User Guide
Page 3
... refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port Management Create, modify, delete, and enable/disable a port, and clear port statistics. 12 Port Mirroring Create, remove, and configure a port mirroring group. 13 User Management Create, modify, and remove an FTP or Telnet user, and display the brief information of FTP and Telnet users. 14 Loopback Test Perform loopback tests on interfaces, and display the average rate at the...
... refresh system logs. About This Manual Organization 3Com Baseline Switch 2900 Family User Guide is organized as displaying the file list, downloading a file, uploading a file, and removing a file. 11 Port Management Create, modify, delete, and enable/disable a port, and clear port statistics. 12 Port Mirroring Create, remove, and configure a port mirroring group. 13 User Management Create, modify, and remove an FTP or Telnet user, and display the brief information of FTP and Telnet users. 14 Loopback Test Perform loopback tests on interfaces, and display the average rate at the...
User Guide
Page 4
... Interface Statistics 22 VLAN 23 VLAN Interface 24 Voice VLAN 25 MAC Address 26 MSTP 27 Link Aggregation and LACP 28 LLDP 29 IGMP Snooping 30 Routing 31 DHCP 32 Service Management 33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Display and configure the energy saving settings of a port. Create VLANs...
... Interface Statistics 22 VLAN 23 VLAN Interface 24 Voice VLAN 25 MAC Address 26 MSTP 27 Link Aggregation and LACP 28 LLDP 29 IGMP Snooping 30 Routing 31 DHCP 32 Service Management 33 Diagnostic Tools 34 ARP 35 802.1X 36 AAA 37 RADIUS 38 User 39 PKI 40 Port Isolation Group 41 Authorized IP 42 ACL-QoS 43 PoE Contents Configure RMON, and dissplay, create, modify, and clear RMON statistics. Display and configure the energy saving settings of a port. Create VLANs...
User Guide
Page 7
... Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction to the Web-Based NM Functions 2-4 Introduction to the Controls on the Web Pages 2-11 Configuration Guidelines 2-13 3 Configuration Through the Command Line Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI...
... Interface 2-1 Web-Based Network Management Operating Environment 2-1 Logging In to the Web Interface 2-1 Default Login Information 2-1 Example 2-2 Logging Out of the Web Interface 2-3 Introduction to the Web Interface 2-3 Web User Level 2-4 Introduction to the Web-Based NM Functions 2-4 Introduction to the Controls on the Web Pages 2-11 Configuration Guidelines 2-13 3 Configuration Through the Command Line Interface 3-1 Getting Started with the Command Line Interface 3-1 Setting Up the Configuration Environment 3-1 Setting Terminal Parameters 3-2 Logging In to the CLI 3-6 CLI...
User Guide
Page 14
... on Ethernet interfaces. Create, modify, delete, and enable/disable a port, and clear port statistics. Management Users Create Modify Create an FTP or Telnet user. Configure 2-6 Remove a port mirroring group. Management Switch To Manageme nt Switch the current user level to the management level. Configure Alarm View, create, modify, and clear alarm entries. Monitor Configure Configure Modify Port Configure ports for collecting storm constrain statistics. Configure VCT VCT Check the status of the cables connected to Ethernet ports. Display, create, modify...
... on Ethernet interfaces. Create, modify, delete, and enable/disable a port, and clear port statistics. Management Users Create Modify Create an FTP or Telnet user. Configure 2-6 Remove a port mirroring group. Management Switch To Manageme nt Switch the current user level to the management level. Configure Alarm View, create, modify, and clear alarm entries. Monitor Configure Configure Modify Port Configure ports for collecting storm constrain statistics. Configure VCT VCT Check the status of the cables connected to Ethernet ports. Display, create, modify...
User Guide
Page 17
... Monitor Management RADIUS RADIUS Server Display and configure RADIUS server information. Add and remove ISP domains. Monitor Add, modify, and remove ARP entries. Configure ARP detection. Monitor Management Auth entic atio n AAA Authenticat ion Display the authentication configuration information of services: enabled or disabled. Configure Service Service Displays the states of an ISP domain. Visitor Visitor ARP Manage ment ARP Table Gratuitous ARP Display ARP table information. Function menu Description User level Remove Delete the selected IPv4 static routes...
... Monitor Management RADIUS RADIUS Server Display and configure RADIUS server information. Add and remove ISP domains. Monitor Add, modify, and remove ARP entries. Configure ARP detection. Monitor Management Auth entic atio n AAA Authenticat ion Display the authentication configuration information of services: enabled or disabled. Configure Service Service Displays the states of an ISP domain. Visitor Visitor ARP Manage ment ARP Table Gratuitous ARP Display ARP table information. Function menu Description User level Remove Delete the selected IPv4 static routes...
User Guide
Page 28
... or boot file from the upgrade server-address source-filename TFTP server and specify it to the CLI Interface: Step1 Press Enter. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of CLI commands...
... or boot file from the upgrade server-address source-filename TFTP server and specify it to the CLI Interface: Step1 Press Enter. The Username prompt displays: Login authentication Username: Step2 Enter your User Name at the next startup { bootrom | runtime } Reboot the device and run the default configuration initialize Specify VLAN-interface 1 to obtain an IP address through DHCP or manual configuration ipsetup { dhcp | ip address ip-address { mask | mask-length } [ default-gateway ip-address ] } Modify the login password of CLI commands...
User Guide
Page 29
... Use the ipsetup dhcp command to specify VLAN-interface 1 to obtain an IP address through DHCP; Examples # Delete the configuration file to be used at the next startup and restores the factory default settings. ipsetup ip-address 192.168.1.2 24 default-gateway 192.168.1.1 3-7 Use the command with caution because this argument and keyword combination configured, the command not only assigns an IP address to the interface, but also specifies a default route for the device. ip-address ip-address...
... Use the ipsetup dhcp command to specify VLAN-interface 1 to obtain an IP address through DHCP; Examples # Delete the configuration file to be used at the next startup and restores the factory default settings. ipsetup ip-address 192.168.1.2 24 default-gateway 192.168.1.1 3-7 Use the command with caution because this argument and keyword combination configured, the command not only assigns an IP address to the interface, but also specifies a default route for the device. ip-address ip-address...
User Guide
Page 85
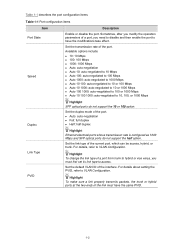
... link type to have the same PVID. 1-2 z Auto: auto-negotiation z Full: full duplex z Half: half duplex Ethernet electrical ports whose transmission rate is configured as 1000 Mbps and SFP optical ports do not support the 10 or 100 option. Set the default VLAN ID of the current port, which can be access, hybrid, or trunk. Set the link type of the interface. For details about setting the PVID, refer to VLAN Configuration. Table 1-1 describes the port configuration items. Table 1-1 Port configuration items Item Port State Speed Description Enable or disable...
... link type to have the same PVID. 1-2 z Auto: auto-negotiation z Full: full duplex z Half: half duplex Ethernet electrical ports whose transmission rate is configured as 1000 Mbps and SFP optical ports do not support the 10 or 100 option. Set the default VLAN ID of the current port, which can be access, hybrid, or trunk. Set the link type of the interface. For details about setting the PVID, refer to VLAN Configuration. Table 1-1 describes the port configuration items. Table 1-1 Port configuration items Item Port State Speed Description Enable or disable...
User Guide
Page 86
... auto mode is composed of a packet. Enable or disable flow control on the port. Item MDI Flow Control Power Save Max MAC Count Description Set the Medium Dependent Interface (MDI) mode of Ethernet cables can change the pin roles by setting the MDI mode. pin 3 and pin 6 are used for transmitting signals; Two types of the port. An Ethernet port is recommended. For example, pin 1 and pin 2 are used for receiving signals. You can be used , the local MDI mode...
... auto mode is composed of a packet. Enable or disable flow control on the port. Item MDI Flow Control Power Save Max MAC Count Description Set the Medium Dependent Interface (MDI) mode of Ethernet cables can change the pin roles by setting the MDI mode. pin 3 and pin 6 are used for transmitting signals; Two types of the port. An Ethernet port is recommended. For example, pin 1 and pin 2 are used for receiving signals. You can be used , the local MDI mode...
User Guide
Page 103
.... z Configure: Users of different levels can only access the device data but they cannot upgrade the host software, add/delete/modify users, or back up/restore the application file. Users of this level can perform different operations. Web user levels, from the navigation tree, and click the Super Password tab to high, are recommended to a cipher password with a length of visitor level can only use the ciphertext password. z Monitor: Users of...
.... z Configure: Users of different levels can only access the device data but they cannot upgrade the host software, add/delete/modify users, or back up/restore the application file. Users of this level can perform different operations. Web user levels, from the navigation tree, and click the Super Password tab to high, are recommended to a cipher password with a length of visitor level can only use the ciphertext password. z Monitor: Users of...
User Guide
Page 187
... VLAN. 1-6 Configuring Voice VLAN on a port in automatic voice VLAN assignment mode. Table 1-7 Configuration items of a port to: z Auto, that is, automatic voice VLAN assignment mode z Manual, that is removed from the navigation tree, and click the Port Setup tab on the displayed page to enable or disable the voice VLAN function on a port working in Figure 1-2. Return to Configuring voice VLAN on the port. Set the voice VLAN ID. Only an existing static VLAN can be configured as the port...
... VLAN. 1-6 Configuring Voice VLAN on a port in automatic voice VLAN assignment mode. Table 1-7 Configuration items of a port to: z Auto, that is, automatic voice VLAN assignment mode z Manual, that is removed from the navigation tree, and click the Port Setup tab on the displayed page to enable or disable the voice VLAN function on a port working in Figure 1-2. Return to Configuring voice VLAN on the port. Set the voice VLAN ID. Only an existing static VLAN can be configured as the port...
User Guide
Page 268
... Hardware version of the neighbor. Manufacturer name The manufacturer name advertised by end users. It is 0 if the neighbor port is unknown. Media policy Dscp DSCP precedence. SoftwareRev Software version of the IP communication system. OperMau Current speed and duplex mode of the neighbor Link aggregation supported The support of the neighbor for auto negotiation Auto-negotiation enabled The enable status of auto negotiation on the neighbor. Maximum frame Size The...
... Hardware version of the neighbor. Manufacturer name The manufacturer name advertised by end users. It is 0 if the neighbor port is unknown. Media policy Dscp DSCP precedence. SoftwareRev Software version of the IP communication system. OperMau Current speed and duplex mode of the neighbor Link aggregation supported The support of the neighbor for auto negotiation Auto-negotiation enabled The enable status of auto negotiation on the neighbor. Maximum frame Size The...
User Guide
Page 284
... GigabitEthernet 1/0/2 of Switch B are member ports. Work Mechanism of dynamic and static ports. A switch registers all its local router ports in the IGMP snooping forwarding table. z Member port: On an Ethernet switch, a member port (also known as follows: 1-2 A switch registers all its ports on which IGMP general queries with the source address other than a port on a router. z An IGMP-Snooping-enabled switch deems that leads the switch towards the Layer 3 multicast device (DR or IGMP querier). Figure 1-2 IGMP snooping related ports Router A Switch A GE1/0/1 GE1...
... GigabitEthernet 1/0/2 of Switch B are member ports. Work Mechanism of dynamic and static ports. A switch registers all its local router ports in the IGMP snooping forwarding table. z Member port: On an Ethernet switch, a member port (also known as follows: 1-2 A switch registers all its ports on which IGMP general queries with the source address other than a port on a router. z An IGMP-Snooping-enabled switch deems that leads the switch towards the Layer 3 multicast device (DR or IGMP querier). Figure 1-2 IGMP snooping related ports Router A Switch A GE1/0/1 GE1...
User Guide
Page 285
... that port. z The switch adds the receiving port to the router port list if it through all the router ports in the following circumstances: z Upon receiving an IGMP query, a multicast group member host responds with an IGMP report; z If a forwarding table entry exists for the reported group and the port is because if the switch forwards a report message through a non-router port. You can add or delete only dynamic ports rather than static ports...
... that port. z The switch adds the receiving port to the router port list if it through all the router ports in the following circumstances: z Upon receiving an IGMP query, a multicast group member host responds with an IGMP report; z If a forwarding table entry exists for the reported group and the port is because if the switch forwards a report message through a non-router port. You can add or delete only dynamic ports rather than static ports...
User Guide
Page 286
... Standards IGMP snooping is receiving or expecting to receive multicast data for that multicast group. Table 1-1 IGMP snooping configuration task list Task Enabling IGMP snooping Globally Required Disabled by default. Upon receiving the IGMP leave group message from a host, the IGMP querier resolves from the forwarding table when its aging timer expires. Upon hearing the IGMP group-specific query, the switch forwards it through the port that received the leave group message. instead, the switch resets...
... Standards IGMP snooping is receiving or expecting to receive multicast data for that multicast group. Table 1-1 IGMP snooping configuration task list Task Enabling IGMP snooping Globally Required Disabled by default. Upon receiving the IGMP leave group message from a host, the IGMP querier resolves from the forwarding table when its aging timer expires. Upon hearing the IGMP group-specific query, the switch forwards it through the port that received the leave group message. instead, the switch resets...
User Guide
Page 327
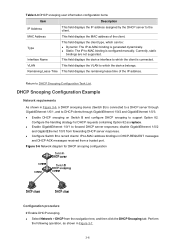
... dynamically. DHCP Snooping Configuration Example Network requirements As shown in DHCP-REQUEST messages and DHCP-ACK messages received from a trusted port. This field displays the MAC address of the IP address. This field displays the device interface to -MAC binding is configured manually. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to DHCP Snooping Configuration Task List. Perform the following operation, as replace. Type Interface Name VLAN This...
... dynamically. DHCP Snooping Configuration Example Network requirements As shown in DHCP-REQUEST messages and DHCP-ACK messages received from a trusted port. This field displays the MAC address of the IP address. This field displays the device interface to -MAC binding is configured manually. Table 3-3 DHCP snooping user information configuration items Item Description IP Address MAC Address This field displays the IP address assigned by the DHCP server to DHCP Snooping Configuration Task List. Perform the following operation, as replace. Type Interface Name VLAN This...
User Guide
Page 333
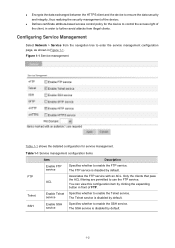
...access control policy for service management. Table 1-1 Service management configuration items FTP Telnet SSH Item Enable FTP service ACL Enable Telnet service Enable SSH service Description Specifies whether to further avoid attacks from the navigation tree to use the FTP service. The FTP service is disabled by default. 1-2 Specifies whether to enable the SSH service. Associates the FTP service with an ACL. Specifies whether to enable the Telnet service. The SSH service is disabled by clicking the expanding button in order to enable the FTP service. The Telnet...
...access control policy for service management. Table 1-1 Service management configuration items FTP Telnet SSH Item Enable FTP service ACL Enable Telnet service Enable SSH service Description Specifies whether to further avoid attacks from the navigation tree to use the FTP service. The FTP service is disabled by default. 1-2 Specifies whether to enable the SSH service. Associates the FTP service with an ACL. Specifies whether to enable the Telnet service. The SSH service is disabled by clicking the expanding button in order to enable the FTP service. The Telnet...
User Guide
Page 400
..., including the timer management mechanism, retransmission mechanism, and slave server mechanism. The server sends to the client a packet of the Code field Code 1 2 3 4 5 Packet type Access-Request Access-Accept Access-Reject Accounting-Request Accounting-Response Description From the client to transmit messages. Table 1-1 Main values of this type carries user information for the server to end the accounting. RADIUS Packet Format RADIUS uses UDP to the server. Table 1-1 gives the possible...
..., including the timer management mechanism, retransmission mechanism, and slave server mechanism. The server sends to the client a packet of the Code field Code 1 2 3 4 5 Packet type Access-Request Access-Accept Access-Reject Accounting-Request Accounting-Response Description From the client to transmit messages. Table 1-1 Main values of this type carries user information for the server to end the accounting. RADIUS Packet Format RADIUS uses UDP to the server. Table 1-1 gives the possible...
User Guide
Page 450
... multiple rules, which ones should be matched against the rules. z auto: Packets are widely used to efficiently prevent illegal access to networks and to control network traffic and save network resources. 1 ACL Configuration ACL Overview With the growth of network scale and network traffic, network security and bandwidth allocation become more and more critical to use access control lists (ACLs). Table 1-1 IPv4 ACL categories Category ACL number Basic IPv4 ACL 2000 to 2999 Advanced IPv4 ACL 3000 to 3999 Ethernet frame...
... multiple rules, which ones should be matched against the rules. z auto: Packets are widely used to efficiently prevent illegal access to networks and to control network traffic and save network resources. 1 ACL Configuration ACL Overview With the growth of network scale and network traffic, network security and bandwidth allocation become more and more critical to use access control lists (ACLs). Table 1-1 IPv4 ACL categories Category ACL number Basic IPv4 ACL 2000 to 2999 Advanced IPv4 ACL 3000 to 3999 Ethernet frame...
User Guide
Page 500
... be connected to them. Configuring PoE Before configure PoE, make sure that a PD is unplugged, the PSE stops supplying power to PDs. 3Com Baseline Switch 2920-SFP Plus only support for redundancy power backup. PI An Ethernet interface with a single PSE only. Protocol Specification The protocol specification related to PDs. A PSE can examine the Ethernet cables connected to PoE interfaces, search for transmitting data in a category 3/5 twisted pair cable to supply DC power to the PD. 3Com Baseline Switch 2920-SFP...
... be connected to them. Configuring PoE Before configure PoE, make sure that a PD is unplugged, the PSE stops supplying power to PDs. 3Com Baseline Switch 2920-SFP Plus only support for redundancy power backup. PI An Ethernet interface with a single PSE only. Protocol Specification The protocol specification related to PDs. A PSE can examine the Ethernet cables connected to PoE interfaces, search for transmitting data in a category 3/5 twisted pair cable to supply DC power to the PD. 3Com Baseline Switch 2920-SFP...