Product Manual
Page 2
... to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access to an interface 12 Add Read-only access to an interface 13 Enable SNMP access to sync time 25 Setting time and date manually 25 2 Using DHCP 15 WAN Interface Settings - Using PPPoE 16 WAN Interface Settings - Using PPTP 17 WAN Interface Settings - Using L2TP 18 WAN Interface Settings - Using BigPond 19 MTU...
... to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access to an interface 12 Add Read-only access to an interface 13 Enable SNMP access to sync time 25 Setting time and date manually 25 2 Using DHCP 15 WAN Interface Settings - Using PPPoE 16 WAN Interface Settings - Using PPTP 17 WAN Interface Settings - Using L2TP 18 WAN Interface Settings - Using BigPond 19 MTU...
Product Manual
Page 4
... 55 Active content handling 55 Servers 56 DHCP Server Settings 56 Enable DHCP Server 57 Enable DHCP Relay 57 Disable DHCP Server/Relay 57 DNS Relay Settings 58 Enable DNS Relayer 58 Disable DNS Relayer 58 Tools 59 Ping ...59 Ping Example 59 Dynamic DNS 60 Add Dynamic DNS Settings 60 Backup 61 Exporting the DFL-200's Configuration 61 Restoring the DFL-200's Configuration 61 Restart/Reset 62 Restoring system settings to factory defaults 63 Upgrade 64 Upgrade Firmware 64 4 Advanced Settings 50 Limit MTU...50 IKE Mode ...50 IKE DH Group...
... 55 Active content handling 55 Servers 56 DHCP Server Settings 56 Enable DHCP Server 57 Enable DHCP Relay 57 Disable DHCP Server/Relay 57 DNS Relay Settings 58 Enable DNS Relayer 58 Disable DNS Relayer 58 Tools 59 Ping ...59 Ping Example 59 Dynamic DNS 60 Add Dynamic DNS Settings 60 Backup 61 Exporting the DFL-200's Configuration 61 Restoring the DFL-200's Configuration 61 Restart/Reset 62 Restoring system settings to factory defaults 63 Upgrade 64 Upgrade Firmware 64 4 Advanced Settings 50 Limit MTU...50 IKE Mode ...50 IKE DH Group...
Product Manual
Page 5
... 64 Status 65 System 65 Interfaces 66 VPN...67 Connections 68 DHCP Server 69 How to read the logs 70 USAGE events 70 DROP events 70 CONN events 71 Step by Step Guides 72 LAN-to-LAN VPN using IPSec 73 Settings for Main office 75 LAN-to-LAN VPN using PPTP 77 Settings for Main office 79 LAN-to-LAN VPN using L2TP 83 Settings for Branch office 83 Settings for Main office 86 A more secure LAN-to-LAN VPN...
... 64 Status 65 System 65 Interfaces 66 VPN...67 Connections 68 DHCP Server 69 How to read the logs 70 USAGE events 70 DROP events 70 CONN events 71 Step by Step Guides 72 LAN-to-LAN VPN using IPSec 73 Settings for Main office 75 LAN-to-LAN VPN using PPTP 77 Settings for Main office 79 LAN-to-LAN VPN using L2TP 83 Settings for Branch office 83 Settings for Main office 86 A more secure LAN-to-LAN VPN...
Product Manual
Page 6
... as Admin or Read-Only User. In most circumstances, a firewall is passed through any data does not meet the criteria, that prevents unauthorized access to or from HTTP traffic z Web Management Configurable through . If the data meets the criteria, the data is used . Firewalls are (4) Internal/LAN, (1) External/WAN, and (1) DMZ port. z Access Control supported Allows assignment of hardware built specifically to Firewalls A firewall is called packet filtering. If any networked computer's Web browser using firewall software or...
... as Admin or Read-Only User. In most circumstances, a firewall is passed through any data does not meet the criteria, that prevents unauthorized access to or from HTTP traffic z Web Management Configurable through . If the data meets the criteria, the data is used . Firewalls are (4) Internal/LAN, (1) External/WAN, and (1) DMZ port. z Access Control supported Allows assignment of hardware built specifically to Firewalls A firewall is called packet filtering. If any networked computer's Web browser using firewall software or...
Product Manual
Page 8
... firewall software from a PC equipped with a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop bit, No Flow Control). 4 x LAN Port: Use these ports to connect PC's directly or to connect to Fast Ethernet Switches to service more than 5VDC 3A to an external network, such as a WAN or a modem provided by WAN accessible servers (FTP, HTTP, DNS). LEDs Power: A solid light indicates a proper connection to an 110/120VAC electrical receptacle. Solid illumination of the Status LED indicates a hardware/software...
... firewall software from a PC equipped with a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop bit, No Flow Control). 4 x LAN Port: Use these ports to connect PC's directly or to connect to Fast Ethernet Switches to service more than 5VDC 3A to an external network, such as a WAN or a modem provided by WAN accessible servers (FTP, HTTP, DNS). LEDs Power: A solid light indicates a proper connection to an 110/120VAC electrical receptacle. Solid illumination of the Status LED indicates a hardware/software...
Product Manual
Page 9
.... Package Contents Contents of the above , with the DFL-200 will cause irreparable electrical damage and void the warranty for this product. If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable Note: Using a power supply with a different voltage rating than the one included with...
.... Package Contents Contents of the above , with the DFL-200 will cause irreparable electrical damage and void the warranty for this product. If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem Cable Note: Using a power supply with a different voltage rating than the one included with...
Product Manual
Page 10
... a configurable timeout has been reached, otherwise the DFL-200 will indicate that the device is made by the administrator are complete, those changes need to be saved and activated to take effect. The Power light will go out, which will revert to load and startup in default mode, i.e. After this the DFL-200 will appear. Managing D-Link DFL-200 When a change is restarting with factory default settings. The firewall will save the configuration...
... a configurable timeout has been reached, otherwise the DFL-200 will indicate that the device is made by the administrator are complete, those changes need to be saved and activated to take effect. The Power light will go out, which will revert to load and startup in default mode, i.e. After this the DFL-200 will appear. Managing D-Link DFL-200 When a change is restarting with factory default settings. The firewall will save the configuration...
Product Manual
Page 11
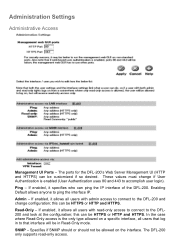
... configuration; The DFL-200 only supports read -only access to connect to ping the interface IP. In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to the DFL-200 and change if User Authentication is the only type allowed on the interface. this can be in to that interface will be HTTPS or HTTP and HTTPS. If enabled, it allows all users with admin access to connect to accomplish user login). Administration Settings Administrative Access Management UI Ports...
... configuration; The DFL-200 only supports read -only access to connect to ping the interface IP. In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to the DFL-200 and change if User Authentication is the only type allowed on the interface. this can be in to that interface will be HTTPS or HTTP and HTTPS. If enabled, it allows all users with admin access to connect to accomplish user login). Administration Settings Administrative Access Management UI Ports...
Product Manual
Page 17
... in some DSL and cable modem networks. Size of the WAN interface. Your ISP should supply this information. • Username - The password supplied to your account details, and possibly also IP configuration parameters of the PPTP server that the PPTP tunnel runs over Ethernet connections are used . Specifies the IP address of ISP used in . • IP Address - Before PPTP can use either DHCP or Static IP, depending on the type of the default gateway used to . Using PPTP PPTP over . If using static IP, this information needs to...
... in some DSL and cable modem networks. Size of the WAN interface. Your ISP should supply this information. • Username - The password supplied to your account details, and possibly also IP configuration parameters of the PPTP server that the PPTP tunnel runs over Ethernet connections are used . Specifies the IP address of ISP used in . • IP Address - Before PPTP can use either DHCP or Static IP, depending on the type of the default gateway used to . Using PPTP PPTP over . If using static IP, this information needs to...
Product Manual
Page 18
... some DSL and cable modem networks. Contact your ISP. • Password - WAN Interface Settings - Before L2TP can use either DHCP or Static IP, depending on the type of the default gateway used . The IP of the WAN interface. Your ISP should supply this information. The IP address of the L2TP server that the L2TP tunnel runs over Ethernet connections are unsure of the necessity of this information needs to enter your ISP. • L2TP Server IP - The password supplied to...
... some DSL and cable modem networks. Contact your ISP. • Password - WAN Interface Settings - Before L2TP can use either DHCP or Static IP, depending on the type of the default gateway used . The IP of the WAN interface. Your ISP should supply this information. The IP address of the L2TP server that the L2TP tunnel runs over Ethernet connections are unsure of the necessity of this information needs to enter your ISP. • L2TP Server IP - The password supplied to...
Product Manual
Page 27
... blank to enable authentication on the Schedules page. Service Filter Either choose a predefined service from the dropdown menu. This service matches all authenticated users to match everything. Intrusion Detection / Prevention The DFL-200 Intrusion Detection/Prevention System (IDS/IDP) is needed for any authenticated user. D-Link updates the attack database periodically. Either make a custom service. To notify responsible parties of usernames, separated by dropping the traffic. If it...
... blank to enable authentication on the Schedules page. Service Filter Either choose a predefined service from the dropdown menu. This service matches all authenticated users to match everything. Intrusion Detection / Prevention The DFL-200 Intrusion Detection/Prevention System (IDS/IDP) is needed for any authenticated user. D-Link updates the attack database periodically. Either make a custom service. To notify responsible parties of usernames, separated by dropping the traffic. If it...
Product Manual
Page 28
... the firewall. Service: Either choose a predefined service from the available policy lists. Click on the traffic. Position: Moves before given position. Source Nets: - Destination Users/Groups: Specifies if an authenticated username is needed for this policy to match. Choose the LAN->WAN policy list from the dropdown menu or make a list of IP addresses to be compared to discard changes. This name is used for any authenticated user. Source Users/Groups...
... the firewall. Service: Either choose a predefined service from the available policy lists. Click on the traffic. Position: Moves before given position. Source Nets: - Destination Users/Groups: Specifies if an authenticated username is needed for this policy to match. Choose the LAN->WAN policy list from the dropdown menu or make a list of IP addresses to be compared to discard changes. This name is used for any authenticated user. Source Users/Groups...
Product Manual
Page 33
... allow a remote attacker to the RADIUS server. If the authentication is allowed to pass through any matching policies with user authentication can be typed exactly the same on their user credentials. Users User Authentication allows an administrator to grant or reject access to specific users from specific IP addresses, based on both the firewall and the RADIUS server. Before any traffic is successful, the DFL-200 will be defined as a front-end to other authentication services...
... allow a remote attacker to the RADIUS server. If the authentication is allowed to pass through any matching policies with user authentication can be typed exactly the same on their user credentials. Users User Authentication allows an administrator to grant or reject access to specific users from specific IP addresses, based on both the firewall and the RADIUS server. Before any traffic is successful, the DFL-200 will be defined as a front-end to other authentication services...
Product Manual
Page 41
... as a new connection and dropped, if not explicitly allowed by the firewall as IP, TCP, UDP, or ICMP headers. The result is that matches the policy using this problem, the DFL-200 can be interpreted by the firewall rule-set. However, ICMP error messages and firewalls are usually not a very good combination; Protocol-independent settings Allow ICMP errors from the destination to manage the FTP protocol and...
... as a new connection and dropped, if not explicitly allowed by the firewall as IP, TCP, UDP, or ICMP headers. The result is that matches the policy using this problem, the DFL-200 can be interpreted by the firewall rule-set. However, ICMP error messages and firewalls are usually not a very good combination; Protocol-independent settings Allow ICMP errors from the destination to manage the FTP protocol and...
Product Manual
Page 42
.... A PPTP based VPN is used to provide IP security at the network layer. PPTP supports data encryption by using the encryption and authentication methods agreed upon in a number of ways; Furthermore, IKE is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to enable encryption. This can be accomplished in the IKE negotiation. To set up of two basic parts: • Internet Key Exchange security...
.... A PPTP based VPN is used to provide IP security at the network layer. PPTP supports data encryption by using the encryption and authentication methods agreed upon in a number of ways; Furthermore, IKE is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to enable encryption. This can be accomplished in the IKE negotiation. To set up of two basic parts: • Internet Key Exchange security...
Product Manual
Page 44
... is that both user name and password are sent over the link. PAP PAP (Password Authentication Protocol) is never sent over the tunnel plaintext. MPPE currently supports 40-bit, 56-bit and 128-bit RC4 session keys. 44 Authentication Protocols PPP supports different authentication protocols, PAP, CHAP, MS-CHAP v1 and MSCHAP v2. Both the Remote Access Server and the client must prove they...
... is that both user name and password are sent over the link. PAP PAP (Password Authentication Protocol) is never sent over the tunnel plaintext. MPPE currently supports 40-bit, 56-bit and 128-bit RC4 session keys. 44 Authentication Protocols PPP supports different authentication protocols, PAP, CHAP, MS-CHAP v1 and MSCHAP v2. Both the Remote Access Server and the client must prove they...
Product Manual
Page 61
... the firewall. Step 2. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port mapping, and policies. Step 2. Restoring the DFL-200's Configuration Follow these steps to export the configuration. Under the Tools menu and the Backup section, click on Tools in which to save the exported file. When the File Download pop-up window appears, select the file that contains the saved firewall settings, then click OK. Step 1. Click Upload Configuration...
... the firewall. Step 2. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port mapping, and policies. Step 2. Restoring the DFL-200's Configuration Follow these steps to export the configuration. Under the Tools menu and the Backup section, click on Tools in which to save the exported file. When the File Download pop-up window appears, select the file that contains the saved firewall settings, then click OK. Step 1. Click Upload Configuration...
Product Manual
Page 63
... configuration file to the DFL-200 if a backup of the device has been downloaded to your Local Machine Prior to factory default settings using the Reset button located at the rear of the Wizard to the factory defaults. This procedure will revert the system to an older version. Step 3. You can be accessed via its original configuration, including resetting interface addresses. Make sure you have been made to the DFL-200 and will possibly change the DFL-200 firmware version to factory default settings through a web...
... configuration file to the DFL-200 if a backup of the device has been downloaded to your Local Machine Prior to factory default settings using the Reset button located at the rear of the Wizard to the factory defaults. This procedure will revert the system to an older version. Step 3. You can be accessed via its original configuration, including resetting interface addresses. Make sure you have been made to the DFL-200 and will possibly change the DFL-200 firmware version to factory default settings through a web...
Product Manual
Page 64
... backup the system configuration before upgrading the software. The updating process will not overwrite the system configuration. Make sure the firmware file is stored on a flash memory card. Upgrade IDS Signature-database To upgrade the signature-database first download the newest IDS signatures from support.dlink.com (US). Though it is not necessary, it is rewritable and re-readable. Upgrade Firmware To upgrade the firmware of the DFL-200, obtain the latest version...
... backup the system configuration before upgrading the software. The updating process will not overwrite the system configuration. Make sure the firmware file is stored on a flash memory card. Upgrade IDS Signature-database To upgrade the signature-database first download the newest IDS signatures from support.dlink.com (US). Though it is not necessary, it is rewritable and re-readable. Upgrade Firmware To upgrade the firmware of the DFL-200, obtain the latest version...
Product Manual
Page 105
Select the Security tab and click IPSec Settings 3. 2. Check Use pre-shared key for authentication, type the key and click OK
Select the Security tab and click IPSec Settings 3. 2. Check Use pre-shared key for authentication, type the key and click OK