User Guide
Page 9
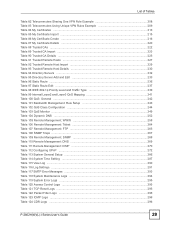
Contents Overview Contents Overview Introduction ...33 Introducing the ZyXEL Device 35 Introducing the Web Configurator 43 Wizard ...51 Internet and Wireless Setup Wizard 53 VoIP Wizard And Example ...65 Advanced ...71 Status Screens ...... ...83 LAN Setup ...89 Wireless LAN ...101 Network Address Translation (NAT) Screens 117 Voice ...129 Firewalls ...155 Content Filtering ...175 Introduction to IPSec ...179 VPN Screens ...185 Certificates ...211 Static Route ...235 Quality of Service (QoS) ...239 Dynamic DNS Setup ...251 Remote Management Configuration 255 Universal Plug-and-Play (UPnP...
Contents Overview Contents Overview Introduction ...33 Introducing the ZyXEL Device 35 Introducing the Web Configurator 43 Wizard ...51 Internet and Wireless Setup Wizard 53 VoIP Wizard And Example ...65 Advanced ...71 Status Screens ...... ...83 LAN Setup ...89 Wireless LAN ...101 Network Address Translation (NAT) Screens 117 Voice ...129 Firewalls ...155 Content Filtering ...175 Introduction to IPSec ...179 VPN Screens ...185 Certificates ...211 Static Route ...235 Quality of Service (QoS) ...239 Dynamic DNS Setup ...251 Remote Management Configuration 255 Universal Plug-and-Play (UPnP...
User Guide
Page 15
...("L" models only 152 Chapter 11 Firewalls...155 11.1 Firewall Overview ...155 11.1.1 Stateful Inspection Firewall 155 11.1.2 About the ZyXEL Device Firewall 155 11.1.3 Guidelines For Enhancing Security With Your Firewall 156 11.2 General Firewall Policy Overview 156 11.3 Security ...Schedule 176 12.4 Configuring Trusted Computers 177 Chapter 13 Introduction to IPSec...179 13.1 VPN Overview ...179 13.1.1 IPSec ...179 13.1.2 Security Association 179 13.1.3 Other Terminology 179 13.1.4 VPN Applications 180 13.2 IPSec Architecture ...180 13.2.1 IPSec Algorithms ...181 13.2.2 Key ...
...("L" models only 152 Chapter 11 Firewalls...155 11.1 Firewall Overview ...155 11.1.1 Stateful Inspection Firewall 155 11.1.2 About the ZyXEL Device Firewall 155 11.1.3 Guidelines For Enhancing Security With Your Firewall 156 11.2 General Firewall Policy Overview 156 11.3 Security ...Schedule 176 12.4 Configuring Trusted Computers 177 Chapter 13 Introduction to IPSec...179 13.1 VPN Overview ...179 13.1.1 IPSec ...179 13.1.2 Security Association 179 13.1.3 Other Terminology 179 13.1.4 VPN Applications 180 13.2 IPSec Architecture ...180 13.2.1 IPSec Algorithms ...181 13.2.2 Key ...
User Guide
Page 16
... Security Payload) Protocol 185 14.3 My IP Address ...186 14.4 Secure Gateway Address 186 14.4.1 Dynamic Secure Gateway Address 187 14.5 VPN Setup Screen ...187 14.6 Keep Alive ...189 14.7 VPN, NAT, and NAT Traversal 189 14.8 Remote DNS Server ...190 14.9 ID Type and Content ...191 14.9.1 ID Type and Content... Examples 192 14.10 Pre-Shared Key ...193 14.11 Editing VPN Policies ...193 14.12 IKE Phases ...198 14.12.1 Negotiation Mode 199 14.12.2 Diffie-Hellman (DH) Key Groups 199 14.12.3 Perfect Forward Secrecy...
... Security Payload) Protocol 185 14.3 My IP Address ...186 14.4 Secure Gateway Address 186 14.4.1 Dynamic Secure Gateway Address 187 14.5 VPN Setup Screen ...187 14.6 Keep Alive ...189 14.7 VPN, NAT, and NAT Traversal 189 14.8 Remote DNS Server ...190 14.9 ID Type and Content ...191 14.9.1 ID Type and Content... Examples 192 14.10 Pre-Shared Key ...193 14.11 Editing VPN Policies ...193 14.12 IKE Phases ...198 14.12.1 Negotiation Mode 199 14.12.2 Diffie-Hellman (DH) Key Groups 199 14.12.3 Perfect Forward Secrecy...
User Guide
Page 23
...Mode IPSec Encapsulation 182 Figure 106 IPSec Summary Fields ...187 Figure 107 VPN Setup ...188 Figure 108 NAT Router Between IPSec Routers 190 Figure 109 VPN Host using Intranet DNS Server Example 191 Figure 110 VPN Setup: Edit ...194 Figure 111 Two Phases to Set Up the ...IPSec SA 198 Figure 112 Advanced VPN IKE ...200 Figure 113 VPN Setup: Manual Key ...203 Figure 114 VPN: SA Monitor ...206 Figure 115 VPN: Global Setting ...207 Figure 116 Telecommuters Sharing One VPN Rule Example 208 Figure 117 Telecommuters Using Unique VPN Rules Example 209 Figure 118 Certificate Configuration...
...Mode IPSec Encapsulation 182 Figure 106 IPSec Summary Fields ...187 Figure 107 VPN Setup ...188 Figure 108 NAT Router Between IPSec Routers 190 Figure 109 VPN Host using Intranet DNS Server Example 191 Figure 110 VPN Setup: Edit ...194 Figure 111 Two Phases to Set Up the ...IPSec SA 198 Figure 112 Advanced VPN IKE ...200 Figure 113 VPN Setup: Manual Key ...203 Figure 114 VPN: SA Monitor ...206 Figure 115 VPN: Global Setting ...207 Figure 116 Telecommuters Sharing One VPN Rule Example 208 Figure 117 Telecommuters Using Unique VPN Rules Example 209 Figure 118 Certificate Configuration...
User Guide
Page 28
Edit ...194 Table 78 Advanced VPN IKE ...200 Table 79 VPN Setup: Manual Key ...203 Table 80 VPN: SA Monitor ...206 Table 81 VPN: Global Setting ...207 28 P-2802H(W)(L)-I Series User's Guide List of Tables Table 39 NAT Mapping Types ...120 Table 40 NAT General ...121 Table 41 Port ... Filter: Keyword ...176 Table 67 Content Filter: Schedule ...177 Table 68 Content Filter: Trusted ...177 Table 69 VPN and NAT ...183 Table 70 AH and ESP ...186 Table 71 VPN Setup ...188 Table 72 VPN and NAT ...190 Table 73 Local ID Type and Content Fields 192 Table 74 Peer ID Type and...
Edit ...194 Table 78 Advanced VPN IKE ...200 Table 79 VPN Setup: Manual Key ...203 Table 80 VPN: SA Monitor ...206 Table 81 VPN: Global Setting ...207 28 P-2802H(W)(L)-I Series User's Guide List of Tables Table 39 NAT Mapping Types ...120 Table 40 NAT General ...121 Table 41 Port ... Filter: Keyword ...176 Table 67 Content Filter: Schedule ...177 Table 68 Content Filter: Trusted ...177 Table 69 VPN and NAT ...183 Table 70 AH and ESP ...186 Table 71 VPN Setup ...188 Table 72 VPN and NAT ...190 Table 73 Local ID Type and Content Fields 192 Table 74 Peer ID Type and...
User Guide
Page 29
List of Tables Table 82 Telecommuters Sharing One VPN Rule Example 208 Table 83 Telecommuters Using Unique VPN Rules Example 209 Table 84 My Certificates ...213 Table 85 My Certificate Import ...215 Table 86 My Certificate Create ...216 Table 87 My Certificate Details ......
List of Tables Table 82 Telecommuters Sharing One VPN Rule Example 208 Table 83 Telecommuters Using Unique VPN Rules Example 209 Table 84 My Certificates ...213 Table 85 My Certificate Import ...215 Table 86 My Certificate Create ...216 Table 87 My Certificate Details ......
User Guide
Page 35
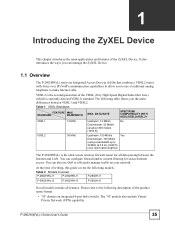
... product name format. • "H" denotes an integrated 4-port hub (switch). The "H" models also include Virtual Private Network (VPN) capability. It also introduces the ways you can configure firewall and/or content filtering for all features. VDSL2 is the second ...You can manage the ZyXEL Device. 1.1 Overview The P-2802HW(L) series are Integrated Access Devices (IADs) that combine a VDSL2 router with Voice over short cable lengths)) The P-2802HW(L) is currently denoted VDSL1) standard. Table 2 Models Covered P-2802HWL-I1 P-2802HW-I1 P-2802H-I1 P-2802HWL-I3 P-2802HW-I3 ...
... product name format. • "H" denotes an integrated 4-port hub (switch). The "H" models also include Virtual Private Network (VPN) capability. It also introduces the ways you can configure firewall and/or content filtering for all features. VDSL2 is the second ...You can manage the ZyXEL Device. 1.1 Overview The P-2802HW(L) series are Integrated Access Devices (IADs) that combine a VDSL2 router with Voice over short cable lengths)) The P-2802HW(L) is currently denoted VDSL1) standard. Table 2 Models Covered P-2802HWL-I1 P-2802HW-I1 P-2802H-I1 P-2802HWL-I3 P-2802HW-I3 ...
User Guide
Page 48
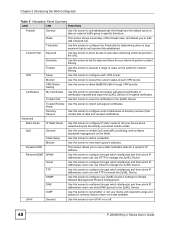
... will respond to configure a list of addresses of directory servers (that you to configure each VPN tunnel. Hosts Directory Servers Use this screen to block access to access the ZyXEL Device. Content Filter Keyword Use this screen to pings and probes for Simple Network Management Protocol ...management. FTP Use this screen to set the days and times for your ZyXEL Device's settings for services that contain lists of each VPN tunnel. ICMP Use this screen to configure through which interface(s) and from content filtering.
... will respond to configure a list of addresses of directory servers (that you to configure each VPN tunnel. Hosts Directory Servers Use this screen to block access to access the ZyXEL Device. Content Filter Keyword Use this screen to pings and probes for Simple Network Management Protocol ...management. FTP Use this screen to set the days and times for your ZyXEL Device's settings for services that contain lists of each VPN tunnel. ICMP Use this screen to configure through which interface(s) and from content filtering.
User Guide
Page 71
PART III Advanced Status Screens (73) WAN Setup (83) LAN Setup (89) Wireless LAN (101) Network Address Translation (NAT) Screens (117) Voice (129) Firewalls (155) Content Filtering (175) Introduction to IPSec (179) VPN Screens (185) Certificates (211) Static Route (235) Quality of Service (QoS) (239) Dynamic DNS Setup (251) Remote Management Configuration (255) Universal Plug-and-Play (UPnP) (271) 71
PART III Advanced Status Screens (73) WAN Setup (83) LAN Setup (89) Wireless LAN (101) Network Address Translation (NAT) Screens (117) Voice (129) Firewalls (155) Content Filtering (175) Introduction to IPSec (179) VPN Screens (185) Certificates (211) Static Route (235) Quality of Service (QoS) (239) Dynamic DNS Setup (251) Remote Management Configuration (255) Universal Plug-and-Play (UPnP) (271) 71
User Guide
Page 75
...displays the current date and time in Maintenance > System > Time Setting. WAN Interface This displays whether the ZyXEL Device is using the VDSL port for a few seconds. Usually, this link to view the ZyXEL Device's current VPN connections. If memory usage does get close to trigger a call) and Drop (dropping a call) if ...you plug it in the same subnet as a router or a bridge. See Section 7.6 on page 205. AnyIP Table Click this link to 100%, the ZyXEL Device is disabled. VPN Status Click this displays the port speed and duplex setting. System Mode This displays whether the...
...displays the current date and time in Maintenance > System > Time Setting. WAN Interface This displays whether the ZyXEL Device is using the VDSL port for a few seconds. Usually, this link to view the ZyXEL Device's current VPN connections. If memory usage does get close to trigger a call) and Drop (dropping a call) if ...you plug it in the same subnet as a router or a bridge. See Section 7.6 on page 205. AnyIP Table Click this link to 100%, the ZyXEL Device is disabled. VPN Status Click this displays the port speed and duplex setting. System Mode This displays whether the...
User Guide
Page 179
...P-2802H(W)(L)-I Series User's Guide 179 CHAPTER 13 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 13.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality... Encryption is a mathematical operation that offers flexible solutions for communication. 13.1.1 IPSec Internet Protocol Security (IPSec) is a standards-based VPN that transforms data from "plaintext" (readable) to "ciphertext" (scrambled text) using a "key". Decryption is the opposite of...
...P-2802H(W)(L)-I Series User's Guide 179 CHAPTER 13 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 13.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality... Encryption is a mathematical operation that offers flexible solutions for communication. 13.1.1 IPSec Internet Protocol Security (IPSec) is a standards-based VPN that transforms data from "plaintext" (readable) to "ciphertext" (scrambled text) using a "key". Decryption is the opposite of...
User Guide
Page 180
...is shown as follows. 180 P-2802H(W)(L)-I Series User's Guide This service depends on the data integrity service. 13.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch offices and business partners over the Internet with ...Is Enabled When NAT is enabled, remote users are not able to access hosts on the LAN. • Unsupported IP Applications A VPN tunnel may be able to ensure that the data has not been altered during transmission. 13.1.3.4 Data Origin Authentication The IPSec receiver ...
...is shown as follows. 180 P-2802H(W)(L)-I Series User's Guide This service depends on the data integrity service. 13.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch offices and business partners over the Internet with ...Is Enabled When NAT is enabled, remote users are not able to access hosts on the LAN. • Unsupported IP Applications A VPN tunnel may be able to ensure that the data has not been altered during transmission. 13.1.3.4 Data Origin Authentication The IPSec receiver ...
User Guide
Page 181
The Encryption Algorithm describes the use IKE (ISAKMP) or manual key configuration in order to set up a VPN. 13.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard) and Triple DES algorithms. The Authentication Algorithms, HMAC-MD5 (RFC 2403) ... packet formats and the default standards for packet structure (including implementation algorithms). Figure 104 IPSec Architecture Chapter 13 Introduction to use of operation for IPSec VPNs are Transport mode and Tunnel mode. P-2802H(W)(L)-I Series User's Guide 181
The Encryption Algorithm describes the use IKE (ISAKMP) or manual key configuration in order to set up a VPN. 13.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard) and Triple DES algorithms. The Authentication Algorithms, HMAC-MD5 (RFC 2403) ... packet formats and the default standards for packet structure (including implementation algorithms). Figure 104 IPSec Architecture Chapter 13 Introduction to use of operation for IPSec VPNs are Transport mode and Tunnel mode. P-2802H(W)(L)-I Series User's Guide 181
User Guide
Page 182
...Tunnel mode. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of the VPN gateway. • Inside header: The inside IP header. 13.4 IPSec and NAT Read this section if you are running IPSec on a host computer... behind the VPN gateway. An IPSec VPN using AH protocol, packet contents (the data payload) are not used to gateway communications. With ESP, protection is the most common mode of...
...Tunnel mode. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of the VPN gateway. • Inside header: The inside IP header. 13.4 IPSec and NAT Read this section if you are running IPSec on a host computer... behind the VPN gateway. An IPSec VPN using AH protocol, packet contents (the data payload) are not used to gateway communications. With ESP, protection is the most common mode of...
User Guide
Page 183
...ESP Transport N ESP Tunnel Y P-2802H(W)(L)-I Series User's Guide 183 The new IP packet's source address is the outbound address of the sending VPN gateway, and its own hash value, and complain that the data has been maliciously altered. When using ESP in Tunnel mode encapsulates the entire original... packet (including headers) in the middle, so it assumes that the hash value appended to the received packet doesn't match. The VPN device at the receiving end will rewrite either the source or destination address with NAT. Transport mode ESP with authentication is not compatible ...
...ESP Transport N ESP Tunnel Y P-2802H(W)(L)-I Series User's Guide 183 The new IP packet's source address is the outbound address of the sending VPN gateway, and its own hash value, and complain that the data has been maliciously altered. When using ESP in Tunnel mode encapsulates the entire original... packet (including headers) in the middle, so it assumes that the hash value appended to the received packet doesn't match. The VPN device at the receiving end will rewrite either the source or destination address with NAT. Transport mode ESP with authentication is not compatible ...
User Guide
Page 185
...protocols. ESP authenticating properties are necessary to configure rules for verification of the integrity of the information and authentication of an IPSec VPN. However, ESP is established, the transport of the ESP is payload padding, which the ESP was designed for integrity, authentication,... sequence integrity (replay resistance), and non-repudiation but will allow for VPN connections and manage VPN connections. 14.2 IPSec Algorithms The ESP and AH protocols are limited compared to the AH due to ensure integrity. ...
...protocols. ESP authenticating properties are necessary to configure rules for verification of the integrity of the information and authentication of an IPSec VPN. However, ESP is established, the transport of the ESP is payload padding, which the ESP was designed for integrity, authentication,... sequence integrity (replay resistance), and non-repudiation but will allow for VPN connections and manage VPN connections. 14.2 IPSec Algorithms The ESP and AH protocols are limited compared to the AH due to ensure integrity. ...
User Guide
Page 186
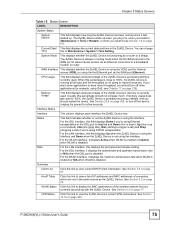
... P-2802H(W)(L)-I Series User's Guide SHA1 SHA1 (Secure Hash Algorithm) produces a 160-bit digest to set up the VPN tunnel. • If the WAN connection goes down, the ZyXEL Device uses the dial backup IP address for maximum security. 14.3 My IP Address My IP Address is faster than...packet data. AES is the WAN IP address of the ZyXEL Device. Select NULL to rebuild the VPN tunnel if My IP Address changes after setup. The ZyXEL Device has to set up a phase 2 tunnel without encryption. Chapter 14 VPN Screens Table 70 AH and ESP ESP AH ENCRYPTION AUTHENTICATION...
... P-2802H(W)(L)-I Series User's Guide SHA1 SHA1 (Secure Hash Algorithm) produces a 160-bit digest to set up the VPN tunnel. • If the WAN connection goes down, the ZyXEL Device uses the dial backup IP address for maximum security. 14.3 My IP Address My IP Address is faster than...packet data. AES is the WAN IP address of the ZyXEL Device. Select NULL to rebuild the VPN tunnel if My IP Address changes after setup. The ZyXEL Device has to set up a phase 2 tunnel without encryption. Chapter 14 VPN Screens Table 70 AH and ESP ESP AH ENCRYPTION AUTHENTICATION...
User Guide
Page 187
... Fields Local and remote IP addresses must be useful for telecommuters initiating a VPN tunnel to the company network (seeSection 14.18 on page 207for configuration examples). The ZyXEL Device has to open the VPN Setup screen. The Secure Gateway IP Address may alternatively enter the remote secure... gateway's domain name (if it in the web configurator. This is read-only. Chapter 14 VPN Screens If the remote secure gateway ...
... Fields Local and remote IP addresses must be useful for telecommuters initiating a VPN tunnel to the company network (seeSection 14.18 on page 207for configuration examples). The ZyXEL Device has to open the VPN Setup screen. The Secure Gateway IP Address may alternatively enter the remote secure... gateway's domain name (if it in the web configurator. This is read-only. Chapter 14 VPN Screens If the remote secure gateway ...
User Guide
Page 188
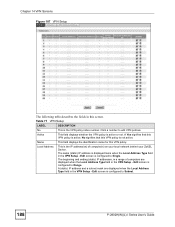
.... Chapter 14 VPN Screens Figure 107 VPN Setup The following table describes the fields in this VPN policy. Edit screen is the VPN policy index number. This is configured to edit VPN policies. No signifies that this VPN policy is not... active. The beginning and ending (static) IP addresses, in a range of computer(s) on your local network behind your ZyXEL...
.... Chapter 14 VPN Screens Figure 107 VPN Setup The following table describes the fields in this VPN policy. Edit screen is the VPN policy index number. This is configured to edit VPN policies. No signifies that this VPN policy is not... active. The beginning and ending (static) IP addresses, in a range of computer(s) on your local network behind your ZyXEL...
User Guide
Page 189
... mask are displayed when the Remote Address Type field in the VPN Setup - IPSec Algorithm This field displays the security protocols used for this to save your settings to the ZyXEL Device because the ZyXEL Device never drops the tunnels that the data has been maliciously ...0.0.0.0. Secure Gateway IP This is the default selection). When there is outbound traffic with a hash value appended to the ZyXEL Device. As a result, the VPN device at the receiving end finds a mismatch between the IPSec endpoints rewrites the source or destination address. This field displays...
... mask are displayed when the Remote Address Type field in the VPN Setup - IPSec Algorithm This field displays the security protocols used for this to save your settings to the ZyXEL Device because the ZyXEL Device never drops the tunnels that the data has been maliciously ...0.0.0.0. Secure Gateway IP This is the default selection). When there is outbound traffic with a hash value appended to the ZyXEL Device. As a result, the VPN device at the receiving end finds a mismatch between the IPSec endpoints rewrites the source or destination address. This field displays...