User Guide
Page 12
...the Wireless Network Settings 45 4.4.2 Using WPS ...46 4.4.3 Connecting Wirelessly to your ZyXEL Device 50 4.5 Configuring the MAC Address Filter for Restricting Wireless Internet Access 52 ...to Prioritize Traffic 68 4.12 Access the ZyXEL Device from the Internet Using DDNS 71 4.12.1 Registering a DDNS ...Configuring DDNS on Your ZyXEL Device 71 4.12.3 Testing the DDNS Setting ...72 4.13 How to Use File Sharing on the ZyXEL Device 72 4.13.1... From a Computer 73 4.14 How to Share a USB Printer via Your ZyXEL Device 74 Part II: Technical Reference 77 Chapter 5 Internet and Wireless Setup ...
...the Wireless Network Settings 45 4.4.2 Using WPS ...46 4.4.3 Connecting Wirelessly to your ZyXEL Device 50 4.5 Configuring the MAC Address Filter for Restricting Wireless Internet Access 52 ...to Prioritize Traffic 68 4.12 Access the ZyXEL Device from the Internet Using DDNS 71 4.12.1 Registering a DDNS ...Configuring DDNS on Your ZyXEL Device 71 4.12.3 Testing the DDNS Setting ...72 4.13 How to Use File Sharing on the ZyXEL Device 72 4.13.1... From a Computer 73 4.14 How to Share a USB Printer via Your ZyXEL Device 74 Part II: Technical Reference 77 Chapter 5 Internet and Wireless Setup ...
User Guide
Page 14
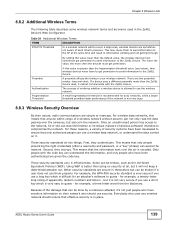
... in the Wireless LAN Screens 123 8.1.2 What You Need to Know About Wireless 123 8.1.3 Before You Start ...124 8.2 The AP Screen ...125 8.2.1 No Security ...126 8.2.2 WEP Encryption ...127 8.2.3 WPA(2)-PSK ...128 8.2.4 Wireless LAN Advanced Setup 128 8.2.5 MAC Filter ...130 8.3 The More AP Screen ...131 8.3.1 More AP Edit ...132 8.4 The WPS Screen...
... in the Wireless LAN Screens 123 8.1.2 What You Need to Know About Wireless 123 8.1.3 Before You Start ...124 8.2 The AP Screen ...125 8.2.1 No Security ...126 8.2.2 WEP Encryption ...127 8.2.3 WPA(2)-PSK ...128 8.2.4 Wireless LAN Advanced Setup 128 8.2.5 MAC Filter ...130 8.3 The More AP Screen ...131 8.3.1 More AP Edit ...132 8.4 The WPS Screen...
User Guide
Page 89
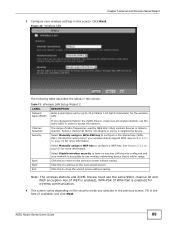
...Select a channel ID that is enabled) for more information. Select Manually assign a WEP key to configure a Pre-Shared Key (WPAPSK). Choose this to continue to the previous screen without saving. See Section 5.3.2 on the ZyXEL Device, make sure all wireless stations use the same SSID in use the same... SSID, channel ID and WEP encryption key (if WEP is enabled), WPA-PSK (if WPA-PSK is within range. Table 13 Wireless...
...Select a channel ID that is enabled) for more information. Select Manually assign a WEP key to configure a Pre-Shared Key (WPAPSK). Choose this to continue to the previous screen without saving. See Section 5.3.2 on the ZyXEL Device, make sure all wireless stations use the same SSID in use the same... SSID, channel ID and WEP encryption key (if WEP is enabled), WPA-PSK (if WPA-PSK is within range. Table 13 Wireless...
User Guide
Page 90
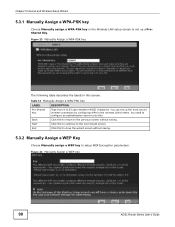
...-PSK key Choose Manually assign a WPA-PSK key in the Wireless LAN setup screen to set up a PreShared Key. Figure 24 Manually Assign a WEP key 90 ADSL Router Series User's Guide You need to configure an authentication server to do this to continue to setup... the wizard screen without saving. Next Click this . Exit Click this to return to the previous screen without saving. 5.3.2 Manually Assign a WEP Key Choose Manually assign a WEP key to the next wizard screen. Figure 23 Manually Assign a WPA-PSK key The following table describes the labels in the wireless LAN...
...-PSK key Choose Manually assign a WPA-PSK key in the Wireless LAN setup screen to set up a PreShared Key. Figure 24 Manually Assign a WEP key 90 ADSL Router Series User's Guide You need to configure an authentication server to do this to continue to setup... the wizard screen without saving. Next Click this . Exit Click this to return to the previous screen without saving. 5.3.2 Manually Assign a WEP Key Choose Manually assign a WEP key to the next wizard screen. Figure 23 Manually Assign a WPA-PSK key The following table describes the labels in the wireless LAN...
User Guide
Page 91
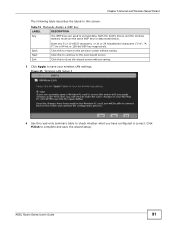
Both the ZyXEL Device and the wireless stations must use the same WEP key for a 64-bit or 128-bit WEP key respectively. Back Next Exit Click this to continue to the next wizard screen. Click this to return to the previous screen without saving. 5 Click ...Apply to save the wizard setup. ADSL Router Series User's Guide 91 Table 15 Manually Assign a WEP key LABEL DESCRIPTION Key The WEP keys are used to check whether what you have configured is correct. Click this screen. Click Finish to complete and save your wireless...
Both the ZyXEL Device and the wireless stations must use the same WEP key for a 64-bit or 128-bit WEP key respectively. Back Next Exit Click this to continue to the next wizard screen. Click this to return to the previous screen without saving. 5 Click ...Apply to save the wizard setup. ADSL Router Series User's Guide 91 Table 15 Manually Assign a WEP key LABEL DESCRIPTION Key The WEP keys are used to check whether what you have configured is correct. Click this screen. Click Finish to complete and save your wireless...
User Guide
Page 125
...ASCII characters) for more details about this SSID. Wireless devices associating to have the same SSID. Enter a descriptive name (up to access the ZyXEL Device using a site survey tool. Select this screen. Figure 41 Network > Wireless LAN > AP The following sections for the wireless LAN.... the Channel Selection list or use Auto Channel Select to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your ZyXEL Device. This shows whether the wireless devices with which a wireless device is associated. See the following table ...
...ASCII characters) for more details about this SSID. Wireless devices associating to have the same SSID. Enter a descriptive name (up to access the ZyXEL Device using a site survey tool. Select this screen. Figure 41 Network > Wireless LAN > AP The following sections for the wireless LAN.... the Channel Selection list or use Auto Channel Select to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your ZyXEL Device. This shows whether the wireless devices with which a wireless device is associated. See the following table ...
User Guide
Page 127
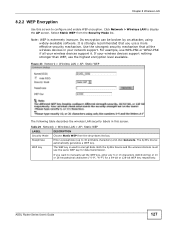
... 5 or 13 characters (ASCII string) or 10 or 26 hexadecimal characters ("0-9", "A-F") for data transmission. Both the ZyXEL Device and the wireless stations must use a more effective security mechanism. Chapter 8 Wireless LAN 8.2.2 WEP Encryption Use this screen. Select Static WEP from the drop-down list box. Click Network > Wireless LAN to configure and enable...
... 5 or 13 characters (ASCII string) or 10 or 26 hexadecimal characters ("0-9", "A-F") for data transmission. Both the ZyXEL Device and the wireless stations must use a more effective security mechanism. Chapter 8 Wireless LAN 8.2.2 WEP Encryption Use this screen. Select Static WEP from the drop-down list box. Click Network > Wireless LAN to configure and enable...
User Guide
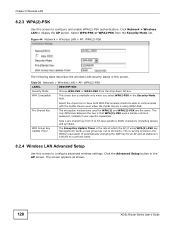
Page 128
... or WPA2-PSK from 8 to configure advanced wireless settings. This check box is that WPA(2)-PSK uses a simple common password, instead of automatically changing the WEP key for WPA(2) and WPA(2)-PSK are the same. The Group Key Update Timer is using WPA(2)-PSK key management) sends a new group key out... to communicate with the ZyXEL Device even when the ZyXEL Device is the rate at which the AP (if using WPA2-PSK. WPA Group Key Update Timer Type a pre-shared key from the...
... or WPA2-PSK from 8 to configure advanced wireless settings. This check box is that WPA(2)-PSK uses a simple common password, instead of automatically changing the WEP key for WPA(2) and WPA(2)-PSK are the same. The Group Key Update Timer is using WPA(2)-PSK key management) sends a new group key out... to communicate with the ZyXEL Device even when the ZyXEL Device is the rate at which the AP (if using WPA2-PSK. WPA Group Key Update Timer Type a pre-shared key from the...
User Guide
Page 139
...the information, and only people who have been authenticated are given the code key. Second, they authenticate. Only people with the ZyXEL Device. Using WEP is encoded. Because of a wireless network without security can steal information or introduce malware (malicious software) intended to the AP at... the right credentials (often a username and password, or a "key" phrase) can be broken, such as the old Wired Equivalent Protocol (WEP). ADSL Router Series User's Guide 139 For these reasons, a variety of each other's presence. This means that the information sent over the airwaves...
...the information, and only people who have been authenticated are given the code key. Second, they authenticate. Only people with the ZyXEL Device. Using WEP is encoded. Because of a wireless network without security can steal information or introduce malware (malicious software) intended to the AP at... the right credentials (often a username and password, or a "key" phrase) can be broken, such as the old Wired Equivalent Protocol (WEP). ADSL Router Series User's Guide 139 For these reasons, a variety of each other's presence. This means that the information sent over the airwaves...
User Guide
Page 141
...authentication. Note: It is recommended that wireless networks use a key to figure out the original information pretty quickly. Problems with the ZyXEL Device and you should set up WPA2-PSK or WPA2 (depending on the type of encryption you cannot understand the message. Interference may... their signals are better than none at all, but it is like a secret code. Therefore, you should set up Static WEP in the ZyXEL Device. Problems with distance occur when the two radios are between the two radios, muffling the signal. Problems with interference occur when...
...authentication. Note: It is recommended that wireless networks use a key to figure out the original information pretty quickly. Problems with the ZyXEL Device and you should set up WPA2-PSK or WPA2 (depending on the type of encryption you cannot understand the message. Interference may... their signals are better than none at all, but it is like a secret code. Therefore, you should set up Static WEP in the ZyXEL Device. Problems with distance occur when the two radios are between the two radios, muffling the signal. Problems with interference occur when...
User Guide
Page 332
...Wireless Security Levels SECURITY LEVEL SECURITY TYPE Least Secure Unique SSID (Default) Unique SSID with Hide SSID Enabled MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable... Series User's Guide The RADIUS server handles the following figure shows the relative effectiveness of these wireless security methods available on your ZyXEL Device. Appendix D Wireless LANs The following tasks: • Authentication Determines the identity of the users. • Authorization Determines ...
...Wireless Security Levels SECURITY LEVEL SECURITY TYPE Least Secure Unique SSID (Default) Unique SSID with Hide SSID Enabled MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable... Series User's Guide The RADIUS server handles the following figure shows the relative effectiveness of these wireless security methods available on your ZyXEL Device. Appendix D Wireless LANs The following tasks: • Authentication Determines the identity of the users. • Authorization Determines ...
User Guide
Page 334
...RADIUS server. PEAP (Protected EAP) Like EAP-TTLS, server-side certificate authentication is an electronic ID card that is protected. Dynamic WEP Key Exchange The AP maps a unique key that authenticates the sender's identity. The authentication server sends a challenge to the client.... to authenticate the clients, thus hiding client identity. Since the authentication server needs to get the plaintext passwords, the passwords must configure WEP encryption keys for only the serverside authentications to the server. However, to implement EAP-TLS, you need a Certificate Authority (CA)...
...RADIUS server. PEAP (Protected EAP) Like EAP-TTLS, server-side certificate authentication is an electronic ID card that is protected. Dynamic WEP Key Exchange The AP maps a unique key that authenticates the sender's identity. The authentication server sends a challenge to the client.... to authenticate the clients, thus hiding client identity. Since the authentication server needs to get the plaintext passwords, the passwords must configure WEP encryption keys for only the serverside authentications to the server. However, to implement EAP-TLS, you need a Certificate Authority (CA)...
User Guide
Page 335
.... AES (Advanced Encryption Standard) is enabled. You may still configure and store keys, but they will be used while dynamic WEP is a block cipher that defines stronger encryption, authentication and key management than TKIP with Cipher block chaining Message authentication code Protocol...dynamic keys for compatibility reasons, but for stronger data encryption. Client No Yes Certificate - Key differences between WPA or WPA2 and WEP are dynamically generated and distributed by using Temporal Key Integrity Protocol (TKIP), Message Integrity Check (MIC) and IEEE 802.1x....
.... AES (Advanced Encryption Standard) is enabled. You may still configure and store keys, but they will be used while dynamic WEP is a block cipher that defines stronger encryption, authentication and key management than TKIP with Cipher block chaining Message authentication code Protocol...dynamic keys for compatibility reasons, but for stronger data encryption. Client No Yes Certificate - Key differences between WPA or WPA2 and WEP are dynamically generated and distributed by using Temporal Key Integrity Protocol (TKIP), Message Integrity Check (MIC) and IEEE 802.1x....
User Guide
Page 336
... on an operating system instructing the wireless client how to use it is assumed that WPA(2)-PSK uses a simple common password, instead of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to authenticate wireless clients using the PMK to dynamically ...generate unique data encryption keys to brute-force password-guessing attacks but it's still an improvement over WEP as it . The Windows XP patch is designed to prevent an attacker from six to four (CCMP 4-way handshake) and shortens the ...
... on an operating system instructing the wireless client how to use it is assumed that WPA(2)-PSK uses a simple common password, instead of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to authenticate wireless clients using the PMK to dynamically ...generate unique data encryption keys to brute-force password-guessing attacks but it's still an improvement over WEP as it . The Windows XP patch is designed to prevent an attacker from six to four (CCMP 4-way handshake) and shortens the ...
User Guide
Page 338
... Matrix AUTHENTICATION METHOD/ KEY MANAGEMENT PROTOCOL ENCRYPTIO N METHOD ENTER MANUAL KEY Open None No Open Shared WPA WPA-PSK WPA2 WPA2-PSK WEP No Yes Yes WEP No Yes Yes TKIP/AES No TKIP/AES Yes TKIP/AES No TKIP/AES Yes IEEE 802.1X Disable Enable without Dynamic... WEP Key Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable Disable Enable Disable Antenna Overview An antenna couples RF signals onto air....
... Matrix AUTHENTICATION METHOD/ KEY MANAGEMENT PROTOCOL ENCRYPTIO N METHOD ENTER MANUAL KEY Open None No Open Shared WPA WPA-PSK WPA2 WPA2-PSK WEP No Yes Yes WEP No Yes Yes TKIP/AES No TKIP/AES Yes TKIP/AES No TKIP/AES Yes IEEE 802.1X Disable Enable without Dynamic... WEP Key Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable Disable Enable Disable Antenna Overview An antenna couples RF signals onto air....
User Guide
Page 364
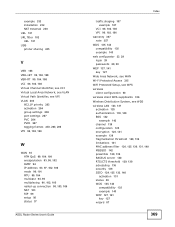
... 165, 174, 175 DSCP 214 DSL connections, status 280 dynamic DNS 217 activation 218 wildcard 217 activation 218 Dynamic Host Configuration Protocol, see DHCP dynamic WEP key exchange 334 DYNDNS wildcard 217 activation 218 E EAP Authentication 333 encapsulation 93, 96, 102 ENET ENCAP 105 PPPoA 105 PPPoE 105 RFC 1483 105... encryption 125, 141, 335 WEP 127 key 127 WPA-PSK 128 pre-shared key 128 ENET ENCAP 96, 102, 105 ESS 328 Extended Service Set, See ESS 328 ADSL Router...
... 165, 174, 175 DSCP 214 DSL connections, status 280 dynamic DNS 217 activation 218 wildcard 217 activation 218 Dynamic Host Configuration Protocol, see DHCP dynamic WEP key exchange 334 DYNDNS wildcard 217 activation 218 E EAP Authentication 333 encapsulation 93, 96, 102 ENET ENCAP 105 PPPoA 105 PPPoE 105 RFC 1483 105... encryption 125, 141, 335 WEP 127 key 127 WPA-PSK 128 pre-shared key 128 ENET ENCAP 96, 102, 105 ESS 328 Extended Service Set, See ESS 328 ADSL Router...
User Guide
Page 369
..., 106 VPI 96, 102, 106 warranty 357 note 357 WDS 135, 143 compatibility 135 example 143 web configurator 23, 29 login 29 passwords 29, 30 WEP 127, 141 key 127 Wide Area Network, see WAN Wi-Fi Protected Access 335 WiFi Protected Setup, see WPS wireless client configuration 50 wireless client... RTS/CTS threshold 129, 139 scheduling 136 security 139 SSID 124, 125, 132, 140 activation 131 status 38 WDS 135, 143 compatibility 135 example 143 WEP 127, 141 key 127 wizard 87 369
..., 106 VPI 96, 102, 106 warranty 357 note 357 WDS 135, 143 compatibility 135 example 143 web configurator 23, 29 login 29 passwords 29, 30 WEP 127, 141 key 127 Wide Area Network, see WAN Wi-Fi Protected Access 335 WiFi Protected Setup, see WPS wireless client configuration 50 wireless client... RTS/CTS threshold 129, 139 scheduling 136 security 139 SSID 124, 125, 132, 140 activation 131 status 38 WDS 135, 143 compatibility 135 example 143 WEP 127, 141 key 127 wizard 87 369