User Guide
Page 7
... antenna(s). • If you to a power outlet by itself; Your product is marked with general waste. NWA1100-N User's Guide 7 This device meets ETSI and FCC certification requirements when using the included antenna(s).
... antenna(s). • If you to a power outlet by itself; Your product is marked with general waste. NWA1100-N User's Guide 7 This device meets ETSI and FCC certification requirements when using the included antenna(s).
User Guide
Page 9
Contents Overview Contents Overview User's Guide ...17 Introducing the NWA ...19 Introducing the Web Configurator 29 Status Screens ...33 Tutorial ...37 Technical Reference ...53 System Screens ...55 Wireless Settings Screen ...60 SSID Screen ...79 Wireless Security Screen ...85 RADIUS Screen ...99 MAC Filter Screen ...102 IP Screen ...105 Remote Management ...109 Certificate Screen ...119 Log Screens ...123 Maintenance ...129 Troubleshooting ...137 NWA1100-N User's Guide 9
Contents Overview Contents Overview User's Guide ...17 Introducing the NWA ...19 Introducing the Web Configurator 29 Status Screens ...33 Tutorial ...37 Technical Reference ...53 System Screens ...55 Wireless Settings Screen ...60 SSID Screen ...79 Wireless Security Screen ...85 RADIUS Screen ...99 MAC Filter Screen ...102 IP Screen ...105 Remote Management ...109 Certificate Screen ...119 Log Screens ...123 Maintenance ...129 Troubleshooting ...137 NWA1100-N User's Guide 9
User Guide
Page 15
....2 What You Can Do in this Chapter 119 13.3 What You Need To Know 119 13.4 Certificate Screen ...120 13.5 Technical Reference ...120 13.5.1 Private-Public Certificates 120 13.5.2 Certification Authorities 121 13.5.3 Checking the Fingerprint of a Certificate on Your Computer 121 Chapter 14 Log Screens ...123 14.1 Overview ...123 14.2 What You Can...
....2 What You Can Do in this Chapter 119 13.3 What You Need To Know 119 13.4 Certificate Screen ...120 13.5 Technical Reference ...120 13.5.1 Private-Public Certificates 120 13.5.2 Certification Authorities 121 13.5.3 Checking the Fingerprint of a Certificate on Your Computer 121 Chapter 14 Log Screens ...123 14.1 Overview ...123 14.2 What You Can...
User Guide
Page 31
... advanced features such as SYSTEM (General, Password and Time), WIRELESS (Wireless Settings, SSID, Security, RADIUS, MAC Filter), IP, REMOTE MGNT (Telnet, FTP, WWW and SNMP), CERTIFICATES, and LOGS (View Log and Log Settings). • Click MAINTENANCE to verify that the configuration has been updated. Figure 14 Status Screen of the Web...
... advanced features such as SYSTEM (General, Password and Time), WIRELESS (Wireless Settings, SSID, Security, RADIUS, MAC Filter), IP, REMOTE MGNT (Telnet, FTP, WWW and SNMP), CERTIFICATES, and LOGS (View Log and Log Settings). • Click MAINTENANCE to verify that the configuration has been updated. Figure 14 Status Screen of the Web...
User Guide
Page 119
... You Can Do in PFX PKCS#12 file format. Key distribution is further encrypted with a password. Figure 58 Certificates Example In the figure above, the NWA (Z) checks the identity of authenticating wireless clients. A certificate contains the certificate owner's identity and public key. NWA1100-N User's Guide 119 It gives background information about public-key...
... You Can Do in PFX PKCS#12 file format. Key distribution is further encrypted with a password. Figure 58 Certificates Example In the figure above, the NWA (Z) checks the identity of authenticating wireless clients. A certificate contains the certificate owner's identity and public key. NWA1100-N User's Guide 119 It gives background information about public-key...
User Guide
Page 120
... the Browse button to the NWA. 13.5 Technical Reference This section provides technical background information about the topics covered in this chapter. 13.5.1 Private-Public Certificates When using public-key cryptology for authentication, each host has two keys. Import Click this button to upload the previously-saved...
... the Browse button to the NWA. 13.5 Technical Reference This section provides technical background information about the topics covered in this chapter. 13.5.1 Private-Public Certificates When using public-key cryptology for authentication, each host has two keys. Import Click this button to upload the previously-saved...
User Guide
Page 121
...as it is from Tim can read it and verify whether it should look. Figure 60 Certificates on Your Computer A certificate's fingerprints are commercial certification authorities like a handwritten signature (in fact, certificates are often referred to Jenny. When people know what your signature exactly as "digital signatures... someone else. There are message digests calculated using the MD5 or SHA1 algorithms. The following procedure describes how to check a certificate's fingerprint to where you , or by you have been able to come from Tim, and that anyone else along the way...
...as it is from Tim can read it and verify whether it should look. Figure 60 Certificates on Your Computer A certificate's fingerprints are commercial certification authorities like a handwritten signature (in fact, certificates are often referred to Jenny. When people know what your signature exactly as "digital signatures... someone else. There are message digests calculated using the MD5 or SHA1 algorithms. The following procedure describes how to check a certificate's fingerprint to where you , or by you have been able to come from Tim, and that anyone else along the way...
User Guide
Page 122
The secure method may vary according to the Thumbprint Algorithm and Thumbprint fields. Possible examples would be over the telephone or through an HTTPS connection. 122 NWA1100-N User's Guide Click the Details tab and scroll down to your situation. Chapter 13 Certificate Screen 3 Double-click the certificate's icon to verify that the certificate owner has the same information in the Thumbprint Algorithm and Thumbprint fields. Figure 61 Certificate Details 4 Use a secure method to open the Certificate window.
The secure method may vary according to the Thumbprint Algorithm and Thumbprint fields. Possible examples would be over the telephone or through an HTTPS connection. 122 NWA1100-N User's Guide Click the Details tab and scroll down to your situation. Chapter 13 Certificate Screen 3 Double-click the certificate's icon to verify that the certificate owner has the same information in the Thumbprint Algorithm and Thumbprint fields. Figure 61 Certificate Details 4 Use a secure method to open the Certificate window.
User Guide
Page 141
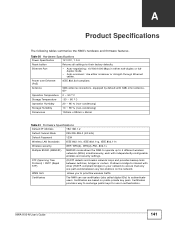
...-configurable wireless and security settings. Ethernet Port • Auto-negotiating: 10/100/1000 Mbps in authentication. Certificates provide a way to exchange public keys for use certificates (also called digital IDs) to ensure that only one path exists between switches, bridges or routers. WMM...network loops and provides backup links between any two stations on public-private key pairs. NWA1100-N User's Guide 141 Certificates are based on the network. Certificates The NWA can use in either half-duplex or fullduplex mode. • Auto-crossover: Use either crossover or...
...-configurable wireless and security settings. Ethernet Port • Auto-negotiating: 10/100/1000 Mbps in authentication. Certificates provide a way to exchange public keys for use certificates (also called digital IDs) to ensure that only one path exists between switches, bridges or routers. WMM...network loops and provides backup links between any two stations on public-private key pairs. NWA1100-N User's Guide 141 Certificates are based on the network. Certificates The NWA can use in either half-duplex or fullduplex mode. • Auto-crossover: Use either crossover or...
User Guide
Page 197
...-MD5, EAP-TLS, EAP-TTLS, PEAP and LEAP. The type of user authentication. The access point sends a proper response from a certificate authority (CA). EAP (Extensible Authentication Protocol) is an authentication protocol that runs on the RADIUS server and an intermediary AP(s) that it has... started or stopped accounting. A certificate (also called digital IDs) can be used to protect the network from unauthorized access. Appendix E Wireless LANs RADIUS is a simple package ...
...-MD5, EAP-TLS, EAP-TTLS, PEAP and LEAP. The type of user authentication. The access point sends a proper response from a certificate authority (CA). EAP (Extensible Authentication Protocol) is an authentication protocol that runs on the RADIUS server and an intermediary AP(s) that it has... started or stopped accounting. A certificate (also called digital IDs) can be used to protect the network from unauthorized access. Appendix E Wireless LANs RADIUS is a simple package ...
User Guide
Page 198
...WEP encryption keys for mutual authentication. You must be stored. The exchange of the server, the client sends a different certificate to impersonate an authentication server as MD5 authentication method does not perform mutual authentication. EAP-GTC is the simplest one-way ...through the secure connection, thus client identity is performed. 198 NWA1100-N User's Guide The wireless client 'proves' that uses certificates for client authentication. This key expires when the wireless connection times out, disconnects or reauthentication times out. However, PEAP only ...
...WEP encryption keys for mutual authentication. You must be stored. The exchange of the server, the client sends a different certificate to impersonate an authentication server as MD5 authentication method does not perform mutual authentication. EAP-GTC is the simplest one-way ...through the secure connection, thus client identity is performed. 198 NWA1100-N User's Guide The wireless client 'proves' that uses certificates for client authentication. This key expires when the wireless connection times out, disconnects or reauthentication times out. However, PEAP only ...
User Guide
Page 199
...Message authentication code Protocol (CCMP). The following table is a comparison of the features of the IEEE 802.11i standard. Client No Yes Certificate - If both an AP and the wireless clients support WPA2 and you have an external RADIUS server or not. Key differences between ..., but offers stronger encryption than TKIP with Advanced Encryption Standard (AES) in the Counter mode with Dynamic WEP Key Exchange For added security, certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use WPA2-PSK (WPA2-Pre-Shared Key) that uses a 256-bit mathematical algorithm NWA1100...
...Message authentication code Protocol (CCMP). The following table is a comparison of the features of the IEEE 802.11i standard. Client No Yes Certificate - If both an AP and the wireless clients support WPA2 and you have an external RADIUS server or not. Key differences between ..., but offers stronger encryption than TKIP with Advanced Encryption Standard (AES) in the Counter mode with Dynamic WEP Key Exchange For added security, certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use WPA2-PSK (WPA2-Pre-Shared Key) that uses a 256-bit mathematical algorithm NWA1100...
User Guide
Page 237
... described herein without wireless) Federal Communications Commission (FCC) Interference Statement This device complies with products that need Rovi certification. Trademarks This item incorporates copy protection technology that have NAT, and/or 3G. Disclaimers ZyXEL does not assume any liability arising out of the application or use the NWA for STBs that have...
... described herein without wireless) Federal Communications Commission (FCC) Interference Statement This device complies with products that need Rovi certification. Trademarks This item incorporates copy protection technology that have NAT, and/or 3G. Disclaimers ZyXEL does not assume any liability arising out of the application or use the NWA for STBs that have...
User Guide
Page 239
... mini-GBIC slots or laser products, such as fiber-optic transceiver and GPON products) Viewing Certifications 1 Go to http://www.zyxel.com. 2 Select your product on the ZyXEL home page to go to that product's page. 3 Select the certification you wish to view from that may cause harmful interference to radio communications. However, there...
... mini-GBIC slots or laser products, such as fiber-optic transceiver and GPON products) Viewing Certifications 1 Go to http://www.zyxel.com. 2 Select your product on the ZyXEL home page to go to that product's page. 3 Select the certification you wish to view from that may cause harmful interference to radio communications. However, there...
User Guide
Page 242
...act of purchase. Note Repair or replacement, as fiber-optic transceiver and GPON products) Viewing Certifications 1 Go to http://www.zyxel.com. 2 Select your product online to receive e-mail notices of ZyXEL. This warranty is in lieu of all other warranties, express or implied, including any ... due to that product's page. 3 Select the certification you bought the device at www.zyxel.com. 242 NWA1100-N User's Guide Registration Register your product on the ZyXEL home page to go to faulty workmanship and/or materials, ZyXEL will be held liable for indirect or consequential damages...
...act of purchase. Note Repair or replacement, as fiber-optic transceiver and GPON products) Viewing Certifications 1 Go to http://www.zyxel.com. 2 Select your product online to receive e-mail notices of ZyXEL. This warranty is in lieu of all other warranties, express or implied, including any ... due to that product's page. 3 Select the certification you bought the device at www.zyxel.com. 242 NWA1100-N User's Guide Registration Register your product on the ZyXEL home page to go to faulty workmanship and/or materials, ZyXEL will be held liable for indirect or consequential damages...
User Guide
Page 243
... 121 MD5 121 public key 119 SHA1 121 Certification Authority 121 certifications 237, 239 notices 238, 241 viewing 239, 242 Channel 61 channel 193 interference 193 command interface 25 Configuration File format 206 Controlling network access, Ways ... Interval 64, 74 BPDU 77 Bridge 20 Bridge loops 21 Bridge Protocol Data Units (BPDUs) 108 BSS 24, 61, 191 C CA 198 Certificate authentication 119 file format 119 Certificate Authority See CA. Numbers 802.1x-Only 86 802.1x-Static128 86 802.1x-Static64 86 A Access Point 20, 47 access privileges 24...
... 121 MD5 121 public key 119 SHA1 121 Certification Authority 121 certifications 237, 239 notices 238, 241 viewing 239, 242 Channel 61 channel 193 interference 193 command interface 25 Configuration File format 206 Controlling network access, Ways ... Interval 64, 74 BPDU 77 Bridge 20 Bridge loops 21 Bridge Protocol Data Units (BPDUs) 108 BSS 24, 61, 191 C CA 198 Certificate authentication 119 file format 119 Certificate Authority See CA. Numbers 802.1x-Only 86 802.1x-Static128 86 802.1x-Static64 86 A Access Point 20, 47 access privileges 24...
User Guide
Page 244
..., 67, 71, 75 Fragmentation threshold 78 fragmentation threshold 194 FTP 111 I IANA 107, 190 IBSS 191 IEEE 802.11g 195 IEEE 802.1x 62 Import Certificate 120 Independent Basic Service Set See IBSS 191 initialization vector (IV) 200 Internet Assigned Numbers Authority 107 See IANA Internet telephony 24 IP Address 55...
..., 67, 71, 75 Fragmentation threshold 78 fragmentation threshold 194 FTP 111 I IANA 107, 190 IBSS 191 IEEE 802.11g 195 IEEE 802.1x 62 Import Certificate 120 Independent Basic Service Set See IBSS 191 initialization vector (IV) 200 Internet Assigned Numbers Authority 107 See IANA Internet telephony 24 IP Address 55...
User Guide
Page 246
Index preamble mode 195 Preamble Type 64, 67, 71, 74 Pre-Shared Key 87 priorities 83 Private-Public Certificates 120 product registration 242 Protected Extensible Authentication Protocol 87 PSK 87, 200 Reset button 141 RJ-45 Port Pin Assignments 142 Roaming 78 root bridge ...
Index preamble mode 195 Preamble Type 64, 67, 71, 74 Pre-Shared Key 87 priorities 83 Private-Public Certificates 120 product registration 242 Protected Extensible Authentication Protocol 87 PSK 87, 200 Reset button 141 RJ-45 Port Pin Assignments 142 Roaming 78 root bridge ...