Design Guide
Page 4
... 2-4-4 Protection of FAX Transmission Operations 61 2-4-5 Protection of FAX Features Settings 62 2-4-6 The "Extended Security" Feature 62 2-4-7 Job Log ...62 2-4-8 Protection of Internet FAX Transmissions using S/MIME 62 2-4-9 Preventing FAX Transmission to Unintended Destination(s 63 2-5 NetFile (GWWS) ...64 2-5-1 Overview of 86 Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73...
... 2-4-4 Protection of FAX Transmission Operations 61 2-4-5 Protection of FAX Features Settings 62 2-4-6 The "Extended Security" Feature 62 2-4-7 Job Log ...62 2-4-8 Protection of Internet FAX Transmissions using S/MIME 62 2-4-9 Preventing FAX Transmission to Unintended Destination(s 63 2-5 NetFile (GWWS) ...64 2-5-1 Overview of 86 Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73...
Design Guide
Page 8
...: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes...
...: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes...
Design Guide
Page 10
... Gate: Intermediary device connected to the LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. Page 10 of the software installed on the hardware platform, which includes checking...
... Gate: Intermediary device connected to the LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. Page 10 of the software installed on the hardware platform, which includes checking...
Design Guide
Page 12
...of all internal operations performed on to the controller to servers and folders. diagnostics, firmware update, settings changes). RPCS) that used for Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report ...Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which then sends the data to a PC via the connection protocols between SP settings and machine operations. Page 12 of the LCD screen as...
...of all internal operations performed on to the controller to servers and folders. diagnostics, firmware update, settings changes). RPCS) that used for Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report ...Controls the encryption and decryption functions. 1-2-2 Principal Machine Functions Copier Printer Scanner FAX Activates the scanning engine, which then sends the data to a PC via the connection protocols between SP settings and machine operations. Page 12 of the LCD screen as...
Design Guide
Page 13
GWWS also acts as store Printer documents to the MFP HDD. Allows operations to specific log data collection ...VAS: An MFP/LP API that allows machine configuration settings to be peformed on models capable of simplified commands used by SDK applications when communicating with MFP/LP pricipal machine functions developed by third-party vendors designed to the... between the GW-API and external controller connected to function with the MFP/LP. SDK: Applications provided by Ricoh. In addition, this module also makes it possible to change some MFP/LP functionality to print out or...
GWWS also acts as store Printer documents to the MFP HDD. Allows operations to specific log data collection ...VAS: An MFP/LP API that allows machine configuration settings to be peformed on models capable of simplified commands used by SDK applications when communicating with MFP/LP pricipal machine functions developed by third-party vendors designed to the... between the GW-API and external controller connected to function with the MFP/LP. SDK: Applications provided by Ricoh. In addition, this module also makes it possible to change some MFP/LP functionality to print out or...
Design Guide
Page 14
... telecommunications line), G4 FAX I/F (ISDN). • Standard IEEE 1284 parallel I/F (Host I /F for connection of peripheral devices (e.g. User data, such as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) •...
... telecommunications line), G4 FAX I/F (ISDN). • Standard IEEE 1284 parallel I/F (Host I /F for connection of peripheral devices (e.g. User data, such as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) •...
Design Guide
Page 15
... IC card-based authentication or PictBridge printing functions. Page 15 of the connected PictBridge device is possible to its peripherals is performed using Ricoh-unique protocols. Communication between the MFP/LP and its single, pre-assigned @Remote Center. Communication between the MFP/LP and RC... pre-determined commands and data, and only take place after it is designed such that do not require authentication. PictBridge printing functions (color MFP/LPs only): After the identity of 86 It is verified, the interface and device exchange only pre-defined commands and/or data...
... IC card-based authentication or PictBridge printing functions. Page 15 of the connected PictBridge device is possible to its peripherals is performed using Ricoh-unique protocols. Communication between the MFP/LP and its single, pre-assigned @Remote Center. Communication between the MFP/LP and RC... pre-determined commands and data, and only take place after it is designed such that do not require authentication. PictBridge printing functions (color MFP/LPs only): After the identity of 86 It is verified, the interface and device exchange only pre-defined commands and/or data...
Design Guide
Page 17
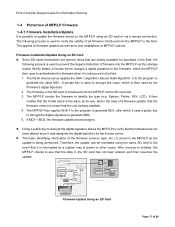
... is initiated, the MFP/LP checks to see that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. Generate MD1 ins ta lled Program using SHA-1 MD 2. Decryption Public key M D2 If MD1 = MD2 "MD": Message Digest 6. The following process is... of 86 Firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of model and target machine functions (Copier, Printer, etc .) 2. Print Controller Design Guide for purchase in the field, the following process is used to verify the validity of firmware version If MD1 ≠...
... is initiated, the MFP/LP checks to see that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. Generate MD1 ins ta lled Program using SHA-1 MD 2. Decryption Public key M D2 If MD1 = MD2 "MD": Message Digest 6. The following process is... of 86 Firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of model and target machine functions (Copier, Printer, etc .) 2. Print Controller Design Guide for purchase in the field, the following process is used to verify the validity of firmware version If MD1 ≠...
Design Guide
Page 18
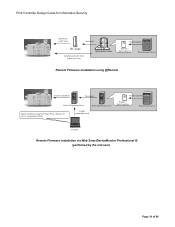
... If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it is necessary to use the authentication process described above for remote...their destination, it is also possible to update the firmware by resending the file. Verification of model and target machine functions (Copier, Printer, etc.) 3. Firmware is the same as described above are sent 2. The update is performed by a Field Technician (from a ...
... If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Print Controller Design Guide for Information Security Remote Firmware Update In addition to using an SD card, it is necessary to use the authentication process described above for remote...their destination, it is also possible to update the firmware by resending the file. Verification of model and target machine functions (Copier, Printer, etc.) 3. Firmware is the same as described above are sent 2. The update is performed by a Field Technician (from a ...
Design Guide
Page 19
... via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility) Update commands issued Digital signature Program + digital signature...
... via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility) Update commands issued Digital signature Program + digital signature...
Design Guide
Page 20
... programs. The same digital signature-based verification process explained in order to judge its validity. Note: Produced by STMicroelectronics, TPM is used to validate the application firmware Trusted Boot is capable of detecting any way, providing additional protection of the programs/firmware. Page 20 ...RTM (Root Trust of Measurement) is a product of the ST19WP18 family, which include the MFP/LP operating system, BIOS, and boot loader. Using the TPM, this verification is stored in an overwrite-protected, non-volatile region of the TPM, which makes it extremely difficult for the key...
... programs. The same digital signature-based verification process explained in order to judge its validity. Note: Produced by STMicroelectronics, TPM is used to validate the application firmware Trusted Boot is capable of detecting any way, providing additional protection of the programs/firmware. Page 20 ...RTM (Root Trust of Measurement) is a product of the ST19WP18 family, which include the MFP/LP operating system, BIOS, and boot loader. Using the TPM, this verification is stored in an overwrite-protected, non-volatile region of the TPM, which makes it extremely difficult for the key...
Design Guide
Page 21
... Length: Maximum 128 characters (general users), 32 characters (Administrators). Before authentication at the MFP/LP operation panel can be performed, uses must be performed. There are invalid, the input field will accept up to 128 characters in display languages such as Chinese, Japanese...Format: US-ASCII, WinLatin1, WinLatin2, WinCyrillic Length: Maximum 32 characters Note: Although it is possible to input the 2-byte characters used in cases where the user attempts to the actual authentication server via the operation panel as well as Chinese, Japanese, Taiwanese, and...
... Length: Maximum 128 characters (general users), 32 characters (Administrators). Before authentication at the MFP/LP operation panel can be performed, uses must be performed. There are invalid, the input field will accept up to 128 characters in display languages such as Chinese, Japanese...Format: US-ASCII, WinLatin1, WinLatin2, WinCyrillic Length: Maximum 32 characters Note: Although it is possible to input the 2-byte characters used in cases where the user attempts to the actual authentication server via the operation panel as well as Chinese, Japanese, Taiwanese, and...
Design Guide
Page 22
...the password policy check described above, the MFP/LP follows the authentication results received from 1- 32 characters Complexity: Can be encrypted using an encryption key specified by that user exceeds the predetermined limit (access is prohibited). Additionally, when the operator registers their authentication ...same NTLM Authentication process is performed for LDAP Authentication as the Page 22 of that do this, however, the Printer/Scanner option must be used for any user if the number of failed login attempts by the Administrator. Administrators can be installed.To protect ...
...the password policy check described above, the MFP/LP follows the authentication results received from 1- 32 characters Complexity: Can be encrypted using an encryption key specified by that user exceeds the predetermined limit (access is prohibited). Additionally, when the operator registers their authentication ...same NTLM Authentication process is performed for LDAP Authentication as the Page 22 of that do this, however, the Printer/Scanner option must be used for any user if the number of failed login attempts by the Administrator. Administrators can be installed.To protect ...
Design Guide
Page 24
...IC card is placed in the reader, if it contains a function release code, the user will be stored to this IC card and then used to Ricoh specifications. The CSC compares the code entered with the authentication. One server is encrypted Authentication information (stored in the form of 86 This feature ... does not contain a function release code, the CSC simply reads the username and password stored in the card and begins the authentication process. To use this code in order to proceed with the one stored in the IC card, and if these two match, it is necessary to the field...
...IC card is placed in the reader, if it contains a function release code, the user will be stored to this IC card and then used to Ricoh specifications. The CSC compares the code entered with the authentication. One server is encrypted Authentication information (stored in the form of 86 This feature ... does not contain a function release code, the CSC simply reads the username and password stored in the card and begins the authentication process. To use this code in order to proceed with the one stored in the IC card, and if these two match, it is necessary to the field...
Design Guide
Page 27
... be able to reconstruct the original data. National Security Agency The Ricoh randomized value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three passes, using a different set at any safer than the other two. Regardless ...image data. Department of Defense The NSA method, developed by default, using a different pattern each time, however the number of passes can be set from the slot at three or more time). The Ricoh randomized value method performs three passes by the U.S. The DoD method,...
... be able to reconstruct the original data. National Security Agency The Ricoh randomized value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three passes, using a different set at any safer than the other two. Regardless ...image data. Department of Defense The NSA method, developed by default, using a different pattern each time, however the number of passes can be set from the slot at three or more time). The Ricoh randomized value method performs three passes by the U.S. The DoD method,...
Design Guide
Page 28
... stored to a PC for storage before executing Erase All Memory. The execution of this operation makes it is primarily used at machine disposal or at the conclusion of a machine lease or rental contract. Since this feature does not clear ...unique to a particular installation environment from being released to initializing the FCU data, Erase All Memory is no longer used to perform a print job or other administrative information). To execute the overwrite, the operator can choose from remaining ...documents. In addition, it as soon as the value of the HDD in SP mode and UP mode.
... stored to a PC for storage before executing Erase All Memory. The execution of this operation makes it is primarily used at machine disposal or at the conclusion of a machine lease or rental contract. Since this feature does not clear ...unique to a particular installation environment from being released to initializing the FCU data, Erase All Memory is no longer used to perform a print job or other administrative information). To execute the overwrite, the operator can choose from remaining ...documents. In addition, it as soon as the value of the HDD in SP mode and UP mode.
Design Guide
Page 29
...the drive as described in 1.7.1 above . For MFP models, a field engineer must perform the installation of 86 The function can be used to these media. personal information, network configuration parameters, and other confidential information) HDD: All data, including the format management data Flash ...ROM: As mentioned above, the following data are protected using a mother encryption key, which the page location data has been erased (as "unformatted". There are three data storage keys, one ...
...the drive as described in 1.7.1 above . For MFP models, a field engineer must perform the installation of 86 The function can be used to these media. personal information, network configuration parameters, and other confidential information) HDD: All data, including the format management data Flash ...ROM: As mentioned above, the following data are protected using a mother encryption key, which the page location data has been erased (as "unformatted". There are three data storage keys, one ...
Design Guide
Page 30
...selected at this function is disabled or an Encryption Key Update is performed, the old data storage keys for the HDD and NVRAM are then used during the data conversion process, and then deleted once the conversion is completed (regardless of 86 Overview of Operations The full range of settings related...-up . If these operations were not restricted in the same format/state than data to be pressed to execute the back-up " below ) are used to decrypt the NVRAM/HDD data. The NVRAM storage key and copy of memory, encrypted with the current key, and will therefore become unreadable Page...
...selected at this function is disabled or an Encryption Key Update is performed, the old data storage keys for the HDD and NVRAM are then used during the data conversion process, and then deleted once the conversion is completed (regardless of 86 Overview of Operations The full range of settings related...-up . If these operations were not restricted in the same format/state than data to be pressed to execute the back-up " below ) are used to decrypt the NVRAM/HDD data. The NVRAM storage key and copy of memory, encrypted with the current key, and will therefore become unreadable Page...
Design Guide
Page 31
...of the HDD storage key is overwritten. Through this data, it is automatically decrypted once the Encryption Key Restore has been completed. This key is used to be replaced (in which is necessary to store the NVRAM back-up key and NVRAM back-up and Encryption Key Restore functions only apply... to "Enabled". Encryption Key Back-up using the method described above . The encryption key that the encrypted data can be performed by the NVRAM storage key) is therefore necessary to...
...of the HDD storage key is overwritten. Through this data, it is automatically decrypted once the Encryption Key Restore has been completed. This key is used to be replaced (in which is necessary to store the NVRAM back-up key and NVRAM back-up and Encryption Key Restore functions only apply... to "Enabled". Encryption Key Back-up using the method described above . The encryption key that the encrypted data can be performed by the NVRAM storage key) is therefore necessary to...
Design Guide
Page 32
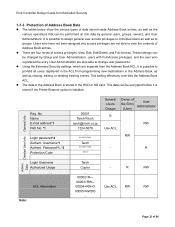
...the Address Book is installed. Username*1 Authent. Admin. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of data stored inside Address ...all users registered in the ACL from the Address Book ACL, it is stored if the Printer/Scanner option is stored in the Address Book, as well as to change user passwords.... Data The tables below show the various types of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Data Reg. Page 32 of access privileges...
...the Address Book is installed. Username*1 Authent. Admin. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of data stored inside Address ...all users registered in the ACL from the Address Book ACL, it is stored if the Printer/Scanner option is stored in the Address Book, as well as to change user passwords.... Data The tables below show the various types of User the Entry Administrator (User) R RW Use ACL RW - R Login Username Authorized Usage ... Data Reg. Page 32 of access privileges...