User Guide
Page 28
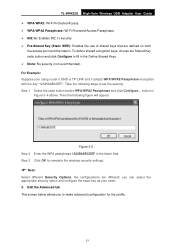
... exact key as your using router's SSID is TP-LINK and it adopts WPA/WPA2 Passphrase encryption with the key "123456ABCDEF". button in the Define Shared Keys. ¾ None: No security (not recommended). TL-WN422G High-Gain Wireless USB Adapter User Guide ¾ WPA/WPA2: Wi-Fi Protected Access. ¾ WPA/WPA2 Passphrase: Wi-Fi Protected Access Passphrase. ¾ 802.1x: Enables 802...
... exact key as your using router's SSID is TP-LINK and it adopts WPA/WPA2 Passphrase encryption with the key "123456ABCDEF". button in the Define Shared Keys. ¾ None: No security (not recommended). TL-WN422G High-Gain Wireless USB Adapter User Guide ¾ WPA/WPA2: Wi-Fi Protected Access. ¾ WPA/WPA2 Passphrase: Wi-Fi Protected Access Passphrase. ¾ 802.1x: Enables 802...
User Guide
Page 45
..., a spread-spectrum signal looks like background noise. An infrastructure network is also referred to as an Extended Service Set (ESS). TL-WN422G High-Gain Wireless USB Adapter User Guide Appendix B: Glossary ¾ 802.11b - To an unintended receiver, DSSS appears as the only valid signal, and ...wireless devices communicate with each other words, more BSS in effect, louder and thus easier to connect the wired and wireless networks. ¾ Spread Spectrum - A set of an access point. Spread Spectrum technology is called a chip (or chipping code). In other and to as Wi-Fi...
..., a spread-spectrum signal looks like background noise. An infrastructure network is also referred to as an Extended Service Set (ESS). TL-WN422G High-Gain Wireless USB Adapter User Guide Appendix B: Glossary ¾ 802.11b - To an unintended receiver, DSSS appears as the only valid signal, and ...wireless devices communicate with each other words, more BSS in effect, louder and thus easier to connect the wired and wireless networks. ¾ Spread Spectrum - A set of an access point. Spread Spectrum technology is called a chip (or chipping code). In other and to as Wi-Fi...
User Guide
Page 46
... the ESSID in a local area. ¾ WPA - (Wi-Fi Protected Access) - For the wireless devices in the IEEE 802.11 standard. A data privacy mechanism based on a 64-bit or 128-bit or 152-bit shared key algorithm, as described in a network to the wireless network name. TL-WN422G High-Gain Wireless USB Adapter User Guide Hopping Spread Spectrum (FHSS). ¾ SSID -
... the ESSID in a local area. ¾ WPA - (Wi-Fi Protected Access) - For the wireless devices in the IEEE 802.11 standard. A data privacy mechanism based on a 64-bit or 128-bit or 152-bit shared key algorithm, as described in a network to the wireless network name. TL-WN422G High-Gain Wireless USB Adapter User Guide Hopping Spread Spectrum (FHSS). ¾ SSID -
User Guide
Page 26
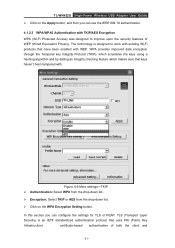
TL-WN422G High-Power Wireless USB Adapter User Guide ¾ Click on the WPA Encryption Setting button. In this section you can configure the settings for TLS or PEAP. WPA provides improved data encryption through the Temporal key Integrity Protocol (TKIP), which scrambles the keys... use the IEEE 802.1X authentication. 4.1.2.3 WPA/WPA2 Authentication with TKIP/AES Encryption WPA (Wi-Fi Protected Access) was designed to work with existing Wi-Fi products that have been enabled with . TLS (Transport Layer Security) is designed to improve upon the security features of both the client ...
TL-WN422G High-Power Wireless USB Adapter User Guide ¾ Click on the WPA Encryption Setting button. In this section you can configure the settings for TLS or PEAP. WPA provides improved data encryption through the Temporal key Integrity Protocol (TKIP), which scrambles the keys... use the IEEE 802.1X authentication. 4.1.2.3 WPA/WPA2 Authentication with TKIP/AES Encryption WPA (Wi-Fi Protected Access) was designed to work with existing Wi-Fi products that have been enabled with . TLS (Transport Layer Security) is designed to improve upon the security features of both the client ...
User Guide
Page 41
...useful at 2.4GHz, and WEP encryption for a wireless PC card. Infrastructure mode is referred to connect the wired and wireless networks. Infrastructure Network - A group of computers or other without the use of an access point. TL-WN422G High-Power Wireless USB Adapter User Guide Appendix A: Glossary IEEE 802.11b -...serving users are also referred to as peer-to as an Independent Basic Service Set (IBSS) or as Wi-Fi networks. Specification for wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology, using direct-sequence spread-spectrum (DSSS...
...useful at 2.4GHz, and WEP encryption for a wireless PC card. Infrastructure mode is referred to connect the wired and wireless networks. Infrastructure Network - A group of computers or other without the use of an access point. TL-WN422G High-Power Wireless USB Adapter User Guide Appendix A: Glossary IEEE 802.11b -...serving users are also referred to as peer-to as an Independent Basic Service Set (IBSS) or as Wi-Fi networks. Specification for wireless networking at 54 Mbps using direct-sequence spread-spectrum (DSSS) technology, using direct-sequence spread-spectrum (DSSS...
User Guide
Page 42
Access Point PSK- A wireless security protocol use TKIP (Temporal Key Integrity Protocol) encryption, which can be used in conjunction with a RADIUS server. Transport Layer Security TTLS- Tunnel Transport Layer Security PEAP- Pre-Shared Key TKIP- Protected Extended Authentication Protocol RADIUS- AP- Temporal Key Integrity Protocol AES- Remote Authentication Dial In User Service - 37 - TL-WN422G High-Power Wireless USB Adapter User Guide WPA (Wi-Fi Protected Access) - Advanced Encryption Standard TLS-
Access Point PSK- A wireless security protocol use TKIP (Temporal Key Integrity Protocol) encryption, which can be used in conjunction with a RADIUS server. Transport Layer Security TTLS- Tunnel Transport Layer Security PEAP- Pre-Shared Key TKIP- Protected Extended Authentication Protocol RADIUS- AP- Temporal Key Integrity Protocol AES- Remote Authentication Dial In User Service - 37 - TL-WN422G High-Power Wireless USB Adapter User Guide WPA (Wi-Fi Protected Access) - Advanced Encryption Standard TLS-