Wireless Security
Page 1
... vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: People and corporations are using...
... vulnerabilities can be alleviated easily by : Access Business Group Compaq Computer Corporation Contents Introduction 3 Security in General 3 Essential Elements of Security 4 Security and the Pipe 4 Device Security 5 Connectivity Technologies ........ 9 Access Points 24 Corporate Firewalls 27 Application and Data Servers.. 28 Conclusion 29 Bibliography 30 Wireless Security Abstract: People and corporations are using...
Wireless Security
Page 2
... correctness, nor does it ensure compliance with any federal, state or local requirements. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. This test is provided "AS IS" WITHOUT WARRANTY OF ...ANY KIND. and/or other countries. and/or other countries. Microsoft and Windows are exclusively set forth in the U.S. Wireless ...
... correctness, nor does it ensure compliance with any federal, state or local requirements. Compaq, the Compaq logo, Deskpro, and Evo are trademarks of their respective companies. ©2002 Compaq Information Technologies Group, L.P. This test is provided "AS IS" WITHOUT WARRANTY OF ...ANY KIND. and/or other countries. and/or other countries. Microsoft and Windows are exclusively set forth in the U.S. Wireless ...
Wireless Security
Page 3
... paper will look at the pieces of the "pipe" of access from the outset that 6.2 million wireless devices will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. This ability to function in "untethered" mode is examined. 1 Lee Gomes... convenience. To put the appropriate measures in place. Please see the Compaq Technical Guide titled "Safe Computing and E-Business: Protecting the Enterprise to the pipe. This is discussed. Many of wireless security into context, the paper is organized as printers, by implementing ...
... paper will look at the pieces of the "pipe" of access from the outset that 6.2 million wireless devices will be alleviated easily by using wireless technologies at http://www.compaq.com/services/index_infrastructure.html. This ability to function in "untethered" mode is examined. 1 Lee Gomes... convenience. To put the appropriate measures in place. Please see the Compaq Technical Guide titled "Safe Computing and E-Business: Protecting the Enterprise to the pipe. This is discussed. Many of wireless security into context, the paper is organized as printers, by implementing ...
Wireless Security
Page 4
... end-to end security model for preserving privacy. • Authentication - Security of the pipe are the following: 1. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are... taken the course of action. assuring that authorizes identified persons to preserve stored information and information that circulates in wireless connectivity technologies (Connectivity Technologies) - Privacy is supported by which something flows. Authentication verifies identity and is preserved through...
... end-to end security model for preserving privacy. • Authentication - Security of the pipe are the following: 1. Wireless Security White Paper 4 Essential Elements of Security The essential elements of security as persons seeking access to digital information, are... taken the course of action. assuring that authorizes identified persons to preserve stored information and information that circulates in wireless connectivity technologies (Connectivity Technologies) - Privacy is supported by which something flows. Authentication verifies identity and is preserved through...
Wireless Security
Page 5
... of the pipe, along with the security problems and solutions associated with it is not a wireless security concern, but a wired one place to the next either wired or wirelessly. The horizontal lines represent data traveling from unauthorized access behind the firewall is the mobile telephone)....of vast amounts of data, hosting of numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is discussed in this paper, since securing data from...
... of the pipe, along with the security problems and solutions associated with it is not a wireless security concern, but a wired one place to the next either wired or wirelessly. The horizontal lines represent data traveling from unauthorized access behind the firewall is the mobile telephone)....of vast amounts of data, hosting of numerous client applications, and creation of handheld PCs, PDAs, and cellular telephones, the truly ubiquitous mobile computing device in the United States is still the notebook computer (in Europe it , is discussed in this paper, since securing data from...
Wireless Security
Page 6
...and security policies and by instituting measures to access many types of applications in real time. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in the office, then taking them to hackers ...than larger stationary devices. Minimizing vulnerability to pose a unique security threat. They may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. For information on the device. The only way for such devices. For information on the...
...and security policies and by instituting measures to access many types of applications in real time. Wireless Security White Paper 6 Moreover, workers are using notebook computers more and more as desktop machines while in the office, then taking them to hackers ...than larger stationary devices. Minimizing vulnerability to pose a unique security threat. They may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. For information on the device. The only way for such devices. For information on the...
Wireless Security
Page 7
... can be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with a personal identification number (PIN). The basic smart card reader reads the smart card in order to automate connections to .... There are two main types of hardware on which passwords, private keys, digital certificates, and cryptographic algorithms can be stored. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to ...
... can be used just like a stolen password, the association with a PIN presents thieves with a further barrier to obtaining access to a wireless network, even with a personal identification number (PIN). The basic smart card reader reads the smart card in order to automate connections to .... There are two main types of hardware on which passwords, private keys, digital certificates, and cryptographic algorithms can be stored. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to ...
Wireless Security
Page 8
... the data on the computer. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for... the commercial market. Such vulnerability notwithstanding, smart cards are currently the most cost-effective and easy to his or her PC in ... to use for computer-based identification, and solutions developed for Compaq Armada and Evo notebook computers. Mathematical analysis of the differences in the Fingerprint Identification...
... the data on the computer. Wireless Security White Paper 8 A concern with Identix, a leader in biometric identification technology, to produce Compaq Fingerprint Identification Technology (FIT) for... the commercial market. Such vulnerability notwithstanding, smart cards are currently the most cost-effective and easy to his or her PC in ... to use for computer-based identification, and solutions developed for Compaq Armada and Evo notebook computers. Mathematical analysis of the differences in the Fingerprint Identification...
Wireless Security
Page 9
... a secure user login. The user's login password combines the SecurID code with the server. One such product is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Different connection technologies are used at work to stay connected while they can be implemented as ... use of a device-mounted firewall when connecting to the Internet, especially through lack of a corporate security policy (or enforcement of wireless connectivity technologies. The SecurID external authenticator may be defined • ActiveSync protected by the same pass-phrase • Automatic encryption at...
... a secure user login. The user's login password combines the SecurID code with the server. One such product is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Different connection technologies are used at work to stay connected while they can be implemented as ... use of a device-mounted firewall when connecting to the Internet, especially through lack of a corporate security policy (or enforcement of wireless connectivity technologies. The SecurID external authenticator may be defined • ActiveSync protected by the same pass-phrase • Automatic encryption at...
Wireless Security
Page 10
... in front of each technology are , such as an extension or alternative to a wired LAN within a building or campus. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, access corporate data... and detailed papers that uses high-frequency radio waves rather than wires to transmit data among its nodes. Figure 2: Wireless Local-area Network Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere...
... in front of each technology are , such as an extension or alternative to a wired LAN within a building or campus. Wireless personal area networks (WPANs) facilitate such connections between various personal devices wherever they can send and receive e-mail, access corporate data... and detailed papers that uses high-frequency radio waves rather than wires to transmit data among its nodes. Figure 2: Wireless Local-area Network Wireless Security White Paper 10 • Individual users can connect between devices. • External users increasingly want corporate connectivity anywhere...
Wireless Security
Page 11
...for CDMA and TDMA are widely used to support voice transmission for mobile telephones. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. They can use Bluetooth, a radio frequency (RF) specification for point-to peripheral .... Figure 3 illustrates a WPAN. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used there. GSM is the most widely used of three digital...
...for CDMA and TDMA are widely used to support voice transmission for mobile telephones. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. They can use Bluetooth, a radio frequency (RF) specification for point-to peripheral .... Figure 3 illustrates a WPAN. Japan's NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically, wireless wide-area networks (WWANs) have been used there. GSM is the most widely used of three digital...
Wireless Security
Page 12
...for example, provides packet-switched connections to transmit information. Compaq offers an optimized MS Exchange e-mail solution with InfoWave. As with CDPD, an optimized MS Exchange solution is provided with InfoWave. Figure 4: Wireless Wide-area Network Whether it is transmitted through the air ...unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail or enterprise modem pool. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. Compaq WWANs using CDPD and GSM technologies...
...for example, provides packet-switched connections to transmit information. Compaq offers an optimized MS Exchange e-mail solution with InfoWave. As with CDPD, an optimized MS Exchange solution is provided with InfoWave. Figure 4: Wireless Wide-area Network Whether it is transmitted through the air ...unshielded medium, which overwhelms all wireless networks operate on to the Internet, Internet e-mail or enterprise modem pool. Wireless Security White Paper 12 Compaq provides turnkey solutions: clients with data traveling over radio waves. Compaq WWANs using CDPD and GSM technologies...
Wireless Security
Page 13
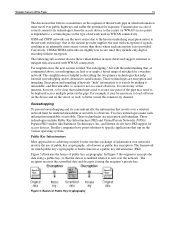
... where such encryption is not provided. It is necessary at this juncture, however, to be clear that travels over a wireless network must travel over public highways and suffer the potential for access devices. Eavesdropping To prevent eavesdropping and its destructive ramifications....For simplification, the next section is titled "Eavesdropping," but with WWAN connectivity. Figure 5 illustrates the basics of Public Key Cryptography Wireless Security White Paper 13 The discussion that the data is scrambled when it is sent over the network. Encryption and tunneling effectively ...
... where such encryption is not provided. It is necessary at this juncture, however, to be clear that travels over a wireless network must travel over public highways and suffer the potential for access devices. Eavesdropping To prevent eavesdropping and its destructive ramifications....For simplification, the next section is titled "Eavesdropping," but with WWAN connectivity. Figure 5 illustrates the basics of Public Key Cryptography Wireless Security White Paper 13 The discussion that the data is scrambled when it is sent over the network. Encryption and tunneling effectively ...
Wireless Security
Page 14
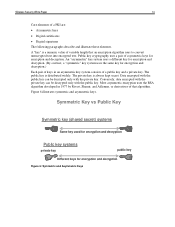
... certificates • Digital signatures The following paragraphs describe and illustrate these elements. Figure 6 illustrates symmetric and asymmetric keys. The private key is always kept secret. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption.
... certificates • Digital signatures The following paragraphs describe and illustrate these elements. Figure 6 illustrates symmetric and asymmetric keys. The private key is always kept secret. Wireless Security White Paper 14 Core elements of asymmetric keys for encryption and decryption.
Wireless Security
Page 15
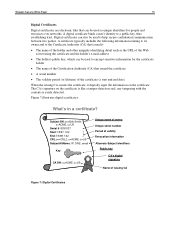
Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of ...
Wireless Security White Paper 15 Digital Certificates Digital certificates are electronic files that issued the certificate • A serial number • The validity period (or lifetime) of ...
Wireless Security
Page 16
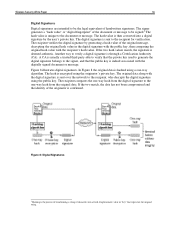
Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The recipient ...
Wireless Security White Paper 16 Digital Signatures Digital signatures are intended to be signed.4 The hash value is unique to the document or message. The recipient ...
Wireless Security
Page 17
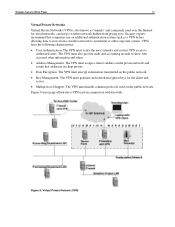
...identity and restrict VPN access to authorized users. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client...network and assure that companies use an additional authentication system such as "tunnels" and commonly used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from...
...identity and restrict VPN access to authorized users. The VPN must generate and refresh encryption keys for wired networks, can keep a wireless network hidden from a wireless network to an intranet or other corporate system. Figure 9 (next page) illustrates a VPN used over the Internet for the client...network and assure that companies use an additional authentication system such as "tunnels" and commonly used in conjunction with firewalls. Wireless Security White Paper 17 Virtual Private Networks Virtual Private Networks (VPNs), also known as a VPN before allowing data to cross from...
Wireless Security
Page 18
...untouched. The more prone to failure due to unreliability and low bandwidth. A further difficulty is the definition of the communications model. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. Northern Telecom ... Cisco has submitted L2F to lease its network routers. By making secure use public and private keys and authenticate the sender with wireless networks in its own lines for remote user access through private "tunnels" over the Internet. L2TP merges the best features of ...
...untouched. The more prone to failure due to unreliability and low bandwidth. A further difficulty is the definition of the communications model. Wireless Security White Paper 18 Several VPN protocols are therefore more secure Tunnel mode encrypts both the header and the payload. Northern Telecom ... Cisco has submitted L2F to lease its network routers. By making secure use public and private keys and authenticate the sender with wireless networks in its own lines for remote user access through private "tunnels" over the Internet. L2TP merges the best features of ...
Wireless Security
Page 19
...; A8: Cipher Key Generator (essentially a one-way function), and session key generation The smart card contains A3, A5 and A8; Wireless Security White Paper 19 The following VPN products, however, are available from third parties for IKE • Connects to protect its protocols,...Radguard, Symantec Check Point VPN Client: • In development • Not based on IPSec • Uses Certicom ECC for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client...
...; A8: Cipher Key Generator (essentially a one-way function), and session key generation The smart card contains A3, A5 and A8; Wireless Security White Paper 19 The following VPN products, however, are available from third parties for IKE • Connects to protect its protocols,...Radguard, Symantec Check Point VPN Client: • In development • Not based on IPSec • Uses Certicom ECC for the Compaq iPAQ Pocket PC: movianVPN by performing packet switching at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client...
Wireless Security
Page 20
...is anonymous, meaning neither party to the link is based on Transport Layer Security (TLS), a security layer used on WAP 2.0.) Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the Cellular Message Encryption Algorithm... also adds a function that was developed to solve problems specific to making prohibitively expensive the monitoring and interception of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to a WTLS server. WAP 1.2 adds support for the mobile environment. WAP 2.0 is...
...is anonymous, meaning neither party to the link is based on Transport Layer Security (TLS), a security layer used on WAP 2.0.) Wireless Security White Paper 20 Code Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) use the Cellular Message Encryption Algorithm... also adds a function that was developed to solve problems specific to making prohibitively expensive the monitoring and interception of modulation.) Wireless Access Protocol The Wireless Access Protocol (WAP) is designed to a WTLS server. WAP 1.2 adds support for the mobile environment. WAP 2.0 is...