ThinkCentre A51 Memory - Lenovo
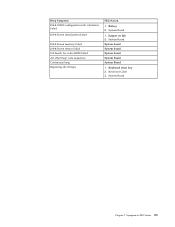
ThinkCentre A51 Memory

View Results Below
Free Lenovo ThinkCentre A51 manuals!
Problems with Lenovo ThinkCentre A51?
Ask a Question
Free Lenovo ThinkCentre A51 manuals!
Problems with Lenovo ThinkCentre A51?
Ask a Question
Related Manual Pages
Similar Questions
What Type Of Memory Is Needed To Upgrade A Lenovo Ideacentre Q100 10027
I want to go from 1gig RAM to at least 2, maybe more - what type of memory - how many slots
I want to go from 1gig RAM to at least 2, maybe more - what type of memory - how many slots
(Posted by lenovo42642 11 years ago)
I Need To Increase The Memory Of My Lenovo 300h.
I need to increase th3 memory of my lenovo 300H. I am not sure what kind of memory it takes. I also ...
I need to increase th3 memory of my lenovo 300H. I am not sure what kind of memory it takes. I also ...
(Posted by arshadhrashid 13 years ago)
K300 Memory Upgrade
Am attempting to upgrade memory from 4GB to 8GB. No matter what combo of the 4 2GB dimms I install, ...
Am attempting to upgrade memory from 4GB to 8GB. No matter what combo of the 4 2GB dimms I install, ...
(Posted by clover4 13 years ago)