FVS114 Reference Manual
Page 59
... two or more NETGEAR VPN-enabled firewalls is configured on the WAN port, configure the VPN using FDQN. See "How to Set Up a Gateway-to-Gateway VPN Configuration" on page...VPN tunnel end points. This set of the WAN port can change from time to time. Many DSL accounts are provisioned with a dynamic DNS (DynDNS) service provider simplifies the configuration task. Reference Manual for the ProSafe VPN Firewall FVS114 VPN Gateway A VPN Tunnel VPN Gateway B PCs PCs Figure 5-2: Gateway-to-gateway VPN tunnel A VPN between the two VPN endpoints. VPN tunnels also enable access...
... two or more NETGEAR VPN-enabled firewalls is configured on the WAN port, configure the VPN using FDQN. See "How to Set Up a Gateway-to-Gateway VPN Configuration" on page...VPN tunnel end points. This set of the WAN port can change from time to time. Many DSL accounts are provisioned with a dynamic DNS (DynDNS) service provider simplifies the configuration task. Reference Manual for the ProSafe VPN Firewall FVS114 VPN Gateway A VPN Tunnel VPN Gateway B PCs PCs Figure 5-2: Gateway-to-gateway VPN tunnel A VPN between the two VPN endpoints. VPN tunnels also enable access...
FVS114 Reference Manual
Page 101
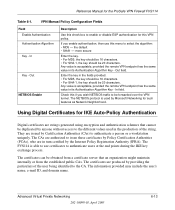
...use this if you wish NETBIOS traffic to be duplicated by anyone without access to the different values used by the Internet Policy Registration Authority (IPRA). Using Digital Certificates for the ProSafe VPN Firewall FVS114 Table 6-1. The certificates are issued by providing the particulars of the ...certificates to authenticate users at the end points during the IKE key exchange process. The certificates can be obtained from a certificate server that cannot be forwarded over the VPN tunnel. Out NETBIOS Enable Description Use this VPN policy. The CAs are authorized to ...
...use this if you wish NETBIOS traffic to be duplicated by anyone without access to the different values used by the Internet Policy Registration Authority (IPRA). Using Digital Certificates for the ProSafe VPN Firewall FVS114 Table 6-1. The certificates are issued by providing the particulars of the ...certificates to authenticate users at the end points during the IKE key exchange process. The certificates can be obtained from a certificate server that cannot be forwarded over the VPN tunnel. Out NETBIOS Enable Description Use this VPN policy. The CAs are authorized to ...
FVS114 Reference Manual
Page 139
...points have current device status at the expense of steps allowed to propagate for each UPnP packet sent. Advanced Configuration 202-10098-01, April 2005 8-13 If disabled, the router will advertise (broadcast) its UPnP information. UPnP Reference Manual for the ProSafe VPN Firewall FVS114... Universal Plug and Play (UPnP) helps devices, such as Internet appliances and computers, access the network and connect to other registered UPnP...
...points have current device status at the expense of steps allowed to propagate for each UPnP packet sent. Advanced Configuration 202-10098-01, April 2005 8-13 If disabled, the router will advertise (broadcast) its UPnP information. UPnP Reference Manual for the ProSafe VPN Firewall FVS114... Universal Plug and Play (UPnP) helps devices, such as Internet appliances and computers, access the network and connect to other registered UPnP...
FVS114 Reference Manual
Page 168
...extranets include supply-chain management, development partnerships, and subscription services. IPSec-based VPNs are secure connections between communication points across IP networks. IPSec Components IPSec contains the following security features when transferring..., and access availability. A dial-up a secure IPSec-based VPN communications to access e-mail and business applications. Remote access VPNs greatly reduce expenses by protecting data while in the packet). Common uses for the ProSafe VPN Firewall FVS114 • Remote Access: Remote access enables telecommuters...
...extranets include supply-chain management, development partnerships, and subscription services. IPSec-based VPNs are secure connections between communication points across IP networks. IPSec Components IPSec contains the following security features when transferring..., and access availability. A dial-up a secure IPSec-based VPN communications to access e-mail and business applications. Remote access VPNs greatly reduce expenses by protecting data while in the packet). Common uses for the ProSafe VPN Firewall FVS114 • Remote Access: Remote access enables telecommuters...
FVS114 Reference Manual
Page 184
...radio button to the left of it to the end of Windows on this version of the Wizard. Repeat these steps for the ProSafe VPN Firewall FVS114 • By default, the IP Address tab is open on your PC is required to enable the DHCP server to automatically assign...Verifying TCP/IP Properties After your network. On the Windows taskbar, click the Start button, point to continue. Select I want to connect through a Local Area Network and click Next. 5. Selecting Windows' Internet Access Method 1. This setting is configured and has rebooted, you can check the TCP/IP configuration ...
...radio button to the left of it to the end of Windows on this version of the Wizard. Repeat these steps for the ProSafe VPN Firewall FVS114 • By default, the IP Address tab is open on your PC is required to enable the DHCP server to automatically assign...Verifying TCP/IP Properties After your network. On the Windows taskbar, click the Start button, point to continue. Select I want to connect through a Local Area Network and click Next. 5. Selecting Windows' Internet Access Method 1. This setting is configured and has rebooted, you can check the TCP/IP configuration ...
FVS114 Reference Manual
Page 197
...for use this example, the domain suffix is xxx.yyy.com. On the Windows taskbar, click the Start button, point to configure the firewall for Internet access: 1. Select TCP/IP, and then click Properties. Preparing Your Network 202-10098-01, April 2005 D-19 If...you configure the FVS114 VPN Firewall. Select the Gateway tab. Click "Obtain an IP address automatically". 5. Reference Manual for the ProSafe VPN Firewall FVS114 • An IP address and subnet mask • A gateway IP address, which displays a list of installed components. 3. If any of the ISP's router • One...
...for use this example, the domain suffix is xxx.yyy.com. On the Windows taskbar, click the Start button, point to configure the firewall for Internet access: 1. Select TCP/IP, and then click Properties. Preparing Your Network 202-10098-01, April 2005 D-19 If...you configure the FVS114 VPN Firewall. Select the Gateway tab. Click "Obtain an IP address automatically". 5. Reference Manual for the ProSafe VPN Firewall FVS114 • An IP address and subnet mask • A gateway IP address, which displays a list of installed components. 3. If any of the ISP's router • One...
FVS114 Reference Manual
Page 207
Reference Manual for the ProSafe VPN Firewall FVS114 M MAC (1) Medium Access Control. The MAC sublayer includes the method of Computing Terms) MAC address The Media Access Control address is a unique 48-bit hardware address assigned to every network interface card. In computer security, a value...concept of transmit and receive are as Media Dependant Interface - Point-to the Internet. Mbps Megabits per second. This wiring is reversed, and the hub receives on pins 1 and 2. At the hub, switch, router, or access point, the perspective is referred to the transmission medium. (2) ...
Reference Manual for the ProSafe VPN Firewall FVS114 M MAC (1) Medium Access Control. The MAC sublayer includes the method of Computing Terms) MAC address The Media Access Control address is a unique 48-bit hardware address assigned to every network interface card. In computer security, a value...concept of transmit and receive are as Media Dependant Interface - Point-to the Internet. Mbps Megabits per second. This wiring is reversed, and the hub receives on pins 1 and 2. At the hub, switch, router, or access point, the perspective is referred to the transmission medium. (2) ...