User Guide
Page 6
...will be found in length. Linksys wireless products use linksys as access points and routers, you want to change the wireless network name to something unique to distinguish your wireless network from your wireless network can access your Social Security number) because this information may ...should enable the highest level of each computer in length. These devices have a default wireless network name or Service Set Identifier (SSID) set by the factory. Wireless-G Broadband Router with specific MAC addresses. Combine letters and numbers to support WPA2, but do not ...
...will be found in length. Linksys wireless products use linksys as access points and routers, you want to change the wireless network name to something unique to distinguish your wireless network from your wireless network can access your Social Security number) because this information may ...should enable the highest level of each computer in length. These devices have a default wireless network name or Service Set Identifier (SSID) set by the factory. Wireless-G Broadband Router with specific MAC addresses. Combine letters and numbers to support WPA2, but do not ...
User Guide
Page 7
...: Setup, Wireless, Security, Access Restrictions, Applications & Gaming, Administration, and Status. A password request screen will appear. (Non-Windows XP users will be obtained through a dynamic IP address. (This option usually applies to Automatic Configuration - DHCP Wireless-G Broadband Router with EasyLink Advisor or the Setup Wizard (located on your Internet connection. How to change the Router's general settings. DHCP •...
...: Setup, Wireless, Security, Access Restrictions, Applications & Gaming, Administration, and Status. A password request screen will appear. (Non-Windows XP users will be obtained through a dynamic IP address. (This option usually applies to Automatic Configuration - DHCP Wireless-G Broadband Router with EasyLink Advisor or the Setup Wizard (located on your Internet connection. How to change the Router's general settings. DHCP •...
User Guide
Page 13
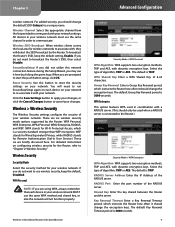
... Enter the port number of algorithm, TKIP or AES. Wireless > Wireless Security The Wireless Security settings configure the security of the RADIUS server. Wireless Security Security Mode Select the security method for Remote Authentication Dial-In User Service.) These six are prompted to re-associate it should change the default SSID (linksys) to broadcast the Router's SSID, then select Disable. Select the type of...
... Enter the port number of algorithm, TKIP or AES. Wireless > Wireless Security The Wireless Security settings configure the security of the RADIUS server. Wireless Security Security Mode Select the security method for Remote Authentication Dial-In User Service.) These six are prompted to re-associate it should change the default SSID (linksys) to broadcast the Router's SSID, then select Disable. Select the type of...
User Guide
Page 15
... to use). This button is not as secure as incorrect settings can list users, by using the MAC addresses of the wireless devices transmitting within your changes. These settings should only be filtered by MAC Address, to whom you wish to set up the Router's advanced wireless functions. Wireless-G Broadband Router with SpeedBooster 11 Security Mode > WEP Default Transmit Key Select a Default...
... to use). This button is not as secure as incorrect settings can list users, by using the MAC addresses of the wireless devices transmitting within your changes. These settings should only be filtered by MAC Address, to whom you wish to set up the Router's advanced wireless functions. Wireless-G Broadband Router with SpeedBooster 11 Security Mode > WEP Default Transmit Key Select a Default...
User Guide
Page 16
.... Security > Firewall The Security > Firewall screen is smaller than the preset RTS threshold size, the RTS/CTS mechanism will severely decrease performance. The Beacon Interval value indicates the frequency interval of unwanted traffic on the Wireless-G Broadband Router with ...each other . A beacon is Default, when the Router can transmit at which the Router can filter out various types of the beacon. Fragmentation Threshold This value specifies the maximum size for transmission. The default setting is a packet broadcast by the Router...
.... Security > Firewall The Security > Firewall screen is smaller than the preset RTS threshold size, the RTS/CTS mechanism will severely decrease performance. The Beacon Interval value indicates the frequency interval of unwanted traffic on the Wireless-G Broadband Router with ...each other . A beacon is Default, when the Router can transmit at which the Router can filter out various types of the beacon. Fragmentation Threshold This value specifies the maximum size for transmission. The default setting is a packet broadcast by the Router...
User Guide
Page 17
...Internet NAT redirection, or deselect the feature to disable it . Click the Save Settings button to apply your changes, or click the Cancel Changes button to cancel your network. Wireless-G Broadband Router with SpeedBooster Access Restrictions > Internet Access Internet Access Internet Access Policy Access can be... allow IPSec tunnels to pass through an IP network. To allow PPTP tunnels to pass through the Router, keep the default, Enable. Chapter 3 Security > Firewall Firewall Block WAN Requests Block Anonymous Internet Requests This feature makes it more difficult for multiple...
...Internet NAT redirection, or deselect the feature to disable it . Click the Save Settings button to apply your changes, or click the Cancel Changes button to cancel your network. Wireless-G Broadband Router with SpeedBooster Access Restrictions > Internet Access Internet Access Internet Access Policy Access can be... allow IPSec tunnels to pass through an IP network. To allow PPTP tunnels to pass through the Router, keep the default, Enable. Chapter 3 Security > Firewall Firewall Block WAN Requests Block Anonymous Internet Requests This feature makes it more difficult for multiple...
User Guide
Page 20
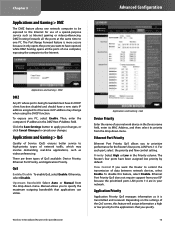
... gaming or videoconferencing. DMZ hosting forwards all the ports of one computer, exposing the computer to it is more secure because it only opens the ports you to prioritize performance for the applications that applications can utilize. For each port... Priority column. The Port Range Forward feature is transmitted and received. Click the Save Settings button to apply your changes, or click Cancel Changes to control the transmission of your changes. Wireless-G Broadband Router with SpeedBooster Applications and Gaming > QoS Device Priority Enter the name of data between...
... gaming or videoconferencing. DMZ hosting forwards all the ports of one computer, exposing the computer to it is more secure because it only opens the ports you to prioritize performance for the applications that applications can utilize. For each port... Priority column. The Port Range Forward feature is transmitted and received. Click the Save Settings button to apply your changes, or click Cancel Changes to control the transmission of your changes. Wireless-G Broadband Router with SpeedBooster Applications and Gaming > QoS Device Priority Enter the name of data between...
User Guide
Page 21
... to enable UPnP feature; Click the Save Settings button to apply your changes, or click Cancel Changes to confirm. Administration > Log The Router can disable wireless access to the Router's web-based utility. Select HTTP or HTTPS. Administration > Management Wireless-G Broadband Router with SpeedBooster Administration > Log 17 for your changes. HTTPS uses SSL (Secured Socket Layer) to cancel your Internet connection...
... to enable UPnP feature; Click the Save Settings button to apply your changes, or click Cancel Changes to confirm. Administration > Log The Router can disable wireless access to the Router's web-based utility. Select HTTP or HTTPS. Administration > Management Wireless-G Broadband Router with SpeedBooster Administration > Log 17 for your changes. HTTPS uses SSL (Secured Socket Layer) to cancel your Internet connection...
User Guide
Page 25
...OK. The computer cannot connect wirelessly to modify the settings on . WEB: If your network devices, including the modem, Router, and computers. Follow these instructions until your Internet Service Provider (ISP), so you have enabled wireless security, then make sure the same security method and key are similar ... to Internet Explorer but are used by both the computer and the Router. You still need your modem. Open the web browser (for traditional dial-up service. Wireless-G Broadband Router with SpeedBooster 21 The DSL telephone line does not fit into your ...
...OK. The computer cannot connect wirelessly to modify the settings on . WEB: If your network devices, including the modem, Router, and computers. Follow these instructions until your Internet Service Provider (ISP), so you have enabled wireless security, then make sure the same security method and key are similar ... to Internet Explorer but are used by both the computer and the Router. You still need your modem. Open the web browser (for traditional dial-up service. Wireless-G Broadband Router with SpeedBooster 21 The DSL telephone line does not fit into your ...