WGT624v3 Reference Manual
Page 11
... User input Screen text, file and server names, extensions, commands, IP addresses This guide uses the following typographical conventions: Table 1-1. Manual Scope Product Version Manual Publication Date WGT624 v3 108 Mbps Wireless Firewall Router April 2005 Note: Product updates are available on the Netgear website. However, basic computer network, Internet, firewall, and VPN technologies tutorial information is written for the WGT624 v3 wireless router...
... User input Screen text, file and server names, extensions, commands, IP addresses This guide uses the following typographical conventions: Table 1-1. Manual Scope Product Version Manual Publication Date WGT624 v3 108 Mbps Wireless Firewall Router April 2005 Note: Product updates are available on the Netgear website. However, basic computer network, Internet, firewall, and VPN technologies tutorial information is written for the WGT624 v3 wireless router...
WGT624v3 Reference Manual
Page 17
...users outside the LAN from finding and directly accessing the PCs on the LAN. • Port Forwarding with NAT Although NAT prevents Internet locations from directly accessing the PCs on the LAN, the router allows you to control access to a switch or hub. Security The WGT624 v3 wireless router...• PCs Hidden by screening for keywords within web addresses. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • The WGT624 v3 prevents objectionable content from the local network. The router allows you to direct incoming traffic to specific PCs based on the ...
...users outside the LAN from finding and directly accessing the PCs on the LAN. • Port Forwarding with NAT Although NAT prevents Internet locations from directly accessing the PCs on the LAN, the router allows you to control access to a switch or hub. Security The WGT624 v3 wireless router...• PCs Hidden by screening for keywords within web addresses. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • The WGT624 v3 prevents objectionable content from the local network. The router allows you to direct incoming traffic to specific PCs based on the ...
WGT624v3 Reference Manual
Page 18
...user ISP account. • Automatic Configuration of Internet connection, asking you want to install the upgrade. This feature eliminates the need to run a login program such as they become available. 2-4 Introduction 202-10090-01, April 2005 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • IP Address Sharing by NAT The WGT624 v3 wireless router...and operate the WGT624 v3 108 Mbps Wireless Firewall Router within minutes after connecting it asks you if you only for the information required for your Internet service provider (ISP). A user-friendly Setup ...
...user ISP account. • Automatic Configuration of Internet connection, asking you want to install the upgrade. This feature eliminates the need to run a login program such as they become available. 2-4 Introduction 202-10090-01, April 2005 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • IP Address Sharing by NAT The WGT624 v3 wireless router...and operate the WGT624 v3 108 Mbps Wireless Firewall Router within minutes after connecting it asks you if you only for the information required for your Internet service provider (ISP). A user-friendly Setup ...
WGT624v3 Reference Manual
Page 25
...Manual for the router password, both in lower case letters (or enter the password you chose if you changed it during the setup in to your router, do the following: 1. A login window like the one shown below opens: Figure 3-3: Login window Configuring the Internet and Wireless Settings 3-3 202-10090-01, April 2005 Note: The router user...your Internet connection. When prompted, enter admin for the router user name and password for the 108 Mbps Wireless Firewall Router WGT624 v3 If you want to change your Internet or wireless settings later, see "Changing Your Configuration" on page ...
...Manual for the router password, both in lower case letters (or enter the password you chose if you changed it during the setup in to your router, do the following: 1. A login window like the one shown below opens: Figure 3-3: Login window Configuring the Internet and Wireless Settings 3-3 202-10090-01, April 2005 Note: The router user...your Internet connection. When prompted, enter admin for the router user name and password for the 108 Mbps Wireless Firewall Router WGT624 v3 If you want to change your Internet or wireless settings later, see "Changing Your Configuration" on page ...
WGT624v3 Reference Manual
Page 30
... name or user name in this box. For example, if your ISP's mail server is mail.xxx.yyy.zzz, you may leave this is also referred to you by your ISP. If you have a Domain name given to as the Domain Name. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 If... you have a fixed (static, permanent) IP address, your ISP will have provided you connect. You may require a Host name of your ISP did not provide you with a fixed IP address, the router will find an IP address for...
... name or user name in this box. For example, if your ISP's mail server is mail.xxx.yyy.zzz, you may leave this is also referred to you by your ISP. If you have a Domain name given to as the Domain Name. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 If... you have a fixed (static, permanent) IP address, your ISP will have provided you connect. You may require a Host name of your ISP did not provide you with a fixed IP address, the router will find an IP address for...
WGT624v3 Reference Manual
Page 36
...) can be sure that PC's IP address in the Schedule menu. You may specify one Trusted User, which is shown below: Figure 4-2: Block Services menu 4-2 202-10090-01, April 2005 Content Filtering Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 To enable keyword blocking, select either "Per Schedule" or "Always", then click Apply. To delete...
...) can be sure that PC's IP address in the Schedule menu. You may specify one Trusted User, which is shown below: Figure 4-2: Block Services menu 4-2 202-10090-01, April 2005 Content Filtering Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 To enable keyword blocking, select either "Per Schedule" or "Always", then click Apply. To delete...
WGT624v3 Reference Manual
Page 37
... servers serve web pages, time servers serve time and date information, and game hosts serve data about other applications are typically chosen from user groups of newsgroups. For example, a packet that a time period is an HTTP (web server) request. This information can usually be... "Assigned Numbers." To specify a service for blocking, click Add. If you are not limited to these choices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Services are functions performed by contacting the publisher of the application or from the range 1024 to 65535 by the authors...
... servers serve web pages, time servers serve time and date information, and game hosts serve data about other applications are typically chosen from user groups of newsgroups. For example, a packet that a time period is an HTTP (web server) request. This information can usually be... "Assigned Numbers." To specify a service for blocking, click Add. If you are not limited to these choices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Services are functions performed by contacting the publisher of the application or from the range 1024 to 65535 by the authors...
WGT624v3 Reference Manual
Page 40
...have accessed or attempted to send the log. If the Weekly, Daily or Hourly option is selected and the log fills up . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Your outgoing mail server Enter the name of your ISP's outgoing (SMTP) mail server (such as required. Specifies which day...sent daily or weekly. If you turn on the Internet. Time for the Trusted User. Relevant when the log is sent but not the log. When you don't want logs sent, select None from the router's memory. Select your local time zone. You may fill up before the specified ...
...have accessed or attempted to send the log. If the Weekly, Daily or Hourly option is selected and the log fills up . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Your outgoing mail server Enter the name of your ISP's outgoing (SMTP) mail server (such as required. Specifies which day...sent daily or weekly. If you turn on the Internet. Time for the Trusted User. Relevant when the log is sent but not the log. When you don't want logs sent, select None from the router's memory. Select your local time zone. You may fill up before the specified ...
WGT624v3 Reference Manual
Page 49
... menu allow you to save your settings, select the Backup tab. To save and retrieve a file containing your router's configuration settings. Reference Manual for a location on your PC or click the Browse button to browse to the file. Figure 5-6: Settings Backup...Backup button. When you for the 108 Mbps Wireless Firewall Router WGT624 v3 Configuration File Management The configuration settings of the browser interface, under the Maintenance heading, select the Settings Backup heading to bring up ) to a user's PC, retrieved (restored) from the user's PC, or cleared to store the...
... menu allow you to save your settings, select the Backup tab. To save and retrieve a file containing your router's configuration settings. Reference Manual for a location on your PC or click the Browse button to browse to the file. Figure 5-6: Settings Backup...Backup button. When you for the 108 Mbps Wireless Firewall Router WGT624 v3 Configuration File Management The configuration settings of the browser interface, under the Maintenance heading, select the Settings Backup heading to bring up ) to a user's PC, retrieved (restored) from the user's PC, or cleared to store the...
WGT624v3 Reference Manual
Page 53
... second computer's port number would be 26901, and the third computer would be found in the default listing and add +1 for example, an Internet user can be 26902. 4. Click the button of an unused port in the Start Port box. Change the beginning port number in the table. 2. ...://172.16.1.23. The assigned IP address can access your ISP. Type the IP address of the additional computer in this example). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Local Web and FTP Server Example If a local PC with a private IP address of 192.168.1.33 acts as a web and...
... second computer's port number would be 26901, and the third computer would be found in the default listing and add +1 for example, an Internet user can be 26902. 4. Click the button of an unused port in the Start Port box. Change the beginning port number in the table. 2. ...://172.16.1.23. The assigned IP address can access your ISP. Type the IP address of the additional computer in this example). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Local Web and FTP Server Example If a local PC with a private IP address of 192.168.1.33 acts as a web and...
WGT624v3 Reference Manual
Page 60
... of the dynamic DNS service providers whose names appear in resolving your dynamic DNS account. 6. Type the Password (or key) for the 108 Mbps Wireless Firewall Router WGT624 v3 To configure Dynamic DNS: 1. For example, the wildcard feature will cause *.yourhost.dyndns.org to be aliased to www.dyndns.org....that your dynamic DNS service provider gave you may select the Use wildcards check box to save your dynamic DNS Service Provider. 4. Reference Manual for your dynamic DNS account. 7. Register for dyndns.org, go to the same IP address as yourhost.dyndns.org 8. For example...
... of the dynamic DNS service providers whose names appear in resolving your dynamic DNS account. 6. Type the Password (or key) for the 108 Mbps Wireless Firewall Router WGT624 v3 To configure Dynamic DNS: 1. For example, the wildcard feature will cause *.yourhost.dyndns.org to be aliased to www.dyndns.org....that your dynamic DNS service provider gave you may select the Use wildcards check box to save your dynamic DNS Service Provider. 4. Reference Manual for your dynamic DNS account. 7. Register for dyndns.org, go to the same IP address as yourhost.dyndns.org 8. For example...
WGT624v3 Reference Manual
Page 67
...ideal password should contain no dictionary words from any language, and should be a mixture of your router for the 108 Mbps Wireless Firewall Router WGT624 v3 Enabling Remote Management Access Using the Remote Management page, you can be up to 30 characters..., restrict access to access the router's remote management. Select the Turn Remote Management On check box. 2. To allow a user or users on the Internet, select Everyone. Figure 6-9: Remote Management screen To configure your WGT624 v3 wireless router. Note: Be sure to change the router's default configuration password to a ...
...ideal password should contain no dictionary words from any language, and should be a mixture of your router for the 108 Mbps Wireless Firewall Router WGT624 v3 Enabling Remote Management Access Using the Remote Management page, you can be up to 30 characters..., restrict access to access the router's remote management. Select the Turn Remote Management On check box. 2. To allow a user or users on the Internet, select Everyone. Figure 6-9: Remote Management screen To configure your WGT624 v3 wireless router. Note: Be sure to change the router's default configuration password to a ...
WGT624v3 Reference Manual
Page 82
... class has been determined, the software can contact IANA at www.iana.org. Using RIP, routers periodically update one another and check for most home applications. Individual users and small organizations may vary depending on a network. The address is easier to remember and ..., April 2005 Blocks of the network is used by a router to build and maintain a picture of addresses are assigned to organizations by the Internet Assigned Numbers Authority (IANA). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Routing Information Protocol One of the protocols used by the...
... class has been determined, the software can contact IANA at www.iana.org. Using RIP, routers periodically update one another and check for most home applications. Individual users and small organizations may vary depending on a network. The address is easier to remember and ..., April 2005 Blocks of the network is used by a router to build and maintain a picture of addresses are assigned to organizations by the Internet Assigned Numbers Authority (IANA). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Routing Information Protocol One of the protocols used by the...
WGT624v3 Reference Manual
Page 87
...the Internet simultaneously, you can be statically or dynamically assigned by a single user with all devices on the segment must agree on which bits comprise the host address. • So that a local router or bridge recognizes which addresses are local and which are remote Private IP ...the Internet (for example, when using only a single IP address, which may be either private addresses or registered addresses. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • So that is globally unique on the Internet. In order for this range. For more costly than...
...the Internet simultaneously, you can be statically or dynamically assigned by a single user with all devices on the segment must agree on which bits comprise the host address. • So that a local router or bridge recognizes which addresses are local and which are remote Private IP ...the Internet (for example, when using only a single IP address, which may be either private addresses or registered addresses. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • So that is globally unique on the Internet. In order for this range. For more costly than...
WGT624v3 Reference Manual
Page 88
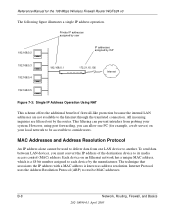
...LAN devices, you can prevent intruders from one PC (for the 108 Mbps Wireless Firewall Router WGT624 v3 The following figure illustrates a single IP address operation. However, using port forwarding, you... must convert the IP address of firewall-like protection because the internal LAN addresses are filtered out by ISP 192.168...to be used to deliver data from probing your system. B-8 Network, Routing, Firewall, and Basics 202-10090-01, April 2005 Reference Manual for example, a web server) on an Ethernet network has a unique MAC ...
...LAN devices, you can prevent intruders from one PC (for the 108 Mbps Wireless Firewall Router WGT624 v3 The following figure illustrates a single IP address operation. However, using port forwarding, you... must convert the IP address of firewall-like protection because the internal LAN addresses are filtered out by ISP 192.168...to be used to deliver data from probing your system. B-8 Network, Routing, Firewall, and Basics 202-10090-01, April 2005 Reference Manual for example, a web server) on an Ethernet network has a unique MAC ...
WGT624v3 Reference Manual
Page 89
... IP address data and MAC address data for each station are held in order for a user to actually contact the resource. For more information about address assignment, refer to the IETF ... so that only the station with this IP address responds to the ARP request. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 If a device sends data to another station on the network receive and read the... Just as a telephone directory maps names to phone numbers, or as www.NETGEAR.com. When a PC accesses a resource by simple descriptive names such as an ARP table maps IP...
... IP address data and MAC address data for each station are held in order for a user to actually contact the resource. For more information about address assignment, refer to the IETF ... so that only the station with this IP address responds to the ARP request. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 If a device sends data to another station on the network receive and read the... Just as a telephone directory maps names to phone numbers, or as www.NETGEAR.com. When a PC accesses a resource by simple descriptive names such as an ARP table maps IP...
WGT624v3 Reference Manual
Page 91
... operating or communicating by your router or gateway. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Stateful Packet Inspection Unlike simple Internet sharing routers, a firewall uses a process called stateful packet inspection to ensure secure firewall filtering to protect your network... Brown/White 8 Brown Network, Routing, Firewall, and Basics 202-10090-01, April 2005 B-11 Some operating systems can handle. Ethernet Cabling Most Ethernet networks now use unshielded twisted pair (UTP) cabling. Since user-level applications such as described in the ...
... operating or communicating by your router or gateway. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Stateful Packet Inspection Unlike simple Internet sharing routers, a firewall uses a process called stateful packet inspection to ensure secure firewall filtering to protect your network... Brown/White 8 Brown Network, Routing, Firewall, and Basics 202-10090-01, April 2005 B-11 Some operating systems can handle. Ethernet Cabling Most Ethernet networks now use unshielded twisted pair (UTP) cabling. Since user-level applications such as described in the ...
WGT624v3 Reference Manual
Page 112
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Verifying the Readiness of the configuration information is dynamically assigned when your PC is first booted up while connected to the ISP, and you ... be a separate physical box (not a card) and must provide an Ethernet port intended for a single-user Internet access account using a cable modem or DSL modem. When the firewall's Internet port is connected to the broadband modem, the firewall appears to uninstall the login program. After your PC. Some ISPs require a special login protocol...
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Verifying the Readiness of the configuration information is dynamically assigned when your PC is first booted up while connected to the ISP, and you ... be a separate physical box (not a card) and must provide an Ethernet port intended for a single-user Internet access account using a cable modem or DSL modem. When the firewall's Internet port is connected to the broadband modem, the firewall appears to uninstall the login program. After your PC. Some ISPs require a special login protocol...
WGT624v3 Reference Manual
Page 122
...-bit key. The 24 factory-set and not user configurable. Some vendors refer to encrypt/decrypt all data transmitted via the wireless interface. Each 40-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). When configured for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports... support only one . For example, "12 34 56 78 90 AB CD EF 12 34 56 78 90" is a 40-bit WEP Key. Reference Manual for 128-bit encryption, 802.11 products typically support four WEP Keys but some 802.11 client adapters can store up to four 128-bit...
...-bit key. The 24 factory-set and not user configurable. Some vendors refer to encrypt/decrypt all data transmitted via the wireless interface. Each 40-bit WEP Key is expressed as 13 sets of two hexadecimal digits (0-9 and A-F). When configured for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports... support only one . For example, "12 34 56 78 90 AB CD EF 12 34 56 78 90" is a 40-bit WEP Key. Reference Manual for 128-bit encryption, 802.11 products typically support four WEP Keys but some 802.11 client adapters can store up to four 128-bit...
WGT624v3 Reference Manual
Page 125
...in WPA. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is not intended as a user authentication mechanism. A ...standard is required in 2004. Products based on a particular wireless LAN must use the same encryption key. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). NETGEAR is implementing WPA and WPA2 on EAP specifically, refer to...
...in WPA. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is not intended as a user authentication mechanism. A ...standard is required in 2004. Products based on a particular wireless LAN must use the same encryption key. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). NETGEAR is implementing WPA and WPA2 on EAP specifically, refer to...