User Guide
Page 61
... wireless LAN adapters communicating through access points which bridge network traffic to protect wireless communication between wireless stations, access points and the wired network. WPA has user authentication and improved data encryption over WEP. • Use WPA-PSK if you have WPA-aware wireless ... computers with wireless LAN adapters communicating in a peer-to-peer network or as complex as a number of computers with a RADIUS server via the Prestige. P-320W User's Guide CHAPTER 4 Wireless LAN This chapter discusses how to configure Wireless LAN. 4.1 Introduction A wireless LAN can ...
... wireless LAN adapters communicating through access points which bridge network traffic to protect wireless communication between wireless stations, access points and the wired network. WPA has user authentication and improved data encryption over WEP. • Use WPA-PSK if you have WPA-aware wireless ... computers with wireless LAN adapters communicating in a peer-to-peer network or as complex as a number of computers with a RADIUS server via the Prestige. P-320W User's Guide CHAPTER 4 Wireless LAN This chapter discusses how to configure Wireless LAN. 4.1 Introduction A wireless LAN can ...
User Guide
Page 164
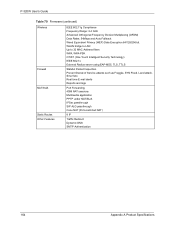
WLAN bridge to LAN Up to 32 MAC Address filters WPA, WPA-PSK OTIST (One Touch Intelligent Security Technology) IEEE 802.1x External Radius server using EAP-MD5, TLS, TTLS Stateful Packet Inspection. P-320W User's Guide Table 70 Firmware (continued) Wireless Firewall NAT/SUA Static Routes Other Features IEEE 802.11g Compliance Frequency Range...
WLAN bridge to LAN Up to 32 MAC Address filters WPA, WPA-PSK OTIST (One Touch Intelligent Security Technology) IEEE 802.1x External Radius server using EAP-MD5, TLS, TTLS Stateful Packet Inspection. P-320W User's Guide Table 70 Firmware (continued) Wireless Firewall NAT/SUA Static Routes Other Features IEEE 802.11g Compliance Frequency Range...
User Guide
Page 206
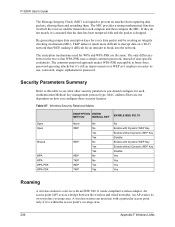
...acts as it is within the access point's coverage area. 206 Appendix F Wireless LANs The MIC provides a strong mathematical function in which the receiver and the transmitter each Authentication Method/ key management protocol type. P-320W User's Guide The Message Integrity Check (MIC) is designed to brute-force... password-guessing attacks but it difficult for WPA and WPA-PSK are not dependent on a Wi-Fi network than WEP, making it 's still an improvement over WEP as a bridge between the ...
...acts as it is within the access point's coverage area. 206 Appendix F Wireless LANs The MIC provides a strong mathematical function in which the receiver and the transmitter each Authentication Method/ key management protocol type. P-320W User's Guide The Message Integrity Check (MIC) is designed to brute-force... password-guessing attacks but it difficult for WPA and WPA-PSK are not dependent on a Wi-Fi network than WEP, making it 's still an improvement over WEP as a bridge between the ...