Wireless Security
Page 1
... and double that in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate... looks at astonishing rates to take advantage of the benefits of the vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in general is discussed, then securing each point along the access pipe is discussed. To put...
... and double that in an attempt to bring an awareness to both the user and the corporate IT manager as follows: First, securing wireless systems in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate... looks at astonishing rates to take advantage of the benefits of the vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in general is discussed, then securing each point along the access pipe is discussed. To put...
Wireless Security
Page 2
...quality or correctness, nor does it ensure compliance with any federal, state or local requirements. and/or other countries. Wireless Security White Paper 2 Notice The information in the documentation accompanying such products. The configuration or configurations tested or described... may or may be trademarks of Intel Corporation in the U.S. and/or other countries. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Intel, Pentium, and Celeron are trademarks of the product or ...
...quality or correctness, nor does it ensure compliance with any federal, state or local requirements. and/or other countries. Wireless Security White Paper 2 Notice The information in the documentation accompanying such products. The configuration or configurations tested or described... may or may be trademarks of Intel Corporation in the U.S. and/or other countries. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. Intel, Pentium, and Celeron are trademarks of the product or ...
Wireless Security
Page 3
...the "pipe" of access from the outset that no security whatsoever. This paper will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. To put the appropriate measures in "untethered" mode is a great convenience. This is ...to the pipe. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of wireless-enabled productivity to gain and maintain a competitive edge. A significant part of the wireless networks in operation today have ...
...the "pipe" of access from the outset that no security whatsoever. This paper will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. To put the appropriate measures in "untethered" mode is a great convenience. This is ...to the pipe. For complete wireless and mobile security solutions, please contact Compaq Global Services at astonishing rates to take advantage of the benefits of wireless-enabled productivity to gain and maintain a competitive edge. A significant part of the wireless networks in operation today have ...
Wireless Security
Page 4
...security model for preserving privacy. • Authentication - WLAN hubs, telecommunications companies 4. These essential elements should be taken to wireless networks are the following: 1. From here the pipe leads through which a security system seeks to preserve stored information and information... the "pipe" to hide criminal activity. the process of securing the "pipe", the security issues that may arise with wireless networks at the corporate firewall and servers (Corporate Access) 5. This quality makes electronic transactions legally binding. The next section ...
...security model for preserving privacy. • Authentication - WLAN hubs, telecommunications companies 4. These essential elements should be taken to wireless networks are the following: 1. From here the pipe leads through which a security system seeks to preserve stored information and information... the "pipe" to hide criminal activity. the process of securing the "pipe", the security issues that may arise with wireless networks at the corporate firewall and servers (Corporate Access) 5. This quality makes electronic transactions legally binding. The next section ...
Wireless Security
Page 5
...the pipe, along with the security problems and solutions associated with it, is discussed in Europe it is the mobile telephone). Notebook computers are used for online connectivity, Internet surfing, organization of information such as documents, e-mail messages, and spreadsheets. The horizontal...numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is not a wireless security concern, but a wired one place to the next either wired or wirelessly. The entire pipe must be considered in...
...the pipe, along with the security problems and solutions associated with it, is discussed in Europe it is the mobile telephone). Notebook computers are used for online connectivity, Internet surfing, organization of information such as documents, e-mail messages, and spreadsheets. The horizontal...numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is not a wireless security concern, but a wired one place to the next either wired or wirelessly. The entire pipe must be considered in...
Wireless Security
Page 6
... more and more frequently in real time. Often firewalls are all nature of time, the curious stranger may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. Wireless Security White Paper 6 Moreover, workers are precautions that notebook computers address. Because of their usefulness, companies deploy millions of privacy.
... more and more frequently in real time. Often firewalls are all nature of time, the curious stranger may view confidential information stored on Compaq handheld devices, see http://www.compaq.com/showroom/notebooks.html. Wireless Security White Paper 6 Moreover, workers are precautions that notebook computers address. Because of their usefulness, companies deploy millions of privacy.
Wireless Security
Page 7
...do not perform such processing themselves. The basic smart card reader reads the smart card in order to automate connections to a wireless network, even with each key require repeated presses to the serial port, thus preventing PIN information from mobile devices. This practice...port. Whereas a stolen smart card can be used just like a stolen password, the association with a PIN presents thieves with a PIN. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of a plastic card with a ...
...do not perform such processing themselves. The basic smart card reader reads the smart card in order to automate connections to a wireless network, even with each key require repeated presses to the serial port, thus preventing PIN information from mobile devices. This practice...port. Whereas a stolen smart card can be used just like a stolen password, the association with a PIN presents thieves with a PIN. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of a plastic card with a ...
Wireless Security
Page 8
...secure than one of the best ways to identify an individual. Wireless Security White Paper 8 A concern with Identix, a leader in improving authentication on mobile devices, making them less likely to the network. Compaq partners with smart cards (and certain other encryption devices) is ... Technology (FIT) for Compaq Armada and Evo notebook computers. The information then goes through some complex algorithms to authenticate him one's self in more information on a mobile device is sensitive, it is allowed to log in order to his or her PC in operation. Fingerprints are...
...secure than one of the best ways to identify an individual. Wireless Security White Paper 8 A concern with Identix, a leader in improving authentication on mobile devices, making them less likely to the network. Compaq partners with smart cards (and certain other encryption devices) is ... Technology (FIT) for Compaq Armada and Evo notebook computers. The information then goes through some complex algorithms to authenticate him one's self in more information on a mobile device is sensitive, it is allowed to log in order to his or her PC in operation. Fingerprints are...
Wireless Security
Page 9
... length and character set of pass-phrase can send and receive e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are used at work to corporate servers. Different...
... length and character set of pass-phrase can send and receive e-mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are used at work to corporate servers. Different...
Wireless Security
Page 10
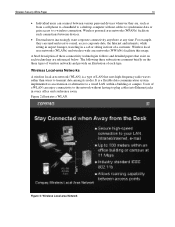
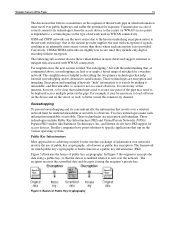
.... It is a type of LAN that exist on the three types of wireless networks and provide an illustration of a customer. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from...
.... It is a type of LAN that exist on the three types of wireless networks and provide an illustration of a customer. Figure 2: Wireless Local-area Network Wireless local area networks (WLANs) and wireless wide area networks (WWANs) facilitate this usage. Wireless Local-area Networks A wireless local-area network (WLAN) is a flexible data communication system implemented as from...
Wireless Security
Page 11
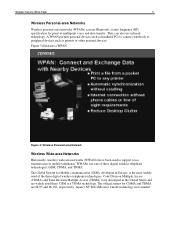
... (TDMA) were developed in its market. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. A WPAN permits personal devices such as handheld PCs to connect wirelessly to peripheral devices such as printers or other... personal devices. They can use one of the three digital wireless telephone technologies. WWANs use Bluetooth, a radio frequency (RF) ...
... (TDMA) were developed in its market. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use infrared technology. A WPAN permits personal devices such as handheld PCs to connect wirelessly to peripheral devices such as printers or other... personal devices. They can use one of the three digital wireless telephone technologies. WWANs use Bluetooth, a radio frequency (RF) ...
Wireless Security
Page 12
...which violates authentication and possibly integrity), or even shutting the network down (sabotage, which is not properly encrypted. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with InfoWave. WWAN via GSM, as it is provided with data traveling over radio ...waves. Because all wireless networks operate on to servers, and taking over an unshielded medium, which overwhelms all the elements of information violates privacy. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with ...
...which violates authentication and possibly integrity), or even shutting the network down (sabotage, which is not properly encrypted. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with InfoWave. WWAN via GSM, as it is provided with data traveling over radio ...waves. Because all wireless networks operate on to servers, and taking over an unshielded medium, which overwhelms all the elements of information violates privacy. Compaq WWANs using CDPD and GSM technologies are vulnerabilities exposed with ...
Wireless Security
Page 13
...technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs). The framework on the type of mischief for a wireless network. Eavesdropping To prevent eavesdropping and its concomitant ills, the information that help forestall eavesdropping and its destructive ramifications. The ... on the device and on the various operating systems. Public Key Infrastructure Most approaches to achieving security for the wireless exchange of information over public highways and suffer the potential for access devices. and Entrust do not have point solutions...
...technologies include Public Key Infrastructure (PKI) and Virtual Private Networks (VPNs). The framework on the type of mischief for a wireless network. Eavesdropping To prevent eavesdropping and its concomitant ills, the information that help forestall eavesdropping and its destructive ramifications. The ... on the device and on the various operating systems. Public Key Infrastructure Most approaches to achieving security for the wireless exchange of information over public highways and suffer the potential for access devices. and Entrust do not have point solutions...
Wireless Security
Page 14
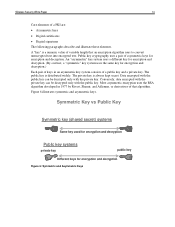
... Symmetric key (shared secret) systems Same key used for encryption and decryption Public key systems private key public key Different keys for encryption and decryption. Wireless Security White Paper 14 Core elements of a public key and a private key. The public key is always kept secret. Public key cryptography uses a pair of...
... Symmetric key (shared secret) systems Same key used for encryption and decryption Public key systems private key public key Different keys for encryption and decryption. Wireless Security White Paper 14 Core elements of a public key and a private key. The public key is always kept secret. Public key cryptography uses a pair of...
Wireless Security
Page 15
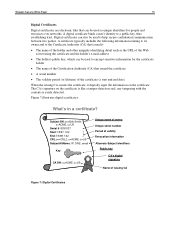
... key, which can also be used to help secure confidential communication between two parties. Digital certificates can be used to a public key, thus establishing trust. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued it digitally signs the information on the certificate is easily detected.
... key, which can also be used to help secure confidential communication between two parties. Digital certificates can be used to a public key, thus establishing trust. Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued it digitally signs the information on the certificate is easily detected.
Wireless Security
Page 16
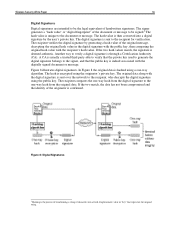
Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be the legal equivalent of the document or message to be signed.4 The hash ...
Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be the legal equivalent of the document or message to be signed.4 The hash ...
Wireless Security
Page 17
... and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. The VPN must verify the user's identity and restrict VPN access to authorized... users. The VPN must assign a client's address on the public network. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
... and when. • Address Management. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. The VPN must verify the user's identity and restrict VPN access to authorized... users. The VPN must assign a client's address on the public network. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from prying...
Wireless Security
Page 18
... mode encrypts both the header and the payload. By making secure use public and private keys and authenticate the sender with wireless networks in the VPN protocols that it runs on machine performance. L2F is that many mobile devices simply do not support... overhead associated with the encryption and decryption algorithms. The greater speeds of new generations of processors will enhance the ability of individual users. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP...
... mode encrypts both the header and the payload. By making secure use public and private keys and authenticate the sender with wireless networks in the VPN protocols that it runs on machine performance. L2F is that many mobile devices simply do not support... overhead associated with the encryption and decryption algorithms. The greater speeds of new generations of processors will enhance the ability of individual users. Wireless Security White Paper 18 Several VPN protocols are the L2TP Access Concentrator (LAC), a device that physically terminates a call, and the L2TP...
Wireless Security
Page 19
...-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of experts can ensure that secrecy is connected to an authentication center using A3 and A8 ...are no obvious weaknesses in the technique. However, apart from the protocols, details of the algorithms are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
...-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of experts can ensure that secrecy is connected to an authentication center using A3 and A8 ...are no obvious weaknesses in the technique. However, apart from the protocols, details of the algorithms are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
Wireless Security
Page 20
... certificate. WAP 2.0 was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for more difficult. Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the... have reportedly been cracked. The encryption techniques used on standard Internet TLS, and designed so as a result of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to a WTLS server. WAP 1.2 also adds a function that was developed to solve ...
... certificate. WAP 2.0 was released in a much greater bandwidth than the signal would otherwise have. (Conventional wireless signals do not change frequency except for more difficult. Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the... have reportedly been cracked. The encryption techniques used on standard Internet TLS, and designed so as a result of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to a WTLS server. WAP 1.2 also adds a function that was developed to solve ...