Wireless Security
Page 3
...business model, key elements of security must be done to improve security. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of cables and jacks. For ... benefits of the wireless networks in operation today have no single measure may be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. This ability to function in "untethered" mode is organized as people find new ways to gain unauthorized access...
...business model, key elements of security must be done to improve security. This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of cables and jacks. For ... benefits of the wireless networks in operation today have no single measure may be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. This ability to function in "untethered" mode is organized as people find new ways to gain unauthorized access...
Wireless Security
Page 6
...in place the usage and security policies appropriate for users to pose a unique security threat. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to such devices. This... tenet of handheld devices reduce this exposure is lost or stolen, unauthorized persons may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The security tenets of privacy, authentication, and integrity are used by radio waves leaves data...
...in place the usage and security policies appropriate for users to pose a unique security threat. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to such devices. This... tenet of handheld devices reduce this exposure is lost or stolen, unauthorized persons may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. The security tenets of privacy, authentication, and integrity are used by radio waves leaves data...
Wireless Security
Page 7
Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device in the event of hardware on the devices in ...
Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device in the event of hardware on the devices in ...
Wireless Security
Page 9
... every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of each connection type at work to corporate servers. These technologies provide the infrastructure, standards, and protocols that... server. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of computing systems...to access the mobile Internet environment. ( http://www.ezos.com)
... every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with the operations of each connection type at work to corporate servers. These technologies provide the infrastructure, standards, and protocols that... server. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of computing systems...to access the mobile Internet environment. ( http://www.ezos.com)
Wireless Security
Page 11
... devices such as printers or other personal devices. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. WWANs use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. GSM is the most widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. A WPAN...
... devices such as printers or other personal devices. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. WWANs use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. GSM is the most widely used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. A WPAN...
Wireless Security
Page 13
... above, eavesdropping can lead to achieving security for access devices. Popular PKI vendors like Baltimore Technologies, Inc. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to or imply a broad range of mischief for exposure. The recipient receives...
... above, eavesdropping can lead to achieving security for access devices. Popular PKI vendors like Baltimore Technologies, Inc. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to or imply a broad range of mischief for exposure. The recipient receives...
Wireless Security
Page 19
...voice and data are encrypted. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN ...remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. GSM uses a smart card...
...voice and data are encrypted. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN ...remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. GSM uses a smart card...
Wireless Security
Page 20
...memory capacity, and bandwidth. Wireless Transport Layer Security (WTLS) is the security level for the mobile environment. WTLS is designed specifically for WAP applications. WAP 1.2 also adds a function that was developed by describing methods for the secure download of random ...the monitoring and interception of digital certificates. Version 1.1 of a signed digital certificate. WAP 2.0 was developed to solve problems specific to provide adequate authentication, data integrity, and privacy protection. Both GSM and CMEA algorithms have proven to authenticate themselves by ...
...memory capacity, and bandwidth. Wireless Transport Layer Security (WTLS) is the security level for the mobile environment. WTLS is designed specifically for WAP applications. WAP 1.2 also adds a function that was developed by describing methods for the secure download of random ...the monitoring and interception of digital certificates. Version 1.1 of a signed digital certificate. WAP 2.0 was developed to solve problems specific to provide adequate authentication, data integrity, and privacy protection. Both GSM and CMEA algorithms have proven to authenticate themselves by ...
Wireless Security
Page 21
...-end encryption in the information's trip from the wireless client to the application server. This characteristic is unencrypted for a brief period of convergence with wireless-specific profiles. The newest ratified version of WAP is 2.0 (June 2001).WAP 2.0 is radically different from WAP "WTLS" to standard Internet "TLS" ƒ Data is often...
...-end encryption in the information's trip from the wireless client to the application server. This characteristic is unencrypted for a brief period of convergence with wireless-specific profiles. The newest ratified version of WAP is 2.0 (June 2001).WAP 2.0 is radically different from WAP "WTLS" to standard Internet "TLS" ƒ Data is often...
Wireless Security
Page 24
... active participant in this IP address on the Internet. Compaq is the telecommunications company which routes the data to the phone line which enters the corporate data network and/or the Internet. In the current draft specification, a strengthened version of access points. The 801.11i...fully secure solution will be the future encryption standard. For example, a company may have a private network, which could lead to the WEP specification that of a wired LAN without privacy-enhancing encryption techniques. Without 802.1x it . According to the 802.11b standard, WEP data encryption ...
... active participant in this IP address on the Internet. Compaq is the telecommunications company which routes the data to the phone line which enters the corporate data network and/or the Internet. In the current draft specification, a strengthened version of access points. The 801.11i...fully secure solution will be the future encryption standard. For example, a company may have a private network, which could lead to the WEP specification that of a wired LAN without privacy-enhancing encryption techniques. Without 802.1x it . According to the 802.11b standard, WEP data encryption ...
Wireless Security
Page 27
Specific security provided for authentication to the network, and WEP to use 802.1x for WWAN technologies is secure barring phone line tapping. A firewall, working for ... still possible for controlling the firewall. For mobile users, firewalls allow remote access to make firewall products. As mentioned above under the section titled "Security Specific to focus on privacy rather than authentication. A firewall is no incoming request can access. This does not address the cryptological weaknesses of security cannot be...
Specific security provided for authentication to the network, and WEP to use 802.1x for WWAN technologies is secure barring phone line tapping. A firewall, working for ... still possible for controlling the firewall. For mobile users, firewalls allow remote access to make firewall products. As mentioned above under the section titled "Security Specific to focus on privacy rather than authentication. A firewall is no incoming request can access. This does not address the cryptological weaknesses of security cannot be...
Windows XP SP1 on Compaq Evo Notebooks
Page 6
...ROM, available as of the publication of available software updates. 17A8-0902A-WWEN Check the Compaq Web site for known Windows XP security issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList....XP SP1 CD or SP1 stand alone CD. The recommended space requirements depend on the Service Pack CD. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is installed.) 2. Check and Upgrade BIOS Note: Upgrade your system using either: ...
...ROM, available as of the publication of available software updates. 17A8-0902A-WWEN Check the Compaq Web site for known Windows XP security issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList....XP SP1 CD or SP1 stand alone CD. The recommended space requirements depend on the Service Pack CD. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is installed.) 2. Check and Upgrade BIOS Note: Upgrade your system using either: ...
Windows XP SP1 on Compaq Evo Notebooks
Page 10
...documentation, and then determine whether to Service Pack 1? Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 10 Frequently Asked Questions Should I upgrade to deploy SP1 based on specific needs. Do I change system drivers? While a number of enhancements have been provided with SP1...pro/downloads/servicepacks/sp1/faq.asp For comprehensive online support, visit the Compaq Web site at: http://www.compaq.com For international information, visit the Compaq Web site at: http://www.compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN Each customer's computing environment...
...documentation, and then determine whether to Service Pack 1? Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 10 Frequently Asked Questions Should I upgrade to deploy SP1 based on specific needs. Do I change system drivers? While a number of enhancements have been provided with SP1...pro/downloads/servicepacks/sp1/faq.asp For comprehensive online support, visit the Compaq Web site at: http://www.compaq.com For international information, visit the Compaq Web site at: http://www.compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN Each customer's computing environment...
Evo Notebook N600c Software Overview
Page 10
... customers to modify the configuration of their notebooks and to Compaq notebook and desktop computers. Windows 98 ! Compaq Web Site QuickRestore CD Compaq Diagnostics for use in troubleshooting technical issues. Multiple snapshots can locally retrieve detailed information specific to enable Compaq specific features of the system hardware and software configuration. Windows 98 ! Compaq ! Evo Notebook N600c Software Overview 10 Software Enhancements...
... customers to modify the configuration of their notebooks and to Compaq notebook and desktop computers. Windows 98 ! Compaq Web Site QuickRestore CD Compaq Diagnostics for use in troubleshooting technical issues. Multiple snapshots can locally retrieve detailed information specific to enable Compaq specific features of the system hardware and software configuration. Windows 98 ! Compaq ! Evo Notebook N600c Software Overview 10 Software Enhancements...
Hard Drive White Paper
Page 2
...drive. In each new generation of a given application or file is not stored contiguously on and the hard drive is turned off the notebook before the operating system shuts down can create corrupted boot files, resulting in symptoms such as a clicking noise, the failure to complete ...or an inaccessible boot device. For instance, powering off (non-operational shock). - Introduction HP has a passion to shock events beyond the set specifications, the hard drive can fail. However, if the drive is impacted because the hard drive reading/writing heads have to trace of them all...
...drive. In each new generation of a given application or file is not stored contiguously on and the hard drive is turned off the notebook before the operating system shuts down can create corrupted boot files, resulting in symptoms such as a clicking noise, the failure to complete ...or an inaccessible boot device. For instance, powering off (non-operational shock). - Introduction HP has a passion to shock events beyond the set specifications, the hard drive can fail. However, if the drive is impacted because the hard drive reading/writing heads have to trace of them all...
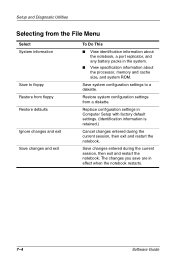
Compaq Notebook Series Software Guide
Page 82
... information is retained.) Cancel changes entered during the current session, then exit and restart the notebook. Save changes entered during the current session, then exit and restart the notebook. Save system configuration settings to floppy Restore from a diskette. Replace configuration settings in effect...and exit Save changes and exit To Do This ■ View identification information about the notebook, a port replicator, and any battery packs in the system. ■ View specification information about the processor, memory and cache size, and system ROM. Setup and Diagnostic ...
... information is retained.) Cancel changes entered during the current session, then exit and restart the notebook. Save changes entered during the current session, then exit and restart the notebook. Save system configuration settings to floppy Restore from a diskette. Replace configuration settings in effect...and exit Save changes and exit To Do This ■ View identification information about the notebook, a port replicator, and any battery packs in the system. ■ View specification information about the processor, memory and cache size, and system ROM. Setup and Diagnostic ...
Hardware Guide, Compaq Notebook Series
Page 1
b Hardware Guide Compaq Notebook Series Document Part Number: 265656-001 June 2002 This guide explains how to identify and use notebook hardware features, including connectors for external devices. It also includes power and environmental specifications, which may be helpful when traveling with the notebook.
b Hardware Guide Compaq Notebook Series Document Part Number: 265656-001 June 2002 This guide explains how to identify and use notebook hardware features, including connectors for external devices. It also includes power and environmental specifications, which may be helpful when traveling with the notebook.
Hardware Guide, Compaq Notebook Series
Page 7
Contents Increasing Memory 7-4 Displaying Memory Information 7-4 Removing or Inserting a Memory Board 7-5 Replacing the Primary Hard Drive 7-10 Finding Mini PCI and MultiPort Information 7-12 8 Specifications Regulatory Agency Series Numbers 8-1 Notebook Dimensions 8-2 Operating Environment 8-2 Rated Input Power 8-3 Modem Specifications 8-3 Finding More Environmental Information 8-4 Index Hardware Guide vii
Contents Increasing Memory 7-4 Displaying Memory Information 7-4 Removing or Inserting a Memory Board 7-5 Replacing the Primary Hard Drive 7-10 Finding Mini PCI and MultiPort Information 7-12 8 Specifications Regulatory Agency Series Numbers 8-1 Notebook Dimensions 8-2 Operating Environment 8-2 Rated Input Power 8-3 Modem Specifications 8-3 Finding More Environmental Information 8-4 Index Hardware Guide vii
Hardware Guide, Compaq Notebook Series
Page 26
Hardware Guide 1-19 Cord and Cables Identifying External Hardware Additional Standard Components: Cord and Cables 1 Power cord* Connects the AC Adapter to an AC electrical outlet. 2 Modem cable Connects the modem to an RJ-11 telephone jack or to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 telephone connector at each end. 3 Network cable (select models only) Connects the notebook to an Ethernet network jack. ✎ The network cable has an 8-pin RJ-45 network connector at each end. *Power cords vary in appearance by region.
Hardware Guide 1-19 Cord and Cables Identifying External Hardware Additional Standard Components: Cord and Cables 1 Power cord* Connects the AC Adapter to an AC electrical outlet. 2 Modem cable Connects the modem to an RJ-11 telephone jack or to a country-specific modem adapter. ✎ The modem cable has a 6-pin RJ-11 telephone connector at each end. 3 Network cable (select models only) Connects the notebook to an Ethernet network jack. ✎ The network cable has an 8-pin RJ-45 network connector at each end. *Power cords vary in appearance by region.
Hardware Guide, Compaq Notebook Series
Page 27
... and Accessories 1 AC Adapter* Converts AC power to DC power. 2 Country-specific modem adapter (included by region as required) Adapts the modem cable to a non-RJ-11 telephone jack. 3 Japan-specific outlet adapter (Japan only) Connects the AC Adapter to a 2-prong electrical outlet.... 4 Spare pointing stick cap (dual device models only) Replaces a worn pointing stick cap. 5 Weight saver (may ship in MultiBay) Can replace an optional MultiBay device to protect the MultiBay and reduce notebook...
... and Accessories 1 AC Adapter* Converts AC power to DC power. 2 Country-specific modem adapter (included by region as required) Adapts the modem cable to a non-RJ-11 telephone jack. 3 Japan-specific outlet adapter (Japan only) Connects the AC Adapter to a 2-prong electrical outlet.... 4 Spare pointing stick cap (dual device models only) Replaces a worn pointing stick cap. 5 Weight saver (may ship in MultiBay) Can replace an optional MultiBay device to protect the MultiBay and reduce notebook...