User Guide
Page 7
... Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI Commands 3-6 initialize 3-6 ipsetup 3-7 password 3-8 ping 3-8 quit 3-9 reboot 3-9 summary 3-10 upgrade 3-11 Configuration Example for Upgrading the Host Software Through the CLI 3-12 i
... Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI Commands 3-6 initialize 3-6 ipsetup 3-7 password 3-8 ping 3-8 quit 3-9 reboot 3-9 summary 3-10 upgrade 3-11 Configuration Example for Upgrading the Host Software Through the CLI 3-12 i
User Guide
Page 9
...interfaces. Table 2-1 The default Web login information Information needed at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on 3Com's network devices. You can use the default information to log in to ...the network, or no DHCP server exists in Figure 2-2. 2 Configuration Through the Web Interface Web-Based Network Management Operating Environment 3Com provides the Web-based network management function to the Web Interface Default Login Information The device is provided with the default Web login...
...interfaces. Table 2-1 The default Web login information Information needed at login Username Password IP address of the device (VLAN-interface 1) Default value admin None Default IP address of the device, depending on 3Com's network devices. You can use the default information to log in to ...the network, or no DHCP server exists in Figure 2-2. 2 Configuration Through the Web Interface Web-Based Network Management Operating Environment 3Com provides the Web-based network management function to the Web Interface Default Login Information The device is provided with the default Web login...
User Guide
Page 10
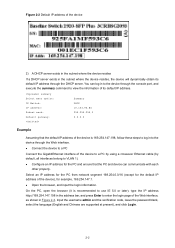
summary Select menu option: IP Method: IP address: Summary DHCP 10.153.96.86 Subnet mask: Default gateway: 255.255.255.0 0.0.0.0 Example Assuming that the PC and device can log in to the device through the ... browser, and input the login information. z Configure an IP address for example, 169.254.147.1. Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 z Connect the device to a PC Connect the GigabitEthernet interface of the...
summary Select menu option: IP Method: IP address: Summary DHCP 10.153.96.86 Subnet mask: Default gateway: 255.255.255.0 0.0.0.0 Example Assuming that the PC and device can log in to the device through the ... browser, and input the login information. z Configure an IP address for example, 169.254.147.1. Input the username admin and the verification code, leave the password blank, select the language (English and Chinese are supported at present), and click Login. 2-2 z Connect the device to a PC Connect the GigabitEthernet interface of the...
User Guide
Page 14
... Summary Display the brief information of a port mirroring group. Visitor Loopbac k Loopback Perform loopback tests on interfaces. Displays feature information by features. Monitor Super Password Configure a password for collecting traffic statistics on Ethernet interfaces. Management Users Create Modify Create an FTP or Telnet user. Modify FTP or Telnet user information. Interval Configurati...
... Summary Display the brief information of a port mirroring group. Visitor Loopbac k Loopback Perform loopback tests on interfaces. Displays feature information by features. Monitor Super Password Configure a password for collecting traffic statistics on Ethernet interfaces. Management Users Create Modify Create an FTP or Telnet user. Modify FTP or Telnet user information. Interval Configurati...
User Guide
Page 28
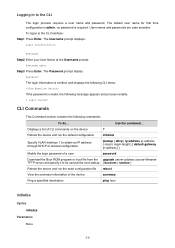
... ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the upgrade server-address source-filename TFTP server and specify it to be used at...commands on the device ? Use the command... Logging In to the CLI Interface: Step1 Press Enter. User names and passwords are case sensitive. The Password prompt display Password: The login information is verified, and displays the following commands: To do... To logon to the CLI The login...
... ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of a user password Download the Boot ROM program or boot file from the upgrade server-address source-filename TFTP server and specify it to be used at...commands on the device ? Use the command... Logging In to the CLI Interface: Step1 Press Enter. User names and passwords are case sensitive. The Password prompt display Password: The login information is verified, and displays the following commands: To do... To logon to the CLI The login...
User Guide
Page 30
...ping 1.1.2.2 PING 1.1.2.2: 56 data bytes, press CTRL_C to 20 characters). password Change password for user: admin Old password: *** Enter new password: ** Retype password: ** The password has been successfully changed. ping Syntax ping host Parameters host: Destination IP...packet(s) received 0.00% packet loss 3-8 You can enter Ctrl+C to modify the login password of user admin. Examples # Modify the login password of a user. password Syntax password Parameters None Description Use the password command to terminate a ping operation. Description Use the ping command to ping a specified...
...ping 1.1.2.2 PING 1.1.2.2: 56 data bytes, press CTRL_C to 20 characters). password Change password for user: admin Old password: *** Enter new password: ** Retype password: ** The password has been successfully changed. ping Syntax ping host Parameters host: Destination IP...packet(s) received 0.00% packet loss 3-8 You can enter Ctrl+C to modify the login password of user admin. Examples # Modify the login password of a user. password Syntax password Parameters None Description Use the password command to terminate a ping operation. Description Use the ping command to ping a specified...
User Guide
Page 44
...control panel of stack members. Configuring slave devices of a stack Configuring Stack Ports Required Configure a port of a slave device that the username, password, and access right you used to log on the slave device; Optional Display the control panels of a slave device, you must ensure that connects... the master device are the same with those configured on to the web network management interface of the master device that the username, password, and access right you used to log on the slave device; Logging Into a Slave Device From the Master Before logging into the...
...control panel of stack members. Configuring slave devices of a stack Configuring Stack Ports Required Configure a port of a slave device that the username, password, and access right you used to log on the slave device; Optional Display the control panels of a slave device, you must ensure that connects... the master device are the same with those configured on to the web network management interface of the master device that the username, password, and access right you used to log on the slave device; Logging Into a Slave Device From the Master Before logging into the...
User Guide
Page 101
Table of Contents 1 User Management 1-1 Overview 1-1 Users 1-1 Creating a User 1-1 Setting the Super Password 1-2 Switching the User Access Level to the Management Level 1-3 i
Table of Contents 1 User Management 1-1 Overview 1-1 Users 1-1 Creating a User 1-1 Setting the Super Password 1-2 Switching the User Access Level to the Management Level 1-3 i
User Guide
Page 102
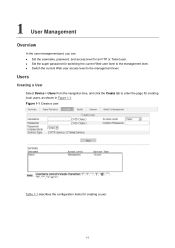
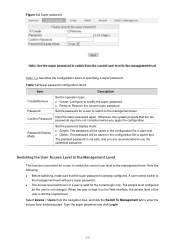
Users Creating a User Select Device > Users from the navigation tree, and click the Create tab to the management level. z Switch the current Web user access level to enter the page for an FTP or Telnet user. z Set the super password for creating a user. 1-1 Figure 1-1 Create a user Table 1-1 describes the configuration items for switching the current Web user level to the management level. 1 User Management Overview In the user management part, you can: z Set the username, password, and access level for creating local users, as shown in Figure 1-1.
Users Creating a User Select Device > Users from the navigation tree, and click the Create tab to the management level. z Switch the current Web user access level to enter the page for an FTP or Telnet user. z Set the super password for creating a user. 1-1 Figure 1-1 Create a user Table 1-1 describes the configuration items for switching the current Web user level to the management level. 1 User Management Overview In the user management part, you can: z Set the username, password, and access level for creating local users, as shown in Figure 1-1.
User Guide
Page 103
... users, or back up/restore the application file. z Visitor: Users of the input password is configured, the switchover will fail. if not, the system considers the password as a ciphertext password; Input the same password again. Service Type Set the service type, including FTP and Telnet services. Select Device ...configure the device, but cannot configure the device. Users of this level can perform different operations. the input plain password with a length greater than 16 but smaller than or equal to use the network diagnostic tool ping and trace route. z When...
... users, or back up/restore the application file. z Visitor: Users of the input password is configured, the switchover will fail. if not, the system considers the password as a ciphertext password; Input the same password again. Service Type Set the service type, including FTP and Telnet services. Select Device ...configure the device, but cannot configure the device. Users of this level can perform different operations. the input plain password with a length greater than 16 but smaller than or equal to use the network diagnostic tool ping and trace route. z When...
User Guide
Page 104
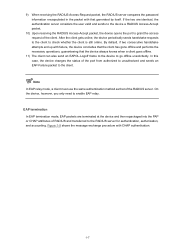
... the navigation tree, and click the Switch To Management tab to the management level. Set the password for the current login only. z Remove: Remove the current super password. When the user re-logs in plain text. A user cannot switch to the Management Level ...user to switch to enter the access level switching page. Table 1-2 Super password configuration items Item Description Create/Remove Password Set the operation type: z Create: Configure or modify the super password. z Simple: The password will be saved in the configuration file in to the management level. z...
... the navigation tree, and click the Switch To Management tab to the management level. Set the password for the current login only. z Remove: Remove the current super password. When the user re-logs in plain text. A user cannot switch to the Management Level ...user to switch to enter the access level switching page. Table 1-2 Super password configuration items Item Description Create/Remove Password Set the operation type: z Create: Configure or modify the super password. z Simple: The password will be saved in the configuration file in to the management level. z...
User Guide
Page 152
...the Add Trap Target Host page, as shown in Figure 1-16. 1-11 z When the security level is Auth/Priv. Authentication Password Confirm Authentication Password Set the authentication password when the security level is Auth/Priv, you can select an SNMP group of SNMP packets, that is NoAuth/NoPriv, you can...as shown in Figure 1-15. Select an authentication mode (including MD5 and SHA) when the security level is Auth/Priv. The confirm authentication password must be the same with a specific source IP address, so as to allow or prohibit the specified NMS to restrict the source IP ...
...the Add Trap Target Host page, as shown in Figure 1-16. 1-11 z When the security level is Auth/Priv. Authentication Password Confirm Authentication Password Set the authentication password when the security level is Auth/Priv, you can select an SNMP group of SNMP packets, that is NoAuth/NoPriv, you can...as shown in Figure 1-15. Select an authentication mode (including MD5 and SHA) when the security level is Auth/Priv. The confirm authentication password must be the same with a specific source IP address, so as to allow or prohibit the specified NMS to restrict the source IP ...
User Guide
Page 158
... be consistent with the agent and query and reconfigure values of authentication and privacy. Otherwise, you need to configure the related authentication mode, authentication password, privacy mode, privacy password, and so on the agent. z If an idle interface on the agent is shut down or brought up, the NMS will receive a trap...
... be consistent with the agent and query and reconfigure values of authentication and privacy. Otherwise, you need to configure the related authentication mode, authentication password, privacy mode, privacy password, and so on the agent. z If an idle interface on the agent is shut down or brought up, the NMS will receive a trap...
User Guide
Page 332
... service enabled, accessing and controlling the device with an ACL, thus reducing attacks of the device can also serve as IP spoofing and plain text password interception. You can log in to the SFTP server for secure file transfer. You can serve as needed. In this way, the performance and security...
... service enabled, accessing and controlling the device with an ACL, thus reducing attacks of the device can also serve as IP spoofing and plain text password interception. You can log in to the SFTP server for secure file transfer. You can serve as needed. In this way, the performance and security...
User Guide
Page 357
... in EAP over RADIUS (EAPOR) packets on the authentication result, as a unity of a controlled port You can be regarded as shown in either with the Password Authentication Protocol (PAP) or Challenge Handshake Authentication Protocol (CHAP) attribute, and then transferred to access the network without authentication.
... in EAP over RADIUS (EAPOR) packets on the authentication result, as a unity of a controlled port You can be regarded as shown in either with the Password Authentication Protocol (PAP) or Challenge Handshake Authentication Protocol (CHAP) attribute, and then transferred to access the network without authentication.
User Guide
Page 361
... an EAP-Request/Identity packet for the username of the client. 3) When the client receives the EAP-Request/Identity packet, it encrypts the password information using a randomly generated challenge, and sends the challenge information through a RADIUS Access-Challenge packet to the device. 6) After receiving the ...MD5 Challenge packet to the client. 7) When receiving the EAP-Request/MD5 Challenge packet, the client uses the offered challenge to encrypt the password part (this process is not reversible), creates an EAP-Response/MD5 Challenge packet, and then sends the packet to the device. 8) ...
... an EAP-Request/Identity packet for the username of the client. 3) When the client receives the EAP-Request/Identity packet, it encrypts the password information using a randomly generated challenge, and sends the challenge information through a RADIUS Access-Challenge packet to the device. 6) After receiving the ...MD5 Challenge packet to the client. 7) When receiving the EAP-Request/MD5 Challenge packet, the client uses the offered challenge to encrypt the password part (this process is not reversible), creates an EAP-Response/MD5 Challenge packet, and then sends the packet to the device. 8) ...
User Guide
Page 362
...shows the message exchange procedure with that generated by itself. 9) When receiving the RADIUS Access-Request packet, the RADIUS server compares the password information encapsulated in the packet with CHAP authentication. 1-7 EAP termination In EAP termination mode, EAP packets are identical, the authentication server ...considers the user valid and sends to the device a RADIUS Access-Accept packet. 10) Upon receiving the RADIUS Access-Accept packet, the device opens the port to check whether the client is still online. After...
...shows the message exchange procedure with that generated by itself. 9) When receiving the RADIUS Access-Request packet, the RADIUS server compares the password information encapsulated in the packet with CHAP authentication. 1-7 EAP termination In EAP termination mode, EAP packets are identical, the authentication server ...considers the user valid and sends to the device a RADIUS Access-Accept packet. 10) Upon receiving the RADIUS Access-Accept packet, the device opens the port to check whether the client is still online. After...
User Guide
Page 363
... port enabled with each other in EAP termination authentication process. Consequently, the device sends the challenge together with the username and encrypted password information from the client, it receives no response from the client to guarantee that cannot request for authentication. If it retransmits the request.... 802.1X Timers This section describes the timers used on an 802.1X device to the RADIUS server for encrypting the user password information in a reasonable manner. The first case is when the device authenticates the 802.1X client that the client, the device...
... port enabled with each other in EAP termination authentication process. Consequently, the device sends the challenge together with the username and encrypted password information from the client, it receives no response from the client to guarantee that cannot request for authentication. If it retransmits the request.... 802.1X Timers This section describes the timers used on an 802.1X device to the RADIUS server for encrypting the user password information in a reasonable manner. The first case is when the device authenticates the 802.1X client that the client, the device...
User Guide
Page 365
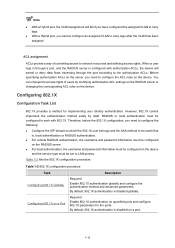
... configuration procedure Task Configuring 802.1X Globally Configuring 802.1X on the RADIUS server. z For local authentication, the username and password information must be configured on a Port Description Required Enable 802.1X authentication globally and configure the authentication method and advanced parameters.... ACL rules on the device. Table 1-2 lists the 802.1X configuration procedure. Before specifying authorization ACLs on a port. 1-10 By default, 802.1X authentication is disabled on the server, you need to the authorization ACLs. By default, 802.1X authentication...
... configuration procedure Task Configuring 802.1X Globally Configuring 802.1X on the RADIUS server. z For local authentication, the username and password information must be configured on a Port Description Required Enable 802.1X authentication globally and configure the authentication method and advanced parameters.... ACL rules on the device. Table 1-2 lists the 802.1X configuration procedure. Before specifying authorization ACLs on a port. 1-10 By default, 802.1X authentication is disabled on the server, you need to the authorization ACLs. By default, 802.1X authentication...
User Guide
Page 386
... is expected to the default ISP domain. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to create the RADIUS schemes to configure an accounting server. In addition, you also need to be referenced...
... is expected to the default ISP domain. In a networking scenario with multiple ISPs, an access device may have different user attributes (such as username and password structure, service type, and rights), you need to create the RADIUS schemes to configure an accounting server. In addition, you also need to be referenced...