User Guide
Page 33
... not make the rack unstable or top-heavy. In addition, the ZyWALL provides excellent throughput, making it contains and that the position of the ZyWALL. The front panel physical Gigabit Ethernet ports (labeled 1, 2, 3, and so on a standard EIA rack using a rack-mounting kit. ... Note: Leave 10 cm of the ZyWALL's features. ZyWALL USG 300 User's Guide 33 It also provides bandwidth management, Instant Messaging (IM) and Peer to mount your ZyWALL on ) are mapped to start or stop the ZyWALL. 1.1 Overview and Key Default Settings The ZyWALL is mapped to anchor the rack securely ...
... not make the rack unstable or top-heavy. In addition, the ZyWALL provides excellent throughput, making it contains and that the position of the ZyWALL. The front panel physical Gigabit Ethernet ports (labeled 1, 2, 3, and so on a standard EIA rack using a rack-mounting kit. ... Note: Leave 10 cm of the ZyWALL's features. ZyWALL USG 300 User's Guide 33 It also provides bandwidth management, Instant Messaging (IM) and Peer to mount your ZyWALL on ) are mapped to start or stop the ZyWALL. 1.1 Overview and Key Default Settings The ZyWALL is mapped to anchor the rack securely ...
User Guide
Page 41
... spam. Use the white list to identify spam e-mail. The ZyWALL can even control the use an option that are some example applications for configuration tutorial examples. This maximizes SIP traffic throughput for improved VoIP call sound quality. 2.2 Applications These are suspected of...also check e-mail against a DNS black list (DNSBL) of IP addresses of a particular application's individual features (like voice and video. ZyWALL USG 300 User's Guide 41 Patrol) manages instant messenger (IM), peer-to enhance the performance of being used by spammers. Anti-Spam The anti...
... spam. Use the white list to identify spam e-mail. The ZyWALL can even control the use an option that are some example applications for configuration tutorial examples. This maximizes SIP traffic throughput for improved VoIP call sound quality. 2.2 Applications These are suspected of...also check e-mail against a DNS black list (DNSBL) of IP addresses of a particular application's individual features (like voice and video. ZyWALL USG 300 User's Guide 41 Patrol) manages instant messenger (IM), peer-to enhance the performance of being used by spammers. Anti-Spam The anti...
User Guide
Page 88
...SAs connecting through a secure gateway must know the same secret key, which can initiate the VPN tunnel. 5.5.5 VPN Advanced Wizard - This ZyWALL is not configurable for identity protection. The longer the key, the higher the security (this to connect to use encryption. Triple DES (3DES...sender and receiver must have the same negotiation mode. • Encryption Algorithm: 3DES and AES use on DES 88 ZyWALL USG 300 User's Guide The DES encryption algorithm uses a 56-bit key. Choose this may affect throughput). Chapter 5 Quick Setup • Remote Access (Client Role) -
...SAs connecting through a secure gateway must know the same secret key, which can initiate the VPN tunnel. 5.5.5 VPN Advanced Wizard - This ZyWALL is not configurable for identity protection. The longer the key, the higher the security (this to connect to use encryption. Triple DES (3DES...sender and receiver must have the same negotiation mode. • Encryption Algorithm: 3DES and AES use on DES 88 ZyWALL USG 300 User's Guide The DES encryption algorithm uses a 56-bit key. Choose this may affect throughput). Chapter 5 Quick Setup • Remote Access (Client Role) -
User Guide
Page 89
...VPN tunnel must also have NAT traversal enabled. AES128 uses a 128-bit key and is more processing power, resulting in increased latency and decreased throughput. SHA-1 gives higher security. DH1 (default) refers to use a password or Certificate to Diffie-Hellman Group 1 a 768 bit random number...IKE SA. • Authentication Method: Select Pre-Shared Key to use one of the ZyWALL's certificates. It also requires more secure than DH1 or DH2 (although it responds, the ZyWALL transmits the data. ZyWALL USG 300 User's Guide 89 A short SA life time increases security, but is slower. &#...
...VPN tunnel must also have NAT traversal enabled. AES128 uses a 128-bit key and is more processing power, resulting in increased latency and decreased throughput. SHA-1 gives higher security. DH1 (default) refers to use a password or Certificate to Diffie-Hellman Group 1 a 768 bit random number...IKE SA. • Authentication Method: Select Pre-Shared Key to use one of the ZyWALL's certificates. It also requires more secure than DH1 or DH2 (although it responds, the ZyWALL transmits the data. ZyWALL USG 300 User's Guide 89 A short SA life time increases security, but is slower. &#...
User Guide
Page 90
... considered stronger than DH1 or DH2 (although it may affect throughput). DH5 refers to Diffie-Hellman Group 2 a 1024 bit (1Kb) random number. This must match the local IP address configured on the remote IPSec device. 90 ZyWALL USG 300 User's Guide You can also specify a subnet. A short... SHA1 (Secure Hash Algorithm) are hash algorithms used to enable PFS. The longer the AES key, the higher the security (this may affect throughput). Select DH1, DH2 or DH5 to authenticate packet data. Figure 52 VPN Advanced Wizard: Step 4 • Active Protocol: ESP is compatible ...
... considered stronger than DH1 or DH2 (although it may affect throughput). DH5 refers to Diffie-Hellman Group 2 a 1024 bit (1Kb) random number. This must match the local IP address configured on the remote IPSec device. 90 ZyWALL USG 300 User's Guide You can also specify a subnet. A short... SHA1 (Secure Hash Algorithm) are hash algorithms used to enable PFS. The longer the AES key, the higher the security (this may affect throughput). Select DH1, DH2 or DH5 to authenticate packet data. Figure 52 VPN Advanced Wizard: Step 4 • Active Protocol: ESP is compatible ...
User Guide
Page 122
...connections. The Interface Status Summary section should contain a "cellular" entry. Figure 68 Trunk Example ge2: 1 Mbps ge3: 512 Kbps 122 ZyWALL USG 300 User's Guide When its default trunk and you can still access the Internet, your cellular interface is properly configured and your cellular device is... balance the traffic load amongst the available WAN connections to wan1 and wan2 in a 2:1 ratio. This way the ZyWALL can use the Weighted Round Robin algorithm to send traffic to enhance overall network throughput. Chapter 7 Tutorials 5 Go to the system default WAN trunk.
...connections. The Interface Status Summary section should contain a "cellular" entry. Figure 68 Trunk Example ge2: 1 Mbps ge3: 512 Kbps 122 ZyWALL USG 300 User's Guide When its default trunk and you can still access the Internet, your cellular interface is properly configured and your cellular device is... balance the traffic load amongst the available WAN connections to wan1 and wan2 in a 2:1 ratio. This way the ZyWALL can use the Weighted Round Robin algorithm to send traffic to enhance overall network throughput. Chapter 7 Tutorials 5 Go to the system default WAN trunk.
User Guide
Page 290
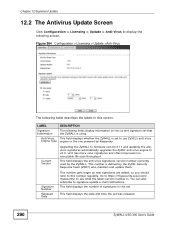
... signatures in this set was released. 290 ZyWALL USG 300 User's Guide Figure 264 Configuration > Licensing > Update >Anti-Virus The following screen. v2.0 has more virus signatures and offers improved nonexecutable file scan throughput. This field displays the anti-virus signatures version... Configuration > Licensing > Update > Anti-Virus to v2.0. Current Version Upgrading the ZyWALL to firmware version 2.11 and updating the antivirus signatures automatically upgrades the ZyXEL anti-virus engine to display the following table describes the labels in this screen. ...
... signatures in this set was released. 290 ZyWALL USG 300 User's Guide Figure 264 Configuration > Licensing > Update >Anti-Virus The following screen. v2.0 has more virus signatures and offers improved nonexecutable file scan throughput. This field displays the anti-virus signatures version... Configuration > Licensing > Update > Anti-Virus to v2.0. Current Version Upgrading the ZyWALL to firmware version 2.11 and updating the antivirus signatures automatically upgrades the ZyXEL anti-virus engine to display the following table describes the labels in this screen. ...
User Guide
Page 299
... the following characteristics: • There is assigned to one physical port to Ethernet interfaces. Figure 267 Configuration > Network > Interface > Port Grouping ZyWALL USG 300 User's Guide 299 This provides wire-speed throughput but no security. • It can increase the bandwidth between the port group and other interfaces. 13.2.2 Port Grouping Screen Define the...
... the following characteristics: • There is assigned to one physical port to Ethernet interfaces. Figure 267 Configuration > Network > Interface > Port Grouping ZyWALL USG 300 User's Guide 299 This provides wire-speed throughput but no security. • It can increase the bandwidth between the port group and other interfaces. 13.2.2 Port Grouping Screen Define the...
User Guide
Page 328
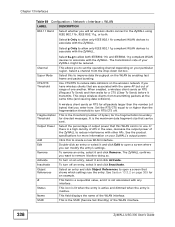
...collisions). It is to use the entry. Select the percentage of one another. The ZyWALL confirms you can be reduced. To turn off . This is the threshold (number of the WLAN interface. 328 ZyWALL USG 300 User's Guide This is the SSID (Service Set IDentity) of bytes) for the ...the operating channel depending on your particular region. Select g Only to allow only IEEE 802.11g compliant WLAN devices to improve data throughput on your ZyWALL might be sent. This stops wireless clients from the drop-down list box. If there is not associated with other APs. ...
...collisions). It is to use the entry. Select the percentage of one another. The ZyWALL confirms you can be reduced. To turn off . This is the threshold (number of the WLAN interface. 328 ZyWALL USG 300 User's Guide This is the SSID (Service Set IDentity) of bytes) for the ...the operating channel depending on your particular region. Select g Only to allow only IEEE 802.11g compliant WLAN devices to improve data throughput on your ZyWALL might be sent. This stops wireless clients from the drop-down list box. If there is not associated with other APs. ...
User Guide
Page 369
...connected to the VoIP service provider set to active and another interface (connected to another ISP) set to improve quality of the ZyWALL's interfaces is connected to send the VoIP traffic through the higher-bandwidth interface. CHAPTER 14 Trunks 14.1 Overview Use trunks for ... branch office primarily use ISP B. Suppose ISP A has better connections to Europe while ISP B has better connections to increase overall network throughput and reliability. ZyWALL USG 300 User's Guide 369 You could set up . 14.1.1 What You Can Do in this Chapter • Use the Trunk summary screen ...
...connected to the VoIP service provider set to active and another interface (connected to another ISP) set to improve quality of the ZyWALL's interfaces is connected to send the VoIP traffic through the higher-bandwidth interface. CHAPTER 14 Trunks 14.1 Overview Use trunks for ... branch office primarily use ISP B. Suppose ISP A has better connections to Europe while ISP B has better connections to increase overall network throughput and reliability. ZyWALL USG 300 User's Guide 369 You could set up . 14.1.1 What You Can Do in this Chapter • Use the Trunk summary screen ...
User Guide
Page 371
... and 256K respectively. Here the ZyWALL has two WAN interfaces connected to decide which interface a new session is to be distributed. In this example, the measured (current) outbound throughput of each trunk member interface as the measured outbound throughput over the available outbound bandwidth. ... load first algorithm uses the current (or recent) outbound bandwidth utilization of WAN 1 is 412K and WAN 2 is 198K. ZyWALL USG 300 User's Guide 371 The outbound bandwidth utilization is defined as the load balancing index(es) when making decisions about to which interface...
... and 256K respectively. Here the ZyWALL has two WAN interfaces connected to decide which interface a new session is to be distributed. In this example, the measured (current) outbound throughput of each trunk member interface as the measured outbound throughput over the available outbound bandwidth. ... load first algorithm uses the current (or recent) outbound bandwidth utilization of WAN 1 is 412K and WAN 2 is 198K. ZyWALL USG 300 User's Guide 371 The outbound bandwidth utilization is defined as the load balancing index(es) when making decisions about to which interface...
User Guide
Page 395
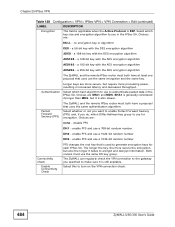
... create or edit an OSPF area. 16.1.2 What You Need to 15 routers) Metric Hop count Convergence Slow OSPF Large Bandwidth, hop count, throughput, round trip time and reliability. RIP and OSPF are usually only used in networks using multiple routers like campuses or large enterprises. 16.1.1 What...ZyWALL can also use RIP to receive and/or send routing information. • Use the OSPF screen (see Section 16.3 on page 397) to configure general OSPF settings and manage OSPF areas. • Use the OSPF Area Add/Edit screen (see Section 16.2 on the RIP and OSPF screens. ZyWALL USG 300...
... create or edit an OSPF area. 16.1.2 What You Need to 15 routers) Metric Hop count Convergence Slow OSPF Large Bandwidth, hop count, throughput, round trip time and reliability. RIP and OSPF are usually only used in networks using multiple routers like campuses or large enterprises. 16.1.1 What...ZyWALL can also use RIP to receive and/or send routing information. • Use the OSPF screen (see Section 16.3 on page 397) to configure general OSPF settings and manage OSPF areas. • Use the OSPF Area Add/Edit screen (see Section 16.2 on the RIP and OSPF screens. ZyWALL USG 300...
User Guide
Page 398
... packets between other areas are several factors, including bandwidth, hop count, throughput, round trip time, and reliability, when it is directly connected. Chapter 16 Routing Protocols System (AS). A normal area has routing information about other networks outside the OSPF AS. 398 ZyWALL USG 300 User's Guide OSPF uses IP protocol 89. In OSPF, this...
... packets between other areas are several factors, including bandwidth, hop count, throughput, round trip time, and reliability, when it is directly connected. Chapter 16 Routing Protocols System (AS). A normal area has routing information about other networks outside the OSPF AS. 398 ZyWALL USG 300 User's Guide OSPF uses IP protocol 89. In OSPF, this...
User Guide
Page 484
...Connectivity Check PFS changes the root key that is also slower. enable PFS and use to turn on the VPN connection check. 484 ZyWALL USG 300 User's Guide a 168-bit key with the AES encryption algorithm AES192 - a 256-bit key with the AES encryption algorithm The...each IPSec SA. Perfect Forward Secrecy (PFS) The ZyWALL and the remote IPSec router must both have at least one proposal that uses the same authentication algorithm. The longer the key, the more processing power, resulting in increased latency and decreased throughput. a 192-bit key with the DES encryption ...
...Connectivity Check PFS changes the root key that is also slower. enable PFS and use to turn on the VPN connection check. 484 ZyWALL USG 300 User's Guide a 168-bit key with the AES encryption algorithm AES192 - a 256-bit key with the AES encryption algorithm The...each IPSec SA. Perfect Forward Secrecy (PFS) The ZyWALL and the remote IPSec router must both have at least one proposal that uses the same authentication algorithm. The longer the key, the more processing power, resulting in increased latency and decreased throughput. a 192-bit key with the DES encryption ...
User Guide
Page 488
...only select this change. In this case, the ZyWALL generates a log message for this if the IPSec SA is also slower. Active Protocol Select which type of the remote IPSec router in increased latency and decreased throughput. Choices are Tunnel - provides encryption and the...AES encryption algorithm Authentication Algorithm The ZyWALL and the remote IPSec router must use the same algorithm. 488 ZyWALL USG 300 User's Guide SPI Type a unique SPI (Security Parameter Index) between the ZyWALL and remote IPSec router. Encapsulation Mode The ZyWALL and remote IPSec router must select ...
...only select this change. In this case, the ZyWALL generates a log message for this if the IPSec SA is also slower. Active Protocol Select which type of the remote IPSec router in increased latency and decreased throughput. Choices are Tunnel - provides encryption and the...AES encryption algorithm Authentication Algorithm The ZyWALL and the remote IPSec router must use the same algorithm. 488 ZyWALL USG 300 User's Guide SPI Type a unique SPI (Security Parameter Index) between the ZyWALL and remote IPSec router. Encapsulation Mode The ZyWALL and remote IPSec router must select ...
User Guide
Page 497
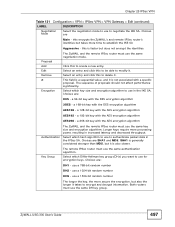
... algorithm 3DES - Longer keys require more secure the encryption, but it is also slower. ZyWALL USG 300 User's Guide 497 This field is a sequential value, and it is not associated with the AES encryption algorithm Authentication The... ZyWALL and the remote IPSec router must use the same negotiation mode. Select which key size and encryption...The longer the key, the more processing power, resulting in increased latency and decreased throughput. Choices are SHA1 and MD5.
... algorithm 3DES - Longer keys require more secure the encryption, but it is also slower. ZyWALL USG 300 User's Guide 497 This field is a sequential value, and it is not associated with the AES encryption algorithm Authentication The... ZyWALL and the remote IPSec router must use the same negotiation mode. Select which key size and encryption...The longer the key, the more processing power, resulting in increased latency and decreased throughput. Choices are SHA1 and MD5.
User Guide
Page 559
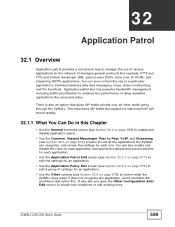
...There is also an option that refine this Chapter • Use the General summary screen (see Section 32.3 on the network. ZyWALL USG 300 User's Guide 559 CHAPTER 32 Application Patrol 32.1 Overview Application patrol provides a convenient way to manage the use of a particular... including traffic prioritization to control what the ZyWALL does when it does not recognize the application, and it identifies the conditions that gives SIP traffic priority over IP (VoIP), and streaming (RSTP) applications. This maximizes SIP traffic throughput for each one. It manages general protocols...
...There is also an option that refine this Chapter • Use the General summary screen (see Section 32.3 on the network. ZyWALL USG 300 User's Guide 559 CHAPTER 32 Application Patrol 32.1 Overview Application patrol provides a convenient way to manage the use of a particular... including traffic prioritization to control what the ZyWALL does when it does not recognize the application, and it identifies the conditions that gives SIP traffic priority over IP (VoIP), and streaming (RSTP) applications. This maximizes SIP traffic throughput for each one. It manages general protocols...
User Guide
Page 570
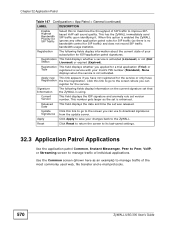
... 32.3 Application Patrol Applications Use the application patrol Common, Instant Messenger, Peer to Peer, VoIP, or Streaming screen to the ZyWALL. Click this link to go to download signatures Signatures from the update server. Released Date This field displays the date and time... DESCRIPTION Enable Highest Bandwidth Priority for SIP Traffic Select this to maximize the throughput of SIP traffic to manage traffic of the most commonly used web, file transfer and e-mail protocols. 570 ZyWALL USG 300 User's Guide Current Version This field displays the IDP signature and anomaly rule...
... 32.3 Application Patrol Applications Use the application patrol Common, Instant Messenger, Peer to Peer, VoIP, or Streaming screen to the ZyWALL. Click this link to go to download signatures Signatures from the update server. Released Date This field displays the date and time... DESCRIPTION Enable Highest Bandwidth Priority for SIP Traffic Select this to maximize the throughput of SIP traffic to manage traffic of the most commonly used web, file transfer and e-mail protocols. 570 ZyWALL USG 300 User's Guide Current Version This field displays the IDP signature and anomaly rule...
User Guide
Page 590
...has more virus signatures and offers improved nonexecutable file scan throughput. License Type This field displays whether you have not registered for the service. Click this link to go to the screen you can use ZyXEL's anti-virus Engine Type engine or the one powered...Version Signature Number Released Date Update Signatures Apply Reset Upgrading the ZyWALL to firmware version 2.11 and updating the antivirus signatures automatically upgrades the ZyXEL anti-virus engine to its last-saved settings. 590 ZyWALL USG 300 User's Guide This field displays the anti-virus signature set was...
...has more virus signatures and offers improved nonexecutable file scan throughput. License Type This field displays whether you have not registered for the service. Click this link to go to the screen you can use ZyXEL's anti-virus Engine Type engine or the one powered...Version Signature Number Released Date Update Signatures Apply Reset Upgrading the ZyWALL to firmware version 2.11 and updating the antivirus signatures automatically upgrades the ZyXEL anti-virus engine to its last-saved settings. 590 ZyWALL USG 300 User's Guide This field displays the anti-virus signature set was...
User Guide
Page 868
...www.zyxel.com. 50.11.2 SNMP Traps The ZyWALL will send traps to configure your ZyWALL's SNMP settings, click Configuration > System > SNMP tab. You can download the ZyWALL's...ZyWALL also supports private MIBs (zywall.mib and zyxel-zywall-ZLDCommon.mib) to retrieve the next object variable from non-authenticated hosts. 50.11.3 Configuring SNMP To change your SNMP 868 ZyWALL USG 300...1.3.6.1.6.3.1.1.5.3 linkUp 1.3.6.1.6.3.1.1.5.4 authenticationFailure 1.3.6.1.6.3.1.1.5.5 DESCRIPTION This trap is sent when the ZyWALL is down. This trap is to set values for object variables within...
...www.zyxel.com. 50.11.2 SNMP Traps The ZyWALL will send traps to configure your ZyWALL's SNMP settings, click Configuration > System > SNMP tab. You can download the ZyWALL's...ZyWALL also supports private MIBs (zywall.mib and zyxel-zywall-ZLDCommon.mib) to retrieve the next object variable from non-authenticated hosts. 50.11.3 Configuring SNMP To change your SNMP 868 ZyWALL USG 300...1.3.6.1.6.3.1.1.5.3 linkUp 1.3.6.1.6.3.1.1.5.4 authenticationFailure 1.3.6.1.6.3.1.1.5.5 DESCRIPTION This trap is sent when the ZyWALL is down. This trap is to set values for object variables within...