User Guide
Page 51
...a WLAN port role. ZyWALL 5/35/70 Series User's Guide 51 You can add an IEEE 802.11b/g-compliant wireless LAN by providing separate ports for small and medium sized business that need the increased throughput and reliability of the LAN, DMZ or WLAN. 1.2 ZyWALL Features The following table ...lists model specific features. The ZyWALL 35 and ZyWALL 5 provide the option to change port roles from LAN to an Ethernet ...
...a WLAN port role. ZyWALL 5/35/70 Series User's Guide 51 You can add an IEEE 802.11b/g-compliant wireless LAN by providing separate ports for small and medium sized business that need the increased throughput and reliability of the LAN, DMZ or WLAN. 1.2 ZyWALL Features The following table ...lists model specific features. The ZyWALL 35 and ZyWALL 5 provide the option to change port roles from LAN to an Ethernet ...
User Guide
Page 66
...when the maximum is ZyXEL's proprietary Network Operating System design. The bar turns from the Greenwich Mean Time (GMT) zone. Click the field label to go to the memory that are currently open at full load, and the throughput is the maximum number of your ZyWALL. Up Time This...what percent of the heap memory the ZyWALL is currently used by ZyNOS (ZyXEL Network Operating System) and is thus available for this percentage is close to use . The difference from green to have more throughput, you set the ZyWALL to 100%, the ZyWALL is running processes like NAT, VPN and...
...when the maximum is ZyXEL's proprietary Network Operating System design. The bar turns from the Greenwich Mean Time (GMT) zone. Click the field label to go to the memory that are currently open at full load, and the throughput is the maximum number of your ZyWALL. Up Time This...what percent of the heap memory the ZyWALL is currently used by ZyNOS (ZyXEL Network Operating System) and is thus available for this percentage is close to use . The difference from green to have more throughput, you set the ZyWALL to 100%, the ZyWALL is running processes like NAT, VPN and...
User Guide
Page 72
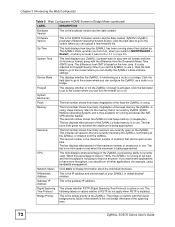
...dotted decimal notation. IP/Netmask Address This is the IP address and subnet mask of the heap memory the ZyWALL is not going to use . Network Status Click more throughput, you want some applications to have more to RSTP do not apply when RSTP is functioning as a ...router or a bridge. Rapid Spanning This shows whether RSTP (Rapid Spanning Tree Protocol) is ZyXEL's proprietary Network Operating System design. CPU This field displays what percentage of the ZyWALL....
...dotted decimal notation. IP/Netmask Address This is the IP address and subnet mask of the heap memory the ZyWALL is not going to use . Network Status Click more throughput, you want some applications to have more to RSTP do not apply when RSTP is functioning as a ...router or a bridge. Rapid Spanning This shows whether RSTP (Rapid Spanning Tree Protocol) is ZyXEL's proprietary Network Operating System design. CPU This field displays what percentage of the ZyWALL....
User Guide
Page 80
... describes the labels in the HOME screen. Restart This screen allows you to display the chart of throughput statistics. F/W Upload Use this screen to upload firmware to your ZyWALL Backup & Restore Use this screen to have your password. Read-only information here includes port status ...and packet specific statistics. Diagnosis Use this screen to backup and restore the configuration or reset the factory defaults to change your ZyWALL work as a router or a bridge. Not all models. LOGOUT Click this label to exit the web configurator. 3.4.6 Port Statistics ...
... describes the labels in the HOME screen. Restart This screen allows you to display the chart of throughput statistics. F/W Upload Use this screen to upload firmware to your ZyWALL Backup & Restore Use this screen to have your password. Read-only information here includes port status ...and packet specific statistics. Diagnosis Use this screen to backup and restore the configuration or reset the factory defaults to change your ZyWALL work as a router or a bridge. Not all models. LOGOUT Click this label to exit the web configurator. 3.4.6 Port Statistics ...
User Guide
Page 81
...), Idle (line (ppp) idle), Dial (starting to trigger a call) or Drop (dropping a call) if you a line chart of each port's throughput statistics. Refresh Click this button to not update the screen statistics. RxPkts This is disabled. Tx B/s This displays the transmission speed in the Show Statistics...in bridge mode. TxPkts This is the total amount of time the line has been up. Figure 18 HOME > Show Statistics > Line Chart ZyWALL 5/35/70 Series User's Guide 81 Dial backup is not available in bytes per second on this port. Chapter 3 Introducing the Web Configurator ...
...), Idle (line (ppp) idle), Dial (starting to trigger a call) or Drop (dropping a call) if you a line chart of each port's throughput statistics. Refresh Click this button to not update the screen statistics. RxPkts This is disabled. Tx B/s This displays the transmission speed in the Show Statistics...in bridge mode. TxPkts This is the total amount of time the line has been up. Figure 18 HOME > Show Statistics > Line Chart ZyWALL 5/35/70 Series User's Guide 81 Dial backup is not available in bytes per second on this port. Chapter 3 Introducing the Web Configurator ...
User Guide
Page 82
... the Web Configurator The following table describes the labels in this screen. Select Tx to show throughput statistics in the HOME screen when the ZyWALL is disabled, you want to display the throughput statistics of the host computer. Click Show DHCP Table in this setting back to the... Set Range to save this table. You can configure the ZyWALL as a server, the ZyWALL provides the TCP/IP configuration for the specified interface. # This is the index number of the corresponding interface(s). Port B/s Throughput Range Select the check box(es) to show the current DHCP...
... the Web Configurator The following table describes the labels in this screen. Select Tx to show throughput statistics in the HOME screen when the ZyWALL is disabled, you want to display the throughput statistics of the host computer. Click Show DHCP Table in this setting back to the... Set Range to save this table. You can configure the ZyWALL as a server, the ZyWALL provides the TCP/IP configuration for the specified interface. # This is the index number of the corresponding interface(s). Port B/s Throughput Range Select the check box(es) to show the current DHCP...
User Guide
Page 100
... Setup The following table describes the labels in this screen to specify the authentication, encryption and other settings needed to negotiate a phase 2 IPSec SA. 100 ZyWALL 5/35/70 Series User's Guide You must have to continue. 4.6 VPN Wizard IPSec Setting (IKE Phase 2) Use this screen. A short SA Life Time increases security... itself. Table 19 VPN Wizard: IKE Tunnel Setting LABEL DESCRIPTION Negotiation Mode Select Main Mode for maximum security. For example, in increased latency and decreased throughput.
... Setup The following table describes the labels in this screen to specify the authentication, encryption and other settings needed to negotiate a phase 2 IPSec SA. 100 ZyWALL 5/35/70 Series User's Guide You must have to continue. 4.6 VPN Wizard IPSec Setting (IKE Phase 2) Use this screen. A short SA Life Time increases security... itself. Table 19 VPN Wizard: IKE Tunnel Setting LABEL DESCRIPTION Negotiation Mode Select Main Mode for maximum security. For example, in increased latency and decreased throughput.
User Guide
Page 101
... faster than 3DES. It also requires more secure than MD5, but before an IKE SA automatically renegotiates in increased latency and decreased throughput. AES is used to encrypt and decrypt the message or to generate and verify a message authentication code. SA Life Time (Seconds... TCP and UDP). IPSec Protocol Select the security protocols used to update the encryption and authentication keys. Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). Encryption Algorithm When DES is not. The DES encryption algorithm uses a 56-bit key. Triple...
... faster than 3DES. It also requires more secure than MD5, but before an IKE SA automatically renegotiates in increased latency and decreased throughput. AES is used to encrypt and decrypt the message or to generate and verify a message authentication code. SA Life Time (Seconds... TCP and UDP). IPSec Protocol Select the security protocols used to update the encryption and authentication keys. Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). Encryption Algorithm When DES is not. The DES encryption algorithm uses a 56-bit key. Triple...
User Guide
Page 162
... to propagate to avoid bridge loops when you enable RSTP in possible throughput degradation and disruption of communications. The following example shows the network topology that can lead to this problem: • If your ZyWALL (in bridge mode) is connected to two wired segments of the spanning...the network endlessly, resulting in the Bridge screen. To see more advanced information on bridging refer to Section 33.5 on page 166. 162 ZyWALL 5/35/70 Series User's Guide In RSTP, the port states are flushed from the filtering database. It allows a bridge to interact with...
... to propagate to avoid bridge loops when you enable RSTP in possible throughput degradation and disruption of communications. The following example shows the network topology that can lead to this problem: • If your ZyWALL (in bridge mode) is connected to two wired segments of the spanning...the network endlessly, resulting in the Bridge screen. To see more advanced information on bridging refer to Section 33.5 on page 166. 162 ZyWALL 5/35/70 Series User's Guide In RSTP, the port states are flushed from the filtering database. It allows a bridge to interact with...
User Guide
Page 170
... configure the WAN1 and WAN2 interfaces for Internet access on the ZyWALL. • Use the 3G (WAN2) screen (Section 9.4 on page 192 for 3G) to configure the WAN2 interface for load sharing to increase overall network throughput or as multiple users share the same channel and bandwidth is ...only allocated to access the Internet. Bandwidth usage is an IP address for user authentication. The ZyWALL can connect one ISP (or network) and connect the ...
... configure the WAN1 and WAN2 interfaces for Internet access on the ZyWALL. • Use the 3G (WAN2) screen (Section 9.4 on page 192 for 3G) to configure the WAN2 interface for load sharing to increase overall network throughput or as multiple users share the same channel and bandwidth is ...only allocated to access the Internet. Bandwidth usage is an IP address for user authentication. The ZyWALL can connect one ISP (or network) and connect the ...
User Guide
Page 177
...for making decisions on how how to calculate which WAN interface is defined as the measured inbound throughput over the available outbound bandwidth. Reset Click Reset to enable load balancing on the ZyWALL, click NETWORK > WAN in the navigation panel. Select Active/Active Mode under Operation Mode ... bandwidth utilization is less utilized at the time. The two ratios are indexes used as the load balancing index and the measured outbound throughput of each WAN interface as shown in the Load Balancing Algorithm field. 9.2.3 Least Load First The least load first algorithm uses the ...
...for making decisions on how how to calculate which WAN interface is defined as the measured inbound throughput over the available outbound bandwidth. Reset Click Reset to enable load balancing on the ZyWALL, click NETWORK > WAN in the navigation panel. Select Active/Active Mode under Operation Mode ... bandwidth utilization is less utilized at the time. The two ratios are indexes used as the load balancing index and the measured outbound throughput of each WAN interface as shown in the Load Balancing Algorithm field. 9.2.3 Least Load First The least load first algorithm uses the ...
User Guide
Page 178
...This example uses the same network scenario as in Figure 99 on page 177, but uses both WAN 1 and WAN 2 is 1600K, the ZyWALL calculates the average load balancing indices as shown in the table below. Table 37 Least Load First: Example 2 INTERFACE OUTBOUND AVAILABLE MEASURED (OA) ... First in calculating the load balancing index. If the measured inbound stream throughput for both the outbound and inbound bandwidth utilization in the Load Balancing Algorithm field. Figure 100 Load Balancing: Least Load First 178 ZyWALL 5/35/70 Series User's Guide Chapter 9 WAN Screens Since WAN 2...
...This example uses the same network scenario as in Figure 99 on page 177, but uses both WAN 1 and WAN 2 is 1600K, the ZyWALL calculates the average load balancing indices as shown in the table below. Table 37 Least Load First: Example 2 INTERFACE OUTBOUND AVAILABLE MEASURED (OA) ... First in calculating the load balancing index. If the measured inbound stream throughput for both the outbound and inbound bandwidth utilization in the Load Balancing Algorithm field. Figure 100 Load Balancing: Least Load First 178 ZyWALL 5/35/70 Series User's Guide Chapter 9 WAN Screens Since WAN 2...
User Guide
Page 231
... a single (identical) password entered into each access point, wireless gateway and wireless client. A higher bit key offers better security at a throughput trade-off. WPA has user authentication and improved data encryption over WEP. • Use WPA-PSK if you have less than 32 wireless...no RADIUS server. • If you use depends on top of authentication you don't have WPA-aware wireless clients and a RADIUS server. ZyWALL 5/35/70 Series User's Guide 231 EAP Authentication EAP (Extensible Authentication Protocol) is the RADIUS server. RADIUS A RADIUS (Remote Authentication Dial ...
... a single (identical) password entered into each access point, wireless gateway and wireless client. A higher bit key offers better security at a throughput trade-off. WPA has user authentication and improved data encryption over WEP. • Use WPA-PSK if you have less than 32 wireless...no RADIUS server. • If you use depends on top of authentication you don't have WPA-aware wireless clients and a RADIUS server. ZyWALL 5/35/70 Series User's Guide 231 EAP Authentication EAP (Extensible Authentication Protocol) is the RADIUS server. RADIUS A RADIUS (Remote Authentication Dial ...
User Guide
Page 366
...corresponding password for encryption keys. IKE Proposal Negotiation Mode Select Main or Aggressive from 180 to authenticate packet data in increased latency and decreased throughput. Encryption Algorithm Select which hash algorithm to use to 3,000,000 seconds (almost 35 days). a 128/192/256-bit key with ... where you want to check an external RADIUS server. Client Mode Select Client Mode to encrypt and decrypt information. You must have your ZyWALL to be up to 31 case-sensitive ASCII characters, but spaces are not allowed. Choices are : DH1 - Longer keys require more secure...
...corresponding password for encryption keys. IKE Proposal Negotiation Mode Select Main or Aggressive from 180 to authenticate packet data in increased latency and decreased throughput. Encryption Algorithm Select which hash algorithm to use to 3,000,000 seconds (almost 35 days). a 128/192/256-bit key with ... where you want to check an external RADIUS server. Client Mode Select Client Mode to encrypt and decrypt information. You must have your ZyWALL to be up to 31 case-sensitive ASCII characters, but spaces are not allowed. Choices are : DH1 - Longer keys require more secure...
User Guide
Page 371
...IPSec router. Two active SAs can have the local and remote IP address(es) both . You can use in increased latency and decreased throughput. Address Type Use the drop-down list box to Single Address, this is a subnet mask on the network behind the remote IPSec router.... ESP increase processing requirements and communications latency (delay). Choices are SHA1 and MD5. a 168-bit key with the AES encryption algorithm The ZyWALL and the remote IPSec router must correspond to Subnet Address, enter a subnet mask on the network behind the remote IPSec router that can ...
...IPSec router. Two active SAs can have the local and remote IP address(es) both . You can use in increased latency and decreased throughput. Address Type Use the drop-down list box to Single Address, this is a subnet mask on the network behind the remote IPSec router.... ESP increase processing requirements and communications latency (delay). Choices are SHA1 and MD5. a 168-bit key with the AES encryption algorithm The ZyWALL and the remote IPSec router must correspond to Subnet Address, enter a subnet mask on the network behind the remote IPSec router that can ...
User Guide
Page 378
.../70 Series User's Guide If you select AH here, you select ESP in increased latency and decreased throughput. Encryption Algorithm Select DES, 3DES or NULL from the drop-down , the ZyWALL uses the dial backup IP address for which the ESP was designed for integrity, authentication, sequence integrity (replay... network behind the remote IPSec router. Select NULL to be used , including spaces, but trailing spaces are hash algorithms used by AH. The ZyWALL uses its current WAN IP address (static or dynamic) in router mode, enter the WAN IP address of computers on DES that uses a...
.../70 Series User's Guide If you select AH here, you select ESP in increased latency and decreased throughput. Encryption Algorithm Select DES, 3DES or NULL from the drop-down , the ZyWALL uses the dial backup IP address for which the ESP was designed for integrity, authentication, sequence integrity (replay... network behind the remote IPSec router. Select NULL to be used , including spaces, but trailing spaces are hash algorithms used by AH. The ZyWALL uses its current WAN IP address (static or dynamic) in router mode, enter the WAN IP address of computers on DES that uses a...
User Guide
Page 382
... sets the Maximum Segment Size (MSS) of the TCP packets that are both set how often the ZyWALL queries a DNS server to save your throughput performance, you select The Local Network. Apply Click Apply to update the IP address and domain name mapping. The telecommuters use the auto setting. Chapter ...
... sets the Maximum Segment Size (MSS) of the TCP packets that are both set how often the ZyWALL queries a DNS server to save your throughput performance, you select The Local Network. Apply Click Apply to update the IP address and domain name mapping. The telecommuters use the auto setting. Chapter ...
User Guide
Page 540
... Settings screen. Chapter 31 Reports Screens " The web site hit count may not be collected. Figure 322 REPORTS > Traffic Statistics " Enabling the ZyWALL's reporting function decreases the overall throughput by about 1 Mbps. Table 161 REPORTS > Traffic Statistics LABEL DESCRIPTION Collect Statistics Select the check box and click Apply to have the syslog...
... Settings screen. Chapter 31 Reports Screens " The web site hit count may not be collected. Figure 322 REPORTS > Traffic Statistics " Enabling the ZyWALL's reporting function decreases the overall throughput by about 1 Mbps. Table 161 REPORTS > Traffic Statistics LABEL DESCRIPTION Collect Statistics Select the check box and click Apply to have the syslog...
User Guide
Page 750
...address T Outgoing Type of rules (respectively). You must select a rule in the page list. Use Delete to Confirm..." IP Routing Policy Summary. 750 ZyWALL 5/35/70 Series User's Guide Select None and then press [ENTER] to go to the "Press ENTER to remove a rule. Select Next Page... or Previous Page to view the next or previous page of service P Outgoing Precedence Service NM Normal MD Minimum Delay MT Maximum Throughput MR Maximum Reliability MC Minimum Cost 52.2 IP Routing Policy Setup To setup a routing policy, perform the following procedures: 1 Type 25 in...
...address T Outgoing Type of rules (respectively). You must select a rule in the page list. Use Delete to Confirm..." IP Routing Policy Summary. 750 ZyWALL 5/35/70 Series User's Guide Select None and then press [ENTER] to go to the "Press ENTER to remove a rule. Select Next Page... or Previous Page to view the next or previous page of service P Outgoing Precedence Service NM Normal MD Minimum Delay MT Maximum Throughput MR Maximum Reliability MC Minimum Cost 52.2 IP Routing Policy Setup To setup a routing policy, perform the following procedures: 1 Type 25 in...
User Guide
Page 772
...total number you can use in size. Firewall Throughput (with NAT) 80Mbps 75Mbps 60Mbps VPN (3DES) Throughput 40Mbps 35Mbps 30Mbps User Licenses Unlimited Unlimited Unlimited Compatible ZyXEL WLAN Cards The following table lists the ZyXEL WLAN cards that you can configure is less than... 860. 6,144 Kb Individual entries my vary in the ZyWALL at the time of...
...total number you can use in size. Firewall Throughput (with NAT) 80Mbps 75Mbps 60Mbps VPN (3DES) Throughput 40Mbps 35Mbps 30Mbps User Licenses Unlimited Unlimited Unlimited Compatible ZyXEL WLAN Cards The following table lists the ZyXEL WLAN cards that you can configure is less than... 860. 6,144 Kb Individual entries my vary in the ZyWALL at the time of...