User Guide
Page 5
... 11 Figure 5-7: WEP Security Settings 12 Figure 5-8: WPA Security Settings 12 Figure 5-9: Choose the Range Expander 13 Figure 5-10: Enter the Password 13 Figure 5-11: Configure Network Address Settings 14 Figure 5-12: MAC Address of Access Point or Wireless Router (WRE54G v1 Only) 14 Figure 5-13: Confirmation Screen 15 Figure 5-14: Congratulations Screen 15 Figure 5-15...
... 11 Figure 5-7: WEP Security Settings 12 Figure 5-8: WPA Security Settings 12 Figure 5-9: Choose the Range Expander 13 Figure 5-10: Enter the Password 13 Figure 5-11: Configure Network Address Settings 14 Figure 5-12: MAC Address of Access Point or Wireless Router (WRE54G v1 Only) 14 Figure 5-13: Confirmation Screen 15 Figure 5-14: Congratulations Screen 15 Figure 5-15...
User Guide
Page 14
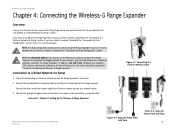
...network port of a networked computer, and enter the Range Expander's IP address, 192.168.1.240. Figure 4-1: Connecting the Ethernet Network Cable Chapter 4: Connecting the Wireless-G Range Expander Overview Figure 4-2: Using the Power Plate with Cord ..."Chapter 5: Setting Up the Wireless-G Range Expander." NOTE TO ADVANCED USERS:If you want to configure the Range Expander using your network router. 3. Wireless-G Range Expander Chapter 4: Connecting the Wireless-G Range Expander Overview Linksys recommends that you connect the Range Expander to your network. Configure your...
...network port of a networked computer, and enter the Range Expander's IP address, 192.168.1.240. Figure 4-1: Connecting the Ethernet Network Cable Chapter 4: Connecting the Wireless-G Range Expander Overview Figure 4-2: Using the Power Plate with Cord ..."Chapter 5: Setting Up the Wireless-G Range Expander." NOTE TO ADVANCED USERS:If you want to configure the Range Expander using your network router. 3. Wireless-G Range Expander Chapter 4: Connecting the Wireless-G Range Expander Overview Linksys recommends that you connect the Range Expander to your network. Configure your...
User Guide
Page 20
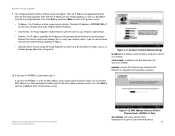
.... Chapter 5: Setting Up the Wireless-G Range Expander Running the Setup Wizard Figure 5-12: MAC Address of Access Point or Wireless Router (WRE54G v1 Only) mac address: the unique address that determines the size of the access point or wireless router. The Range Expander's Subnet Mask must be the IP address of your network router). You can assign the Range Expander any name up to...
.... Chapter 5: Setting Up the Wireless-G Range Expander Running the Setup Wizard Figure 5-12: MAC Address of Access Point or Wireless Router (WRE54G v1 Only) mac address: the unique address that determines the size of the access point or wireless router. The Range Expander's Subnet Mask must be the IP address of your network router). You can assign the Range Expander any name up to...
User Guide
Page 23
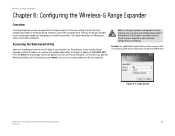
... a way to be configured through your web browser and Web-based Utility. Wireless-G Range Expander Chapter 6: Configuring the Wireless-G Range Expander Overview The Range Expander has been designed to look at and interact with the Auto configuration button or the Setup Wizard. However, if you kept the Range Expander's default IP address or used the Auto configuration button, the default IP...
... a way to be configured through your web browser and Web-based Utility. Wireless-G Range Expander Chapter 6: Configuring the Wireless-G Range Expander Overview The Range Expander has been designed to look at and interact with the Auto configuration button or the Setup Wizard. However, if you kept the Range Expander's default IP address or used the Auto configuration button, the default IP...
User Guide
Page 24
...first screen that runs a networking device Chapter 5: Configuring the Wireless-G Range Expander 18 The Setup Tab You may assign any keyboard character. Unique, memorable names are helpful, especially if you are finished. The IP address must be the same as described here and click Save ... you are employing multiple Range Expanders on the network. • SSID. This allows the SSID to a unique name. • SSID Broadcast. This will be broadcast on your changes. Firmware can be upgraded from the default name, linksys, to be reduced. Wireless The selections under this ...
...first screen that runs a networking device Chapter 5: Configuring the Wireless-G Range Expander 18 The Setup Tab You may assign any keyboard character. Unique, memorable names are helpful, especially if you are finished. The IP address must be the same as described here and click Save ... you are employing multiple Range Expanders on the network. • SSID. This allows the SSID to a unique name. • SSID Broadcast. This will be broadcast on your changes. Firmware can be upgraded from the default name, linksys, to be reduced. Wireless The selections under this ...
User Guide
Page 31
...technique developed by the military for example, must maintain contact with the original access point or whether it and its address. This bit pattern is DSSS? First, it is in reliable, secure, mission-critical communications systems. It is ...wireless network must make sure that links nodes. In such a system, the user's end node undertakes a search for unlicensed use in touch with the wireless network even when not actually transmitting data. Upon finding a new access point, it undertakes a new search. Spectrum in the network. Wireless-G Range Expander...
...technique developed by the military for example, must maintain contact with the original access point or whether it and its address. This bit pattern is DSSS? First, it is in reliable, secure, mission-critical communications systems. It is ...wireless network must make sure that links nodes. In such a system, the user's end node undertakes a search for unlicensed use in touch with the wireless network even when not actually transmitting data. Upon finding a new access point, it undertakes a new search. Spectrum in the network. Wireless-G Range Expander...
User Guide
Page 32
...-fold protection. Can Linksys Wireless products support file and printer sharing? WEP is no way to the network, the MAC address of your environment. This will inhibit the signal and reduce range. On the software side, the wireless series offers the encryption function (WEP) to operate each one another will create signal loss. Wireless-G Range Expander (or chipping...
...-fold protection. Can Linksys Wireless products support file and printer sharing? WEP is no way to the network, the MAC address of your environment. This will inhibit the signal and reduce range. On the software side, the wireless series offers the encryption function (WEP) to operate each one another will create signal loss. Wireless-G Range Expander (or chipping...
User Guide
Page 33
Wireless-G Range Expander Appendix B: Wireless Security Linksys wants to make it is the only person who can take (as shown in mind whenever you are setting up or using your part for ... take : Change the administrator's password regularly. Security Precautions The following in this may reduce your network performance. 7. Enable MAC Address Filtering. 5. Please note that information. With every wireless networking device you use, keep the following is a complete list of Linksys products provide several network security features, but they require specific action on your...
Wireless-G Range Expander Appendix B: Wireless Security Linksys wants to make it is the only person who can take (as shown in mind whenever you are setting up or using your part for ... take : Change the administrator's password regularly. Security Precautions The following in this may reduce your network performance. 7. Enable MAC Address Filtering. 5. Please note that information. With every wireless networking device you use, keep the following is a complete list of Linksys products provide several network security features, but they require specific action on your...
User Guide
Page 34
...Pre-Shared Key and RADIUS. Make it harder for authentication and the use . Wireless networking products come with certain MAC Addresses. Change your network. Wired Equivalent Privacy (WEP) is "linksys".) Hackers know these defaults and can check these against hackers, and AES (Advanced ...networking products you to provide access to break in your wireless network MUST use the same encryption method and encryption key or your network with a random MAC Address. Change your wireless network. Wireless-G Range Expander SSID. While this can be more difficult. This makes...
...Pre-Shared Key and RADIUS. Make it harder for authentication and the use . Wireless networking products come with certain MAC Addresses. Change your network. Wired Equivalent Privacy (WEP) is "linksys".) Hackers know these defaults and can check these against hackers, and AES (Advanced ...networking products you to provide access to break in your wireless network MUST use the same encryption method and encryption key or your network with a random MAC Address. Change your wireless network. Wireless-G Range Expander SSID. While this can be more difficult. This makes...
User Guide
Page 35
...you are transmitting sensitive data over your mind at ease while you are enjoying the most flexible and convenient technology Linksys has to the Router or other device.) First, select the type of algorithm, TKIP or AES, enter ... and the server. Enter the RADIUS server's IP Address and port number, along with a key shared between the device and the server. Appendix B: Wireless Security 29 Security Threats Facing Wireless Networks WPA used . Last, enter a Group Key... used when a RADIUS server is connected to offer. WPA RADIUS. Wireless-G Range Expander WPA Pre-Shared Key.
...you are transmitting sensitive data over your mind at ease while you are enjoying the most flexible and convenient technology Linksys has to the Router or other device.) First, select the type of algorithm, TKIP or AES, enter ... and the server. Enter the RADIUS server's IP Address and port number, along with a key shared between the device and the server. Appendix B: Wireless Security 29 Security Threats Facing Wireless Networks WPA used . Last, enter a Group Key... used when a RADIUS server is connected to offer. WPA RADIUS. Wireless-G Range Expander WPA Pre-Shared Key.
User Guide
Page 39
Wireless-G Range Expander Download - DSL (Digital Subscriber Line) - Dynamic IP Address - Ethernet - Finger - Firmware - A device that runs a networking device. ISM band - A temporary IP address assigned by a DHCP server. The programming code that interconnects networks with different, incompatible communications protocols. Gateway - Hardware - A wireless network that is placed on the World Wide Web. The address...) - IP Address - Appendix E: Glossary 33 Frequency transmission with an e-mail address. Encoding data transmitted in wireless transmissions. LAN ...
Wireless-G Range Expander Download - DSL (Digital Subscriber Line) - Dynamic IP Address - Ethernet - Finger - Firmware - A device that runs a networking device. ISM band - A temporary IP address assigned by a DHCP server. The programming code that interconnects networks with different, incompatible communications protocols. Gateway - Hardware - A wireless network that is placed on the World Wide Web. The address...) - IP Address - Appendix E: Glossary 33 Frequency transmission with an e-mail address. Encoding data transmitted in wireless transmissions. LAN ...
User Guide
Page 40
... to provide user access to eight wires. Server - Instructions for more reliable and secure data transmission. Wireless-G Range Expander MAC (Media Access Control) Address - A networking method of data sharing, storage, and/or transmission between users. SOHO (Small Office/Home... unique address that uses an authentication server to each networking device. mIRC - RADIUS (Remote Authentication Dial-In User Service) - Appendix E: Glossary 34 a unit of data sent over a network. Network - Mbps (MegaBits Per Second) - A unit of measurement for Linksys products...
... to provide user access to eight wires. Server - Instructions for more reliable and secure data transmission. Wireless-G Range Expander MAC (Media Access Control) Address - A networking method of data sharing, storage, and/or transmission between users. SOHO (Small Office/Home... unique address that uses an authentication server to each networking device. mIRC - RADIUS (Remote Authentication Dial-In User Service) - Appendix E: Glossary 34 a unit of data sent over a network. Network - Mbps (MegaBits Per Second) - A unit of measurement for Linksys products...
User Guide
Page 41
... number of a network. Your wireless network's name. A set of a file located on a wireless network for accessing remote PCs. a wireless security protocol using TKIP (Temporal Key Integrity Protocol) encryption, which can be used for greater security. Static IP Address - To replace existing software or firmware with a RADIUS server. Transmission Rate. Wireless-G Range Expander SSID (Service Set IDentifier) - WEP...
... number of a network. Your wireless network's name. A set of a file located on a wireless network for accessing remote PCs. a wireless security protocol using TKIP (Temporal Key Integrity Protocol) encryption, which can be used for greater security. Static IP Address - To replace existing software or firmware with a RADIUS server. Transmission Rate. Wireless-G Range Expander SSID (Service Set IDentifier) - WEP...