User Guide
Page 7
...Know Your ZyWALL 45 Introducing the Web Configurator 49 Wizard Setup ...67 Tutorials ...87 Registration Screens ...125 Network ...129 LAN Screens ...131 Bridge Screens ...143 WAN Screens ...151 DMZ Screens ...171 Wireless LAN Screens ...183 Security ...193 Firewall Screens ......Network Address Translation (NAT) Screens 331 Static Route Screens ...347 Bandwidth Management Screens 351 DNS Screens ...365 Remote Management Screens 377 UPnP Screens ...397 Custom Application Screen ...407 ALG Screen ...409 Logs and Maintenance ...415 Logs Screens ...417 Maintenance Screens ...447 ZyWALL 2 Plus...
...Know Your ZyWALL 45 Introducing the Web Configurator 49 Wizard Setup ...67 Tutorials ...87 Registration Screens ...125 Network ...129 LAN Screens ...131 Bridge Screens ...143 WAN Screens ...151 DMZ Screens ...171 Wireless LAN Screens ...183 Security ...193 Firewall Screens ......Network Address Translation (NAT) Screens 331 Static Route Screens ...347 Bandwidth Management Screens 351 DNS Screens ...365 Remote Management Screens 377 UPnP Screens ...397 Custom Application Screen ...407 ALG Screen ...409 Logs and Maintenance ...415 Logs Screens ...417 Maintenance Screens ...447 ZyWALL 2 Plus...
User Guide
Page 10
... Firewall 105 4.2.6 Testing the Connections 112 4.3 Using NAT with Multiple Game Players 112 4.4 How to Manage the ZyWALL's Bandwidth 113 4.4.1 Example Parameters and Scenario 113 4.4.2 Configuring Bandwidth Management Rules 114 4.5 Configuring Content Filtering 118 4.5.1 Enable Content Filtering 118 4.5.2 Block Categories of Web Content 119 4.5.3 Assign Bob's Computer a Specific IP Address 121 10 ZyWALL 2 Plus...
... Firewall 105 4.2.6 Testing the Connections 112 4.3 Using NAT with Multiple Game Players 112 4.4 How to Manage the ZyWALL's Bandwidth 113 4.4.1 Example Parameters and Scenario 113 4.4.2 Configuring Bandwidth Management Rules 114 4.5 Configuring Content Filtering 118 4.5.1 Enable Content Filtering 118 4.5.2 Block Categories of Web Content 119 4.5.3 Assign Bob's Computer a Specific IP Address 121 10 ZyWALL 2 Plus...
User Guide
Page 25
...25 Internet Access Wizard: Activated Services 77 Figure 26 VPN Wizard: Gateway Setting 78 Figure 27 VPN Wizard: Network Setting 79 Figure 28 VPN Wizard: IKE Tunnel Setting 80 Figure 29 VPN Wizard: IPSec Setting ...82 Figure ...SECURITY > VPN > VPN Rules (IKE 88 Figure 34 SECURITY > VPN > VPN Rules (IKE)> Add Gateway Policy 89 Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 90 Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network Policy 91 Figure 37 SECURITY > FIREWALL > Rule Summary 92 Figure 38 SECURITY > FIREWALL > Rule Summary > Edit: Allow 93 ZyWALL 2 Plus...
...25 Internet Access Wizard: Activated Services 77 Figure 26 VPN Wizard: Gateway Setting 78 Figure 27 VPN Wizard: Network Setting 79 Figure 28 VPN Wizard: IKE Tunnel Setting 80 Figure 29 VPN Wizard: IPSec Setting ...82 Figure ...SECURITY > VPN > VPN Rules (IKE 88 Figure 34 SECURITY > VPN > VPN Rules (IKE)> Add Gateway Policy 89 Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 90 Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network Policy 91 Figure 37 SECURITY > FIREWALL > Rule Summary 92 Figure 38 SECURITY > FIREWALL > Rule Summary > Edit: Allow 93 ZyWALL 2 Plus...
User Guide
Page 28
... 126 NETWORK > WLAN > Port Roles: Change Complete 192 Figure 127 Default Firewall Action ...195 Figure 128 Blocking All LAN to WAN IRC Traffic Example 197 Figure 129 Limited LAN to WAN IRC Traffic Example 198 Figure 130 SECURITY > FIREWALL > Default Rule (Router Mode 199 Figure 131 SECURITY > FIREWALL > Default Rule (Bridge Mode 201 Figure 132 SECURITY > FIREWALL > Rule... Global Report Screen Example 249 Figure 165 Requested URLs Example 250 Figure 166 Web Page Review Process Screen 251 Figure 167 VPN: Example ...253 28 ZyWALL 2 Plus User's Guide
... 126 NETWORK > WLAN > Port Roles: Change Complete 192 Figure 127 Default Firewall Action ...195 Figure 128 Blocking All LAN to WAN IRC Traffic Example 197 Figure 129 Limited LAN to WAN IRC Traffic Example 198 Figure 130 SECURITY > FIREWALL > Default Rule (Router Mode 199 Figure 131 SECURITY > FIREWALL > Default Rule (Bridge Mode 201 Figure 132 SECURITY > FIREWALL > Rule... Global Report Screen Example 249 Figure 165 Requested URLs Example 250 Figure 166 Web Page Review Process Screen 251 Figure 167 VPN: Example ...253 28 ZyWALL 2 Plus User's Guide
User Guide
Page 38
... Table 45 NETWORK > WLAN > Port Roles 192 Table 46 Blocking All LAN to WAN IRC Traffic Example 197 Table 47 Limited LAN to WAN IRC Traffic Example 198 Table 48 SECURITY > FIREWALL > Default Rule (Router Mode 199 Table 49 SECURITY > FIREWALL > Default Rule (Bridge Mode 201 Table 50 SECURITY > FIREWALL > Rule Summary 203 Table 51 SECURITY > FIREWALL > Rule Summary...
... Table 45 NETWORK > WLAN > Port Roles 192 Table 46 Blocking All LAN to WAN IRC Traffic Example 197 Table 47 Limited LAN to WAN IRC Traffic Example 198 Table 48 SECURITY > FIREWALL > Default Rule (Router Mode 199 Table 49 SECURITY > FIREWALL > Default Rule (Bridge Mode 201 Table 50 SECURITY > FIREWALL > Rule Summary 203 Table 51 SECURITY > FIREWALL > Rule Summary...
User Guide
Page 45
.... ZyWALL 2 Plus User's Guide 45 You can add an IEEE 802.11a/b/g-compliant wireless LAN by providing separate ports for the ZyWALL Here are some examples of the ZyWALL. 1.1 ZyWALL Internet Security Appliance Overview The ZyWALL is loaded with security features including VPN, firewall, content filtering and certificates. The ZyWALL guarantees not only high speed Internet access, but secure internal network protection...
.... ZyWALL 2 Plus User's Guide 45 You can add an IEEE 802.11a/b/g-compliant wireless LAN by providing separate ports for the ZyWALL Here are some examples of the ZyWALL. 1.1 ZyWALL Internet Security Appliance Overview The ZyWALL is loaded with security features including VPN, firewall, content filtering and certificates. The ZyWALL guarantees not only high speed Internet access, but secure internal network protection...
User Guide
Page 55
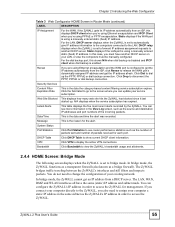
... numbers of your service subscription. In bridge mode, the ZyWALL functions as a transparent firewall (also known as the ZyWALL's IP address in order to assign your LAN, or ...based content filtering service subscription expires. The ZyWALL bridges traffic traveling between the ZyWALL's interfaces and still filters and inspects packets. Security Services Content Filter Expiration Date This is the...bridge mode. You can update your existing network. ZyWALL 2 Plus User's Guide 55 Web Site Blocked This displays how many web site hits the ZyWALL has blocked since it last started up...
... numbers of your service subscription. In bridge mode, the ZyWALL functions as a transparent firewall (also known as the ZyWALL's IP address in order to assign your LAN, or ...based content filtering service subscription expires. The ZyWALL bridges traffic traveling between the ZyWALL's interfaces and still filters and inspects packets. Security Services Content Filter Expiration Date This is the...bridge mode. You can update your existing network. ZyWALL 2 Plus User's Guide 55 Web Site Blocked This displays how many web site hits the ZyWALL has blocked since it last started up...
User Guide
Page 60
... view and manage the list of the directory servers. 60 ZyWALL 2 Plus User's Guide Chapter 2 Introducing the Web Configurator Table 6 ... the ZyWALL. Threshold Use this screen to configure the threshold for external database content filtering and view reports. SECURITY FIREWALL Default ...Rule Use this screen to apply the rule Rule Summary This screen shows a summary of certificates and manage certificates and certification requests. Port Roles Use this screen to activate/deactivate the firewall and the direction of network...
... view and manage the list of the directory servers. 60 ZyWALL 2 Plus User's Guide Chapter 2 Introducing the Web Configurator Table 6 ... the ZyWALL. Threshold Use this screen to configure the threshold for external database content filtering and view reports. SECURITY FIREWALL Default ...Rule Use this screen to apply the rule Rule Summary This screen shows a summary of certificates and manage certificates and certification requests. Port Roles Use this screen to activate/deactivate the firewall and the direction of network...
User Guide
Page 87
...FTP traffic to come from the ZyWALL's VPN tunnels. Furthermore, you can configure firewall rules that allow the network behind device B to access your LAN FTP server through a VPN tunnel (not other remote networks that only the network behind device A. The ZyWALL applies the security settings to the FTP server, you...with IP address 192.168.1.4 behind device B can apply the firewall and content filtering to the traffic going to or from VPN tunnels to the FTP server. You have a LAN FTP server with the ZyWALL). ZyWALL 2 Plus User's Guide 87 Take the following examples show how you ...
...FTP traffic to come from the ZyWALL's VPN tunnels. Furthermore, you can configure firewall rules that allow the network behind device B to access your LAN FTP server through a VPN tunnel (not other remote networks that only the network behind device A. The ZyWALL applies the security settings to the FTP server, you...with IP address 192.168.1.4 behind device B can apply the firewall and content filtering to the traffic going to or from VPN tunnels to the FTP server. You have a LAN FTP server with the ZyWALL). ZyWALL 2 Plus User's Guide 87 Take the following examples show how you ...
User Guide
Page 88
Configure the fields that are circled as follows and click Apply. 88 ZyWALL 2 Plus User's Guide You would also have to configure a corresponding rule on device A to let the network behind B access the FTP server. Figure 33 SECURITY > VPN > VPN Rules (IKE) 2 Use this screen to set up the connection between the routers. Click the Add Gateway Policy icon. Chapter 4 Tutorials Figure 32 Firewall Rule for VPN 4.1.2 Configuring the VPN Rule This section shows how to configure a VPN rule on device B. 1 Click Security > VPN to open the following screen.
Configure the fields that are circled as follows and click Apply. 88 ZyWALL 2 Plus User's Guide You would also have to configure a corresponding rule on device A to let the network behind B access the FTP server. Figure 33 SECURITY > VPN > VPN Rules (IKE) 2 Use this screen to set up the connection between the routers. Click the Add Gateway Policy icon. Chapter 4 Tutorials Figure 32 Firewall Rule for VPN 4.1.2 Configuring the VPN Rule This section shows how to configure a VPN rule on device B. 1 Click Security > VPN to open the following screen.
User Guide
Page 90
... routers can use the VPN tunnel. You may notice that are circled as follows and click Apply. So this example uses the firewall's FTP application layer gateway (ALG) to handle this instead of specifying port numbers in this screen to the following reasons. •... Chapter 4 Tutorials Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 4 Use this VPN network policy. • The firewall provides better security because it operates at layer 3 and just checks IP addresses and port numbers. 90 ZyWALL 2 Plus User's Guide The VPN network policy only operates at layer ...
... routers can use the VPN tunnel. You may notice that are circled as follows and click Apply. So this example uses the firewall's FTP application layer gateway (ALG) to handle this instead of specifying port numbers in this screen to the following reasons. •... Chapter 4 Tutorials Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 4 Use this VPN network policy. • The firewall provides better security because it operates at layer 3 and just checks IP addresses and port numbers. 90 ZyWALL 2 Plus User's Guide The VPN network policy only operates at layer ...
User Guide
Page 91
... following sections show how to configure firewall rules to enforce these restrictions. 4.1.3.1 Firewall Rule to Allow Access Example Configure a firewall rule that allows FTP access from the VPN tunnel to the FTP server. ZyWALL 2 Plus User's Guide 91 Chapter 4 Tutorials Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network Policy 4.1.3 Configuring the Firewall Rules Suppose you have several...
... following sections show how to configure firewall rules to enforce these restrictions. 4.1.3.1 Firewall Rule to Allow Access Example Configure a firewall rule that allows FTP access from the VPN tunnel to the FTP server. ZyWALL 2 Plus User's Guide 91 Chapter 4 Tutorials Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network Policy 4.1.3 Configuring the Firewall Rules Suppose you have several...
User Guide
Page 92
Chapter 4 Tutorials 1 Click Security > Firewall > Rule Summary. 2 Select VPN to LAN as follows and click Apply. Figure 37 SECURITY > FIREWALL > Rule Summary 4 Configure the rule as the packet direction and click Refresh. 3 Click the insert icon. The source addresses are the VPN rule's remote network and the destination address is the LAN FTP server. 92 ZyWALL 2 Plus User's Guide
Chapter 4 Tutorials 1 Click Security > Firewall > Rule Summary. 2 Select VPN to LAN as follows and click Apply. Figure 37 SECURITY > FIREWALL > Rule Summary 4 Configure the rule as the packet direction and click Refresh. 3 Click the insert icon. The source addresses are the VPN rule's remote network and the destination address is the LAN FTP server. 92 ZyWALL 2 Plus User's Guide
User Guide
Page 164
...to LAN/ZyWALL firewall rule that forwards packets from the protected LAN (Subnet 1) to configure the LAN into two or three logical networks with the ZyWALL itself as shown. The screen appears as the gateway for each LAN network. Figure 110 NETWORK > WAN > Traffic Redirect 164 ZyWALL 2 Plus User's ...Guide Chapter 8 WAN Screens Figure 108 Traffic Redirect WAN Setup IP alias allows you to avoid triangle route security...
...to LAN/ZyWALL firewall rule that forwards packets from the protected LAN (Subnet 1) to configure the LAN into two or three logical networks with the ZyWALL itself as shown. The screen appears as the gateway for each LAN network. Figure 110 NETWORK > WAN > Traffic Redirect 164 ZyWALL 2 Plus User's ...Guide Chapter 8 WAN Screens Figure 108 Traffic Redirect WAN Setup IP alias allows you to avoid triangle route security...
User Guide
Page 172
...Firewall Rules By default the firewall allows traffic between the WAN and the DMZ, traffic from the DMZ to the LAN is denied, and traffic from the LAN to the DMZ is also highly recommended that you keep all of the DMZ and WAN ports are in separate subnets. 172 ZyWALL 2 Plus... User's Guide See Section 6.1.2 on page 132 for more information on IP alias. Port roles See Section 6.5 on page 140 for more information on port roles. 9.1.3 DMZ Public IP Address Example The following figure shows a simple network setup with public IP addresses on...
...Firewall Rules By default the firewall allows traffic between the WAN and the DMZ, traffic from the DMZ to the LAN is denied, and traffic from the LAN to the DMZ is also highly recommended that you keep all of the DMZ and WAN ports are in separate subnets. 172 ZyWALL 2 Plus... User's Guide See Section 6.1.2 on page 132 for more information on IP alias. Port roles See Section 6.5 on page 140 for more information on port roles. 9.1.3 DMZ Public IP Address Example The following figure shows a simple network setup with public IP addresses on...
User Guide
Page 195
... VPN traffic between two networks. Enable the firewall to protect your LAN computers from your LAN computers to go to all data passing between the LAN, DMZ, WLAN and WAN. ZyWALL 2 Plus User's Guide 195 When the traffic matches a rule, the ZyWALL takes the action specified in...list them). Figure 127 Default Firewall Action Your customized rules take precedence and override the ZyWALL's default settings. It is generally a mechanism used to the WAN (1). The ZyWALL physically separates the LAN, DMZ, WLAN and the WAN and acts as a secure gateway for this session is also...
... VPN traffic between two networks. Enable the firewall to protect your LAN computers from your LAN computers to go to all data passing between the LAN, DMZ, WLAN and WAN. ZyWALL 2 Plus User's Guide 195 When the traffic matches a rule, the ZyWALL takes the action specified in...list them). Figure 127 Default Firewall Action Your customized rules take precedence and override the ZyWALL's default settings. It is generally a mechanism used to the WAN (1). The ZyWALL physically separates the LAN, DMZ, WLAN and the WAN and acts as a secure gateway for this session is also...
User Guide
Page 199
... gateway on the network (not reset the connection). See Asymmetrical Routes and IP Alias on separate subnets. Enable Firewall Select this screen. Note: Allowing asymmetrical routes may let traffic from the WAN go directly to reset the connection, as the ZyWALL's LAN IP address, return traffic may not go through the ZyWALL. ZyWALL 2 Plus User's Guide...
... gateway on the network (not reset the connection). See Asymmetrical Routes and IP Alias on separate subnets. Enable Firewall Select this screen. Note: Allowing asymmetrical routes may let traffic from the WAN go directly to reset the connection, as the ZyWALL's LAN IP address, return traffic may not go through the ZyWALL. ZyWALL 2 Plus User's Guide...
User Guide
Page 202
... the passage of the configured firewall rules. 202 ZyWALL 2 Plus User's Guide Select this screen afresh. 11.5 The Firewall Rule Summary Screen Click SECURITY > FIREWALL > Rule Summary to open the screen. Many of the rules for which the ZyWALL is taken. A broadcast storm occurs when a packet triggers multiple responses from a computer on a network or when computers attempt to...
... the passage of the configured firewall rules. 202 ZyWALL 2 Plus User's Guide Select this screen afresh. 11.5 The Firewall Rule Summary Screen Click SECURITY > FIREWALL > Rule Summary to open the screen. Many of the rules for which the ZyWALL is taken. A broadcast storm occurs when a packet triggers multiple responses from a computer on a network or when computers attempt to...
User Guide
Page 209
...ZyWALL 2 Plus User's Guide 209 You may want the ZyWALL to not use the Denial of existing half-open TCP sessions with the same destination host address could indicate that causes the firewall...minute low. The ZyWALL continues to disable DoS protection for a smaller network, a slower system...ZyWALL sends alerts whenever the TCP Maximum Incomplete is reached. As a general rule, you want to delete half-open session when a new connection request comes. Chapter 11 Firewall Screens The following table describes the labels in this screen afresh. Table 53 SECURITY > FIREWALL...
...ZyWALL 2 Plus User's Guide 209 You may want the ZyWALL to not use the Denial of existing half-open TCP sessions with the same destination host address could indicate that causes the firewall...minute low. The ZyWALL continues to disable DoS protection for a smaller network, a slower system...ZyWALL sends alerts whenever the TCP Maximum Incomplete is reached. As a general rule, you want to delete half-open session when a new connection request comes. Chapter 11 Firewall Screens The following table describes the labels in this screen afresh. Table 53 SECURITY > FIREWALL...
User Guide
Page 398
...ZyWALL 2 Plus User's Guide For security reasons, the ZyWALL allows multicast messages on the LAN only. When a UPnP device joins a network, it announces its presence with each other without additional configuration. All UPnP-enabled devices may also be obtained and modified by users in establishing their own services and opening firewall ports may present network security... issues. Disable UPnP if this is not your intention. UPnP and ZyXEL ZyXEL has achieved UPnP certification from the Universal ...
...ZyWALL 2 Plus User's Guide For security reasons, the ZyWALL allows multicast messages on the LAN only. When a UPnP device joins a network, it announces its presence with each other without additional configuration. All UPnP-enabled devices may also be obtained and modified by users in establishing their own services and opening firewall ports may present network security... issues. Disable UPnP if this is not your intention. UPnP and ZyXEL ZyXEL has achieved UPnP certification from the Universal ...