User Guide
Page 53
...Enable (factory default) ƒ Disable PPTP Passthrough Enables/disables Point-to configure Virtual Private Network (VPN) support. Configure Security Security > VPN Passthrough Use this page allows VPN tunnels using IPsec or PPTP protocols to Point Tunneling Protocol (PPTP) can pass through the firewall To... disable PPTP Passthrough select Disable. Use the descriptions and instructions in the following table to configure the VPN passthrough for your changes or Cancel Changes to cancel. Select the desired option: ƒ Enable (factory default) ƒ ...
...Enable (factory default) ƒ Disable PPTP Passthrough Enables/disables Point-to configure Virtual Private Network (VPN) support. Configure Security Security > VPN Passthrough Use this page allows VPN tunnels using IPsec or PPTP protocols to Point Tunneling Protocol (PPTP) can pass through the firewall To... disable PPTP Passthrough select Disable. Use the descriptions and instructions in the following table to configure the VPN passthrough for your changes or Cancel Changes to cancel. Select the desired option: ƒ Enable (factory default) ƒ ...
User Guide
Page 54
... network just as if you were directly connected to be transmitted over public networks or other private networks. For example, a VPN allows users to sit at home and connect to his/her employer's corporate network and receive an IP address in their office... connected to configure the VPN for a private network. Configure Security Security > VPN A Virtual Private Network (VPN) is accomplished by creating a "VPN tunnel." Use this page to their corporate LAN. This is a connection between networks securely ...
... network just as if you were directly connected to be transmitted over public networks or other private networks. For example, a VPN allows users to sit at home and connect to his/her employer's corporate network and receive an IP address in their office... connected to configure the VPN for a private network. Configure Security Security > VPN A Virtual Private Network (VPN) is accomplished by creating a "VPN tunnel." Use this page to their corporate LAN. This is a connection between networks securely ...
User Guide
Page 55
...must match the remote gateway's Local Secure Group. This may be a single IP Group address or sub-network. Section Field Description VPN Tunnel Select Tunnel Entry Allows you make your selections, click Save Settings to apply your gateway. Note that can use this tunnel ...Local Secure Select the local LAN user(s) that the Remote Secure Group must match the remote gateway's Remote Secure Group. Configure Security Security VPN Tunnel Page Description Use the descriptions and instructions in the following table to cancel. This may be a single IP address, a sub-...
...must match the remote gateway's Local Secure Group. This may be a single IP Group address or sub-network. Section Field Description VPN Tunnel Select Tunnel Entry Allows you make your selections, click Save Settings to apply your gateway. Note that can use this tunnel ...Local Secure Select the local LAN user(s) that the Remote Secure Group must match the remote gateway's Remote Secure Group. Configure Security Security VPN Tunnel Page Description Use the descriptions and instructions in the following table to cancel. This may be a single IP address, a sub-...
User Guide
Page 57
...Configure Security Section Field Description Key Select one of the following options for IP traffic encryption and authentication. Notice that both sides (VPN endpoints) must use the same Encryption Key. - Authentication: The Authentication method authenticates the Encapsulating Security Payload (ESP) packets. ...MD5: A one-way hashing algorithm that produces a 128-bit digest ƒ SHA: A one -way hashing algorithm that both sides (VPN endpoints) must match the remote gateway's Outbound SPI, and vice versa. 4021196 Rev A 57 Key Lifetime: This field specifies the lifetime of...
...Configure Security Section Field Description Key Select one of the following options for IP traffic encryption and authentication. Notice that both sides (VPN endpoints) must use the same Encryption Key. - Authentication: The Authentication method authenticates the Encapsulating Security Payload (ESP) packets. ...MD5: A one-way hashing algorithm that produces a 128-bit digest ƒ SHA: A one -way hashing algorithm that both sides (VPN endpoints) must match the remote gateway's Outbound SPI, and vice versa. 4021196 Rev A 57 Key Lifetime: This field specifies the lifetime of...
User Guide
Page 58
...Advanced Settings If the Key Exchange Method is slower but less secure ƒ Local Identity Select the desired option to break a connection for the current VPN tunnel. Name: Domain name of this button to match the Remote Identity setting at the other end of each established tunnel. Local IP Address: Your... WAN (Internet) IP address - The state is the Encryption algorithm used at the other end of the remote VPN endpoint - If you have made any changes, click Save Settings to match the Local Identity setting at the other end of the remote...
...Advanced Settings If the Key Exchange Method is slower but less secure ƒ Local Identity Select the desired option to break a connection for the current VPN tunnel. Name: Domain name of this button to match the Remote Identity setting at the other end of each established tunnel. Local IP Address: Your... WAN (Internet) IP address - The state is the Encryption algorithm used at the other end of the remote VPN endpoint - If you have made any changes, click Save Settings to match the Local Identity setting at the other end of the remote...
User Guide
Page 59
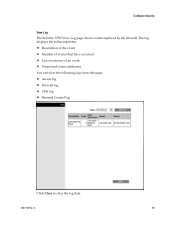
Configure Security View Log The Security VPN View Log page shows events captured by the firewall. The log displays the following items: Description of the event Number of events that have occurred Last occurrence of an event Target and source addresses You can view the following logs from this page: Access log Firewall log VPN log Parental Control log Click Clear to clear the log data. 4021196 Rev A 59
Configure Security View Log The Security VPN View Log page shows events captured by the firewall. The log displays the following items: Description of the event Number of events that have occurred Last occurrence of an event Target and source addresses You can view the following logs from this page: Access log Firewall log VPN log Parental Control log Click Clear to clear the log data. 4021196 Rev A 59
User Guide
Page 80
... page. 2 To view a particular log, select one of the following options from the Type dropdown menu: „ All „ Access Log „ Firewall Log „ VPN Log 3 After the log data is displayed, use one of the log, if available. 80 4021196 Rev A Manage the Gateway View Log To view the...
... page. 2 To view a particular log, select one of the following options from the Type dropdown menu: „ All „ Access Log „ Firewall Log „ VPN Log 3 After the log data is displayed, use one of the log, if available. 80 4021196 Rev A Manage the Gateway View Log To view the...
Software Configuration Guide
Page 13
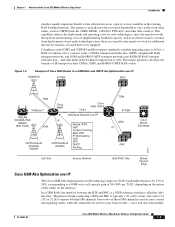
... Cisco 3825 Mobile Wireless Edge Router Introduction Another equally important benefit is that substantial excess capacity is typically a T1 or E1 circuit, and carries 24 (T1) or 32 (E1) separate 64 kbps DS0 channels. This means operators can reallocate this recovered bandwidth to carry bearer traffic-voice... IP/FA VoIP Content Caching Multi VPN IP Multicasting QoS PPP DHCP Routing TDM IP-PBX ATM IP RNC Cisco Mobile Exchange 203232 Cell Site Access Network BSC/RNC Site Mobile Internet Edge Cisco GSM Abis Optimization over IP The Cisco GSM Abis Optimization over IP technology ...
... Cisco 3825 Mobile Wireless Edge Router Introduction Another equally important benefit is that substantial excess capacity is typically a T1 or E1 circuit, and carries 24 (T1) or 32 (E1) separate 64 kbps DS0 channels. This means operators can reallocate this recovered bandwidth to carry bearer traffic-voice... IP/FA VoIP Content Caching Multi VPN IP Multicasting QoS PPP DHCP Routing TDM IP-PBX ATM IP RNC Cisco Mobile Exchange 203232 Cell Site Access Network BSC/RNC Site Mobile Internet Edge Cisco GSM Abis Optimization over IP The Cisco GSM Abis Optimization over IP technology ...
Software Configuration Guide
Page 15
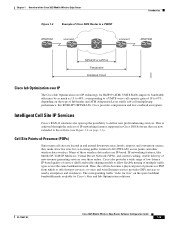
..., Virtual Private Network (VPN), and content caching, enable delivery of new revenue-generating services over IP technology for R4/R99 (ATM) UMTS RANs improves bandwidth efficiency by Cisco's Abis and Iub Optimization solutions. Intelligent Cell Site IP Services Cisco's RAN-O solutions also ... as much as 15 to 40%, corresponding to a UMTS voice call capacity gain of 18 to nearby enterprises and residences. Chapter 1 Overview of the Cisco 3825 Mobile Wireless Edge Router Figure 1-3 Example of Cisco 3825 Router in a PWE3f Introduction ATM/TDM xconnect xconnect ATM/TDM 201865...
..., Virtual Private Network (VPN), and content caching, enable delivery of new revenue-generating services over IP technology for R4/R99 (ATM) UMTS RANs improves bandwidth efficiency by Cisco's Abis and Iub Optimization solutions. Intelligent Cell Site IP Services Cisco's RAN-O solutions also ... as much as 15 to 40%, corresponding to a UMTS voice call capacity gain of 18 to nearby enterprises and residences. Chapter 1 Overview of the Cisco 3825 Mobile Wireless Edge Router Figure 1-3 Example of Cisco 3825 Router in a PWE3f Introduction ATM/TDM xconnect xconnect ATM/TDM 201865...
Software Configuration Guide
Page 17
... standalone subcommand. These relays allow "Y" cabling for router redundancy where the T1/E1 link is not redundant and default to use the Cisco 3825 router in the Cisco 3825 router for the Cisco MWR 1941-DC-A router and Cisco 3825 router includes relays that activate the T1/E1 ports....VPN • IP Multicast • Mobile IP/FA • content caching • MPLS • L2TPv3 Other Services • ACFC and PFC Handling During PPP Negotiation • HSRP • NTP • SNMP Redundancy Support In a RAN-O application, to ensure availability, the backhaul links to a Cisco 3825 router...
... standalone subcommand. These relays allow "Y" cabling for router redundancy where the T1/E1 link is not redundant and default to use the Cisco 3825 router in the Cisco 3825 router for the Cisco MWR 1941-DC-A router and Cisco 3825 router includes relays that activate the T1/E1 ports....VPN • IP Multicast • Mobile IP/FA • content caching • MPLS • L2TPv3 Other Services • ACFC and PFC Handling During PPP Negotiation • HSRP • NTP • SNMP Redundancy Support In a RAN-O application, to ensure availability, the backhaul links to a Cisco 3825 router...