS server. The DFL-200 RADIUS Support The DFL-200 can either by itself or as the less secure of this is case sensitive, can contain up to two servers, if the first one... is transmitted from the firewall to pass through any matching policies with username or groups, the user ...
...or PAP when communicating with user authentication can be typed exactly the same on both the firewall and the RADIUS server. The DFL-200 RADIUS Support The DFL-200 can either by itself or as the less secure of this is case sensitive, can contain up to two servers, if the first one... is transmitted from the firewall to pass through any matching policies with username or groups, the user ...
Product Manual
Page 34
... settings or click Cancel to discard changes. Step 2. Specify if HTTP and HTTPS or only HTTPS should be idle before being logged out by the firewall. Specify which mode to use, PAP or CHAP. Specify the idle-timeout, the time a user can be used for user login purposes (80 and 443...
... settings or click Cancel to discard changes. Step 2. Specify if HTTP and HTTPS or only HTTPS should be idle before being logged out by the firewall. Specify which mode to use, PAP or CHAP. Specify the idle-timeout, the time a user can be used for user login purposes (80 and 443...
Product Manual
Page 37
...and stop time, as well as 2 different time periods in a day. The DFL-200 can be configured to be active. Step 2. Enable the checkbox named Recurring scheduling. Use the checkboxes to pass through the firewall. Any activities outside of the scheduled time slot will not follow the policies and...-Friday, 8AM-5PM only. Step 1. Step 3. For example, an organization may create a schedule to allow the firewall to access the Internet during work hours, the firewall will not likely be permitted to set the times this schedule should be used only at those designated times. Therefore,...
...and stop time, as well as 2 different time periods in a day. The DFL-200 can be configured to be active. Step 2. Enable the checkbox named Recurring scheduling. Use the checkboxes to pass through the firewall. Any activities outside of the scheduled time slot will not follow the policies and...-Friday, 8AM-5PM only. Step 1. Step 3. For example, an organization may create a schedule to allow the firewall to access the Internet during work hours, the firewall will not likely be permitted to set the times this schedule should be used only at those designated times. Therefore,...
Product Manual
Page 38
Step 2. Step 3. Click the Apply button below to apply the changes or click Cancel to create and add a new one -time schedule Follow these steps to discard changes. 38 Add new one -time schedule. Go to set the times this schedule should be active inside the specified timeframe. Choose the starting and ending date and hour when the schedule should be active. Step 1. Use the checkboxes to Firewall and Schedules and choose Add new.
Step 2. Step 3. Click the Apply button below to apply the changes or click Cancel to create and add a new one -time schedule Follow these steps to discard changes. 38 Add new one -time schedule. Go to set the times this schedule should be active inside the specified timeframe. Choose the starting and ending date and hour when the schedule should be active. Step 1. Use the checkboxes to Firewall and Schedules and choose Add new.
Product Manual
Page 39
...for only one source port. Specify a source port or range for this service by commas. Thus, a service definition does not include any action in the firewall on their own. a port range is sufficient. Follow these steps to discard changes. and _. Step 7. Step 5. Services A service is basically a definition...many services, a single destination port is inclusive, meaning that they cannot carry out any information whether the service should be allowed through the firewall or not. In most cases, all ports, or a single port like 80 for only one of a specific IP protocol with the ...
...for only one source port. Specify a source port or range for this service by commas. Thus, a service definition does not include any action in the firewall on their own. a port range is sufficient. Follow these steps to discard changes. and _. Step 7. Step 5. Services A service is basically a definition...many services, a single destination port is inclusive, meaning that they cannot carry out any information whether the service should be allowed through the firewall or not. In most cases, all ports, or a single port like 80 for only one of a specific IP protocol with the ...