User Guide
Page 13
... ...110 7.2 How to Configure a Cellular Interface 111 7.3 How to Configure Load Balancing 113 7.3.1 Set Up Available Bandwidth on Ethernet Interfaces 113 7.3.2 Configure the WAN Trunk 114 7.4 How to Set Up an IPSec VPN Tunnel 116 7.4.1 Set Up the VPN Gateway 117 7.4.2 Set Up the VPN Connection 118 7.4.3 Configure Security Policies for the VPN Tunnel 119 ZyWALL USG 20/20W User's Guide...
... ...110 7.2 How to Configure a Cellular Interface 111 7.3 How to Configure Load Balancing 113 7.3.1 Set Up Available Bandwidth on Ethernet Interfaces 113 7.3.2 Configure the WAN Trunk 114 7.4 How to Set Up an IPSec VPN Tunnel 116 7.4.1 Set Up the VPN Gateway 117 7.4.2 Set Up the VPN Connection 118 7.4.3 Configure Security Policies for the VPN Tunnel 119 ZyWALL USG 20/20W User's Guide...
User Guide
Page 98
...zone. MENU ITEM(S) Configuration > Network > NAT 98 ZyWALL USG 20/20W User's Guide The ZyWALL uses zones, not interfaces, in many security settings, such as the interface on which they run. MENU ITEM(S) Configuration > Network > Zone PREREQUISITES Interfaces, IPSec VPN, SSL VPN WHERE USED Firewall, ...remote management, ADP Example: For example, to create the DMZ-2 zone, click Network > Zone and then the Add icon. 6.5.8 DDNS Dynamic DNS maps a domain name to the ZyWALL. The ZyWALL helps...
...zone. MENU ITEM(S) Configuration > Network > NAT 98 ZyWALL USG 20/20W User's Guide The ZyWALL uses zones, not interfaces, in many security settings, such as the interface on which they run. MENU ITEM(S) Configuration > Network > Zone PREREQUISITES Interfaces, IPSec VPN, SSL VPN WHERE USED Firewall, ...remote management, ADP Example: For example, to create the DMZ-2 zone, click Network > Zone and then the Add icon. 6.5.8 DDNS Dynamic DNS maps a domain name to the ZyWALL. The ZyWALL helps...
User Guide
Page 101
.... MENU ITEM(S) Configuration > VPN > IPSec VPN; ZyWALL USG 20/20W User's Guide 101 Chapter 6 Configuration Basics 1 Create a VoIP service object for UDP port 5060 traffic (Configuration > Object > Service). 2 Create an address object for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED Policy routes, zones Example: See Chapter 7 on page 107. 6.5.15 SSL VPN Use SSL VPN to give...
.... MENU ITEM(S) Configuration > VPN > IPSec VPN; ZyWALL USG 20/20W User's Guide 101 Chapter 6 Configuration Basics 1 Create a VoIP service object for UDP port 5060 traffic (Configuration > Object > Service). 2 Create an address object for assigning to clients, DNS and WINS server addresses), to-ZyWALL firewall, firewall WHERE USED Policy routes, zones Example: See Chapter 7 on page 107. 6.5.15 SSL VPN Use SSL VPN to give...
User Guide
Page 428
... ZyWALL USG 20/20W User's Guide Configure an address object to specify which you have configured the SSL VPN settings on the ZyWALL). • See Chapter 42 on page 621 for details on endpoint security objects. • See Chapter 41 on the network. • allow user access to specific networks. • assign private IP addresses and provide DNS/WINS...
... ZyWALL USG 20/20W User's Guide Configure an address object to specify which you have configured the SSL VPN settings on the ZyWALL). • See Chapter 42 on page 621 for details on endpoint security objects. • See Chapter 41 on the network. • allow user access to specific networks. • assign private IP addresses and provide DNS/WINS...
User Guide
Page 432
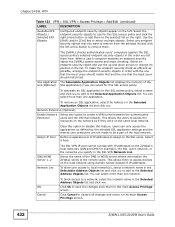
...Application Objects list. You can select more than one network. Chapter 24 SSL VPN Table 123 VPN > SSL VPN > Access Privilege > Add/Edit (continued) LABEL DESCRIPTION Available EPS Objects / Selected EPS Objects Configured endpoint security objects appear on the right. Select any endpoint security objects that...to remove them here. To block access to select multiple objects. When a user's computer matches an endpoint security object the ZyWALL grants access and stops checking. To make the endpoint security check as efficient as possible, arrange the endpoint security objects in ...
...Application Objects list. You can select more than one network. Chapter 24 SSL VPN Table 123 VPN > SSL VPN > Access Privilege > Add/Edit (continued) LABEL DESCRIPTION Available EPS Objects / Selected EPS Objects Configured endpoint security objects appear on the right. Select any endpoint security objects that...to remove them here. To block access to select multiple objects. When a user's computer matches an endpoint security object the ZyWALL grants access and stops checking. To make the endpoint security check as efficient as possible, arrange the endpoint security objects in ...
User Guide
Page 752
... SSL VPN policy %s does not configure users or user groups. of networks has been modified in the has been changed 'ippool' value. has been deleted. 752 ZyWALL USG 20/20W User's Guide specified SSL VPN policy (%s). specified SSL VPN policy (%s). SSL VPN policy rule %s The listed SSL VPN policy (%s) has been added to the end of the listed SSL VPN policy (%s) has been has been modified. SSL VPN...
... SSL VPN policy %s does not configure users or user groups. of networks has been modified in the has been changed 'ippool' value. has been deleted. 752 ZyWALL USG 20/20W User's Guide specified SSL VPN policy (%s). specified SSL VPN policy (%s). SSL VPN policy rule %s The listed SSL VPN policy (%s) has been added to the end of the listed SSL VPN policy (%s) has been has been modified. SSL VPN...
User Guide
Page 944
... DES 416 encryption method 613 end-point control 621 end-point security 621 multiple 622 multiple objects 366 SSL policy 622 summary 623 endpoint security object where used 104 enforcing policies in IPSec 399 EPC (End Point...related 3 domain name 630 Domain Name System, see DNS double-encoding attack 484 DPD 414 DSA 596 DSCP 302, 304, 718 Dynamic Domain Name System, see DDNS Dynamic Host Configuration Protocol, see also end-point security 626 ESP ...) 107 exceptional services 368 experimental-options attack 485 extended authentication and VPN gateways 394 IKE SA 420 ZyWALL USG 20/20W User's Guide
... DES 416 encryption method 613 end-point control 621 end-point security 621 multiple 622 multiple objects 366 SSL policy 622 summary 623 endpoint security object where used 104 enforcing policies in IPSec 399 EPC (End Point...related 3 domain name 630 Domain Name System, see DNS double-encoding attack 484 DPD 414 DSA 596 DSCP 302, 304, 718 Dynamic Domain Name System, see DDNS Dynamic Host Configuration Protocol, see also end-point security 626 ESP ...) 107 exceptional services 368 experimental-options attack 485 extended authentication and VPN gateways 394 IKE SA 420 ZyWALL USG 20/20W User's Guide
User Guide
Page 948
...422 tunnel mode 422 when IKE SA is disconnected 421 IPSec VPN configuration overview 101 prerequisites 100, 101 see also IPSec troubleshooting 732...DN 576 Bind DN 576, 579 directory 573 directory structure 575 Distinguished Name, see DN DN 576, 577, 579, 580 password 579 port 578, 581 search time limit 579 SSL... 579 user attributes 553 least load first load balancing 290 LED troubleshooting 727 legitimate e-mail 521 license key 215 upgrading 215 licensing 211 Lightweight Directory Access Protocol, see LDAP load balancing 289 algorithms 290, 294 least load first 290 round robin 295 ZyWALL USG 20...
...422 tunnel mode 422 when IKE SA is disconnected 421 IPSec VPN configuration overview 101 prerequisites 100, 101 see also IPSec troubleshooting 732...DN 576 Bind DN 576, 579 directory 573 directory structure 575 Distinguished Name, see DN DN 576, 577, 579, 580 password 579 port 578, 581 search time limit 579 SSL... 579 user attributes 553 least load first load balancing 290 LED troubleshooting 727 legitimate e-mail 521 license key 215 upgrading 215 licensing 211 Lightweight Directory Access Protocol, see LDAP load balancing 289 algorithms 290, 294 least load first 290 round robin 295 ZyWALL USG 20...