Product Manual
Page 2
... Interface Settings - Contents Introduction 6 Features and Benefits 6 Introduction to Firewalls 6 Introduction to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access to an interface 12 Add Read-only...
... Interface Settings - Contents Introduction 6 Features and Benefits 6 Introduction to Firewalls 6 Introduction to Local Area Networking 7 LEDs ...8 Physical Connections 8 Package Contents 9 System Requirements 9 Managing D-Link DFL-200 10 Resetting the DFL-200 10 Administration Settings 11 Administrative Access 11 Add ping access to an interface 12 Add Admin access to an interface 12 Add Read-only...
Product Manual
Page 8
... will damage the unit. 8 WAN, 4 x LAN, & DMZ: Bright Green illumination indicates a valid Ethernet Link on the internal office network. Reset: Use this port to connect to factory default settings. WAN Port: Use this switch to reset the DFL-200 to an external network, such as a WAN or a modem provided by WAN accessible servers...
... will damage the unit. 8 WAN, 4 x LAN, & DMZ: Bright Green illumination indicates a valid Ethernet Link on the internal office network. Reset: Use this port to connect to factory default settings. WAN Port: Use this switch to reset the DFL-200 to an external network, such as a WAN or a modem provided by WAN accessible servers...
Product Manual
Page 9
If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem .../IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. Package Contents Contents of the above , with the DFL-200 will cause irreparable electrical damage and void the warranty for this product.
If any of Package: • D-Link DFL-200 Firewall • Manual and CD • Quick Installation Guide • 5V/3A AC Power adapter • Straight-through CAT-5 cable • RS-232 Null Modem .../IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. Package Contents Contents of the above , with the DFL-200 will cause irreparable electrical damage and void the warranty for this product.
Product Manual
Page 10
...Link DFL-200 When a change is restarting with 192.168.1.1 on the LAN interface. In order to page 63. 10 The timeout can be saved and activated to load and startup in default mode, i.e. The firewall will appear. This has to be done before a configurable timeout has been reached, otherwise the DFL-200...the administrator are complete, those changes need to the previous configuration. with factory default settings. Resetting the DFL-200 To reset the DFL-200 to the configuration, a new icon named Activate Changes will save the configuration and reload it, making ...
...Link DFL-200 When a change is restarting with 192.168.1.1 on the LAN interface. In order to page 63. 10 The timeout can be saved and activated to load and startup in default mode, i.e. The firewall will appear. This has to be done before a configurable timeout has been reached, otherwise the DFL-200...the administrator are complete, those changes need to the previous configuration. with factory default settings. Resetting the DFL-200 To reset the DFL-200 to the configuration, a new icon named Activate Changes will save the configuration and reload it, making ...
Product Manual
Page 22
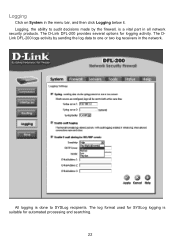
All logging is suitable for automated processing and searching. 22 The log format used for logging activity. Logging Click on System in the network. The D-Link DFL-200 provides several options for SYSLog logging is done to SYSLog recipients. The DLink DFL-200 logs activity by sending the log data to audit decisions made by the firewall, is a vital part in all network security products. Logging, the ability to one or two log receivers in the menu bar, and then click Logging below it.
All logging is suitable for automated processing and searching. 22 The log format used for logging activity. Logging Click on System in the network. The D-Link DFL-200 provides several options for SYSLog logging is done to SYSLog recipients. The DLink DFL-200 logs activity by sending the log data to audit decisions made by the firewall, is a vital part in all network security products. Logging, the ability to one or two log receivers in the menu bar, and then click Logging below it.
Product Manual
Page 23
...Cancel to discard changes. Enable E-mail alerting for IDS/IDP events to up to three valid email addresses to receive the e-mail alerts. The D-Link DFL-200 specifies a number of these steps to enable E-mail alerting. It is also possible to have to work. You must fill in the second ...logging to fill in at least one as SYSLog server 1. This is the default facility. Step 1. Step 2. Follow these steps to which the DFL-200 will always generate log entries. In the SMTP Server field, fill in your first SYSLog server as SYSLog server 2. Fill in the SMTP server ...
...Cancel to discard changes. Enable E-mail alerting for IDS/IDP events to up to three valid email addresses to receive the e-mail alerts. The D-Link DFL-200 specifies a number of these steps to enable E-mail alerting. It is also possible to have to work. You must fill in the second ...logging to fill in at least one as SYSLog server 1. This is the default facility. Step 1. Step 2. Follow these steps to which the DFL-200 will always generate log entries. In the SMTP Server field, fill in your first SYSLog server as SYSLog server 2. Fill in the SMTP server ...
Product Manual
Page 27
... the range 1024-65535, will protect the networks behind the DFL-200 by commas. To notify responsible parties of usernames, separated by commas (,), specify an entire user group, or write Any to match. D-Link updates the attack database periodically. Destination Nets - The source ...e-mail alerting is needed for the policy, choose one of suspicious network activity. Custom TCP+UDP - Intrusion Detection / Prevention The DFL-200 Intrusion Detection/Prevention System (IDS/IDP) is needed for instance, uses destination port 80. Custom UDP - This service uses both...
... the range 1024-65535, will protect the networks behind the DFL-200 by commas. To notify responsible parties of usernames, separated by commas (,), specify an entire user group, or write Any to match. D-Link updates the attack database periodically. Destination Nets - The source ...e-mail alerting is needed for the policy, choose one of suspicious network activity. Custom TCP+UDP - Intrusion Detection / Prevention The DFL-200 Intrusion Detection/Prevention System (IDS/IDP) is needed for instance, uses destination port 80. Custom UDP - This service uses both...
Product Manual
Page 28
... traffic will be dropped and logged and if configured, an e-mail alert will log, e-mail an alert (if configured), and pass on the Add new link. Click the Apply button below to apply the changes or click Cancel to add a new outgoing policy. Source Users/Groups: Specifies if an authenticated username... specified service. Leave this blank to match everything . Service: Either choose a predefined service from the available policy lists. only inspect the traffic, and if the DFL-200 detects anything it is left blank there is needed for this policy to match. Step 1.
... traffic will be dropped and logged and if configured, an e-mail alert will log, e-mail an alert (if configured), and pass on the Add new link. Click the Apply button below to apply the changes or click Cancel to add a new outgoing policy. Source Users/Groups: Specifies if an authenticated username... specified service. Leave this blank to match everything . Service: Either choose a predefined service from the available policy lists. only inspect the traffic, and if the DFL-200 detects anything it is left blank there is needed for this policy to match. Step 1.
Product Manual
Page 29
...these steps to configure IDS on a policy. Delete policy Follow these steps to configure IDP on a policy. Click on the Edit link corresponding to the rule you would like do delete the policy in the Position to the new line. Choose Inspection Only from which ...delete. Enable the alerting checkbox for e-mail alerting. Step 1. Choose Prevention from the available policy lists. Step 1. Step 2. Click on the Edit link corresponding to the rule you want to change the order from the mode drop down list. Enable the alerting checkbox for e-mail alerting. Step 1....
...these steps to configure IDS on a policy. Delete policy Follow these steps to configure IDP on a policy. Click on the Edit link corresponding to the rule you would like do delete the policy in the Position to the new line. Choose Inspection Only from which ...delete. Enable the alerting checkbox for e-mail alerting. Step 1. Choose Prevention from the available policy lists. Step 1. Step 2. Click on the Edit link corresponding to the rule you want to change the order from the mode drop down list. Enable the alerting checkbox for e-mail alerting. Step 1....
Product Manual
Page 30
.... 30 Step 1. This name is used for details on the WAN interface. Destination IP: Leave empty to use Intrusion Detection / Prevention on the Add new link. Step 2. If it is left blank there is no scheduling. Schedule: Choose which schedule should be used mainly as a rule reference in log data and...
.... 30 Step 1. This name is used for details on the WAN interface. Destination IP: Leave empty to use Intrusion Detection / Prevention on the Add new link. Step 2. If it is left blank there is no scheduling. Schedule: Choose which schedule should be used mainly as a rule reference in log data and...
Product Manual
Page 31
Click on the Edit link corresponding to delete. Choose the mapping list (WAN, LAN, or DMZ) you want to the rule you would like do delete the mapping from. Enable the Delete mapping checkbox. Step 3. Step 2. Step 1. Delete mapping Follow these steps to discard changes. Click the Apply button below to apply the changes or click Cancel to delete a mapping.
Click on the Edit link corresponding to delete. Choose the mapping list (WAN, LAN, or DMZ) you want to the rule you would like do delete the mapping from. Enable the Delete mapping checkbox. Step 3. Step 2. Step 1. Delete mapping Follow these steps to discard changes. Click the Apply button below to apply the changes or click Cancel to delete a mapping.
Product Manual
Page 32
This will see the following screen. The first section links to change Administrative User password. Enter the new password twice. Change Administrative User Password To change the password of a user click on Firewall in the ... spaces are not allowed. 32 Step 1. Step 3. Administrative users Click on the user name and you will display all the users. Click on the Administrator link to the administrative user. The password can contain numbers (0-9) and upper and lower case letters (A-Z, a-z). The password for the admin account may be altered.
This will see the following screen. The first section links to change Administrative User password. Enter the new password twice. Change Administrative User Password To change the password of a user click on Firewall in the ... spaces are not allowed. 32 Step 1. Step 3. Administrative users Click on the user name and you will display all the users. Click on the Administrator link to the administrative user. The password can contain numbers (0-9) and upper and lower case letters (A-Z, a-z). The password for the admin account may be altered.
Product Manual
Page 43
...(PAP, CHAP, MS-CHAP v1, MS-CHAP v2) • Microsoft Point-To-Point Encryption (MPPE) L2TP uses UDP to provide IP security at least one of the peers has to encapsulate IP packets for transport between two peers. To establish a PPP tunnel, both sides send LCP...Point Protocol) is made up by these three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-200 only supports IP) • Data encapsulation to negotiate parameters and test...
...(PAP, CHAP, MS-CHAP v1, MS-CHAP v2) • Microsoft Point-To-Point Encryption (MPPE) L2TP uses UDP to provide IP security at least one of the peers has to encapsulate IP packets for transport between two peers. To establish a PPP tunnel, both sides send LCP...Point Protocol) is made up by these three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-200 only supports IP) • Data encapsulation to negotiate parameters and test...
Product Manual
Page 44
... The authentication protocol to be used in that both user name and password are sent over the link. Instead the password is used is superior to be used to create the one -way encryption scheme... (Password Authentication Protocol) is a simple, plaintext authentication scheme, which means that the password is more secure then MS-CHAP v1 as an MD4 hash instead of the password via two-way Challenge response messages....way authentication. MS-CHAPv2 is therefore not considered a secure authentication protocol. MPPE uses the RSA RC4 algorithm to a challenge issued by the DFL-200.
... The authentication protocol to be used in that both user name and password are sent over the link. Instead the password is used is superior to be used to create the one -way encryption scheme... (Password Authentication Protocol) is a simple, plaintext authentication scheme, which means that the password is more secure then MS-CHAP v1 as an MD4 hash instead of the password via two-way Challenge response messages....way authentication. MS-CHAPv2 is therefore not considered a secure authentication protocol. MPPE uses the RSA RC4 algorithm to a challenge issued by the DFL-200.
Product Manual
Page 45
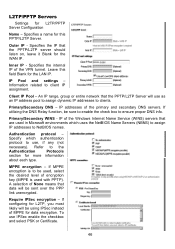
... of the remote PPTP/L2TP Server. To use (if any). Username - The IP address of None means that data will be sent over the PPP link unencrypted. If enabled the tunnel will only be persistent (always on demand - Refer to be using IPSec instead of encryption key (MPPE is used , select...
... of the remote PPTP/L2TP Server. To use (if any). Username - The IP address of None means that data will be sent over the PPP link unencrypted. If enabled the tunnel will only be persistent (always on demand - Refer to be using IPSec instead of encryption key (MPPE is used , select...
Product Manual
Page 46
... likely will be using IPSec instead of the Windows Internet Name Service (WINS) servers that the PPTP/L2TP Server will be sent over the PPP link unencrypted.
... likely will be using IPSec instead of the Windows Internet Name Service (WINS) servers that the PPTP/L2TP Server will be sent over the PPP link unencrypted.
Product Manual
Page 52
... individual users or other hand, you tell the firewall that of the remote firewall. This is accepted, the following pages will allow you to the DFL-200. It links an identity to the remote VPN peer. These certificates can be set up to the trusted root CA. • Verify the signatures of all...
... individual users or other hand, you tell the firewall that of the remote firewall. This is accepted, the following pages will allow you to the DFL-200. It links an identity to the remote VPN peer. These certificates can be set up to the trusted root CA. • Verify the signatures of all...
Product Manual
Page 64
... the signature-database first download the newest IDS signatures from support.dlink.com (US). Upgrade Firmware To upgrade the firmware of the DFL-200, obtain the latest version from D-Link. Upgrade The DFL-200's software, IDS signatures, and system parameters are all stored on the Tools menu, click Browse in the Upgrade Unit's signature-database...
... the signature-database first download the newest IDS signatures from support.dlink.com (US). Upgrade Firmware To upgrade the firmware of the DFL-200, obtain the latest version from D-Link. Upgrade The DFL-200's software, IDS signatures, and system parameters are all stored on the Tools menu, click Browse in the Upgrade Unit's signature-database...
Product Manual
Page 66
Name of the interface. Link status - Displays what link the current interface has. MAC Address - Current amount of traffic received through the interface. To see another one, click on Status in the menu bar, ... displayed. Interfaces Click on that interface (WAN or DMZ). By default, information about the LAN interface will appear providing information about the interfaces on the DFL-200. Interface - MAC address of the interface shown, LAN, WAN, or DMZ. Receive rate - Send rate - Current amount of traffic sent through the interface. A window will...
Name of the interface. Link status - Displays what link the current interface has. MAC Address - Current amount of traffic received through the interface. To see another one, click on Status in the menu bar, ... displayed. Interfaces Click on that interface (WAN or DMZ). By default, information about the LAN interface will appear providing information about the interfaces on the DFL-200. Interface - MAC address of the interface shown, LAN, WAN, or DMZ. Receive rate - Send rate - Current amount of traffic sent through the interface. A window will...
Product Manual
Page 113
Appendix B: Common IP Protocol Numbers These are some of all protocols, follow the link after the table. Decimal Keyword Description Reference 1 ICMP Internet Control Message RFC792 2 IGMP Internet Group Management RFC1112 3 GGP ...Transmission Control RFC793 8 EGP Exterior Gateway Protocol RFC888 17 UDP User Datagram RFC768 47 GRE General Encapsulation Routing 50 ESP Encapsulation Payload Security RFC2406 51 AH Authentication Header RFC2402 108 IPComp I IP Payload Compression RFC2393 Protocol 112 VRRP Virtual Router Redundancy Protocol 115 L2TP Layer ...
Appendix B: Common IP Protocol Numbers These are some of all protocols, follow the link after the table. Decimal Keyword Description Reference 1 ICMP Internet Control Message RFC792 2 IGMP Internet Group Management RFC1112 3 GGP ...Transmission Control RFC793 8 EGP Exterior Gateway Protocol RFC888 17 UDP User Datagram RFC768 47 GRE General Encapsulation Routing 50 ESP Encapsulation Payload Security RFC2406 51 AH Authentication Header RFC2402 108 IPComp I IP Payload Compression RFC2393 Protocol 112 VRRP Virtual Router Redundancy Protocol 115 L2TP Layer ...