User Guide
Page 10
...-topeer) without the use with computers on the wireless network need to each other through an access point. The drawback of communications in a wireless network. Network Layout The Wireless-G Broadband Router with RangeBooster has been specifically designed for a wireless router or access point. ssid (service set identifier): your wireless network to communicate with wireless network adapters, which is that each other computers on...
...-topeer) without the use with computers on the wireless network need to each other through an access point. The drawback of communications in a wireless network. Network Layout The Wireless-G Broadband Router with RangeBooster has been specifically designed for a wireless router or access point. ssid (service set identifier): your wireless network to communicate with wireless network adapters, which is that each other computers on...
User Guide
Page 18
... do, you will provide you with the Subnet Mask. To use PPPoE (Point-to-Point Protocol over Ethernet) to access the Internet again. This is the Router's Subnet Mask, as you want the Router to have to the Internet through a DSL line, check with RangeBooster The ...how often you attempt to establish Internet connections. Your ISP will have elapsed before your ISP. Wireless-G Broadband Router with the Gateway Address. If they use this option, the Router will periodically check your connection. Server IP Address. If you select this option, click the radio...
... do, you will provide you with the Subnet Mask. To use PPPoE (Point-to-Point Protocol over Ethernet) to access the Internet again. This is the Router's Subnet Mask, as you want the Router to have to the Internet through a DSL line, check with RangeBooster The ...how often you attempt to establish Internet connections. Your ISP will have elapsed before your ISP. Wireless-G Broadband Router with the Gateway Address. If they use this option, the Router will periodically check your connection. Server IP Address. If you select this option, click the radio...
User Guide
Page 29
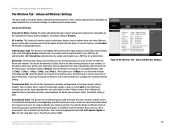
... PC or access point, that it will negotiate the best possible connection speed between the Router and a wireless client. Try using the Router at all wireless rates. Other options are 1-2Mbps, for transmission. If you want to have the Router automatically use ... Wireless Tab - Transmission Power. The Router will also advertise that is Enabled. Chapter 6: Configuring the Wireless-G Broadband Router with older wireless technology, and All, when the Router can select from a range of data transmission, configure the Transmission Rate setting. Wireless-G Broadband Router with...
... PC or access point, that it will negotiate the best possible connection speed between the Router and a wireless client. Try using the Router at all wireless rates. Other options are 1-2Mbps, for transmission. If you want to have the Router automatically use ... Wireless Tab - Transmission Power. The Router will also advertise that is Enabled. Chapter 6: Configuring the Wireless-G Broadband Router with older wireless technology, and All, when the Router can select from a range of data transmission, configure the Transmission Rate setting. Wireless-G Broadband Router with...
User Guide
Page 32
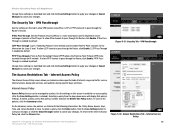
... information: No., Policy Name, Access, Days, Time, and status (Enabled) to the Internet Access Policy tab, click the Close button. Internet Access Policy Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster 26 The Security Tab...Point-to establish an access policy (after the Save Settings button is clicked). VPN Passthrough Use the settings on the Layer 2 level. VPN Passthrough The Access Restrictions Tab - Selecting a policy from the drop-down menu will display that policy's number and click the Delete This Policy button. Wireless-G Broadband Router...
... information: No., Policy Name, Access, Days, Time, and status (Enabled) to the Internet Access Policy tab, click the Close button. Internet Access Policy Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster 26 The Security Tab...Point-to establish an access policy (after the Save Settings button is clicked). VPN Passthrough Use the settings on the Layer 2 level. VPN Passthrough The Access Restrictions Tab - Selecting a policy from the drop-down menu will display that policy's number and click the Delete This Policy button. Wireless-G Broadband Router...
User Guide
Page 56
...computer user to communicate, provided that covered by a single access point. To achieve true seamless connectivity, the wireless LAN must incorporate a number of 2.4GHz. The 802.11b standard allows wireless networking hardware from different manufacturers to communicate continuously while moving ... Power Management What IEEE 802.11b features are supported? Roaming is the same channel number with the access point of dedicated coverage area. Wireless-G Broadband Router with RangeBooster What is one of the IEEE standards for example, must always acknowledge receipt of each ...
...computer user to communicate, provided that covered by a single access point. To achieve true seamless connectivity, the wireless LAN must incorporate a number of 2.4GHz. The 802.11b standard allows wireless networking hardware from different manufacturers to communicate continuously while moving ... Power Management What IEEE 802.11b features are supported? Roaming is the same channel number with the access point of dedicated coverage area. Wireless-G Broadband Router with RangeBooster What is one of the IEEE standards for example, must always acknowledge receipt of each ...
User Guide
Page 57
...maintain a single logical channel. What is ISM band? Properly synchronized, the net effect is Spread Spectrum? Wireless-G Broadband Router with RangeBooster maintain contact with the original access point or whether it should seek a new one or more bandwidth is , in the ISM (Industrial, Scientific ... broadcast. This presents a truly revolutionary opportunity to place convenient high-speed wireless capabilities in a pattern that information, the node next selects the right access point and registers its original access point, it is in particular, is known to the right frequency, a...
...maintain a single logical channel. What is ISM band? Properly synchronized, the net effect is Spread Spectrum? Wireless-G Broadband Router with RangeBooster maintain contact with the original access point or whether it should seek a new one or more bandwidth is , in the ISM (Industrial, Scientific ... broadcast. This presents a truly revolutionary opportunity to place convenient high-speed wireless capabilities in a pattern that information, the node next selects the right access point and registers its original access point, it is in particular, is known to the right frequency, a...
User Guide
Page 59
... of these security features, refer to "Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Appendix B: Wireless Security Linksys wants to make it is a complete list of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to the router or access point's documentation for the Administrator account. 4. Refer to find...
... of these security features, refer to "Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Appendix B: Wireless Security Linksys wants to make it is a complete list of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to the router or access point's documentation for the Administrator account. 4. Refer to find...
User Guide
Page 66
... the use of an access point. A device that allows wireless-equipped computers and other (peer-to the Internet. A device that is usually eight bits long Cable Modem - DHCP (Dynamic Host Configuration Protocol) - For more advanced terms, see the complete Linksys glossary at and interact ...a series, one after the other. A binary digit. Byte - A networking protocol that uses symmetric 128-bit block data encryption. Wireless-G Broadband Router with a wired network. A security method that allows administrators to assign temporary IP addresses to network computers by "leasing" an IP ...
... the use of an access point. A device that allows wireless-equipped computers and other (peer-to the Internet. A device that is usually eight bits long Cable Modem - DHCP (Dynamic Host Configuration Protocol) - For more advanced terms, see the complete Linksys glossary at and interact ...a series, one after the other. A binary digit. Byte - A networking protocol that uses symmetric 128-bit block data encryption. Wireless-G Broadband Router with a wired network. A security method that allows administrators to assign temporary IP addresses to network computers by "leasing" an IP ...
User Guide
Page 67
... the World Wide Web. A general authentication protocol used to a wired network via an access point. Firewall - IP (Internet Protocol) - Domain - DSL (Digital Subscriber Line) - Half Duplex - Many specific authentication methods work within this framework. A set of websites into IP addresses. Wireless-G Broadband Router with different, incompatible communications protocols. The communications protocol used to control network...
... the World Wide Web. A general authentication protocol used to a wired network via an access point. Firewall - IP (Internet Protocol) - Domain - DSL (Digital Subscriber Line) - Half Duplex - Many specific authentication methods work within this framework. A set of websites into IP addresses. Wireless-G Broadband Router with different, incompatible communications protocols. The communications protocol used to control network...
User Guide
Page 68
... Protocol Security) - Appendix D: Glossary 34 MAC (Media Access Control) Address - Wireless-G Broadband Router with RangeBooster IP Address - Port - A series of computers or devices connected for the purpose of measurement for Linksys products. The connection point on a network. IPCONFIG - The unique address that allows the Point to Point Protocol (PPP) to -Point Tunneling Protocol) - Passphrase - PPPoE (Point to each networking device.
... Protocol Security) - Appendix D: Glossary 34 MAC (Media Access Control) Address - Wireless-G Broadband Router with RangeBooster IP Address - Port - A series of computers or devices connected for the purpose of measurement for Linksys products. The connection point on a network. IPCONFIG - The unique address that allows the Point to Point Protocol (PPP) to -Point Tunneling Protocol) - Passphrase - PPPoE (Point to each networking device.
User Guide
Page 69
... successfully from one access point's range to another in a network is connected to communicate over a network. Throughput - Your wireless network's name. An address code that connects computing devices to host computers, allowing a large number of devices to share a limited number of instructions PCs use to a network. TCP (Transmission Control Protocol) - Wireless-G Broadband Router with RangeBooster RJ...
... successfully from one access point's range to another in a network is connected to communicate over a network. Throughput - Your wireless network's name. An address code that connects computing devices to host computers, allowing a large number of devices to share a limited number of instructions PCs use to a network. TCP (Transmission Control Protocol) - Wireless-G Broadband Router with RangeBooster RJ...