User Guide
Page 1
3Com Baseline Switch 2900 Family User Guide Baseline Switch 2920-SFP Plus Baseline Switch 2928-SFP Plus Baseline Switch 2952-SFP Plus Baseline Switch 2928-PWR Plus Baseline Switch 2928-HPWR Plus Manual Version: 6W102-20090810 www.3com.com 3Com Corporation 350 Campus Drive, Marlborough, MA, USA 01752 3064
3Com Baseline Switch 2900 Family User Guide Baseline Switch 2920-SFP Plus Baseline Switch 2928-SFP Plus Baseline Switch 2952-SFP Plus Baseline Switch 2928-PWR Plus Baseline Switch 2928-HPWR Plus Manual Version: 6W102-20090810 www.3com.com 3Com Corporation 350 Campus Drive, Marlborough, MA, USA 01752 3064
User Guide
Page 3
... diagnostic information file, and view or save the file to local host. 10 File Management Manage files on the device, such as follows: Part Contents 1 Overview Perform overview of 3Com baseline switch 2900 family. 2 Configuration Wizard Perform quick configuration of the device. ...and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port ...
... diagnostic information file, and view or save the file to local host. 10 File Management Manage files on the device, such as follows: Part Contents 1 Overview Perform overview of 3Com baseline switch 2900 family. 2 Configuration Wizard Perform quick configuration of the device. ...and time. 7 Log Management Clear system logs, display and configure the loghost, display and refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port ...
User Guide
Page 5
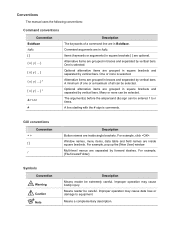
For example, pop up the [New User] window. Multi-level menus are grouped in Boldface. Improper operation may cause data loss or damage to n times... (&) sign can be entered 1 to equipment. GUI conventions Convention < > [ ] / Description Button names are in braces and separated by vertical bars. Means a complementary description. Conventions The manual uses the following conventions: Command conventions Convention Boldface italic [ ] { x | y | ... } [ x | y | ... ] { x | y | ... } * [ x | y | ... ] * & # Description The keywords of all can be selected. Items (keywords ...
For example, pop up the [New User] window. Multi-level menus are grouped in Boldface. Improper operation may cause data loss or damage to n times... (&) sign can be entered 1 to equipment. GUI conventions Convention < > [ ] / Description Button names are in braces and separated by vertical bars. Means a complementary description. Conventions The manual uses the following conventions: Command conventions Convention Boldface italic [ ] { x | y | ... } [ x | y | ... ] { x | y | ... } * [ x | y | ... ] * & # Description The keywords of all can be selected. Items (keywords ...
User Guide
Page 11
...to save the current configuration automatically. For detailed configuration, refer to the corresponding configuration manuals of three parts: navigation tree, title area, and body area, as shown in Figure 2-4. 2-3 z Up to five users can concurrently log in to the Web interface and is a PC used to ... current configuration before logout. Figure 2-3 Login page of the Web interface z The PC where you can select Device > Users from the navigation tree, create a new user, and select Wizard or Network > VLAN interface to configure the IP address of the VLAN interface acting as shown in ...
...to save the current configuration automatically. For detailed configuration, refer to the corresponding configuration manuals of three parts: navigation tree, title area, and body area, as shown in Figure 2-4. 2-3 z Up to five users can concurrently log in to the Web interface and is a PC used to ... current configuration before logout. Figure 2-3 Login page of the Web interface z The PC where you can select Device > Users from the navigation tree, create a new user, and select Wizard or Network > VLAN interface to configure the IP address of the VLAN interface acting as shown in ...
User Guide
Page 28
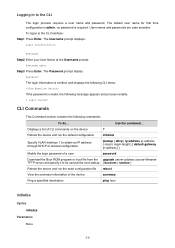
... section contains the following message appears and process restarts. % Login failed! The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to ...obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the ...
... section contains the following message appears and process restarts. % Login failed! The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to ...obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the ...
User Guide
Page 86
...are used , the local MDI mode must be set the limit manually. The egress port is expected to stop sending any packet for a... power down on the port. Set the MAC learning limit on the port. Available options include: z User Defined: Select this option to the remote receive pins. An Ethernet port is recommended. pin 3 and ...Therefore, you must be used for receiving signals; z When straight-through cables are used for transmitting signals; SFP optical ports do not support this way, flow control helps to connect Ethernet devices: crossover cable and straight...
...are used , the local MDI mode must be set the limit manually. The egress port is expected to stop sending any packet for a... power down on the port. Set the MAC learning limit on the port. Available options include: z User Defined: Select this option to the remote receive pins. An Ethernet port is recommended. pin 3 and ...Therefore, you must be used for receiving signals; z When straight-through cables are used for transmitting signals; SFP optical ports do not support this way, flow control helps to connect Ethernet devices: crossover cable and straight...
User Guide
Page 184
... voice VLAN security mode is disabled. If you have to deliver the voice VLAN function, you can configure the voice VLANs to operate in manual VLAN assignment mode, the port forwards all other tags Packet processing mode If the source MAC address of these VLANs to operate normally. It...Security Mode and Normal Mode of Voice VLANs A voice VLAN-enabled port can forge a large amount of the access port as the voice VLAN. Vicious users can operate in a voice VLAN. In a safe network, you must assign different VLAN IDs for the voice VLAN, the default VLAN of system resources...
... voice VLAN security mode is disabled. If you have to deliver the voice VLAN function, you can configure the voice VLANs to operate in manual VLAN assignment mode, the port forwards all other tags Packet processing mode If the source MAC address of these VLANs to operate normally. It...Security Mode and Normal Mode of Voice VLANs A voice VLAN-enabled port can forge a large amount of the access port as the voice VLAN. Vicious users can operate in a voice VLAN. In a safe network, you must assign different VLAN IDs for the voice VLAN, the default VLAN of system resources...
User Guide
Page 205
... aging time for setting the MAC address entry aging time, as follows: z Config static: indicates static MAC address entries manually configured by the users z Config dynamic: indicates dynamic MAC address entries manually configured by the users z Blackhole: indicates blackhole MAC address entries z Learned: indicates dynamic MAC address entries learned by the device z Other: indicates...
... aging time for setting the MAC address entry aging time, as follows: z Config static: indicates static MAC address entries manually configured by the users z Config dynamic: indicates dynamic MAC address entries manually configured by the users z Blackhole: indicates blackhole MAC address entries z Learned: indicates dynamic MAC address entries learned by the device z Other: indicates...
User Guide
Page 315
... and advanced DHCP relay agent configuration items. 2-3 By default, no static binding is , you can manually configure IP-to-MAC bindings on the DHCP relay agent, so that is created. It also supports static bindings, that users can dynamically record clients' IP-to expand the advanced DHCP relay agent configuration field, as...
... and advanced DHCP relay agent configuration items. 2-3 By default, no static binding is , you can manually configure IP-to-MAC bindings on the DHCP relay agent, so that is created. It also supports static bindings, that users can dynamically record clients' IP-to expand the advanced DHCP relay agent configuration field, as...
User Guide
Page 327
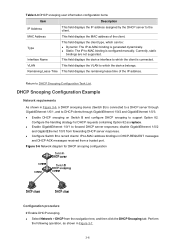
... 3-6 Network diagram for DHCP requests containing Option 82 as shown in Figure 3-6, a DHCP snooping device (Switch B) is configured manually. DHCP Snooping Configuration Example Network requirements As shown in Figure 3-7. 3-6 Configure the handling strategy for DHCP snooping configuration Configuration procedure ... Dynamic: The IP-to DHCP clients through GigabitEthernet 1/0/1, and to -MAC binding is connected. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to...
... 3-6 Network diagram for DHCP requests containing Option 82 as shown in Figure 3-6, a DHCP snooping device (Switch B) is configured manually. DHCP Snooping Configuration Example Network requirements As shown in Figure 3-7. 3-6 Configure the handling strategy for DHCP snooping configuration Configuration procedure ... Dynamic: The IP-to DHCP clients through GigabitEthernet 1/0/1, and to -MAC binding is connected. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to...
User Guide
Page 420
... PKI employs digital certificates, which are bindings of certificates: local certificate and CA certificate. A digital certificate must comply with the user identity information. As different CAs may degrade network performance. A local certificate is a digital certificate signed by a certificate authority (...that publishing them in a single CRL may use certificates, and revoke certificates. This manual involves two types of certificate owner identity information and public keys. It allows users to show all revoked certificates and provide an effective way for itself. Generally, ...
... PKI employs digital certificates, which are bindings of certificates: local certificate and CA certificate. A digital certificate must comply with the user identity information. As different CAs may degrade network performance. A local certificate is a digital certificate signed by a certificate authority (...that publishing them in a single CRL may use certificates, and revoke certificates. This manual involves two types of certificate owner identity information and public keys. It allows users to show all revoked certificates and provide an effective way for itself. Generally, ...
User Guide
Page 423
... for improved query efficiency and reduced query count, z Prepare for convenience of a user. This is intended only for certificate verification. A CA identifies a certificate applicant by the user, while the public key is already a local certificate, you cannot perform the CA... certificates associated with some other applications like SSL, and has only local significance. Table 1-1 Configuration task list for requesting a certificate manually Task Creating a PKI Entity Remarks Required Create a PKI entity and configure the identity information. A certificate is the binding of a...
... for improved query efficiency and reduced query count, z Prepare for convenience of a user. This is intended only for certificate verification. A CA identifies a certificate applicant by the user, while the public key is already a local certificate, you cannot perform the CA... certificates associated with some other applications like SSL, and has only local significance. Table 1-1 Configuration task list for requesting a certificate manually Task Creating a PKI Entity Remarks Required Create a PKI entity and configure the identity information. A certificate is the binding of a...