User Guide
Page 78
...can enable this option so that move around a lot. Positioning the antennas properly increases the range and coverage area of a wireless LAN. 78 NWA1100-N User's Guide A transmitter within a wireless device sends an RF signal to log in reverse by capturing RF signals from the air. Chapter... 6 Wireless Settings Screen TERM Fragmentation Threshold Roaming Antenna DESCRIPTION A small fragmentation threshold is not very busy. If you have two or more NWAs (or other wireless access points) ...
...can enable this option so that move around a lot. Positioning the antennas properly increases the range and coverage area of a wireless LAN. 78 NWA1100-N User's Guide A transmitter within a wireless device sends an RF signal to log in reverse by capturing RF signals from the air. Chapter... 6 Wireless Settings Screen TERM Fragmentation Threshold Roaming Antenna DESCRIPTION A small fragmentation threshold is not very busy. If you have two or more NWAs (or other wireless access points) ...
User Guide
Page 196
...it. Some advantages of IEEE 802.1x are connected to the network. • Accounting Keeps track of the client's network activity. 196 NWA1100-N User's Guide IEEE 802.1x In June 2001, the IEEE 802.1x standard was designed to extend the features of network devices. ...of the users. • Authorization Determines the network services available to authenticated users once they are : • User based identification that allows for roaming. • Support for RADIUS (Remote Authentication Dial In User Service, RFC 2138, 2139) for centralized user profile and accounting management on a ...
...it. Some advantages of IEEE 802.1x are connected to the network. • Accounting Keeps track of the client's network activity. 196 NWA1100-N User's Guide IEEE 802.1x In June 2001, the IEEE 802.1x standard was designed to extend the features of network devices. ...of the users. • Authorization Determines the network services available to authenticated users once they are : • User based identification that allows for roaming. • Support for RADIUS (Remote Authentication Dial In User Service, RFC 2138, 2139) for centralized user profile and accounting management on a ...
User Guide
Page 200
...the time of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to store the PMK it . 200 NWA1100-N User's Guide This all wireless devices sharing the same encryption keys. (a weakness of writing, the most widely available supplicant is a free download... and shortens the time required to connect to it is the software that the same encryption key is dropped. Pre-authentication enables fast roaming by creating an integrity checking mechanism (MIC), with and the packet is never used to encrypt every data packet that WPA(2)-PSK uses ...
...the time of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to store the PMK it . 200 NWA1100-N User's Guide This all wireless devices sharing the same encryption keys. (a weakness of writing, the most widely available supplicant is a free download... and shortens the time required to connect to it is the software that the same encryption key is dropped. Pre-authentication enables fast roaming by creating an integrity checking mechanism (MIC), with and the packet is never used to encrypt every data packet that WPA(2)-PSK uses ...
User Guide
Page 246
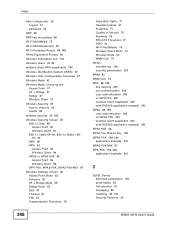
... 83 Private-Public Certificates 120 product registration 242 Protected Extensible Authentication Protocol 87 PSK 87, 200 Reset button 141 RJ-45 Port Pin Assignments 142 Roaming 78 root bridge 107 root path cost 76 RTS (Request To Send) 194 threshold 193, 194 RTS/CTS Threshold 64, 67, 71, 74, 77 Q QoS... Bridge Protocol Data Units 77 How STP Works 77 Port States 77 Rapid STP 76 Terminology 76 topology 76 Specifications 142 SSID 24, 61 246 NWA1100-N User's Guide
... 83 Private-Public Certificates 120 product registration 242 Protected Extensible Authentication Protocol 87 PSK 87, 200 Reset button 141 RJ-45 Port Pin Assignments 142 Roaming 78 root bridge 107 root path cost 76 RTS (Request To Send) 194 threshold 193, 194 RTS/CTS Threshold 64, 67, 71, 74, 77 Q QoS... Bridge Protocol Data Units 77 How STP Works 77 Port States 77 Rapid STP 76 Terminology 76 topology 76 Specifications 142 SSID 24, 61 246 NWA1100-N User's Guide
User Guide
Page 248
... Bridge Mode 65 BSS 61 Channel 61 ESS 61 Fragmentation Threshold 78 Intra-BSS Traffic 77 Operating Mode 61 Preamble 77 Quality of Service 75 Roaming 78 RTS/CTS Threshold 77 SSID 61 Wi-Fi MultiMedia 75 Wireless Client Mode 70 Wireless Mode 62 WMM QoS 75 WLAN interference 193 security...-MIX 86 WPA2-Pre-Shared Key 199 WPA2-PSK 199, 200 application example 201 WPA2-PSK-MIX 87 WPA-PSK 199, 200 application example 201 Z ZyXEL Device Ethernet parameters 105 good habits 26 Introduction 19 managing 25 resetting 30, 135 Security Features 25 248...
... Bridge Mode 65 BSS 61 Channel 61 ESS 61 Fragmentation Threshold 78 Intra-BSS Traffic 77 Operating Mode 61 Preamble 77 Quality of Service 75 Roaming 78 RTS/CTS Threshold 77 SSID 61 Wi-Fi MultiMedia 75 Wireless Client Mode 70 Wireless Mode 62 WMM QoS 75 WLAN interference 193 security...-MIX 86 WPA2-Pre-Shared Key 199 WPA2-PSK 199, 200 application example 201 WPA2-PSK-MIX 87 WPA-PSK 199, 200 application example 201 Z ZyXEL Device Ethernet parameters 105 good habits 26 Introduction 19 managing 25 resetting 30, 135 Security Features 25 248...