User Guide
Page 7
The ZyWALL icon is not an exact representation of your device. Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons. ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 300 User's Guide 7
The ZyWALL icon is not an exact representation of your device. Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons. ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 300 User's Guide 7
User Guide
Page 9
Contents Overview Contents Overview User's Guide ...31 Introducing the ZyWALL ...33 Features and Applications ...39 Web Configurator ...47 Installation Setup Wizard ...65 Quick Setup ...75 Configuration Basics ...93 Tutorials ...117 L2TP VPN Example ...... ...429 ALG ...435 IP/MAC Binding ...443 Authentication Policy ...449 Firewall ...457 IPSec VPN ...475 SSL VPN ...517 SSL User Screens ...531 SSL User Application Screens 541 SSL User File Sharing ...543 ZyWALL SecuExtender ...551 L2TP VPN ...555 Application Patrol ...559 Anti-Virus ...585 IDP ...601 ADP ...637 ZyWALL USG 300 User's Guide 9
Contents Overview Contents Overview User's Guide ...31 Introducing the ZyWALL ...33 Features and Applications ...39 Web Configurator ...47 Installation Setup Wizard ...65 Quick Setup ...75 Configuration Basics ...93 Tutorials ...117 L2TP VPN Example ...... ...429 ALG ...435 IP/MAC Binding ...443 Authentication Policy ...449 Firewall ...457 IPSec VPN ...475 SSL VPN ...517 SSL User Screens ...531 SSL User Application Screens 541 SSL User File Sharing ...543 ZyWALL SecuExtender ...551 L2TP VPN ...555 Application Patrol ...559 Anti-Virus ...585 IDP ...601 ADP ...637 ZyWALL USG 300 User's Guide 9
User Guide
Page 13
Policy ...107 6.5.14 Firewall ...107 6.5.15 IPSec VPN ...108 6.5.16 SSL VPN ...108 6.5.17 L2TP VPN ...109 6.5.18 Application ... HA ...111 6.6 Objects ...112 6.6.1 User/Group ...112 6.7 System ...113 6.7.1 DNS, WWW, SSH, TELNET, FTP, SNMP, Dial-in the ZyWALL 97 6.4 Packet Flow ...98 6.4.1 ZLD 2.20 Packet Flow Enhancements 98 6.4.2 Routing Table Checking Flow Enhancements 99 6.4.3 NAT Table Checking Flow 100 6.5 ......114 Chapter 7 Tutorials ...117 7.1 How to Configure Interfaces, Port Grouping, and Zones 117 7.1.1 Configure a WAN Ethernet Interface 118 ZyWALL USG 300 User's Guide 13
Policy ...107 6.5.14 Firewall ...107 6.5.15 IPSec VPN ...108 6.5.16 SSL VPN ...108 6.5.17 L2TP VPN ...109 6.5.18 Application ... HA ...111 6.6 Objects ...112 6.6.1 User/Group ...112 6.7 System ...113 6.7.1 DNS, WWW, SSH, TELNET, FTP, SNMP, Dial-in the ZyWALL 97 6.4 Packet Flow ...98 6.4.1 ZLD 2.20 Packet Flow Enhancements 98 6.4.2 Routing Table Checking Flow Enhancements 99 6.4.3 NAT Table Checking Flow 100 6.5 ......114 Chapter 7 Tutorials ...117 7.1 How to Configure Interfaces, Port Grouping, and Zones 117 7.1.1 Configure a WAN Ethernet Interface 118 ZyWALL USG 300 User's Guide 13
User Guide
Page 14
...7.7.3 Set Up User Authentication Using the RADIUS Server 148 7.7.4 Web Surfing Policies With Bandwidth Restrictions 150 7.7.5 Set Up MSN Policies 153 7.7.6 Set Up Firewall Rules 154 7.8 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 155 7.9 How to Use Endpoint Security and Authentication Policies 157...13.3 Setup a NAT Policy for the IPPBX 173 7.13.4 Set Up a WAN to DMZ Firewall Rule for SIP 174 7.13.5 Set Up a DMZ to LAN Firewall Rule for SIP 175 7.14 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 176 14 ZyWALL USG 300 User's Guide
...7.7.3 Set Up User Authentication Using the RADIUS Server 148 7.7.4 Web Surfing Policies With Bandwidth Restrictions 150 7.7.5 Set Up MSN Policies 153 7.7.6 Set Up Firewall Rules 154 7.8 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 155 7.9 How to Use Endpoint Security and Authentication Policies 157...13.3 Setup a NAT Policy for the IPPBX 173 7.13.4 Set Up a WAN to DMZ Firewall Rule for SIP 174 7.13.5 Set Up a DMZ to LAN Firewall Rule for SIP 175 7.14 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 176 14 ZyWALL USG 300 User's Guide
User Guide
Page 19
....1.2 What You Need to Know 450 23.2 Authentication Policy Screen 450 23.2.1 Adding Exceptional Services 452 23.2.2 Creating/Editing an Authentication Policy 453 Chapter 24 Firewall...457 24.1 Overview ...457 24.1.1 What You Can Do in this Chapter 457 ZyWALL USG 300 User's Guide 19
....1.2 What You Need to Know 450 23.2 Authentication Policy Screen 450 23.2.1 Adding Exceptional Services 452 23.2.2 Creating/Editing an Authentication Policy 453 Chapter 24 Firewall...457 24.1 Overview ...457 24.1.1 What You Can Do in this Chapter 457 ZyWALL USG 300 User's Guide 19
User Guide
Page 20
Table of Contents 24.1.2 What You Need to Know 458 24.1.3 Firewall Rule Example Applications 460 24.1.4 Firewall Rule Configuration Example 463 24.2 The Firewall Screen ...465 24.2.1 Configuring the Firewall Screen 466 24.2.2 The Firewall Add/Edit Screen 469 24.3 The Session Limit Screen 470 24.3.1 The Session Limit Add/Edit Screen 472 Chapter 25... Screens ...531 27.1 Overview ...531 27.1.1 What You Need to Know 531 27.2 Remote User Login ...532 27.3 The SSL VPN User Screens 537 20 ZyWALL USG 300 User's Guide
Table of Contents 24.1.2 What You Need to Know 458 24.1.3 Firewall Rule Example Applications 460 24.1.4 Firewall Rule Configuration Example 463 24.2 The Firewall Screen ...465 24.2.1 Configuring the Firewall Screen 466 24.2.2 The Firewall Add/Edit Screen 469 24.3 The Session Limit Screen 470 24.3.1 The Session Limit Add/Edit Screen 472 Chapter 25... Screens ...531 27.1 Overview ...531 27.1.1 What You Need to Know 531 27.2 Remote User Login ...532 27.3 The SSL VPN User Screens 537 20 ZyWALL USG 300 User's Guide
User Guide
Page 33
..., 2 is a comprehensive security device. The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. See Chapter 2 on an EIA standard size, 19-inch rack or in the rear. ZyWALL USG 300 User's Guide 33 In addition, the ZyWALL provides excellent throughput, making it...
..., 2 is a comprehensive security device. The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. See Chapter 2 on an EIA standard size, 19-inch rack or in the rear. ZyWALL USG 300 User's Guide 33 In addition, the ZyWALL provides excellent throughput, making it...
User Guide
Page 39
... zone, not by interface, port, or network. ZyWALL USG 300 User's Guide 39 High Availability To ensure the ZyWALL provides reliable, secure Internet access, set up one or more information about the features of the ZyWALL. It also provides bandwidth management, NAT, port forwarding...policy routing, DHCP server and many other powerful features. The ZyWALL also offers hub-and-spoke IPSec VPN. The rest of this section provides more of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention...
... zone, not by interface, port, or network. ZyWALL USG 300 User's Guide 39 High Availability To ensure the ZyWALL provides reliable, secure Internet access, set up one or more information about the features of the ZyWALL. It also provides bandwidth management, NAT, port forwarding...policy routing, DHCP server and many other powerful features. The ZyWALL also offers hub-and-spoke IPSec VPN. The rest of this section provides more of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention...
User Guide
Page 40
...from a pre-defined list. 40 ZyWALL USG 300 User's Guide It detects pattern-based attacks in another zone first. You can also create your own custom ADP rules. It can detect: • Anomalies based on the kinds of attacks that the ZyWALL can protect against an external database ...according to block or monitor, such as pornography or racial intolerance, from one zone is not allowed unless it is a stateful inspection firewall. The ZyWALL restricts access by a computer in order to check web sites against . Intrusion Detection and Prevention (IDP) IDP (Intrusion Detection and ...
...from a pre-defined list. 40 ZyWALL USG 300 User's Guide It detects pattern-based attacks in another zone first. You can also create your own custom ADP rules. It can detect: • Anomalies based on the kinds of attacks that the ZyWALL can protect against an external database ...according to block or monitor, such as pornography or racial intolerance, from one zone is not allowed unless it is a stateful inspection firewall. The ZyWALL restricts access by a computer in order to check web sites against . Intrusion Detection and Prevention (IDP) IDP (Intrusion Detection and ...
User Guide
Page 54
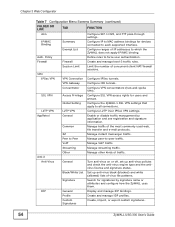
... them. VoIP Manage VoIP traffic. VPN Gateway Configure IKE tunnels. Common Manage traffic of virus file patterns. Firewall Firewall Create and manage level-3 traffic rules. Other Manage other kinds of concurrent client NAT/firewall sessions. Signature Search for users and groups. Concentrator Configure VPN concentrators (hub-and-spoke VPN). L2TP VPN L2TP ...and e-mail protocols. IDP General Display and manage IDP bindings. Profile Create and manage IDP profiles. Custom Signatures Create, import, or export custom signatures. 54 ZyWALL USG 300 User's Guide
... them. VoIP Manage VoIP traffic. VPN Gateway Configure IKE tunnels. Common Manage traffic of virus file patterns. Firewall Firewall Create and manage level-3 traffic rules. Other Manage other kinds of concurrent client NAT/firewall sessions. Signature Search for users and groups. Concentrator Configure VPN concentrators (hub-and-spoke VPN). L2TP VPN L2TP ...and e-mail protocols. IDP General Display and manage IDP bindings. Profile Create and manage IDP profiles. Custom Signatures Create, import, or export custom signatures. 54 ZyWALL USG 300 User's Guide
User Guide
Page 58
...'s link to go to open the Object Reference screen. Figure 19 Object Reference 58 ZyWALL USG 300 User's Guide Select the type of links to show which configuration settings reference the ldap-users user object (in this case the first firewall rule). Chapter 3 Web Configurator 3.3.3.2 Site Map Click Site MAP to see an overview...
...'s link to go to open the Object Reference screen. Figure 19 Object Reference 58 ZyWALL USG 300 User's Guide Select the type of links to show which configuration settings reference the ldap-users user object (in this case the first firewall rule). Chapter 3 Web Configurator 3.3.3.2 Site Map Click Site MAP to see an overview...
User Guide
Page 62
... a list of available entries displays next to create a new entry after the selected entry. Move To change an entry's position in order like the firewall for the most common table icons. For example, if you type 6, the entry you are descriptions for example), you typed. Table 10 Common Table ...click an entry to move the entry to the other. Activate To turn off an entry, select it and click Activate. In some lists 62 ZyWALL USG 300 User's Guide For those types of selected entries, you have icons for an example. Remove To remove an entry, select it directly in the ...
... a list of available entries displays next to create a new entry after the selected entry. Move To change an entry's position in order like the firewall for the most common table icons. For example, if you type 6, the entry you are descriptions for example), you typed. Table 10 Common Table ...click an entry to move the entry to the other. Activate To turn off an entry, select it and click Activate. In some lists 62 ZyWALL USG 300 User's Guide For those types of selected entries, you have icons for an example. Remove To remove an entry, select it directly in the ...
User Guide
Page 93
... reference when you want to configure many of the ZyWALL's features and settings. You use these ZyWALL USG 300 User's Guide 93 For example, if you configure various features in the ZyWALL. • Section 6.1 on page 93 introduces the ZyWALL's object-based configuration. • Section 6.2 on... address, subnet, or gateway. For example, if you create a schedule object, you change an object's settings, the ZyWALL automatically updates all the firewall, application patrol, content filter, and other features. You can have to help you configure the trunk. After you configure...
... reference when you want to configure many of the ZyWALL's features and settings. You use these ZyWALL USG 300 User's Guide 93 For example, if you configure various features in the ZyWALL. • Section 6.1 on page 93 introduces the ZyWALL's object-based configuration. • Section 6.2 on... address, subnet, or gateway. For example, if you create a schedule object, you change an object's settings, the ZyWALL automatically updates all the firewall, application patrol, content filter, and other features. You can have to help you configure the trunk. After you configure...
User Guide
Page 94
... list of zones, interfaces, and physical ports in a screen that use them. Use interfaces in configuring other features. 94 ZyWALL USG 300 User's Guide Figure 55 Zones, Interfaces, and Physical Ethernet Ports Zones Interfaces LAN WAN DMZ WLAN ge1 ge2 ge3 ge4 ge5 ... Port groups combine physical ports into interfaces. In configuration, you use the Configuration > Objects screens to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol. Interfaces (Ethernet, VLAN,...) Interfaces are logical entities that use interfaces and zones ...
... list of zones, interfaces, and physical ports in a screen that use them. Use interfaces in configuring other features. 94 ZyWALL USG 300 User's Guide Figure 55 Zones, Interfaces, and Physical Ethernet Ports Zones Interfaces LAN WAN DMZ WLAN ge1 ge2 ge3 ge4 ge5 ... Port groups combine physical ports into interfaces. In configuration, you use the Configuration > Objects screens to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol. Interfaces (Ethernet, VLAN,...) Interfaces are logical entities that use interfaces and zones ...
User Guide
Page 99
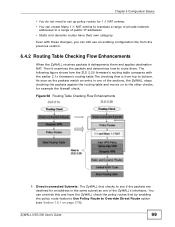
ZyWALL USG 300 User's Guide 99 Chapter 6 Configuration Basics • You do not need to set up policy routes ... an address in the same subnet as one of public IP addresses • Static and dynamic routes have the ZyWALL check the policy routes first by enabling the policy route feature's Use Policy Route to bottom. Even with the earlier...to a range of the ZyWALL's interfaces. You can still use an existing configuration file from top to Override Direct Route option (see Section 15.1 on to see if the packets are destined for example the firewall check. The following figure ...
ZyWALL USG 300 User's Guide 99 Chapter 6 Configuration Basics • You do not need to set up policy routes ... an address in the same subnet as one of public IP addresses • Static and dynamic routes have the ZyWALL check the policy routes first by enabling the policy route feature's Use Policy Route to bottom. Even with the earlier...to a range of the ZyWALL's interfaces. You can still use an existing configuration file from top to Override Direct Route option (see Section 15.1 on to see if the packets are destined for example the firewall check. The following figure ...
User Guide
Page 105
... which they run. Zones cannot overlap. Each interface and VPN tunnel can be assigned to the same zone as firewall rules and remote management. A zone is a group of interfaces and VPN tunnels. ZyWALL USG 300 User's Guide 105 Virtual interfaces are automatically assigned to at most one zone. MENU ITEM(S) Configuration > Network > DDNS PREREQUISITES...
... which they run. Zones cannot overlap. Each interface and VPN tunnel can be assigned to the same zone as firewall rules and remote management. A zone is a group of interfaces and VPN tunnels. ZyWALL USG 300 User's Guide 105 Virtual interfaces are automatically assigned to at most one zone. MENU ITEM(S) Configuration > Network > DDNS PREREQUISITES...
User Guide
Page 106
...readily available the next time one of the FTP server. It does check regular (through-ZyWALL) firewall rules. The ZyWALL will forward the packets received for the original IP address. 6 In Mapping Type, select...configure the NAT entry. Chapter 6 Configuration Basics The ZyWALL only checks regular (through-ZyWALL) firewall rules for packets that are redirected by HTTP redirect. The ZyWALL does not check to -ZyWALL firewall rules. You could configure a NAT rule to forwards... 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add an entry. 106 ZyWALL USG 300 User's Guide
...readily available the next time one of the FTP server. It does check regular (through-ZyWALL) firewall rules. The ZyWALL will forward the packets received for the original IP address. 6 In Mapping Type, select...configure the NAT entry. Chapter 6 Configuration Basics The ZyWALL only checks regular (through-ZyWALL) firewall rules for packets that are redirected by HTTP redirect. The ZyWALL does not check to -ZyWALL firewall rules. You could configure a NAT rule to forwards... 192.168.3.80. 1 Click Configuration > Network > HTTP Redirect. 2 Add an entry. 106 ZyWALL USG 300 User's Guide
User Guide
Page 107
... traffic between or within zones. You can also configure the firewall to control who can access the network. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), services, service groups ZyWALL USG 300 User's Guide 107 You can configure firewall rules based on the ZyWALL. MENU ITEM(S) Configuration > Auth.
... traffic between or within zones. You can also configure the firewall to control who can access the network. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), services, service groups ZyWALL USG 300 User's Guide 107 You can configure firewall rules based on the ZyWALL. MENU ITEM(S) Configuration > Auth.
User Guide
Page 108
... for assigning to clients, DNS and WINS server addresses), to -ZyWALL firewall, firewall WHERE USED Policy routes, zones, L2TP VPN Example: See Chapter 7 on the LAN can also use the Quick Setup VPN Setup wizard. Interfaces, certificates (authentication), authentication methods PREREQUISITES (extended authentication), addresses (local network, remote network, NAT), to -ZyWALL firewall, firewall 108 ZyWALL USG 300 User's Guide
... for assigning to clients, DNS and WINS server addresses), to -ZyWALL firewall, firewall WHERE USED Policy routes, zones, L2TP VPN Example: See Chapter 7 on the LAN can also use the Quick Setup VPN Setup wizard. Interfaces, certificates (authentication), authentication methods PREREQUISITES (extended authentication), addresses (local network, remote network, NAT), to -ZyWALL firewall, firewall 108 ZyWALL USG 300 User's Guide
User Guide
Page 109
...amounts of the wizards. ZyWALL USG 300 User's Guide 109 MENU ITEM(S) Configuration > VPN > L2TP VPN PREREQUISITES Interfaces, IPSec VPN connection, certificates (authentication), authentication methods (extended authentication), addresses (local network, remote network, NAT, IP pool for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED The IPSec VPN...WHERE USED Policy routes, zones Example: See Chapter 7 on page 185. 6.5.18 Application Patrol Use application patrol to control which services through the ZyWALL (and when they can do so).
...amounts of the wizards. ZyWALL USG 300 User's Guide 109 MENU ITEM(S) Configuration > VPN > L2TP VPN PREREQUISITES Interfaces, IPSec VPN connection, certificates (authentication), authentication methods (extended authentication), addresses (local network, remote network, NAT, IP pool for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED The IPSec VPN...WHERE USED Policy routes, zones Example: See Chapter 7 on page 185. 6.5.18 Application Patrol Use application patrol to control which services through the ZyWALL (and when they can do so).