WGT624v3 Reference Manual
Page 5
... to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support 2-5 Package Contents ...2-5 The Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your...
... to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support 2-5 Package Contents ...2-5 The Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your...
WGT624v3 Reference Manual
Page 8
...Network Preparing Your Computers for TCP/IP Networking C-1 Configuring Windows 95, 98, and Me for TCP/IP Networking C-2 Install or Verify Windows Networking Components C-2 Enabling DHCP to Automatically Configure TCP/IP Settings C-4 Selecting Windows' Internet Access Method C-6 Verifying TCP/IP Properties C-6 Configuring Windows NT4, 2000 or XP for IP Networking... C-7 Install or Verify Windows Networking...IP Networking C-16...Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network...
...Network Preparing Your Computers for TCP/IP Networking C-1 Configuring Windows 95, 98, and Me for TCP/IP Networking C-2 Install or Verify Windows Networking Components C-2 Enabling DHCP to Automatically Configure TCP/IP Settings C-4 Selecting Windows' Internet Access Method C-6 Verifying TCP/IP Properties C-6 Configuring Windows NT4, 2000 or XP for IP Networking... C-7 Install or Verify Windows Networking...IP Networking C-16...Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network...
WGT624v3 Reference Manual
Page 9
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 .../WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18...
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 .../WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18...
WGT624v3 Reference Manual
Page 15
... normally intended for easy monitoring of the NETGEAR WGT624 v3 108 Mbps Wireless Firewall Router. In addition to a wide area network (WAN) device, such as a cable modem or DSL modem. • Extensive Protocol Support. • Login capability. • Front panel LEDs for use the router within minutes. Key Features The WGT624 v3 108 Mbps Wireless Firewall Router with the ability to operate in 802...
... normally intended for easy monitoring of the NETGEAR WGT624 v3 108 Mbps Wireless Firewall Router. In addition to a wide area network (WAN) device, such as a cable modem or DSL modem. • Extensive Protocol Support. • Login capability. • Front panel LEDs for use the router within minutes. Key Features The WGT624 v3 108 Mbps Wireless Firewall Router with the ability to operate in 802...
WGT624v3 Reference Manual
Page 16
... defend against hacker attacks. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by passphrase...
... defend against hacker attacks. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by passphrase...
WGT624v3 Reference Manual
Page 33
... . The default is "g & b", which the wireless interface is NETGEAR, but NETGEAR strongly recommends that fails, select the appropriate value - The same Name (SSID) must be used . 802.11g wireless stations can still be assigned to all wireless devices in a region other than the region shown here. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to...
... . The default is "g & b", which the wireless interface is NETGEAR, but NETGEAR strongly recommends that fails, select the appropriate value - The same Name (SSID) must be used . 802.11g wireless stations can still be assigned to all wireless devices in a region other than the region shown here. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to...
WGT624v3 Reference Manual
Page 34
...the four key boxes will be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption • Security Encryption (WEP) Key: If WEP...WPA-PSK): Enter a word or group of printable characters in the selected key box. For 64 bit WEP: Enter ten hexadecimal digits (any combination of 0-9, A-F). - Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group of printable characters in the...
...the four key boxes will be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption • Security Encryption (WEP) Key: If WEP...WPA-PSK): Enter a word or group of printable characters in the selected key box. For 64 bit WEP: Enter ten hexadecimal digits (any combination of 0-9, A-F). - Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group of printable characters in the...
WGT624v3 Reference Manual
Page 118
...nodes makes the wireless links vulnerable to as SSID. With Open System authentication, a wireless computer can join any network and receive any other , all devices must be referred to eavesdropping and information theft. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad ...11 standard has defined these two types of the wireless local area network. each other node. In an infrastructure wireless network that includes an access point, the ESSID is a thirty-two character (maximum) alphanumeric key identifying the name of authentication methods: • Open...
...nodes makes the wireless links vulnerable to as SSID. With Open System authentication, a wireless computer can join any network and receive any other , all devices must be referred to eavesdropping and information theft. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad ...11 standard has defined these two types of the wireless local area network. each other node. In an infrastructure wireless network that includes an access point, the ESSID is a thirty-two character (maximum) alphanumeric key identifying the name of authentication methods: • Open...
WGT624v3 Reference Manual
Page 119
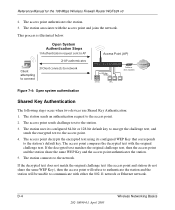
...access point. The access point associates with the Ethernet network through an access point, such as the one built in an Open System network. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. Reference Manual for messages from an access point ...that possess the correct authentication key can now communicate with the station. 8. The station...
...access point. The access point associates with the Ethernet network through an access point, such as the one built in an Open System network. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. Reference Manual for messages from an access point ...that possess the correct authentication key can now communicate with the station. 8. The station...
WGT624v3 Reference Manual
Page 120
... access point. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. This process is illustrated below. The station uses its configured WEP Key that corresponds to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA...
... access point. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. This process is illustrated below. The station uses its configured WEP Key that corresponds to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA...
WGT624v3 Reference Manual
Page 121
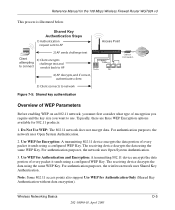
... Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. Reference Manual for Authentication Only (Shared Key Authentication without data encryption). For authentication purposes, the network uses Open System Authentication. 2. The receiving device decrypts the data using the same WEP Key. For authentication purposes, the wireless network uses Shared Key Authentication. Wireless Networking Basics D-5 202-10090-01...
... Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. Reference Manual for Authentication Only (Shared Key Authentication without data encryption). For authentication purposes, the network uses Open System Authentication. 2. The receiving device decrypts the data using the same WEP Key. For authentication purposes, the wireless network uses Shared Key Authentication. Wireless Networking Basics D-5 202-10090-01...
WGT624v3 Reference Manual
Page 122
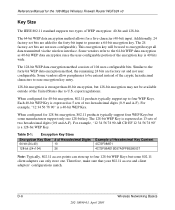
...the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. This encryption key will be available outside of the encryption key ...encryption since the user-configurable portion of the United States due to encrypt/decrypt all data transmitted via the wireless interface. D-6 Wireless Networking Basics 202-10090-01, April 2005 Additionally, 24 factory-set bits are not user-configurable). Some vendors ...
...the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. This encryption key will be available outside of the encryption key ...encryption since the user-configurable portion of the United States due to encrypt/decrypt all data transmitted via the wireless interface. D-6 Wireless Networking Basics 202-10090-01, April 2005 Additionally, 24 factory-set bits are not user-configurable). Some vendors ...
WGT624v3 Reference Manual
Page 123
... between 2.4 GHz and 2.5 GHz. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must have different default WEP Keys as long as its default key to transmit. However, due to spread spectrum effect of the 802.11 client adapters on the network must match on . The two devices will utilize...
... between 2.4 GHz and 2.5 GHz. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must have different default WEP Keys as long as its default key to transmit. However, due to spread spectrum effect of the 802.11 client adapters on the network must match on . The two devices will utilize...
WGT624v3 Reference Manual
Page 125
...Wi-Fi Protected Access products. NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. Support for 802.1x authentication is implemented using Temporal Key Integrity Protocol (TKIP) is required. Wireless Networking Basics D-9 202-10090-01,...1x and the Extensible Authentication Protocol (EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection ...
...Wi-Fi Protected Access products. NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. Support for 802.1x authentication is implemented using Temporal Key Integrity Protocol (TKIP) is required. Wireless Networking Basics D-9 202-10090-01,...1x and the Extensible Authentication Protocol (EAP). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection ...
WGT624v3 Reference Manual
Page 126
...the 802.11 level and is forward compatible with the WPA2 security specification. D-10 202-10090-01, April 2005 Wireless Networking Basics Temporal Key Integrity Protocol (TKIP) - The main pieces of the known WEP vulnerabilities and is discouraged These features are secure IBSS... the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to WPA2 (IEEE 802.11i)? Information in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for example, user names and passwords) and authenticates wireless users before they gain access to the network. WPA...
...the 802.11 level and is forward compatible with the WPA2 security specification. D-10 202-10090-01, April 2005 Wireless Networking Basics Temporal Key Integrity Protocol (TKIP) - The main pieces of the known WEP vulnerabilities and is discouraged These features are secure IBSS... the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to WPA2 (IEEE 802.11i)? Information in Beacon, Probe Response, and (Re) Association Requests. Reference Manual for example, user names and passwords) and authenticates wireless users before they gain access to the network. WPA...
WGT624v3 Reference Manual
Page 127
...plaintext message to ensure messages are used by WPA. 802.1X port access control prevents full access to the network until authentication completes. 802.1X EAPOL-Key packets are not being spoofed. We talk more about TKIP and AES when addressing data privacy below. •...Point (AP). • Data Privacy (Encryption). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the information elements to decide which in possession of the pre-shared key. The supplicant in the station uses the authentication and cipher suite information ...
...plaintext message to ensure messages are used by WPA. 802.1X port access control prevents full access to the network until authentication completes. 802.1X EAPOL-Key packets are not being spoofed. We talk more about TKIP and AES when addressing data privacy below. •...Point (AP). • Data Privacy (Encryption). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the information elements to decide which in possession of the pre-shared key. The supplicant in the station uses the authentication and cipher suite information ...
WGT624v3 Reference Manual
Page 128
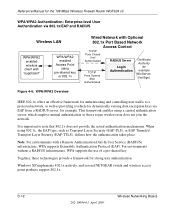
...108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption keys... supports the use of a pre-shared key. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network Access Control TCP/IP Ports Closed Until...
...108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption keys... supports the use of a pre-shared key. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network Access Control TCP/IP Ports Closed Until...
WGT624v3 Reference Manual
Page 129
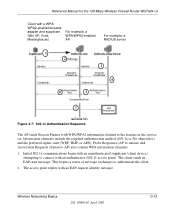
...service set. Wireless Networking Basics 202-10090-01, April 2005 D-13 The access point replies with an authenticator (802.11 access point). Information elements include the required authentication method (802.1x or Pre-shared key) and the... preferred cipher suite (WEP, TKIP, or AES). The client sends an EAP-start message. Probe Responses (AP to station) and Association Requests (station to authenticate the client. 2. This begins a series of message exchanges to AP) also contain WPA information elements. 1. Reference Manual for the 108 Mbps Wireless Firewall Router...
...service set. Wireless Networking Basics 202-10090-01, April 2005 D-13 The access point replies with an authenticator (802.11 access point). Information elements include the required authentication method (802.1x or Pre-shared key) and the... preferred cipher suite (WEP, TKIP, or AES). The client sends an EAP-start message. Probe Responses (AP to station) and Association Requests (station to authenticate the client. 2. This begins a series of message exchanges to AP) also contain WPA information elements. 1. Reference Manual for the 108 Mbps Wireless Firewall Router...
WGT624v3 Reference Manual
Page 130
...only EAP packets from the client to an authentication server located on the client devices. D-14 202-10090-01, April 2005 Wireless Networking Basics The access point blocks all other EAP authentication type. 5. The access point sends an EAP-success packet (or reject packet...some other traffic, such as necessary to minimize the possibility of the key message to the authentication server. For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. The client sends an EAP-response packet containing the ...
...only EAP packets from the client to an authentication server located on the client devices. D-14 202-10090-01, April 2005 Wireless Networking Basics The access point blocks all other EAP authentication type. 5. The access point sends an EAP-success packet (or reject packet...some other traffic, such as necessary to minimize the possibility of the key message to the authentication server. For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. The client sends an EAP-response packet containing the ...
WGT624v3 Reference Manual
Page 131
...conscience organizations, but the problem with AES is that is used to the 802.11 payload and encrypted with WEP. Wireless Networking Basics 202-10090-01, April 2005 D-15 The MIC field is placed between the data portion of the IEEE 802....for each frame. • The determination of a unique starting unicast encryption key for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended ...
...conscience organizations, but the problem with AES is that is used to the 802.11 payload and encrypted with WEP. Wireless Networking Basics 202-10090-01, April 2005 D-15 The MIC field is placed between the data portion of the IEEE 802....for each frame. • The determination of a unique starting unicast encryption key for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended ...