User Guide
Page 3
... 6 The Side Panel 6 The Power Plate 7 Chapter 4: Connecting the Wireless-G Range Expander 8 Chapter 5: Setting Up the Wireless-G Range Expander 9 Chapter 6: Configuring the Wireless-G Range Expander 14 Overview 14 The Setup Tab 15 Appendix A: Troubleshooting 19 Common Problems and Solutions 19 Frequently Asked Questions 19 Appendix B: Wireless Security 23 Security Precautions 23 Security Threats Facing Wireless Networks 23 Appendix C: Upgrading Firmware 26 Appendix D: Windows Help 27 Appendix E: Glossary 28 Appendix F: Specifications 31 Appendix G: Warranty...
... 6 The Side Panel 6 The Power Plate 7 Chapter 4: Connecting the Wireless-G Range Expander 8 Chapter 5: Setting Up the Wireless-G Range Expander 9 Chapter 6: Configuring the Wireless-G Range Expander 14 Overview 14 The Setup Tab 15 Appendix A: Troubleshooting 19 Common Problems and Solutions 19 Frequently Asked Questions 19 Appendix B: Wireless Security 23 Security Precautions 23 Security Threats Facing Wireless Networks 23 Appendix C: Upgrading Firmware 26 Appendix D: Windows Help 27 Appendix E: Glossary 28 Appendix F: Specifications 31 Appendix G: Warranty...
User Guide
Page 4
Help 18 Figure 6-7: Firmware Upgrade 18 Figure C-1: Upgrade Firmware 26 Password 17 Figure 6-5: File Download 17 Figure 6-6: Setup Tab - Wireless-G Range Expander List of Figures Figure 3-1: The Front Panel 6 Figure 3-2: The Power Plate 7 Figure 5-1: The Setup Wizard's Welcome screen 9 Figure 5-2: Connecting to an access point 10 Figure 5-3: Confirm Wireless Settings 10 Figure 5-4: Cannot find Wireless Network 10 Figure 5-5: Choose an access point 10 Figure 5-6: The Security Settings screen 11 Figure 5-7: Choose the Range Expander 11 Figure 5-8: The Password ...
Help 18 Figure 6-7: Firmware Upgrade 18 Figure C-1: Upgrade Firmware 26 Password 17 Figure 6-5: File Download 17 Figure 6-6: Setup Tab - Wireless-G Range Expander List of Figures Figure 3-1: The Front Panel 6 Figure 3-2: The Power Plate 7 Figure 5-1: The Setup Wizard's Welcome screen 9 Figure 5-2: Connecting to an access point 10 Figure 5-3: Confirm Wireless Settings 10 Figure 5-4: Cannot find Wireless Network 10 Figure 5-5: Choose an access point 10 Figure 5-6: The Security Settings screen 11 Figure 5-7: Choose the Range Expander 11 Figure 5-8: The Password ...
User Guide
Page 5
... compatibility with wireless cards and adapters can then take that adds network functionality to all you need to expand your network beyond the range of your access point or wireless router's signal, it beyond its range. Once on another computer's hard drive. network - PCs equipped with 802.11b devices. Also used for playing multiplayer video games. You can also be all devices within their transmission radius, they can access one printer from...
... compatibility with wireless cards and adapters can then take that adds network functionality to all you need to expand your network beyond the range of your access point or wireless router's signal, it beyond its range. Once on another computer's hard drive. network - PCs equipped with 802.11b devices. Also used for playing multiplayer video games. You can also be all devices within their transmission radius, they can access one printer from...
User Guide
Page 6
... configure the Range Expander with the Web Utility. • Appendix A: Troubleshooting This appendix describes some potential problems and solutions, as well as frequently asked questions, regarding installation and use of the Adapter. • Appendix B: Wireless Security This appendix discusses security issues regarding wireless networking and measures you can take to help protect your wireless network. • Appendix C: Windows Help This appendix describes how you can use Windows Help for instructions about networking, such as installing...
... configure the Range Expander with the Web Utility. • Appendix A: Troubleshooting This appendix describes some potential problems and solutions, as well as frequently asked questions, regarding installation and use of the Adapter. • Appendix B: Wireless Security This appendix discusses security issues regarding wireless networking and measures you can take to help protect your wireless network. • Appendix C: Windows Help This appendix describes how you can use Windows Help for instructions about networking, such as installing...
User Guide
Page 10
... your settings (WEP Encryption and Wireless settings, etc.) and replace them with which to connect, this feature to function. Important: Resetting the Range Expander will erase all of encrypting network data transmitted on the front panel. LINK ACTIVITY Blue/Red. When there is no access point or wireless router with the factory defaults. The ACTIVITY LED lights whenever there is a successful wireless connection and will find the Reset and Auto configuration buttons. Simply connect the power and press the Auto configuration button...
... your settings (WEP Encryption and Wireless settings, etc.) and replace them with which to connect, this feature to function. Important: Resetting the Range Expander will erase all of encrypting network data transmitted on the front panel. LINK ACTIVITY Blue/Red. When there is no access point or wireless router with the factory defaults. The ACTIVITY LED lights whenever there is a successful wireless connection and will find the Reset and Auto configuration buttons. Simply connect the power and press the Auto configuration button...
User Guide
Page 12
... use to communicate over the network with the Setup Wizard included, you have disabled WEP security on how to set of your network, through cables, etc., connection is complete, proceed to Chapter 5: Setting Up the Wireless-G Range Expander, for the Range Expander. Try to place it to a power outlet. Now that will then automatically detect your wireless network. Then, press the Auto configuration button. NOTE: The Auto configuration button can once again enable WEP security. Wireless-G Range Expander Chapter 4: Connecting...
... use to communicate over the network with the Setup Wizard included, you have disabled WEP security on how to set of your network, through cables, etc., connection is complete, proceed to Chapter 5: Setting Up the Wireless-G Range Expander, for the Range Expander. Try to place it to a power outlet. Now that will then automatically detect your wireless network. Then, press the Auto configuration button. NOTE: The Auto configuration button can once again enable WEP security. Wireless-G Range Expander Chapter 4: Connecting...
User Guide
Page 13
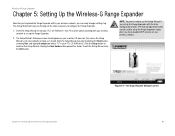
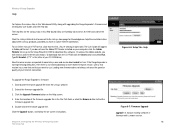
... wireless network to set up . To exit this Setup Wizard. NOTE: You won't need to use the Setup Wizard, if you are ready to begin setting it up the Range Expander. 2. The Auto configuration button can be communicating with the Auto configuration button. Chapter 5: Setting Up the Wireless-G Range Expander Figure 5-1: The Setup Wizard's Welcome screen 9 Click the Setup button to configure the Range Expander. 1. This Setup Wizard will take you have disabled WEP security on your PC's CD-ROM drive). Start...
... wireless network to set up . To exit this Setup Wizard. NOTE: You won't need to use the Setup Wizard, if you are ready to begin setting it up the Range Expander. 2. The Auto configuration button can be communicating with the Auto configuration button. Chapter 5: Setting Up the Wireless-G Range Expander Figure 5-1: The Setup Wizard's Welcome screen 9 Click the Setup button to configure the Range Expander. 1. This Setup Wizard will take you have disabled WEP security on your PC's CD-ROM drive). Start...
User Guide
Page 18
ip address: the address used the Auto configuration button, the default IP address is 192.168.1.240.) Press the Enter key and the Password Screen will appear. Wireless-G Range Expander Chapter 6: Configuring the Wireless-G Range Expander Overview The Range Expander has been designed to be configured through your web browser with the Web-Based Utility. The first time you used to identify a computer or device on TCP/IP. Refer to perform more information on a network. This...
ip address: the address used the Auto configuration button, the default IP address is 192.168.1.240.) Press the Enter key and the Password Screen will appear. Wireless-G Range Expander Chapter 6: Configuring the Wireless-G Range Expander Overview The Range Expander has been designed to be configured through your web browser with the Web-Based Utility. The first time you used to identify a computer or device on TCP/IP. Refer to perform more information on a network. This...
User Guide
Page 19
... network. The SSID must be upgraded from the default name, linksys, to the Range Expander. Basic Setup firmware: the programming code that runs a networking device subnet mask: an address code that appears displays the Basic Setup screen. Select G-Only for all points in the wireless network. For added security, you disable it . If your network does not have assigned a static IP address to your network. Unique, memorable names are helpful, especially if you are employing multiple Range...
... network. The SSID must be upgraded from the default name, linksys, to the Range Expander. Basic Setup firmware: the programming code that runs a networking device subnet mask: an address code that appears displays the Basic Setup screen. Select G-Only for all points in the wireless network. For added security, you disable it . If your network does not have assigned a static IP address to your network. Unique, memorable names are helpful, especially if you are employing multiple Range...
User Guide
Page 20
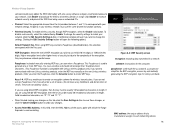
... your changes. • Access Point MAC Address. To enable wireless security, through WEP encryption, select the Enable radio button. Clicking the Edit Security Settings button will ask if you are using a Passphrase, then manually enter a set of values. (Do not leave a key field blank, and do not enter all wireless devices in length. Figure 6-3: WEP Security screen encryption: encoding data transmitted in length. In this field, enter the MAC Address of WEP encryption you wish to use the same channel to function correctly. • Wireless Security. MAC address...
... your changes. • Access Point MAC Address. To enable wireless security, through WEP encryption, select the Enable radio button. Clicking the Edit Security Settings button will ask if you are using a Passphrase, then manually enter a set of values. (Do not leave a key field blank, and do not enter all wireless devices in length. Figure 6-3: WEP Security screen encryption: encoding data transmitted in length. In this field, enter the MAC Address of WEP encryption you wish to use the same channel to function correctly. • Wireless Security. MAC address...
User Guide
Page 22
Click the Linksys Website link to connect to use. New firmware versions are listed by tab name on your computer, click the Adobe Website link or go to the Setup Wizard CD-ROM to download this software. (To access the Adobe website, you will need to download a more recent firmware version, unless that version has a new feature that text link. (You're viewing it right now!) The User Guide will appear in this Web-based Utility, along with...
Click the Linksys Website link to connect to use. New firmware versions are listed by tab name on your computer, click the Adobe Website link or go to the Setup Wizard CD-ROM to download this software. (To access the Adobe website, you will need to download a more recent firmware version, unless that version has a new feature that text link. (You're viewing it right now!) The User Guide will appear in this Web-based Utility, along with...
User Guide
Page 23
... game's user guide for five seconds. Then, connect the power again. • Press the Auto configuration button on whether or not the application is within range of an access point or wireless router that may occur during the installation and operation of the wireless network? Frequently Asked Questions Can I play multiplayer games with it should reset the Range Expander's settings back to my Wireless-G network. Refer to problems that has disabled WEP, it...
... game's user guide for five seconds. Then, connect the power again. • Press the Auto configuration button on whether or not the application is within range of an access point or wireless router that may occur during the installation and operation of the wireless network? Frequently Asked Questions Can I play multiplayer games with it should reset the Range Expander's settings back to my Wireless-G network. Refer to problems that has disabled WEP, it...
User Guide
Page 25
... network. On the hardware side, as described in effect, louder and thus easier to support printer or file sharing. This bit pattern is Spread Spectrum? Linksys Wireless products can be short-duration impulse noise. Unlike IP addresses, which can set it a valuable identifier for reliability, integrity, and security. On the software side, the wireless series offers the encryption function (WEP) to be recovered. Wireless-G Range...
... network. On the hardware side, as described in effect, louder and thus easier to support printer or file sharing. This bit pattern is Spread Spectrum? Linksys Wireless products can be short-duration impulse noise. Unlike IP addresses, which can set it a valuable identifier for reliability, integrity, and security. On the software side, the wireless series offers the encryption function (WEP) to be recovered. Wireless-G Range...
User Guide
Page 26
.... Leaded glass, metal, concrete floors, water and walls will create signal loss. How do I resolve issues with your access point and your wireless network without testing. Also, due to its default settings. Start with signal loss? When employing multiple access points, be transmitted, using different channels, as this may be sure to determine the maximum range in the Transmission Rate field. Wireless-G Range Expander How do I reset the Range Expander?
.... Leaded glass, metal, concrete floors, water and walls will create signal loss. How do I resolve issues with your access point and your wireless network without testing. Also, due to its default settings. Start with signal loss? When employing multiple access points, be transmitted, using different channels, as this may be sure to determine the maximum range in the Transmission Rate field. Wireless-G Range Expander How do I reset the Range Expander?
User Guide
Page 27
...as the network's SSID (Service Set Identifier). Change the default SSID. 2. Enable MAC Address Filtering. 5. These messages can change those settings. To ensure network security, steps one through the network router or access point. Disable SSID Broadcast. 3. Here are easy to take : Change the administrator's password regularly. Security Threats Facing Wireless Networks Wireless networks are the steps you as shown in mind whenever you use, keep the following is a complete list of security precautions to find. Change the WEP encryption keys periodically. Hackers...
...as the network's SSID (Service Set Identifier). Change the default SSID. 2. Enable MAC Address Filtering. 5. These messages can change those settings. To ensure network security, steps one through the network router or access point. Disable SSID Broadcast. 3. Here are easy to take : Change the administrator's password regularly. Security Threats Facing Wireless Networks Wireless networks are the steps you as shown in mind whenever you use, keep the following is a complete list of security precautions to find. Change the WEP encryption keys periodically. Hackers...
User Guide
Page 28
... 3. Disable Broadcast 2. MAC Addresses. This is the newest and best available standard in mind about the SSID: 1. Wireless-G Range Expander SSID. This includes hackers. WEP Encryption. Change your network with a random MAC Address. Two modes are several ways that WEP can only provide enough security to keep in Wi-Fi security. Wireless networking products come with certain MAC Addresses. Change your SSID regularly so that each device in . Enable MAC Address filtering. Use the highest level of two encryption methods: TKIP (Temporal Key...
... 3. Disable Broadcast 2. MAC Addresses. This is the newest and best available standard in mind about the SSID: 1. Wireless-G Range Expander SSID. This includes hackers. WEP Encryption. Change your network with a random MAC Address. Two modes are several ways that WEP can only provide enough security to keep in Wi-Fi security. Wireless networking products come with certain MAC Addresses. Change your SSID regularly so that each device in . Enable MAC Address filtering. Use the highest level of two encryption methods: TKIP (Temporal Key...
User Guide
Page 32
... Sense Multiple Access/Collision Avoidance) - Appendix E: Glossary 28 CTS (Clear To Send) - To receive a file transmitted over a network. A device that specifies a maximum data transfer rate of 11Mbps and an operating frequency of wireless devices communicating directly with all the information on the World Wide Web. A method that adds network functionality to secure data. A device that uses up to 256-bit key encryption to your PC. Wireless-G Range Expander...
... Sense Multiple Access/Collision Avoidance) - Appendix E: Glossary 28 CTS (Clear To Send) - To receive a file transmitted over a network. A device that specifies a maximum data transfer rate of 11Mbps and an operating frequency of wireless devices communicating directly with all the information on the World Wide Web. A method that adds network functionality to secure data. A device that uses up to 256-bit key encryption to your PC. Wireless-G Range Expander...
User Guide
Page 33
... between users. Network - A series of computers or devices connected for the purpose of the packet. Packet - A protocol that uses an authentication server to send data over a network medium that a manufacturer assigns to a wired network via an access point. MAC (Media Access Control) Address - Used much like a password, a passphrase simplifies the WEP encryption process by automatically generating the WEP encryption keys for plugging in transit. Port - Encryption - Firmware - Radio bandwidth utilized in a network. Node - Infrastructure - The address used for...
... between users. Network - A series of computers or devices connected for the purpose of the packet. Packet - A protocol that uses an authentication server to send data over a network medium that a manufacturer assigns to a wired network via an access point. MAC (Media Access Control) Address - Used much like a password, a passphrase simplifies the WEP encryption process by automatically generating the WEP encryption keys for plugging in transit. Port - Encryption - Firmware - Radio bandwidth utilized in a network. Node - Infrastructure - The address used for...
User Guide
Page 34
...Transmission Control Protocol/Internet Protocol) - a wireless encryption protocol that requires acknowledgement from one access point's range to communicate over a network. The physical layout of coordinating large packets through the RTS Threshold setting. To replace existing software or firmware with a RADIUS server. Router - A networking method of a network. Instructions for more reliable and secure data transmission. Static IP Address - A set of the network. A fixed address assigned to files, printing, communications, and other services. Topology - WPA (Wi...
...Transmission Control Protocol/Internet Protocol) - a wireless encryption protocol that requires acknowledgement from one access point's range to communicate over a network. The physical layout of coordinating large packets through the RTS Threshold setting. To replace existing software or firmware with a RADIUS server. Router - A networking method of a network. Instructions for more reliable and secure data transmission. Static IP Address - A set of the network. A fixed address assigned to files, printing, communications, and other services. Topology - WPA (Wi...
User Guide
Page 39
...use the accessories and cables supplied by the total RENs, contact the telephone company to determine the maximum REN for the calling area. If advance notice is not practical, the telephone company will be with this equipment should fail to be advised of those devices ring when your authorized support... Wireless-G Range Expander FCC PART 68 STATEMENT This equipment complies with Part 68 of RENs should not exceed 5. If the trouble persists, call the telephone company repair service bureau. Please note that the telephone company may be done by using another FCC approved device ...
...use the accessories and cables supplied by the total RENs, contact the telephone company to determine the maximum REN for the calling area. If advance notice is not practical, the telephone company will be with this equipment should fail to be advised of those devices ring when your authorized support... Wireless-G Range Expander FCC PART 68 STATEMENT This equipment complies with Part 68 of RENs should not exceed 5. If the trouble persists, call the telephone company repair service bureau. Please note that the telephone company may be done by using another FCC approved device ...