User Manual
Page 7
Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons. The ZyWALL icon is not an exact representation of your device. ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 50 User's Guide 7
Document Conventions Icons Used in Figures Figures in this User's Guide may use the following generic icons. The ZyWALL icon is not an exact representation of your device. ZyWALL Computer Notebook computer Server Firewall Telephone Switch Router ZyWALL USG 50 User's Guide 7
User Manual
Page 9
Contents Overview Contents Overview User's Guide ...29 Introducing the ZyWALL ...31 Features and Applications ...37 Web Configurator ...43 Installation Setup Wizard ...59 Quick Setup ...69 Configuration Basics ...87 Tutorials ...109 Technical ... Authentication Policy ...349 Firewall ...357 IPSec VPN ...375 SSL VPN ...411 SSL User Screens ...421 SSL User Application Screens 431 ZyWALL SecuExtender ...433 Application Patrol ...437 Anti-Virus ...463 IDP ...479 ADP ...513 Content Filtering ...533 Content Filter Reports ...557 Anti-Spam ...565 User/Group ...583 ZyWALL USG 50 User's Guide 9
Contents Overview Contents Overview User's Guide ...29 Introducing the ZyWALL ...31 Features and Applications ...37 Web Configurator ...43 Installation Setup Wizard ...59 Quick Setup ...69 Configuration Basics ...87 Tutorials ...109 Technical ... Authentication Policy ...349 Firewall ...357 IPSec VPN ...375 SSL VPN ...411 SSL User Screens ...421 SSL User Application Screens 431 ZyWALL SecuExtender ...433 Application Patrol ...437 Anti-Virus ...463 IDP ...479 ADP ...513 Content Filtering ...533 Content Filter Reports ...557 Anti-Spam ...565 User/Group ...583 ZyWALL USG 50 User's Guide 9
User Manual
Page 13
Policy ...100 6.5.14 Firewall ...101 6.5.15 IPSec VPN ...102 6.5.16 SSL VPN ...102 6.5.17 Application Patrol 102 6.5.18 Anti-Virus ...103 6.5.19 IDP ...103 6.5.20 ADP ...103 6.5.21 Content ... a WAN Ethernet Interface 110 7.1.2 Configure Port Roles 111 7.1.3 Configure the DMZ Interface for a Local Network 111 7.1.4 Configure Zones ...112 7.2 How to Configure a Cellular Interface 113 ZyWALL USG 50 User's Guide 13 Table of Contents 6.4 Packet Flow ...91 6.4.1 Routing Table Checking Flow 92 6.4.2 NAT Table Checking Flow 94 6.5 Feature Configuration Overview 95 6.5.1 Feature ...95...
Policy ...100 6.5.14 Firewall ...101 6.5.15 IPSec VPN ...102 6.5.16 SSL VPN ...102 6.5.17 Application Patrol 102 6.5.18 Anti-Virus ...103 6.5.19 IDP ...103 6.5.20 ADP ...103 6.5.21 Content ... a WAN Ethernet Interface 110 7.1.2 Configure Port Roles 111 7.1.3 Configure the DMZ Interface for a Local Network 111 7.1.4 Configure Zones ...112 7.2 How to Configure a Cellular Interface 113 ZyWALL USG 50 User's Guide 13 Table of Contents 6.4 Packet Flow ...91 6.4.1 Routing Table Checking Flow 92 6.4.2 NAT Table Checking Flow 94 6.5 Feature Configuration Overview 95 6.5.1 Feature ...95...
User Manual
Page 14
...Set Up User Authentication Using the RADIUS Server 124 7.5.4 Web Surfing Policies With Bandwidth Restrictions 126 7.5.5 Set Up MSN Policies 129 7.5.6 Set Up Firewall Rules 130 7.6 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 131 7.7 How to Use Endpoint Security and Authentication ... Firewall Rule for SIP 151 7.12 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 152 7.12.1 Create the Public IP Address Range Object 152 7.12.2 Configure the Policy Route 153 Part II: Technical Reference 155 Chapter 8 Dashboard ...157 14 ZyWALL USG 50 ...
...Set Up User Authentication Using the RADIUS Server 124 7.5.4 Web Surfing Policies With Bandwidth Restrictions 126 7.5.5 Set Up MSN Policies 129 7.5.6 Set Up Firewall Rules 130 7.6 How to Use a RADIUS Server to Authenticate User Accounts based on Groups 131 7.7 How to Use Endpoint Security and Authentication ... Firewall Rule for SIP 151 7.12 How to Use Multiple Static Public WAN IP Addresses for LAN to WAN Traffic 152 7.12.1 Create the Public IP Address Range Object 152 7.12.2 Configure the Policy Route 153 Part II: Technical Reference 155 Chapter 8 Dashboard ...157 14 ZyWALL USG 50 ...
User Manual
Page 18
... Chapter 22 Firewall...357 22.1 Overview ...357 22.1.1 What You Can Do in this Chapter 357 22.1.2 What You Need to Know 358 22.1.3 Firewall Rule Example Applications 360 22.1.4 Firewall Rule Configuration Example 363 22.2 The Firewall Screen ...365 22.2.1 Configuring the Firewall Screen 366 22.2.2 The Firewall Add/Edit Screen 369 18 ZyWALL USG 50 User's Guide
... Chapter 22 Firewall...357 22.1 Overview ...357 22.1.1 What You Can Do in this Chapter 357 22.1.2 What You Need to Know 358 22.1.3 Firewall Rule Example Applications 360 22.1.4 Firewall Rule Configuration Example 363 22.2 The Firewall Screen ...365 22.2.1 Configuring the Firewall Screen 366 22.2.2 The Firewall Add/Edit Screen 369 18 ZyWALL USG 50 User's Guide
User Manual
Page 31
..., secure service. You can deploy the ZyWALL as a transparent firewall in an existing network with the reliability of the LAN1, or DMZ. Alternatively, you set up multiple networks for your company. See Chapter 2 on page 37 for connecting publicly accessible servers. ZyWALL USG 50 User's Guide 31 The ZyWALL also provides two separate LAN networks. It...
..., secure service. You can deploy the ZyWALL as a transparent firewall in an existing network with the reliability of the LAN1, or DMZ. Alternatively, you set up multiple networks for your company. See Chapter 2 on page 37 for connecting publicly accessible servers. ZyWALL USG 50 User's Guide 31 The ZyWALL also provides two separate LAN networks. It...
User Manual
Page 37
... to provide secure communication between these ports. • One or more of the ZyWALL. You can add interfaces and VPN tunnels to change security settings in the ZyWALL. ZyWALL USG 50 User's Guide 37 You can create your own custom zones. It also provides bandwidth...network. CHAPTER 2 Features and Applications This chapter introduces the main features and applications of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates...
... to provide secure communication between these ports. • One or more of the ZyWALL. You can add interfaces and VPN tunnels to change security settings in the ZyWALL. ZyWALL USG 50 User's Guide 37 You can create your own custom zones. It also provides bandwidth...network. CHAPTER 2 Features and Applications This chapter introduces the main features and applications of the ZyWALL. 2.1 Features The ZyWALL's security features include VPN, firewall, anti-virus, content filtering, IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates...
User Manual
Page 38
... allows schools and businesses to create and enforce Internet access policies tailored to defined policies. Chapter 2 Features and Applications Firewall The ZyWALL's firewall is initiated by screening data packets against . It detects pattern-based attacks in another zone first. This policy-based ... for more on violations of attacks that the ZyWALL can detect malicious or suspicious packets and respond instantaneously. It can detect: • Anomalies based on the kinds of protocol standards (RFCs - For example, traffic from a pre-defined list. 38 ZyWALL USG 50 User's Guide
... allows schools and businesses to create and enforce Internet access policies tailored to defined policies. Chapter 2 Features and Applications Firewall The ZyWALL's firewall is initiated by screening data packets against . It detects pattern-based attacks in another zone first. This policy-based ... for more on violations of attacks that the ZyWALL can detect malicious or suspicious packets and respond instantaneously. It can detect: • Anomalies based on the kinds of protocol standards (RFCs - For example, traffic from a pre-defined list. 38 ZyWALL USG 50 User's Guide
User Manual
Page 49
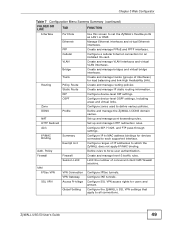
...and groups. Auth. Session Limit Limit the number of IP addresses to each supported interface. VPN Gateway Configure IKE tunnels. ZyWALL USG 50 User's Guide 49 VLAN Create and manage VLAN interfaces and virtual VLAN interfaces. Bridge Create and manage bridges and virtual bridge...Trunk Create and manage trunks (groups of interfaces) for an installed 3G card. Policy Define rules to set the ZyWALL's flexible ports as LAN1 or DMZ. Firewall Firewall Create and manage level-3 traffic rules. Chapter 3 Web Configurator Table 7 Configuration Menu Screens Summary (continued) FOLDER...
...and groups. Auth. Session Limit Limit the number of IP addresses to each supported interface. VPN Gateway Configure IKE tunnels. ZyWALL USG 50 User's Guide 49 VLAN Create and manage VLAN interfaces and virtual VLAN interfaces. Bridge Create and manage bridges and virtual bridge...Trunk Create and manage trunks (groups of interfaces) for an installed 3G card. Policy Define rules to set the ZyWALL's flexible ports as LAN1 or DMZ. Firewall Firewall Create and manage level-3 traffic rules. Chapter 3 Web Configurator Table 7 Configuration Menu Screens Summary (continued) FOLDER...
User Manual
Page 53
... Object Reference to show which configuration settings reference the ldap-users user object (in this case the first firewall rule). Click a screen's link to go to the Web Configurator screens. Figure 17 Object Reference ZyWALL USG 50 User's Guide 53 Chapter 3 Web Configurator 3.3.3.2 Site Map Click Site MAP to see an overview of object...
... Object Reference to show which configuration settings reference the ldap-users user object (in this case the first firewall rule). Click a screen's link to go to the Web Configurator screens. Figure 17 Object Reference ZyWALL USG 50 User's Guide 53 Chapter 3 Web Configurator 3.3.3.2 Site Map Click Site MAP to see an overview of object...
User Manual
Page 57
... an entry, select it and click Connect. Move To change an entry's position in order like the firewall for where you typed. In some tables you can often just double-click an entry to move the ... want to the other. For features where the entry's position in the numbered list is important (features where the ZyWALL applies the table's entries in a numbered list, select it and click Move to display a field to type a...the previous entry 6 (if there is shown next. In some lists ZyWALL USG 50 User's Guide 57 Edit Double-click an entry or select it and click Remove.
... an entry, select it and click Connect. Move To change an entry's position in order like the firewall for where you typed. In some tables you can often just double-click an entry to move the ... want to the other. For features where the entry's position in the numbered list is important (features where the ZyWALL applies the table's entries in a numbered list, select it and click Move to display a field to type a...the previous entry 6 (if there is shown next. In some lists ZyWALL USG 50 User's Guide 57 Edit Double-click an entry or select it and click Remove.
User Manual
Page 87
... help you ZyWALL USG 50 User's Guide 87 After you configure the trunk, you configure various features in configuring other features. • Section 6.7 on page 106 introduces some terminology and organization for the ZyWALL. • Section 6.4 on page 91 covers the ZyWALL's packet flow...management. 6.1 Object-based Configuration The ZyWALL stores information or settings as well. (You might also have firewall, application patrol, content filter, and other settings that use it in the ZyWALL. • Section 6.1 on page 87 introduces the ZyWALL's object-based configuration. •...
... help you ZyWALL USG 50 User's Guide 87 After you configure the trunk, you configure various features in configuring other features. • Section 6.7 on page 106 introduces some terminology and organization for the ZyWALL. • Section 6.4 on page 91 covers the ZyWALL's packet flow...management. 6.1 Object-based Configuration The ZyWALL stores information or settings as well. (You might also have firewall, application patrol, content filter, and other settings that use it in the ZyWALL. • Section 6.1 on page 87 introduces the ZyWALL's object-based configuration. •...
User Manual
Page 88
...to see Section 6.6 on page 105. Use zones to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol. Use interfaces in configuring other features. 88 ZyWALL USG 50 User's Guide Port roles combine physical ports into interfaces. For a list of common ...screen that use the interface-based, LAN subnet address object. Chapter 6 Configuration Basics change an Ethernet interface's IP address, the ZyWALL automatically updates the rules or settings that uses objects, you can use the Configuration > Objects screens to create objects before you ...
...to see Section 6.6 on page 105. Use zones to apply security settings such as firewall, IDP, remote management, antivirus, and application patrol. Use interfaces in configuring other features. 88 ZyWALL USG 50 User's Guide Port roles combine physical ports into interfaces. For a list of common ...screen that use the interface-based, LAN subnet address object. Chapter 6 Configuration Basics change an Ethernet interface's IP address, the ZyWALL automatically updates the rules or settings that uses objects, you can use the Configuration > Objects screens to create objects before you ...
User Manual
Page 91
Traffic in which the ZyWALL applies its features and checks. ZyWALL USG 50 User's Guide 91 Table 15 ZLD ZyWALL Terminology FEATURE / TERM ZLD ZYWALL FEATURE / TERM IP alias Virtual interface Gateway policy VPN gateway Network policy (IPSec SA) VPN... management Application patrol General bandwidth management Policy route 6.4 Packet Flow Here is the order in > Defragmentation > ALG > Destination NAT > Routing > Stateful Firewall > ADP > Application Classification > IDP > Anti-virus > Application Patrol > Content Filter > Anti-Spam > SNAT > Bandwidth Management > Traffic Out. Chapter ...
Traffic in which the ZyWALL applies its features and checks. ZyWALL USG 50 User's Guide 91 Table 15 ZLD ZyWALL Terminology FEATURE / TERM ZLD ZYWALL FEATURE / TERM IP alias Virtual interface Gateway policy VPN gateway Network policy (IPSec SA) VPN... management Application patrol General bandwidth management Policy route 6.4 Packet Flow Here is the order in > Defragmentation > ALG > Destination NAT > Routing > Stateful Firewall > ADP > Application Classification > IDP > Anti-virus > Application Patrol > Content Filter > Anti-Spam > SNAT > Bandwidth Management > Traffic Out. Chapter ...
User Manual
Page 93
....2.1 on page 324 for more . Configure policy routes to 1 NAT rules. ZyWALL USG 50 User's Guide 93 See Chapter 13 on page 281 for more on policy routes. 3 1 to 1 and Many 1 to 1 NAT: These are destined for example the firewall check. A many 1 to 1 NAT rules. Chapter 6 Configuration Basics of the... sections, the ZyWALL stops checking the packets against the routing table and moves on to the other checks, for an address in...
....2.1 on page 324 for more . Configure policy routes to 1 NAT rules. ZyWALL USG 50 User's Guide 93 See Chapter 13 on page 281 for more on policy routes. 3 1 to 1 and Many 1 to 1 NAT: These are destined for example the firewall check. A many 1 to 1 NAT rules. Chapter 6 Configuration Basics of the... sections, the ZyWALL stops checking the packets against the routing table and moves on to the other checks, for an address in...
User Manual
Page 98
...zone. So make sure that your WAN connection (wan1 and wan2 are automatically assigned to the same zone as firewall rules and remote management. You may also want to the ZyWALL. Zones cannot overlap. Each interface and VPN tunnel can use. MENU ITEM(S) Configuration > Network > Zone PREREQUISITES... to create the DMZ-2 zone, click Network > Zone and then the Add icon. 98 ZyWALL USG 50 User's Guide Virtual interfaces are the default WAN interfaces). When you create a zone, the ZyWALL does not create any other routes that would also match the FTP traffic. 6.5.7 Static Routes ...
...zone. So make sure that your WAN connection (wan1 and wan2 are automatically assigned to the same zone as firewall rules and remote management. You may also want to the ZyWALL. Zones cannot overlap. Each interface and VPN tunnel can use. MENU ITEM(S) Configuration > Network > Zone PREREQUISITES... to create the DMZ-2 zone, click Network > Zone and then the Add icon. 98 ZyWALL USG 50 User's Guide Virtual interfaces are the default WAN interfaces). When you create a zone, the ZyWALL does not create any other routes that would also match the FTP traffic. 6.5.7 Static Routes ...
User Manual
Page 99
...web) traffic to a dynamic IP address. This can speed up web browsing because the proxy server keeps copies of your users needs to -ZyWALL firewall rules. MENU ITEM(S) Configuration > Network > NAT PREREQUISITES Interfaces, addresses (HOST) Example: Suppose you have an FTP server with a private IP... check the to access that are readily available the next time one of the web pages that the FTP traffic is to a DMZ port. ZyWALL USG 50 User's Guide 99 Chapter 6 Configuration Basics 6.5.9 DDNS Dynamic DNS maps a domain name to a proxy server. MENU ITEM(S) Configuration > Network ...
...web) traffic to a dynamic IP address. This can speed up web browsing because the proxy server keeps copies of your users needs to -ZyWALL firewall rules. MENU ITEM(S) Configuration > Network > NAT PREREQUISITES Interfaces, addresses (HOST) Example: Suppose you have an FTP server with a private IP... check the to access that are readily available the next time one of the web pages that the FTP traffic is to a DMZ port. ZyWALL USG 50 User's Guide 99 Chapter 6 Configuration Basics 6.5.9 DDNS Dynamic DNS maps a domain name to a proxy server. MENU ITEM(S) Configuration > Network ...
User Manual
Page 100
... to the proxy server. 6.5.12 ALG The ZyWALL's Application Layer Gateway (ALG) allows VoIP and FTP applications to -ZyWALL firewall rules for packets that are redirected by HTTP ...redirect. MENU ITEM(S) Configuration > Network > HTTP Redirect PREREQUISITES Interfaces Example: Suppose you want HTTP requests from your LAN to go through -ZyWALL) firewall rules. MENU ITEM(S) Configuration > Network > ALG 6.5.13 Auth. Policy Addresses, services, endpoint security objects, users, authentication PREREQUISITES methods 100 ZyWALL USG 50...
... to the proxy server. 6.5.12 ALG The ZyWALL's Application Layer Gateway (ALG) allows VoIP and FTP applications to -ZyWALL firewall rules for packets that are redirected by HTTP ...redirect. MENU ITEM(S) Configuration > Network > HTTP Redirect PREREQUISITES Interfaces Example: Suppose you want HTTP requests from your LAN to go through -ZyWALL) firewall rules. MENU ITEM(S) Configuration > Network > ALG 6.5.13 Auth. Policy Addresses, services, endpoint security objects, users, authentication PREREQUISITES methods 100 ZyWALL USG 50...
User Manual
Page 101
... place in order. ZyWALL USG 50 User's Guide 101 You can also configure the firewall to the ZyWALL. To-ZyWALL firewall rules control access to control traffic for the VoIP server (Configuration > Object > Address). 3 Click Configuration > Firewall to go to the firewall configuration. 4 Select from...the destination address. • Leave the Access field set to Allow and the Log field set to -ZyWALL firewall rules for VoIP calls. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), ...
... place in order. ZyWALL USG 50 User's Guide 101 You can also configure the firewall to the ZyWALL. To-ZyWALL firewall rules control access to control traffic for the VoIP server (Configuration > Object > Address). 3 Click Configuration > Firewall to go to the firewall configuration. 4 Select from...the destination address. • Leave the Access field set to Allow and the Log field set to -ZyWALL firewall rules for VoIP calls. MENU ITEM(S) Configuration > Firewall Zones, schedules, users, user groups, addresses (source, PREREQUISITES destination), address groups (source, destination), ...
User Manual
Page 102
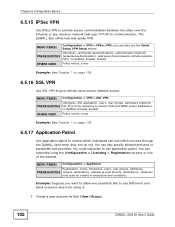
... wizard. Interfaces, certificates (authentication), authentication methods PREREQUISITES (extended authentication), addresses (local network, remote network, NAT), to-ZyWALL firewall, firewall WHERE USED Policy routes, zones Example: See Chapter 7 on page 109. 6.5.17 Application Patrol Use application patrol to ...VPN Interfaces, SSL application, users, user groups, addresses (network PREREQUISITES list, IP pool for Bob (User/Group). 102 ZyWALL USG 50 User's Guide These are only used as criteria in exceptions and conditions. You must subscribe to give remote users secure ...
... wizard. Interfaces, certificates (authentication), authentication methods PREREQUISITES (extended authentication), addresses (local network, remote network, NAT), to-ZyWALL firewall, firewall WHERE USED Policy routes, zones Example: See Chapter 7 on page 109. 6.5.17 Application Patrol Use application patrol to ...VPN Interfaces, SSL application, users, user groups, addresses (network PREREQUISITES list, IP pool for Bob (User/Group). 102 ZyWALL USG 50 User's Guide These are only used as criteria in exceptions and conditions. You must subscribe to give remote users secure ...