Wireless Security
Page 1
...the access pipe is organized as to where the security vulnerabilities lie and what can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity... ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: People and corporations are using wireless technologies at the pieces of the "pipe" of access from the device to the corporate firewall in...
...the access pipe is organized as to where the security vulnerabilities lie and what can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity... ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: People and corporations are using wireless technologies at the pieces of the "pipe" of access from the device to the corporate firewall in...
Wireless Security
Page 2
...Group, L.P. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of Microsoft Corporation in the documentation accompanying such products. and/or other countries. All other countries. THE ENTIRE RISK ARISING OUT OF THE USE OF THIS INFORMATION REMAINS WITH RECIPIENT. Wireless Security White ...tested. Nothing herein should be trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. This test is provided "AS IS" WITHOUT WARRANTY OF ANY KIND. Wireless Security White Paper 2 Notice The information in this publication is subject to ...
...Group, L.P. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of Microsoft Corporation in the documentation accompanying such products. and/or other countries. All other countries. THE ENTIRE RISK ARISING OUT OF THE USE OF THIS INFORMATION REMAINS WITH RECIPIENT. Wireless Security White ...tested. Nothing herein should be trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. This test is provided "AS IS" WITHOUT WARRANTY OF ANY KIND. Wireless Security White Paper 2 Notice The information in this publication is subject to ...
Wireless Security
Page 3
... concerns about vulnerability to security breaches. A significant part of wireless network security overlaps with the machines they use to gain access to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, ... in part because many users are concerned. For complete wireless and mobile security solutions, please contact Compaq Global Services at http://www.compaq.com/services/index_infrastructure.html. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers...
... concerns about vulnerability to security breaches. A significant part of wireless network security overlaps with the machines they use to gain access to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, ... in part because many users are concerned. For complete wireless and mobile security solutions, please contact Compaq Global Services at http://www.compaq.com/services/index_infrastructure.html. Wireless Security White Paper 3 Introduction Wireless networks connect computers in offices or homes to other computers...
Wireless Security
Page 4
.... Security at critical junctures along the pipe, and measures that authorizes identified persons to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - WLAN, WPAN, WWAN, broadband, dial-up ) to the point where access is ...-- WLAN hubs, telecommunications companies 4. Assuring that entity could have permission to do so can be taken to address those issues. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are :...
.... Security at critical junctures along the pipe, and measures that authorizes identified persons to see protected information and engage in wireless connectivity technologies (Connectivity Technologies) - WLAN, WPAN, WWAN, broadband, dial-up ) to the point where access is ...-- WLAN hubs, telecommunications companies 4. Assuring that entity could have permission to do so can be taken to address those issues. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are :...
Wireless Security
Page 5
...it is the mobile telephone). Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Figure 1 represent the pivotal points of data transfer. The horizontal... lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired one place to the next...
...it is the mobile telephone). Device Security Despite the growing popularity of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Figure 1 represent the pivotal points of data transfer. The horizontal... lines represent data traveling from unauthorized access behind the firewall is not a wireless security concern, but a wired one place to the next...
Wireless Security
Page 6
...following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. The only way for such devices. Companies treat the devices as critical resources by defining usage...of some handheld access devices, and lack of enforcement of notebook computers to such devices. If permitted to observe the user's computing activity for . Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in the ...
...following subsections describe security problems specific to mobile access devices, the first link in the pipe on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. The only way for such devices. Companies treat the devices as critical resources by defining usage...of some handheld access devices, and lack of enforcement of notebook computers to such devices. If permitted to observe the user's computing activity for . Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in the ...
Wireless Security
Page 7
...be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with each key require repeated presses to type certain letters. Users often choose passwords that do not perform such processing themselves... further consideration is to endure the trade-off in convenience and make password protection more complex ones offer relatively strong encryption. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security ...
...be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with each key require repeated presses to type certain letters. Users often choose passwords that do not perform such processing themselves... further consideration is to endure the trade-off in convenience and make password protection more complex ones offer relatively strong encryption. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security ...
Wireless Security
Page 8
...the decryption of authentication as requirements for Compaq Armada and Evo notebook computers. The information then goes through ...PC in the Fingerprint Identification Reader captures an image of the fingerprint of strangers. Biometric Technologies Biometric devices use physical traits such as Windows 2000 offer an encrypted file system, this is not yet common on mobile platforms. If the data on Compaq FIT, see http://www.compaq.com/products/notebooks... Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint...
...the decryption of authentication as requirements for Compaq Armada and Evo notebook computers. The information then goes through ...PC in the Fingerprint Identification Reader captures an image of the fingerprint of strangers. Biometric Technologies Biometric devices use physical traits such as Windows 2000 offer an encrypted file system, this is not yet common on mobile platforms. If the data on Compaq FIT, see http://www.compaq.com/products/notebooks... Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint...
Wireless Security
Page 9
... and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. For example, they roam. Wireless Security White Paper 9 Key features of F-Secure FileCrypto for PocketPC are the following: •...Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can send and receive e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage....
... and the wired lines that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. For example, they roam. Wireless Security White Paper 9 Key features of F-Secure FileCrypto for PocketPC are the following: •...Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can send and receive e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage....
Wireless Security
Page 10
... follows and detailed papers that uses high-frequency radio waves rather than wires to a wireless connection. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. It is a type of LAN that...extension or alternative to a wired LAN within a building or campus. Figure 2 illustrates a WLAN. A brief description of a customer. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, access corporate data, the ...
... follows and detailed papers that uses high-frequency radio waves rather than wires to a wireless connection. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. It is a type of LAN that...extension or alternative to a wired LAN within a building or campus. Figure 2 illustrates a WLAN. A brief description of a customer. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, access corporate data, the ...
Wireless Security
Page 11
...(TDMA) were developed in its market. The official names for mobile telephones. They can use infrared technology. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM..., is a TDMA technology. GSM is the most widely used there. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. The Global System for point-to peripheral devices such as printers or other personal...
...(TDMA) were developed in its market. The official names for mobile telephones. They can use infrared technology. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM..., is a TDMA technology. GSM is the most widely used there. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. The Global System for point-to peripheral devices such as printers or other personal...
Wireless Security
Page 12
...control how far radio waves travel over an unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Compaq offers an optimized MS Exchange e-mail solution with InfoWave. Because all the ...(impersonation, which violates authentication and possibly integrity), or even shutting the network down (sabotage, which is available. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. Such eavesdropping and possible theft of security) are available...
...control how far radio waves travel over an unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail, enterprise intranet and corporate e-mail. Compaq offers an optimized MS Exchange e-mail solution with InfoWave. Because all the ...(impersonation, which violates authentication and possibly integrity), or even shutting the network down (sabotage, which is available. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. Such eavesdropping and possible theft of security) are available...
Wireless Security
Page 13
...encryption native to casual or not-so-casual observers. Smaller companies have PKI support for the wireless exchange of information over public highways and suffer the potential for a wireless network. Two key technologies make such information unreadable or invisible. that is titled "Eavesdropping," ... cryptography. The following sub-sections discuss these vulnerabilities in which public key cryptography is built is sent over a wireless network must travel over networks involve the use of public key cryptography, also known as commented above, eavesdropping can lead to observers...
...encryption native to casual or not-so-casual observers. Smaller companies have PKI support for the wireless exchange of information over public highways and suffer the potential for a wireless network. Two key technologies make such information unreadable or invisible. that is titled "Eavesdropping," ... cryptography. The following sub-sections discuss these vulnerabilities in which public key cryptography is built is sent over a wireless network must travel over networks involve the use of public key cryptography, also known as commented above, eavesdropping can lead to observers...
Wireless Security
Page 14
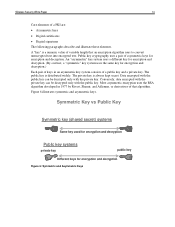
... public key. A "key" is a numeric value of that an encryption algorithm uses to convert unencrypted text into encrypted text. The private key is distributed widely. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. Figure 6 illustrates symmetric and asymmetric keys.
... public key. A "key" is a numeric value of that an encryption algorithm uses to convert unencrypted text into encrypted text. The private key is distributed widely. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption. Figure 6 illustrates symmetric and asymmetric keys.
Wireless Security
Page 15
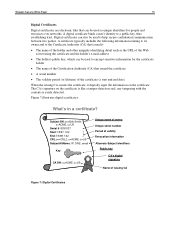
... the certificate and the holder's e-mail address • The holder's public key, which can be used to a public key, thus establishing trust. What's in a certificate? Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used to encrypt sensitive information for people and resources over networks...
... the certificate and the holder's e-mail address • The holder's public key, which can be used to a public key, thus establishing trust. What's in a certificate? Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that can be used to encrypt sensitive information for people and resources over networks...
Wireless Security
Page 16
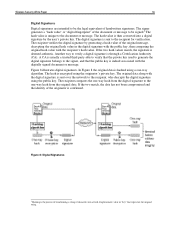
.... The hash value is then converted into a fixed-length numeric value or "key" that the public key is indeed associated with the recipient's hash value. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The original...
.... The hash value is then converted into a fixed-length numeric value or "key" that the public key is indeed associated with the recipient's hash value. Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The original...
Wireless Security
Page 17
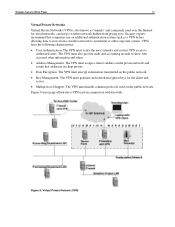
...users. Figure 9: Virtual Private Network (VPN) The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client... and server. • Multiprotocol Support. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
...users. Figure 9: Virtual Private Network (VPN) The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client... and server. • Multiprotocol Support. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
Wireless Security
Page 18
...PPTP that security arrangements can be limited in its own lines for security that it runs on because of the high CPU overhead associated with wireless networks in mind, and are available. By making secure use public and private keys and authenticate the sender with digital certificates.... Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. The PPTP protocol lets ...
...PPTP that security arrangements can be limited in its own lines for security that it runs on because of the high CPU overhead associated with wireless networks in mind, and are available. By making secure use public and private keys and authenticate the sender with digital certificates.... Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. The PPTP protocol lets ...
Wireless Security
Page 19
... products VGate by V-One: • Works only with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. GSM documents specify the rough functional characteristics of its keys. Most security ... both the international mobile subscriber identity (IMSI) and the subscriber identification key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC...
... products VGate by V-One: • Works only with established need-to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. GSM documents specify the rough functional characteristics of its keys. Most security ... both the international mobile subscriber identity (IMSI) and the subscriber identification key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC...
Wireless Security
Page 20
... deliberately varies the frequency of the transmitted signal, resulting in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for small, rapid fluctuations that occur as to eliminate the "WAP gap." (See below for... used by WWANs have reportedly been cracked. Besides encryption, the IS-95 standard of WAP used on WAP 2.0.) WAP 1.2 adds support for Wireless Public Key Infrastructure (WPKI) by the military with which authenticate a WTLS client to encrypt a session between the server and client. Version ...
... deliberately varies the frequency of the transmitted signal, resulting in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for small, rapid fluctuations that occur as to eliminate the "WAP gap." (See below for... used by WWANs have reportedly been cracked. Besides encryption, the IS-95 standard of WAP used on WAP 2.0.) WAP 1.2 adds support for Wireless Public Key Infrastructure (WPKI) by the military with which authenticate a WTLS client to encrypt a session between the server and client. Version ...