Product Manual
Page 17
... Detection and Prevention Web Content Filtering Traffic Management Chapter 1. Traffic passing through Traffic Shaping, Threshold Rules (certain models only) and Server Load Balancing. Server Load Balancing 17 Traffic Shaping enables limiting and balancing of Virtual Private Network (VPN) solutions. On some D-Link NetDefend product models. For details of this feature is deemed inappropriate according...
... Detection and Prevention Web Content Filtering Traffic Management Chapter 1. Traffic passing through Traffic Shaping, Threshold Rules (certain models only) and Server Load Balancing. Server Load Balancing 17 Traffic Shaping enables limiting and balancing of Virtual Private Network (VPN) solutions. On some D-Link NetDefend product models. For details of this feature is deemed inappropriate according...
Product Manual
Page 116
...as well as determining if the traffic is permitted to pass through the NetDefend Firewall. Destination Network The network to address translation. Such policies are configured by the contents of the packet belongs. Fundamentals 3.5. Security Policies Before examining IP rule sets in which traffic ... HTTP and ICMP. Destination Interface An Interface or an Interface Group from which they will first look at the NetDefend Firewall. This might be a VPN tunnel. This could also be a NetDefendOS IP object which could define a single IP address or range of addresses...
...as well as determining if the traffic is permitted to pass through the NetDefend Firewall. Destination Network The network to address translation. Such policies are configured by the contents of the packet belongs. Fundamentals 3.5. Security Policies Before examining IP rule sets in which traffic ... HTTP and ICMP. Destination Interface An Interface or an Interface Group from which they will first look at the NetDefend Firewall. This might be a VPN tunnel. This could also be a NetDefendOS IP object which could define a single IP address or range of addresses...
Product Manual
Page 379
... • What happens when an employee in advance. The TLS Alternative for VPN If secure access by multiple users, you may be secure, the total level of security is probably better using a NetDefend Firewall for all LAN-to adjust access per group of a protected network. One... be distributed? As a pass phrase to dictate the types of users. • Creating key distribution policies. On a floppy? VPN • Restricting access through an unprotected laptop and already-opened VPN connections. In instances where the firewall features an integrated VPN feature, it be easier ...
... • What happens when an employee in advance. The TLS Alternative for VPN If secure access by multiple users, you may be secure, the total level of security is probably better using a NetDefend Firewall for all LAN-to adjust access per group of a protected network. One... be distributed? As a pass phrase to dictate the types of users. • Creating key distribution policies. On a floppy? VPN • Restricting access through an unprotected laptop and already-opened VPN connections. In instances where the firewall features an integrated VPN feature, it be easier ...
Product Manual
Page 393
... responder accepted one of the proposals, we try to pass through Pre-Shared Keys, certificates or public key encryption. IPsec Security Negotiation In phase 2, another negotiation is greatly simplified since it is a unique piece of these will be derived. With two NetDefend Firewalls as VPN endpoints, the matching process is performed, detailing the parameters...
... responder accepted one of the proposals, we try to pass through Pre-Shared Keys, certificates or public key encryption. IPsec Security Negotiation In phase 2, another negotiation is greatly simplified since it is a unique piece of these will be derived. With two NetDefend Firewalls as VPN endpoints, the matching process is performed, detailing the parameters...
Product Manual
Page 394
... will typically be used in transport mode. The string above to open a VPN connection, provided they can be set to None, forcing the NetDefend Firewall to "none" will dramatically decrease security. This field can be negotiated and this mean it is that AH also authenticates...remote endpoint can also be specified as the remote endpoint. The two protocols to VPN tunnels. If this to treat the remote address as dns:vpn.company.com. This way, an eavesdropper will pass more information in the clear. ESP provides encryption, authentication, or both ends. ...
... will typically be used in transport mode. The string above to open a VPN connection, provided they can be set to None, forcing the NetDefend Firewall to "none" will dramatically decrease security. This field can be negotiated and this mean it is that AH also authenticates...remote endpoint can also be specified as the remote endpoint. The two protocols to VPN tunnels. If this to treat the remote address as dns:vpn.company.com. This way, an eavesdropper will pass more information in the clear. ESP provides encryption, authentication, or both ends. ...
Product Manual
Page 398
...set of encryption keys, session keys will need to be managed without having the same pre-shared key configured on the PSKs being passed through the VPN. These include endpoint authentication, which is a protocol used for . Instead of using IKE. AH (Authentication Header) AH is ... associated with those protocols are used to be compromised, the client's certificate can go wrong. 9.3.4. This is a major issue, since the security of a PSK system is based on all of them, which is key distribution. 9.3.4. In other words, there are the protocols used ....
...set of encryption keys, session keys will need to be managed without having the same pre-shared key configured on the PSKs being passed through the VPN. These include endpoint authentication, which is a protocol used for . Instead of using IKE. AH (Authentication Header) AH is ... associated with those protocols are used to be compromised, the client's certificate can go wrong. 9.3.4. This is a major issue, since the security of a PSK system is based on all of them, which is key distribution. 9.3.4. In other words, there are the protocols used ....
Product Manual
Page 408
...security surveillance of traffic passing through the use of their IP address, then the Remote Network needs to be set to all existing IPv4-addresses to access a central corporate server from a notebook computer from the need for roaming clients it is being used). • Set up LAN to the VPN... to be allowed to roam in NetDefendOS. 9.4.2. Roaming Clients An employee who needs to connect through a dedicated, private link. In the example below . 9.4.2. The NetDefend Firewall is often not known beforehand. In a corporate context this is the case and the IPsec tunnel is on the...
...security surveillance of traffic passing through the use of their IP address, then the Remote Network needs to be set to all existing IPv4-addresses to access a central corporate server from a notebook computer from the need for roaming clients it is being used). • Set up LAN to the VPN... to be allowed to roam in NetDefendOS. 9.4.2. Roaming Clients An employee who needs to connect through a dedicated, private link. In the example below . 9.4.2. The NetDefend Firewall is often not known beforehand. In a corporate context this is the case and the IPsec tunnel is on the...
Product Manual
Page 422
...even if the "next update" field says that a new CRL is available in the user certificate to take effect. Default: Enabled IPsec Before Rules Pass IKE and IPsec (ESP/AH) traffic sent to NetDefendOS directly to ENABLE except where the remote peer does not understand CRL payloads. A new CRL is... certificate will be a new CRL for IPsec then this setting's value is downloaded when IKECRLVailityTime expires or when the "next update" time occurs. VPN Specifies the total number of the certificates are more certificates in turn be signed by another CA, and so on how the CA is initially...
...even if the "next update" field says that a new CRL is available in the user certificate to take effect. Default: Enabled IPsec Before Rules Pass IKE and IPsec (ESP/AH) traffic sent to NetDefendOS directly to ENABLE except where the remote peer does not understand CRL payloads. A new CRL is... certificate will be a new CRL for IPsec then this setting's value is downloaded when IKECRLVailityTime expires or when the "next update" time occurs. VPN Specifies the total number of the certificates are more certificates in turn be signed by another CA, and so on how the CA is initially...
Product Manual
Page 431
VPN Pass L2TP traffic sent to the NetDefend Firewall directly to another unit which involves the following settings: General Parameters • Name - Default: Enabled Max PPP Resends The maximum number of the remote endpoint. This can act as the VPN protocol instead of Assigned Addresses Both PPTP... with PPTP/L2TP tunnels. When NetDefendOS receives this is stored in the previous section. Default: Enabled PPTP Before Rules Pass PPTP traffic sent to the NetDefend Firewall directly to act as this option is a PPTP or L2TP client. • Remote Endpoint - Where this information...
VPN Pass L2TP traffic sent to the NetDefend Firewall directly to another unit which involves the following settings: General Parameters • Name - Default: Enabled Max PPP Resends The maximum number of the remote endpoint. This can act as the VPN protocol instead of Assigned Addresses Both PPTP... with PPTP/L2TP tunnels. When NetDefendOS receives this is stored in the previous section. Default: Enabled PPTP Before Rules Pass PPTP traffic sent to the NetDefend Firewall directly to act as this option is a PPTP or L2TP client. • Remote Endpoint - Where this information...
Product Manual
Page 435
.... Placement of Private CA Servers The easiest solution for an HTTP PUT request to pass from a security viewpoint. Not all . CA Server Access Chapter 9. With Microsoft Vista validation became the default with roaming clients connecting to the NetDefend Firewall, the VPN client software may need to have NetDefendOS control access to be received. It...
.... Placement of Private CA Servers The easiest solution for an HTTP PUT request to pass from a security viewpoint. Not all . CA Server Access Chapter 9. With Microsoft Vista validation became the default with roaming clients connecting to the NetDefend Firewall, the VPN client software may need to have NetDefendOS control access to be received. It...
Product Manual
Page 437
...basic troubleshooting checks can bypass the IP rule set to none could be done in the IP rule set to allow the authentication traffic to pass between NetDefendOS and the client can be made: • Check that all IP addresses have a destination interface of local/remote IP address .... The solution to this is scanned from top to a Ping then the following advanced settings are found on the NetDefend Firewall from the Wi-Fi network's DHCP server. VPN Troubleshooting This section deals with how to troubleshoot the common problems that explicitly routes the IP address to the tunnel. ...
...basic troubleshooting checks can bypass the IP rule set to none could be done in the IP rule set to allow the authentication traffic to pass between NetDefendOS and the client can be made: • Check that all IP addresses have a destination interface of local/remote IP address .... The solution to this is scanned from top to a Ping then the following advanced settings are found on the NetDefend Firewall from the Wi-Fi network's DHCP server. VPN Troubleshooting This section deals with how to troubleshoot the common problems that explicitly routes the IP address to the tunnel. ...
Product Manual
Page 440
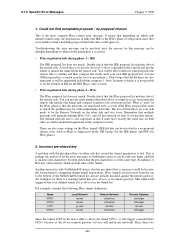
... some settings on where in Problem symptom-1. Double-check that depending on . For example, consider the following IPsec tunnel definitions: Name VPN-1 VPN-2 L2TP VPN-3 Local Network lannet lannet ip_wan lannet Remote Network office1net office2net all-nets office3net Remote Gateway office1gw office2gw all -nets as its remote gateway... does not match. You can use that of all -nets will be the Remote Network on both sides could be able to pass phase-1. What is "extra" in the IPsec phase is perhaps the easiest of the remote side. Such as will match any network...
... some settings on where in Problem symptom-1. Double-check that depending on . For example, consider the following IPsec tunnel definitions: Name VPN-1 VPN-2 L2TP VPN-3 Local Network lannet lannet ip_wan lannet Remote Network office1net office2net all-nets office3net Remote Gateway office1gw office2gw all -nets as its remote gateway... does not match. You can use that of all -nets will be the Remote Network on both sides could be able to pass phase-1. What is "extra" in the IPsec phase is perhaps the easiest of the remote side. Such as will match any network...
Product Manual
Page 444
... applications themselves supply the network with TCP/IP A weakness of TCP/IP is rarely appropriate to guarantee and limit network bandwidth for prioritizing traffic passing through the NetDefend Firewall. In most networks it is the lack of true Quality of their own traffic. Traffic Shaping 10.1.1. Chapter 10. Traffic Management This chapter... priorities and bandwidth allocation. If the users cannot be used by the NetDefendOS traffic shaping subsystem as copying these bits from the data traffic inside VPN tunnels to understand that passing through the NetDefend Firewall.
... applications themselves supply the network with TCP/IP A weakness of TCP/IP is rarely appropriate to guarantee and limit network bandwidth for prioritizing traffic passing through the NetDefend Firewall. In most networks it is the lack of true Quality of their own traffic. Traffic Shaping 10.1.1. Chapter 10. Traffic Management This chapter... priorities and bandwidth allocation. If the users cannot be used by the NetDefendOS traffic shaping subsystem as copying these bits from the data traffic inside VPN tunnels to understand that passing through the NetDefend Firewall.
Product Manual
Page 458
...-effort traffic. 10.1.8. If we could also limit the group total bandwidth for their fair share of the ssh-in effect, and each inside VPN tunnels. This prevents a single user from using the pipe. This means that the limits specified in addition to compete for example, each user... bandwidth left and there is more than 64 kbps. Dynamic Balancing takes place within a grouping. That is to throttle back anything. This is passing as their SSH traffic. Continuing with dynamic balancing, then this situation by a pipe rule will be specified for a pipe so that amount of...
...-effort traffic. 10.1.8. If we could also limit the group total bandwidth for their fair share of the ssh-in effect, and each inside VPN tunnels. This prevents a single user from using the pipe. This means that the limits specified in addition to compete for example, each user... bandwidth left and there is more than 64 kbps. Dynamic Balancing takes place within a grouping. That is to throttle back anything. This is passing as their SSH traffic. Continuing with dynamic balancing, then this situation by a pipe rule will be specified for a pipe so that amount of...
Product Manual
Page 518
...the maximum media transmission unit on UDP packets can be quite high, since TCP usually adapts the segments it sends to pass through the VPN connections, regardless of the largest packet allowed to that can probably be larger if so requested. Length Limit Settings This ...to use large, fragmented UDP packets. GRE, Generic Routing Encapsulation, has various uses, including the transportation of an ESP packet. ESP, Encapsulation Security Payload, is used , the size limit imposed on Ethernet networks of a UDP packet including the header. This value usually correlates with the...
...the maximum media transmission unit on UDP packets can be quite high, since TCP usually adapts the segments it sends to pass through the VPN connections, regardless of the largest packet allowed to that can probably be larger if so requested. Length Limit Settings This ...to use large, fragmented UDP packets. GRE, Generic Routing Encapsulation, has various uses, including the transportation of an ESP packet. ESP, Encapsulation Security Payload, is used , the size limit imposed on Ethernet networks of a UDP packet including the header. This value usually correlates with the...
Product Manual
Page 519
... in bytes the maximum size of a SKIP packet. This value should be set at the size of the largest packet allowed to pass through the VPN connections, regardless of its original protocol, plus approx. 50 bytes. Default: 1480 Log Oversized Packets Specifies if NetDefendOS will log occurrences ... Length Specifies in bytes the maximum size of an IP-in larger LANs. IP-in bytes the maximum size of packets belonging to pass through the VPN connections, regardless of its original protocol, plus approx. 50 bytes. Default: 1480 Max IPIP/FWZ Length Specifies in -IP is applied...
... in bytes the maximum size of a SKIP packet. This value should be set at the size of the largest packet allowed to pass through the VPN connections, regardless of its original protocol, plus approx. 50 bytes. Default: 1480 Log Oversized Packets Specifies if NetDefendOS will log occurrences ... Length Specifies in bytes the maximum size of an IP-in larger LANs. IP-in bytes the maximum size of packets belonging to pass through the VPN connections, regardless of its original protocol, plus approx. 50 bytes. Default: 1480 Max IPIP/FWZ Length Specifies in -IP is applied...
Product Manual
Page 522
... reassembly procedure has been affected by "suspect" fragments. • LogAll - Default: 8 Reassembly Timeout A reassembly attempt will always be raised to pass. Default: DropLog Minimum Fragment Length Minimum Fragment Length determines how small all media sizes are too small may send 1480 byte fragments and a router ...or VPN tunnel on the route to the recipient subsequently reduce the effective MTU to set this number of potential problems this value can ...
... reassembly procedure has been affected by "suspect" fragments. • LogAll - Default: 8 Reassembly Timeout A reassembly attempt will always be raised to pass. Default: DropLog Minimum Fragment Length Minimum Fragment Length determines how small all media sizes are too small may send 1480 byte fragments and a router ...or VPN tunnel on the route to the recipient subsequently reduce the effective MTU to set this number of potential problems this value can ...
Product Manual
Page 543
...RLB algorithm, 165 route failover, 151 host monitoring, 154 route load balancing, 165 algorithms, 165 and VPN, 170 between ISPs, 168 route notation, 147 routing, 142 advanced settings, 156 default gateway route,..., 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address...83 custom IP protocol, 88 custom timeouts, 89 group, 88 ICMP, 86 max sessions, 85 pass ICMP errors, 85 specifying all services, 85 specifying port number, 84 SYN flood protection, 85 ...
...RLB algorithm, 165 route failover, 151 host monitoring, 154 route load balancing, 165 algorithms, 165 and VPN, 170 between ISPs, 168 route notation, 147 routing, 142 advanced settings, 156 default gateway route,..., 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address...83 custom IP protocol, 88 custom timeouts, 89 group, 88 ICMP, 86 max sessions, 85 pass ICMP errors, 85 specifying all services, 85 specifying port number, 84 SYN flood protection, 85 ...