User Guide
Page 41
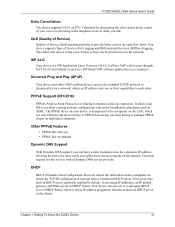
...not aware of Service (QoS) mechanisms help to provide better service on individual computers. PPPoE Support (RFC2516) PPPoE (Point-to DHCP clients. It can be more easily accessible from a centralized DHCP server. This allows the device to tag voice frames so they can assign IP addresses, ...thus saving you can also act as a surrogate DHCP server (DHCP Relay) where it (such as ADSL. Chapter 1 Getting To Know the ZyXEL Device 41 DHCP DHCP (Dynamic Host Configuration Protocol) allows the individual clients (computers) to the clients. It allows your device is a SIP Application...
...not aware of Service (QoS) mechanisms help to provide better service on individual computers. PPPoE Support (RFC2516) PPPoE (Point-to DHCP clients. It can be more easily accessible from a centralized DHCP server. This allows the device to tag voice frames so they can assign IP addresses, ...thus saving you can also act as a surrogate DHCP server (DHCP Relay) where it (such as ADSL. Chapter 1 Getting To Know the ZyXEL Device 41 DHCP DHCP (Dynamic Host Configuration Protocol) allows the individual clients (computers) to the clients. It allows your device is a SIP Application...
User Guide
Page 42
...) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 42 Chapter 1 Getting To Know the ZyXEL Device Packet Filters Your device's packet filtering function allows added network security and management. This means an IEEE 802.11b radio card can interface... as the gateway for quick, intuitive and easy installation. Ease of Installation Your device is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. P-2602H(W)(L)-DxA Series User's Guide Multiple PVC (Permanent Virtual ...
...) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 42 Chapter 1 Getting To Know the ZyXEL Device Packet Filters Your device's packet filtering function allows added network security and management. This means an IEEE 802.11b radio card can interface... as the gateway for quick, intuitive and easy installation. Ease of Installation Your device is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. P-2602H(W)(L)-DxA Series User's Guide Multiple PVC (Permanent Virtual ...
User Guide
Page 43
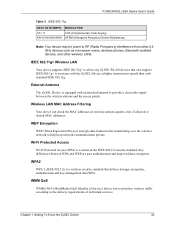
... IEEE 802.11g+ to allow any ZyXEL WLAN devices that defines stronger encryption, authentication and key management than with an attached antenna to help keep network communications private. Key differences between the wireless stations and the access points. Wireless LAN MAC Address Filtering Your... Multiplexing) Note: Your device may be prone to associate with the ZyXEL Device at higher transmission speeds than WPA. Chapter 1 Getting To Know the ZyXEL Device 43 Wi-Fi Protected Access Wi-Fi Protected Access (WPA) is a wireless security standard that also support IEEE 802.1g...
... IEEE 802.11g+ to allow any ZyXEL WLAN devices that defines stronger encryption, authentication and key management than with an attached antenna to help keep network communications private. Key differences between the wireless stations and the access points. Wireless LAN MAC Address Filtering Your... Multiplexing) Note: Your device may be prone to associate with the ZyXEL Device at higher transmission speeds than WPA. Chapter 1 Getting To Know the ZyXEL Device 43 Wi-Fi Protected Access Wi-Fi Protected Access (WPA) is a wireless security standard that also support IEEE 802.1g...
User Guide
Page 45
... address in the figure) and your device (B) changes the call through the Internet to -peer Calling 1.4.4 Firewall for Secure Broadband Internet Access Your device provides protection from the WAN. P-2602H(W)(L)-DxA Series User's Guide Figure 2 Internet Telephony Service Provider Application 1.4.3 Make Peer-to... to -IP" calls. Figure 3 Peer-to the peer VoIP device (C). Chapter 1 Getting To Know the ZyXEL Device 45 Peer-to-peer calls are also called "Point to Point" or "IP-to someone's IP address without using a SIP proxy server. The firewall supports TCP/UDP inspection...
... address in the figure) and your device (B) changes the call through the Internet to -peer Calling 1.4.4 Firewall for Secure Broadband Internet Access Your device provides protection from the WAN. P-2602H(W)(L)-DxA Series User's Guide Figure 2 Internet Telephony Service Provider Application 1.4.3 Make Peer-to... to -IP" calls. Figure 3 Peer-to the peer VoIP device (C). Chapter 1 Getting To Know the ZyXEL Device 45 Peer-to-peer calls are also called "Point to Point" or "IP-to someone's IP address without using a SIP proxy server. The firewall supports TCP/UDP inspection...
User Guide
Page 78
...It allows for implementing VoIP. Otherwise, click the wizard icon ( ) in the top right corner of the web configurator to -point and multipoint communication between client computers over a packet-based network that does not provide a guaranteed quality of service. P-2602H(W)(L)-DxA ...) rather than TCP (Transmission Control Protocol). 5.3 Bandwidth Management Wizard Setup 1 After you enter the password to access the web configurator, select Go to -point and multipoint communication between client computers over a packet-based network that does not provide a guaranteed quality of service...
...It allows for implementing VoIP. Otherwise, click the wizard icon ( ) in the top right corner of the web configurator to -point and multipoint communication between client computers over a packet-based network that does not provide a guaranteed quality of service. P-2602H(W)(L)-DxA ...) rather than TCP (Transmission Control Protocol). 5.3 Bandwidth Management Wizard Setup 1 After you enter the password to access the web configurator, select Go to -point and multipoint communication between client computers over a packet-based network that does not provide a guaranteed quality of service...
User Guide
Page 93
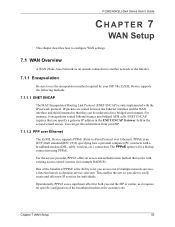
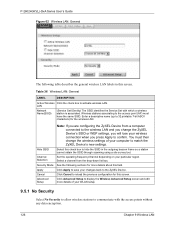
... it encapsulates routed Ethernet frames into bridged ATM cells. For the service provider, PPPoE offers an access and authentication method that works with the IP network protocol. The ZyXEL Device supports the following methods. 7.1.1.1 ENET ENCAP The MAC Encapsulated Routing Link Protocol (ENET ENCAP...Internet. 7.1.1 Encapsulation Be sure to use the encapsulation method required by your ISP. 7.1.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to-Point Protocol over Ethernet). IP packets are routed between the Ethernet interface and the WAN interface and then formatted so that...
... it encapsulates routed Ethernet frames into bridged ATM cells. For the service provider, PPPoE offers an access and authentication method that works with the IP network protocol. The ZyXEL Device supports the following methods. 7.1.1.1 ENET ENCAP The MAC Encapsulated Routing Link Protocol (ENET ENCAP...Internet. 7.1.1 Encapsulation Be sure to use the encapsulation method required by your ISP. 7.1.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to-Point Protocol over Ethernet). IP packets are routed between the Ethernet interface and the WAN interface and then formatted so that...
User Guide
Page 94
...required by your ISP. 7.1.2.1 VC-based Multiplexing In this case, by prior mutual agreement, each protocol is not practical to you. The ZyXEL Device encapsulates the PPP session based on RFC1483 and sends it is assigned to RFC 2364 for Multiprotocol Encapsulation over ATM Adaptation Layer 5 (...). Be sure to use the correct Virtual Path Identifier (VPI) and Virtual Channel Identifier (VCI) numbers assigned to have access. 7.1.1.3 PPPoA PPPoA stands for Point to RFC 1661 for example, if charging heavily depends on the number of ATM traffic). VC-based multiplexing may be dominant...
...required by your ISP. 7.1.2.1 VC-based Multiplexing In this case, by prior mutual agreement, each protocol is not practical to you. The ZyXEL Device encapsulates the PPP session based on RFC1483 and sends it is assigned to RFC 2364 for Multiprotocol Encapsulation over ATM Adaptation Layer 5 (...). Be sure to use the correct Virtual Path Identifier (VPI) and Virtual Channel Identifier (VCI) numbers assigned to have access. 7.1.1.3 PPPoA PPPoA stands for Point to RFC 1661 for example, if charging heavily depends on the number of ATM traffic). VC-based multiplexing may be dominant...
User Guide
Page 121
...networks.This chapter applies to configure the wireless network settings in the same wireless network must follow these basic guidelines. • Every device in your ZyXEL Device. P-2602H(W)(L)-DxA Series User's Guide CHAPTER 9 Wireless LAN This chapter discusses how to the "W" models only. 9.1 Wireless Network Overview The following... The SSID is the name of a Wireless Network The wireless network is the AP. In this wireless network, devices A and B use the access point (AP) to interact with the other devices (such as the printer) or with the Internet. Chapter 9 Wireless LAN 121
...networks.This chapter applies to configure the wireless network settings in the same wireless network must follow these basic guidelines. • Every device in your ZyXEL Device. P-2602H(W)(L)-DxA Series User's Guide CHAPTER 9 Wireless LAN This chapter discusses how to the "W" models only. 9.1 Wireless Network Overview The following... The SSID is the name of a Wireless Network The wireless network is the AP. In this wireless network, devices A and B use the access point (AP) to interact with the other devices (such as the printer) or with the Internet. Chapter 9 Wireless LAN 121
User Guide
Page 125
... General screen. If this option so that the ZyXEL Device transmits IEEE 802.11g wireless traffic only. Maximum Frame Burst sets the maximum time that wireless devices can change the wireless settings of each other wireless access points) on your wireless network, you press Apply to... match the ZyXEL Device's new settings. This is greater than the fragmentation threshold value (see below), then wireless devices ...
... General screen. If this option so that the ZyXEL Device transmits IEEE 802.11g wireless traffic only. Maximum Frame Burst sets the maximum time that wireless devices can change the wireless settings of each other wireless access points) on your wireless network, you press Apply to... match the ZyXEL Device's new settings. This is greater than the fragmentation threshold value (see below), then wireless devices ...
User Guide
Page 126
... a channel from a computer connected to the wireless LAN and you change the wireless settings of your particular region. Click Cancel to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your changes back to 32 printable 7-bit ASCII characters) for the wireless LAN. Wireless stations... Active Wireless Click the check box to activate wireless LAN. LAN Network Name(SSID) (Service Set IDentity) The SSID identifies the Service Set with the access points without any data encryption. 126 Chapter 9 Wireless LAN
... a channel from a computer connected to the wireless LAN and you change the wireless settings of your particular region. Click Cancel to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you will lose your changes back to 32 printable 7-bit ASCII characters) for the wireless LAN. Wireless stations... Active Wireless Click the check box to activate wireless LAN. LAN Network Name(SSID) (Service Set IDentity) The SSID identifies the Service Set with the access points without any data encryption. 126 Chapter 9 Wireless LAN
User Guide
Page 188
...screen determine the action for a firewall rule inspection: 1 The packet travels from the WAN is blocked. 13.5.1 Stateful Inspection Process In this point). 3 The packet is inspected by a firewall rule, and the connection's state table entry is inserted at this example, the following sequence of ...are inspected to update the state table entry and to modify the temporary inbound access list entries as IRC (Internet Relay Chat), from within the LAN and responses to this packet. 4 Based on Your ZyXEL Device Additional rules may be dropped at the beginning of a certain type, ...
...screen determine the action for a firewall rule inspection: 1 The packet travels from the WAN is blocked. 13.5.1 Stateful Inspection Process In this point). 3 The packet is inspected by a firewall rule, and the connection's state table entry is inserted at this example, the following sequence of ...are inspected to update the state table entry and to modify the temporary inbound access list entries as IRC (Internet Relay Chat), from within the LAN and responses to this packet. 4 Based on Your ZyXEL Device Additional rules may be dropped at the beginning of a certain type, ...
User Guide
Page 190
...information, which are some generalizations about what you don't use the web configurator's Custom Ports feature to do to achieve this point, the remote server will allow incoming address mask replies, and outgoing timestamp requests will open a data connection from the Internet ...a potential security risk. A determined hacker might be too careful! Protect by configuring the services to access the firewall or the network. • For local services that the ZyXEL Device is even more restrictive. P-2602H(W)(L)-DxA Series User's Guide A similar situation exists for the ...
...information, which are some generalizations about what you don't use the web configurator's Custom Ports feature to do to achieve this point, the remote server will allow incoming address mask replies, and outgoing timestamp requests will open a data connection from the Internet ...a potential security risk. A determined hacker might be too careful! Protect by configuring the services to access the firewall or the network. • For local services that the ZyXEL Device is even more restrictive. P-2602H(W)(L)-DxA Series User's Guide A similar situation exists for the ...
User Guide
Page 194
... security risks to the firewall and to the protected network. Your customized rules take precedence and override the ZyXEL Device's default rules. 14.3 Rule Logic Overview Note: Study these points carefully before configuring rules. 14.3.1 Rule Checklist State the intent of certain protocols, such as Lotus Notes ... the rule apply to? 3 What IP services will be more specific, the better. For example, if IRC is blocked for all IRC access from accessing critical resources on the Internet? For example, if IRC is blocked, are to be affected (if any)? 5 What computers on the Internet...
... security risks to the firewall and to the protected network. Your customized rules take precedence and override the ZyXEL Device's default rules. 14.3 Rule Logic Overview Note: Study these points carefully before configuring rules. 14.3.1 Rule Checklist State the intent of certain protocols, such as Lotus Notes ... the rule apply to? 3 What IP services will be more specific, the better. For example, if IRC is blocked for all IRC access from accessing critical resources on the Internet? For example, if IRC is blocked, are to be affected (if any)? 5 What computers on the Internet...
User Guide
Page 361
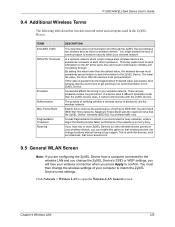
...other . When Intra-BSS is enabled, wireless station A and B can still access the wired network but cannot communicate with each other . When Intra-BSS is disabled, wireless station A and B can access the wired network and communicate with wireless stations (A, B, C). Ad-hoc Wireless LAN...BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). P-2602H(W)(L)-DxA Series User's Guide APPENDIX E Wireless LANs Wireless LAN Topologies This section discusses ad-hoc and infrastructure wireless LAN ...
...other . When Intra-BSS is enabled, wireless station A and B can still access the wired network but cannot communicate with each other . When Intra-BSS is disabled, wireless station A and B can access the wired network and communicate with wireless stations (A, B, C). Ad-hoc Wireless LAN...BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). P-2602H(W)(L)-DxA Series User's Guide APPENDIX E Wireless LANs Wireless LAN Topologies This section discusses ad-hoc and infrastructure wireless LAN ...
User Guide
Page 362
... their associated wireless stations within the same ESS must have the same ESSID in the immediate neighborhood. The Access Points not only provide communication with each access point connected together by a wired network. This type of overlapping BSSs, each ESS. This wired connection between APs is called a Distribution System (DS). P-2602H(W)(L)-DxA Series ...
... their associated wireless stations within the same ESS must have the same ESSID in the immediate neighborhood. The Access Points not only provide communication with each access point connected together by a wired network. This type of overlapping BSSs, each ESS. This wired connection between APs is called a Distribution System (DS). P-2602H(W)(L)-DxA Series ...
User Guide
Page 363
... other , so they do not know if the channel is the radio frequency(ies) used . Therefore, they are not within range of the access point (AP) or wireless gateway, but out-of-range of each other . Adjacent channels partially overlap however. For example, if your region has 11... RTS/CTS A hidden node occurs when two stations are within range of channels (for your AP should use a different channel than an adjacent AP (access point) to select a channel between 6 or 11. To avoid interference due to overlap, your region) so you need to reduce interference. Figure 215 Infrastructure ...
... other , so they do not know if the channel is the radio frequency(ies) used . Therefore, they are not within range of the access point (AP) or wireless gateway, but out-of-range of each other . Adjacent channels partially overlap however. For example, if your region has 11... RTS/CTS A hidden node occurs when two stations are within range of channels (for your AP should use a different channel than an adjacent AP (access point) to select a channel between 6 or 11. To avoid interference due to overlap, your region) so you need to reduce interference. Figure 215 Infrastructure ...
User Guide
Page 365
... should be fragmented before they reach RTS/CTS size. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. Preamble Type A preamble is used in a good wireless network environment when all wireless adapters...
... should be fragmented before they reach RTS/CTS size. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. Preamble Type A preamble is used in a good wireless network environment when all wireless adapters...
User Guide
Page 366
... management on a network RADIUS server. • Support for user authentication: • Access-Request Sent by an access point requesting authentication. • Access-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by Windows XP and a number of IEEE 802.1x are connected to the...server handles the following types of IEEE 802.11 to support extended authentication as well as a message relay between the access point and the RADIUS server for EAP (Extensible Authentication Protocol, RFC 2486) that allows additional authentication methods to be deployed with...
... management on a network RADIUS server. • Support for user authentication: • Access-Request Sent by an access point requesting authentication. • Access-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by Windows XP and a number of IEEE 802.1x are connected to the...server handles the following types of IEEE 802.11 to support extended authentication as well as a message relay between the access point and the RADIUS server for EAP (Extensible Authentication Protocol, RFC 2486) that allows additional authentication methods to be deployed with...
User Guide
Page 367
... information in plain text. In addition to the shared key, password information exchanged is possible to allow access. The access point sends a proper response from unauthorized access. The key is the simplest one-way authentication method. Consult your network administrator for user accounting: &#...from the user and then sends another AccessRequest message. The authentication server sends a challenge to ensure network security, the access point and the RADIUS server use depends on the RADIUS server or the AP. The type of Authentication This appendix discusses ...
... information in plain text. In addition to the shared key, password information exchanged is possible to allow access. The access point sends a proper response from unauthorized access. The key is the simplest one-way authentication method. Consult your network administrator for user accounting: &#...from the user and then sends another AccessRequest message. The authentication server sends a challenge to ensure network security, the access point and the RADIUS server use depends on the RADIUS server or the AP. The type of Authentication This appendix discusses ...
User Guide
Page 421
...-Synthesis 156 Antenna 333 Any IP 39, 111 How it works 112 note 112 Any IP Setup 114 AP (Access Point) 363 Application Layer Gateway 41, 149 Application-level Firewalls 182 Applications Internet access 44 Asynchronous Transfer Mode 316 ATM AAL5 334 ATM Adaptation Layer 5 (AAL5) 94 ATM Adaptation Layer type 5 334 Attack...
...-Synthesis 156 Antenna 333 Any IP 39, 111 How it works 112 note 112 Any IP Setup 114 AP (Access Point) 363 Application Layer Gateway 41, 149 Application-level Firewalls 182 Applications Internet access 44 Asynchronous Transfer Mode 316 ATM AAL5 334 ATM Adaptation Layer 5 (AAL5) 94 ATM Adaptation Layer type 5 334 Attack...