Security Target
Page 3
... in PP 28 2.4.2 Consistency Claim with Security Problems and Security Objectives in PP .........28 2.4.3 Consistency Claim with Security Requirements in PP 28 3 Security Problem Definitions 31 Copyright (c) 2011 RICOH COMPANY, LTD. Security Functions 22 1.4.5 Protected Assets...23 1.4.5.1. All rights reserved. Page 2 of 87 Table of Contents 1 ST Introduction ...6 1.1 ST Reference ...6 1.2 TOE Reference...
... in PP 28 2.4.2 Consistency Claim with Security Problems and Security Objectives in PP .........28 2.4.3 Consistency Claim with Security Requirements in PP 28 3 Security Problem Definitions 31 Copyright (c) 2011 RICOH COMPANY, LTD. Security Functions 22 1.4.5 Protected Assets...23 1.4.5.1. All rights reserved. Page 2 of 87 Table of Contents 1 ST Introduction ...6 1.1 ST Reference ...6 1.2 TOE Reference...
Security Target
Page 4
... Environment ...35 4.2.2 Non-IT Environment 36 4.3 Security Objectives Rationale 37 4.3.1 Correspondence Table of Security Objectives 37 4.3.2 Security Objectives Descriptions 38 5 Extended Components Definition 42 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 42 6 Security Requirements...44 6.1 Security Functional Requirements 44 6.1.1 Class FAU: Security audit 44 ... ...63 6.3.2 Justification of Traceability 64 6.3.3 Dependency Analysis 70 6.3.4 Security Assurance Requirements Rationale 72 7 TOE Summary Specification 73 Copyright (c) 2011 RICOH COMPANY, LTD.
... Environment ...35 4.2.2 Non-IT Environment 36 4.3 Security Objectives Rationale 37 4.3.1 Correspondence Table of Security Objectives 37 4.3.2 Security Objectives Descriptions 38 5 Extended Components Definition 42 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 42 6 Security Requirements...44 6.1 Security Functional Requirements 44 6.1.1 Class FAU: Security audit 44 ... ...63 6.3.2 Justification of Traceability 64 6.3.3 Dependency Analysis 70 6.3.4 Security Assurance Requirements Rationale 72 7 TOE Summary Specification 73 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 5
... for English Version-2 ...14 Table 4 : Guidance for English Version-3 ...15 Table 5 : Guidance for English Version-4 ...16 Table 6 : Definition of Users ...18 Table 7 : List of Administrative Roles ...18 Table 8: Definition of User Data ...23 Table 9: Definition of TSF Data...24 Table 10: Specific Terms Related to This ST 24 Table 11: Rationale for Security... Functional Requirements 63 Table 35: Result of Dependency Analysis of TOE Security Functional Requirements 70 Table 36: Auditable Events and Audit Data 73 Copyright (c) 2011 RICOH COMPANY, LTD.
... for English Version-2 ...14 Table 4 : Guidance for English Version-3 ...15 Table 5 : Guidance for English Version-4 ...16 Table 6 : Definition of Users ...18 Table 7 : List of Administrative Roles ...18 Table 8: Definition of User Data ...23 Table 9: Definition of TSF Data...24 Table 10: Specific Terms Related to This ST 24 Table 11: Rationale for Security... Functional Requirements 63 Table 35: Result of Dependency Analysis of TOE Security Functional Requirements 70 Table 36: Auditable Events and Audit Data 73 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 11
... SD Card Slot, and SD Card. Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, Definition of Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP... of the stored documents in the TOE. 1.3.3 Major Security Features of 87 - Audit Function - Network Protection Function - Copyright (c) 2011 RICOH COMPANY, LTD. Identification and Authentication Function - Stored Data Protection Function - Page 10 of TOE The TOE stores documents in it, and sends...
... SD Card Slot, and SD Card. Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, Definition of Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP... of the stored documents in the TOE. 1.3.3 Major Security Features of 87 - Audit Function - Network Protection Function - Copyright (c) 2011 RICOH COMPANY, LTD. Identification and Authentication Function - Stored Data Protection Function - Page 10 of TOE The TOE stores documents in it, and sends...
Security Target
Page 18
...-2009 - MP 6001/MP 7001/MP 8001/MP 9001 MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP 6001/7001/8001/9001 Operating Instructions Copy and Document Server Reference - Notes On Energy Saving Functions - Quick Reference Fax Guide - Manuals DataOverwriteSecurity Unit Type H/I - 1.4.3 Definition of Users This section defines the users related to the TOE. Notes for Administrators MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP 6001/MP 7001/MP 8001/MP 9001...
...-2009 - MP 6001/MP 7001/MP 8001/MP 9001 MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP 6001/7001/8001/9001 Operating Instructions Copy and Document Server Reference - Notes On Energy Saving Functions - Quick Reference Fax Guide - Manuals DataOverwriteSecurity Unit Type H/I - 1.4.3 Definition of Users This section defines the users related to the TOE. Notes for Administrators MP 6001/MP 7001/MP 8001/MP 9001 Aficio MP 6001/MP 7001/MP 8001/MP 9001...
Security Target
Page 19
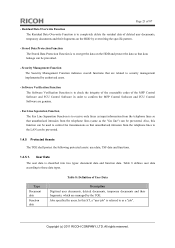
...to delete and register the login password of normal user settings. Authorised to manage normal users. Page 18 of MFP Copyright (c) 2011 RICOH COMPANY, LTD. A normal user is allowed to use the TOE. The "MFP administrator" in this ST refers to multiple MFP ...users. This user consists of the management privilege can be classified as the supervisor and the MFP administrator. Table 6 : Definition of Users Definition of network settings. An administrator performs management operations, which include issuing login names to use the TOE. The administrator means ...
...to delete and register the login password of normal user settings. Authorised to manage normal users. Page 18 of MFP Copyright (c) 2011 RICOH COMPANY, LTD. A normal user is allowed to use the TOE. The "MFP administrator" in this ST refers to multiple MFP ...users. This user consists of the management privilege can be classified as the supervisor and the MFP administrator. Table 6 : Definition of Users Definition of network settings. An administrator performs management operations, which include issuing login names to use the TOE. The administrator means ...
Security Target
Page 24
.... - Jobs specified by authorised users. - Page 23 of deleted user documents, temporary documents and their fragments, which are genuine. - Copyright (c) 2011 RICOH COMPANY, LTD. Type Document data Function data Table 8: Definition of the MFP Control Software and FCU Control Software in order to security management implemented by users. Residual Data Overwrite Function...
.... - Jobs specified by authorised users. - Page 23 of deleted user documents, temporary documents and their fragments, which are genuine. - Copyright (c) 2011 RICOH COMPANY, LTD. Type Document data Function data Table 8: Definition of the MFP Control Software and FCU Control Software in order to security management implemented by users. Residual Data Overwrite Function...
Security Target
Page 25
..., Web Uapl, Network DocBox, animation, Option PCL, OptionPCLFont, LANG0, LANG1 and Data Erase Opt. Type Protected data Confidential data Table 9: Definition of this data is referred to the public. This data must be protected from changes by this ST, "protected data", listed below , ...is exposed to as "TSF protected data". Copyright (c) 2011 RICOH COMPANY, LTD. In this identifier. A password associated with each user. This component is classified into two types: protected data and confidential data...
..., Web Uapl, Network DocBox, animation, Option PCL, OptionPCLFont, LANG0, LANG1 and Data Erase Opt. Type Protected data Confidential data Table 9: Definition of this data is referred to the public. This data must be protected from changes by this ST, "protected data", listed below , ...is exposed to as "TSF protected data". Copyright (c) 2011 RICOH COMPANY, LTD. In this identifier. A password associated with each user. This component is classified into two types: protected data and confidential data...
Security Target
Page 26
... . If a user job is externally received, and its user cannot be terminated. This document is cancelled, the job will be identified. Copyright (c) 2011 RICOH COMPANY, LTD. The minimum number of the attributes associated with user documents. The minimum combination of the characters and symbols that is attempted from the...stored. Page 25 of 87 Terms Auto logout Minimum Length Password Setting Password Complexity HDD User job Documents Document user list Document type Definitions A function for documents (or "user documents", so explicitly referred to be changed by users).
... . If a user job is externally received, and its user cannot be terminated. This document is cancelled, the job will be identified. Copyright (c) 2011 RICOH COMPANY, LTD. The minimum number of the attributes associated with user documents. The minimum combination of the characters and symbols that is attempted from the...stored. Page 25 of 87 Terms Auto logout Minimum Length Password Setting Password Complexity HDD User job Documents Document user list Document type Definitions A function for documents (or "user documents", so explicitly referred to be changed by users).
Security Target
Page 27
... application Application type Available function list Operation Panel Users for stored and received documents Folder transmission Destination folder E-mail transmission S/MIME user information LAN Fax Definitions A general term for each normal user. This attribute can be applicable when a normal user is operating no MFP applications. Consists of Fax Functions. The following..., Scanner Function, Printer Function, and Fax Function. The destination folder is assigned as "PC FAX". One of a touch screen LCD and key switches. Copyright (c) 2011 RICOH COMPANY, LTD.
... application Application type Available function list Operation Panel Users for stored and received documents Folder transmission Destination folder E-mail transmission S/MIME user information LAN Fax Definitions A general term for each normal user. This attribute can be applicable when a normal user is operating no MFP applications. Consists of Fax Functions. The following..., Scanner Function, Printer Function, and Fax Function. The destination folder is assigned as "PC FAX". One of a touch screen LCD and key switches. Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 29
...Function, Printer Function or Fax Function. Therefore, the security problems and security objectives in this TOE type is according to the security problem definitions in chapter 3. FAU_STG.1, FAU_STG.4, FAU_SAR.1, and FAU_SAR.2 are added according to PP APPLICATION NOTE7 in order for the TOE to PP ...APPLICATION NOTE36. Copyright (c) 2011 RICOH COMPANY, LTD. For the authentication function of the TOE, FIA_AFL.1, FIA_UAU.7, and FIA_SOS.1 are added according to maintain and manage the audit...
...Function, Printer Function or Fax Function. Therefore, the security problems and security objectives in this TOE type is according to the security problem definitions in chapter 3. FAU_STG.1, FAU_STG.4, FAU_SAR.1, and FAU_SAR.2 are added according to PP APPLICATION NOTE7 in order for the TOE to PP ...APPLICATION NOTE36. Copyright (c) 2011 RICOH COMPANY, LTD. For the authentication function of the TOE, FIA_AFL.1, FIA_UAU.7, and FIA_SOS.1 are added according to maintain and manage the audit...
Security Target
Page 32
... of this section are unauthorised persons with a login user name but without an access permission to the user job. Copyright (c) 2011 RICOH COMPANY, LTD. Page 31 of 87 3 Security Problem Definitions This section describes Threats, Organisational Security Policies and Assumptions. 3.1 Threats Defined and described below are capable of Basic attack potential. T.CONF...
... of this section are unauthorised persons with a login user name but without an access permission to the user job. Copyright (c) 2011 RICOH COMPANY, LTD. Page 31 of 87 3 Security Problem Definitions This section describes Threats, Organisational Security Policies and Assumptions. 3.1 Threats Defined and described below are capable of Basic attack potential. T.CONF...
Security Target
Page 43
... management activities b) Management of the conditions under which direct forwarding can be considered for the management functions in FMT: a) Definition of the role(s) that are no auditable events foreseen. Management: FPT_FDI_EXP.1 The following actions could be allowed by an administrative...c) Revocation of such an allowance Audit: FPT_FDI_EXP.1 There are connected to the TOE's external interfaces. Rationale: Copyright (c) 2011 RICOH COMPANY, LTD. Many products receive information on specific external interfaces and are sent out on another external interface. Therefore, direct ...
... management activities b) Management of the conditions under which direct forwarding can be considered for the management functions in FMT: a) Definition of the role(s) that are no auditable events foreseen. Management: FPT_FDI_EXP.1 The following actions could be allowed by an administrative...c) Revocation of such an allowance Audit: FPT_FDI_EXP.1 There are connected to the TOE's external interfaces. Rationale: Copyright (c) 2011 RICOH COMPANY, LTD. Many products receive information on specific external interfaces and are sent out on another external interface. Therefore, direct ...
Security Target
Page 45
...] is identified with [bold face and brackets]. 6.1.1 Class FAU: Security audit FAU_GEN.1 Audit data generation Hierarchical to Original: perform an operation on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not defined in CC... the requirement defined in the CC Part2. and b) For each audit record at least the following auditable events: a) Start-up and shutdown of Copyright (c) 2011 RICOH COMPANY, LTD.
...] is identified with [bold face and brackets]. 6.1.1 Class FAU: Security audit FAU_GEN.1 Audit data generation Hierarchical to Original: perform an operation on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not defined in CC... the requirement defined in the CC Part2. and b) For each audit record at least the following auditable events: a) Start-up and shutdown of Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 54
... types: Upper-case letters: [A-Z] (26 letters) Lower-case letters: [a-z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (spaces 33 symbols) Copyright (c) 2011 RICOH COMPANY, LTD. Available function list - FIA_SOS.1.1 The TSF shall provide a mechanism to verify that secrets meet [assignment: the following ...authentication attempts has been [selection: met], the TSF shall [assignment: perform actions shown in Table 25]. FIA_ATD.1 User attribute definition Hierarchical to individual users: [assignment: the security attributes listed in Table 25 for the normal user is released by the ...
... types: Upper-case letters: [A-Z] (26 letters) Lower-case letters: [a-z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (spaces 33 symbols) Copyright (c) 2011 RICOH COMPANY, LTD. Available function list - FIA_SOS.1.1 The TSF shall provide a mechanism to verify that secrets meet [assignment: the following ...authentication attempts has been [selection: met], the TSF shall [assignment: perform actions shown in Table 25]. FIA_ATD.1 User attribute definition Hierarchical to individual users: [assignment: the security attributes listed in Table 25 for the normal user is released by the ...
Security Target
Page 55
.... FIA_UAU.7 Protected authentication feedback Hierarchical to be performed before allowing any other TSF-mediated actions on behalf of that user. Dependencies: FIA_ATD.1 User attribute definition Copyright (c) 2011 RICOH COMPANY, LTD. FIA_UID.1.1 The TSF shall allow [assignment: the viewing of the list of user jobs, Web Image Monitor Help from a Web browser, system...
.... FIA_UAU.7 Protected authentication feedback Hierarchical to be performed before allowing any other TSF-mediated actions on behalf of that user. Dependencies: FIA_ATD.1 User attribute definition Copyright (c) 2011 RICOH COMPANY, LTD. FIA_UID.1.1 The TSF shall allow [assignment: the viewing of the list of user jobs, Web Image Monitor Help from a Web browser, system...
Security Target
Page 63
... 33 lists the assurance components of security measures Developer defined life-cycle model Flaw reporting procedures Conformance claims Extended components definition ST introduction Security objectives Derived security requirements Security problem definition Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is...
... 33 lists the assurance components of security measures Developer defined life-cycle model Flaw reporting procedures Conformance claims Extended components definition ST introduction Security objectives Derived security requirements Security problem definition Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is...
Security Target
Page 78
FIA_ATD.1 (User attribute definition) The TOE associates the normal user with a login user name of normal user and available function list, supervisor with a login user name of supervisor, and ... (3) Lockout release by default). This function uses the characters described below in (1). Table 38: Unlocking Administrators for each user role releases the lockout. Copyright (c) 2011 RICOH COMPANY, LTD. If it does not, it does not register the login password and displays an error message. It checks if the registering or changing...
FIA_ATD.1 (User attribute definition) The TOE associates the normal user with a login user name of normal user and available function list, supervisor with a login user name of supervisor, and ... (3) Lockout release by default). This function uses the characters described below in (1). Table 38: Unlocking Administrators for each user role releases the lockout. Copyright (c) 2011 RICOH COMPANY, LTD. If it does not, it does not register the login password and displays an error message. It checks if the registering or changing...