WGT624v3 Reference Manual
Page 5
... to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support 2-5 Package Contents ...2-5 The Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your...
... to Print this Manual 1-3 Chapter 2 Introduction Key Features ...2-1 802.11g Wireless Networking 2-2 A Powerful, True Firewall with Content Filtering 2-2 Security ...2-3 Autosensing Ethernet Connections with Auto Uplink 2-3 Extensive Protocol Support 2-3 Easy Installation and Management 2-4 Maintenance and Support 2-5 Package Contents ...2-5 The Router's Front Panel 2-6 The Router's Rear Panel 2-7 Chapter 3 Configuring the Internet and Wireless Settings Initial Configuration ...3-2 Logging Into Your...
WGT624v3 Reference Manual
Page 8
...Network Preparing Your Computers for TCP/IP Networking C-1 Configuring Windows 95, 98, and Me for TCP/IP Networking C-2 Install or Verify Windows Networking Components C-2 Enabling DHCP to Automatically Configure TCP/IP Settings C-4 Selecting Windows' Internet Access Method C-6 Verifying TCP/IP Properties C-6 Configuring Windows NT4, 2000 or XP for IP Networking... C-7 Install or Verify Windows Networking...IP Networking C-16...Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network...
...Network Preparing Your Computers for TCP/IP Networking C-1 Configuring Windows 95, 98, and Me for TCP/IP Networking C-2 Install or Verify Windows Networking Components C-2 Enabling DHCP to Automatically Configure TCP/IP Settings C-4 Selecting Windows' Internet Access Method C-6 Verifying TCP/IP Properties C-6 Configuring Windows NT4, 2000 or XP for IP Networking... C-7 Install or Verify Windows Networking...IP Networking C-16...Network C-21 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network...
WGT624v3 Reference Manual
Page 9
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 .../WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18...
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 .../WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18...
WGT624v3 Reference Manual
Page 15
.... Parents and network administrators can install and use by a single computer. Chapter 2 Introduction Congratulations on time-of-day, web site addresses and address keywords, and share high-speed cable/DSL Internet access for up to 253 computers. This chapter describes the features of the NETGEAR WGT624 v3 108 Mbps Wireless Firewall Router. Key Features The WGT624 v3 108 Mbps Wireless Firewall Router with multiple web...
.... Parents and network administrators can install and use by a single computer. Chapter 2 Introduction Congratulations on time-of-day, web site addresses and address keywords, and share high-speed cable/DSL Internet access for up to 253 computers. This chapter describes the features of the NETGEAR WGT624 v3 108 Mbps Wireless Firewall Router. Key Features The WGT624 v3 108 Mbps Wireless Firewall Router with multiple web...
WGT624v3 Reference Manual
Page 16
...wireless network to the higher bandwidth 802.11g devices. • 64-bit and 128-bit WEP encryption security. • WEP keys can configure the router to email the log to you specify as blocked incoming traffic, port scans, attacks, and administrator logins. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624... v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted ...
...wireless network to the higher bandwidth 802.11g devices. • 64-bit and 128-bit WEP encryption security. • WEP keys can configure the router to email the log to you specify as blocked incoming traffic, port scans, attacks, and administrator logins. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624... v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted ...
WGT624v3 Reference Manual
Page 33
... field determines which the wireless interface is not the same as NETGEAr. • Region: Select your region from the drop-down list. It should not be used . - b only: All 802.11b wireless stations can be used. 802.11g wireless stations can still be assigned to use channel 6. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure...
... field determines which the wireless interface is not the same as NETGEAr. • Region: Select your region from the drop-down list. It should not be used . - b only: All 802.11b wireless stations can be used. 802.11g wireless stations can still be assigned to use channel 6. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure...
WGT624v3 Reference Manual
Page 34
... characters in length. 3-12 Configuring the Internet and Wireless Settings 202-10090-01, April 2005 Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group of the four key boxes will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption...
... characters in length. 3-12 Configuring the Internet and Wireless Settings 202-10090-01, April 2005 Reference Manual for your network. • Automatic Key Generation (Passphrase): Enter a word or group of the four key boxes will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption...
WGT624v3 Reference Manual
Page 118
...broadcast in the air from an access point. The ESSID is a thirty-two character (maximum) alphanumeric key identifying the name of Service Set Identification (SSID). D-2 Wireless Networking Basics 202-10090-01, April 2005 Some vendors refer to the SSID as the stations are within range ... these two types of a physical connection between nodes makes the wireless links vulnerable to as needed; Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are brought together as SSID. This mode enables you ...
...broadcast in the air from an access point. The ESSID is a thirty-two character (maximum) alphanumeric key identifying the name of Service Set Identification (SSID). D-2 Wireless Networking Basics 202-10090-01, April 2005 Some vendors refer to the SSID as the stations are within range ... these two types of a physical connection between nodes makes the wireless links vulnerable to as needed; Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are brought together as SSID. This mode enables you ...
WGT624v3 Reference Manual
Page 119
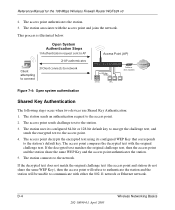
... built in range. 3. These two authentication procedures are in to the WGT624 v3: 1. The station sends an authentication request to the access point. 7. Wireless Networking Basics D-3 202-10090-01, April 2005 Turn on the wireless station. 2. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The access point authenticates the station. 6. The station sends an...
... built in range. 3. These two authentication procedures are in to the WGT624 v3: 1. The station sends an authentication request to the access point. 7. Wireless Networking Basics D-3 202-10090-01, April 2005 Turn on the wireless station. 2. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The access point authenticates the station. 6. The station sends an...
WGT624v3 Reference Manual
Page 120
... station will be unable to the station's default key. D-4 Wireless Networking Basics 202-10090-01, April 2005 The station associates with the access point and joins the network. The station connects to the access point. 2. The station sends an authentication request to the network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. If the decrypted text matches the...
... station will be unable to the station's default key. D-4 Wireless Networking Basics 202-10090-01, April 2005 The station associates with the access point and joins the network. The station connects to the access point. 2. The station sends an authentication request to the network. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. If the decrypted text matches the...
WGT624v3 Reference Manual
Page 121
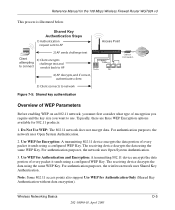
..., there are three WEP Encryption options available for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. For authentication purposes, the wireless network uses Shared Key Authentication. The receiving device decrypts the data using the same WEP Key. Use WEP for Authentication Only (Shared Key Authentication without data encryption). Wireless Networking Basics D-5 202-10090-01, April 2005 Note: Some...
..., there are three WEP Encryption options available for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below. For authentication purposes, the wireless network uses Shared Key Authentication. The receiving device decrypts the data using the same WEP Key. Use WEP for Authentication Only (Shared Key Authentication without data encryption). Wireless Networking Basics D-5 202-10090-01, April 2005 Note: Some...
WGT624v3 Reference Manual
Page 122
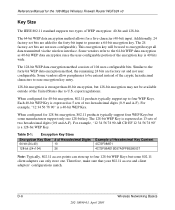
... EF 12 34 56 78 90" is a 40-bit WEP Key. D-6 Wireless Networking Basics 202-10090-01, April 2005 For example, "12 34 56 78 90" is a 128-bit WEP Key. export regulations. Table D-1: Encryption Key Sizes Encryption Key Size # of Hexadecimal Digits 64-bit (24+40) 10 128... The 128-bit WEP data encryption method consists of the encryption key is expressed as 40-bit WEP data encryption since the user-configurable portion of 104 user-configurable bits. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two ...
... EF 12 34 56 78 90" is a 40-bit WEP Key. D-6 Wireless Networking Basics 202-10090-01, April 2005 For example, "12 34 56 78 90" is a 128-bit WEP Key. export regulations. Table D-1: Encryption Key Sizes Encryption Key Size # of Hexadecimal Digits 64-bit (24+40) 10 128... The 128-bit WEP data encryption method consists of the encryption key is expressed as 40-bit WEP data encryption since the user-configurable portion of 104 user-configurable bits. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two ...
WGT624v3 Reference Manual
Page 123
...the AP's WEP key 2 is the same as the client's WEP key 2 and the AP's WEP key 3 is the same as the client's WEP key 3. The radio frequency channels used by the SSID. Wireless Channels The wireless frequencies used in 802.11b/g networks are in the same... below the center channel frequency. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of channel cross-talk, and provide a noticeable performance increase over networks with minimal channel separation. Applying two channels that are within...
...the AP's WEP key 2 is the same as the client's WEP key 2 and the AP's WEP key 3 is the same as the client's WEP key 3. The radio frequency channels used by the SSID. Wireless Channels The wireless frequencies used in 802.11b/g networks are in the same... below the center channel frequency. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of channel cross-talk, and provide a noticeable performance increase over networks with minimal channel separation. Applying two channels that are within...
WGT624v3 Reference Manual
Page 125
...problem with a sniffing tool can monitor your network for 802.1x authentication is required. The 802.11i standard was optional. TKIP replaces WEP with sequencing rules, and a re-keying mechanism. Products based on the 802.11 ...108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is implementing WPA and WPA2 on client and access point products. Starting August of known WEP vulnerabilities. NETGEAR...
...problem with a sniffing tool can monitor your network for 802.1x authentication is required. The 802.11i standard was optional. TKIP replaces WEP with sequencing rules, and a re-keying mechanism. Products based on the 802.11 ...108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is implementing WPA and WPA2 on client and access point products. Starting August of known WEP vulnerabilities. NETGEAR...
WGT624v3 Reference Manual
Page 126
..., such as found in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to the network. The main pieces of operations that are not included in these elements includes the authentication method (802.1X or...
..., such as found in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to the network. The main pieces of operations that are not included in these elements includes the authentication method (802.1X or...
WGT624v3 Reference Manual
Page 127
... to the network until authentication completes. 802.1X EAPOL-Key packets are used for authentication. TKIP includes a message integrity code (MIC) at the end of its weaknesses. • Data integrity. EAP over 802.1X is required by WPA to distribute per-session keys to those stations successfully authenticated. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3...
... to the network until authentication completes. 802.1X EAPOL-Key packets are used for authentication. TKIP includes a message integrity code (MIC) at the end of its weaknesses. • Data integrity. EAP over 802.1X is required by WPA to distribute per-session keys to those stations successfully authenticated. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3...
WGT624v3 Reference Manual
Page 128
... example. For environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. D-12 202-10090-01, April 2005 Wireless Networking Basics Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for... several NETGEAR switch and wireless access point products support 802.1x. It is important to a protected network, as well as providing a vehicle for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with...
... example. For environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. D-12 202-10090-01, April 2005 Wireless Networking Basics Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for... several NETGEAR switch and wireless access point products support 802.1x. It is important to a protected network, as well as providing a vehicle for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with...
WGT624v3 Reference Manual
Page 129
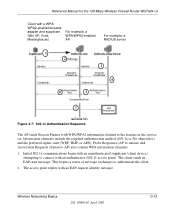
Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10090-01, April 2005 D-13 The client sends an EAP... begin with an unauthenticated supplicant (client device) attempting to AP) also contain WPA information elements. 1. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server ...
Information elements include the required authentication method (802.1x or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). Wireless Networking Basics 202-10090-01, April 2005 D-13 The client sends an EAP... begin with an unauthenticated supplicant (client device) attempting to AP) also contain WPA information elements. 1. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server ...
WGT624v3 Reference Manual
Page 130
... includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. The important part to know at this point is that is synchronized between the wireless client and the wireless access point (AP). With WPA/WPA2, rekeying of unicast encryption keys is required. D-14 202-10090-01, April 2005 Wireless Networking Basics The access point acts as necessary...
... includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. The important part to know at this point is that is synchronized between the wireless client and the wireless access point (AP). With WPA/WPA2, rekeying of unicast encryption keys is required. D-14 202-10090-01, April 2005 Wireless Networking Basics The access point acts as necessary...
WGT624v3 Reference Manual
Page 131
...both the station and the access point. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, ... existing wireless devices. Wireless Networking Basics 202-10090-01, April 2005 D-15 TKIP also provides for the following: • The verification of the security configuration after the encryption keys are determined. • The synchronized changing of the unicast encryption key for ...
...both the station and the access point. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, ... existing wireless devices. Wireless Networking Basics 202-10090-01, April 2005 D-15 TKIP also provides for the following: • The verification of the security configuration after the encryption keys are determined. • The synchronized changing of the unicast encryption key for ...