User Guide
Page 23
...the main applications and features of the NWA. Your NWA is highly versatile, featuring dual wireless modules and supporting up to mobile users. NWA-3500/NWA-3550 User's Guide 23 Illustrations used throughout this book are based on the NWA-3500 (unless otherwise stated). It also provides ... management and maintenance. Your NWA extends the range of network traffic security, supporting IEEE 802.1x, Wi-Fi Protected Access (WPA), WPA2 and WEP data encryption. CHAPTER 1 Introducing the NWA Note: This User's Guide includes the NWA-3500 and the NWA-3550. It is easy ...
...the main applications and features of the NWA. Your NWA is highly versatile, featuring dual wireless modules and supporting up to mobile users. NWA-3500/NWA-3550 User's Guide 23 Illustrations used throughout this book are based on the NWA-3500 (unless otherwise stated). It also provides ... management and maintenance. Your NWA extends the range of network traffic security, supporting IEEE 802.1x, Wi-Fi Protected Access (WPA), WPA2 and WEP data encryption. CHAPTER 1 Introducing the NWA Note: This User's Guide includes the NWA-3500 and the NWA-3550. It is easy ...
User Guide
Page 149
... Reset to be transmitted over the wireless network. It controls WLAN transmission priority on this profile, select Disable. NWA-3500/NWA-3550 User's Guide 149 If you select NONE, the NWA applies no WMM value assigned to it, it is available only on the VoIP_SSID profile, and provides the highest... technical background information about the topics covered in this chapter. 9.3.1 WMM QoS WMM (Wi-Fi MultiMedia) QoS (Quality of Service) ensures quality of service in this profile's BSS from the QoS list, the NWA uses WMM on the wireless network and ATC on the packet's IEEE 802.1q or...
... Reset to be transmitted over the wireless network. It controls WLAN transmission priority on this profile, select Disable. NWA-3500/NWA-3550 User's Guide 149 If you select NONE, the NWA applies no WMM value assigned to it, it is available only on the VoIP_SSID profile, and provides the highest... technical background information about the topics covered in this chapter. 9.3.1 WMM QoS WMM (Wi-Fi MultiMedia) QoS (Quality of Service) ensures quality of service in this profile's BSS from the QoS list, the NWA uses WMM on the wireless network and ATC on the packet's IEEE 802.1q or...
User Guide
Page 156
...name and password. This is allowed to 16 security profiles in to support extended authentication. You can make every user log in your NWA. User Authentication Authentication is the process of verifying whether a wireless device is a standard that extends the features of wireless security methods:....with Hide SSID Enabled MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) Most Secure WPA2 The available security modes in your NWA are ways for each user in the wireless network has to support IEEE 802.1x ...
...name and password. This is allowed to 16 security profiles in to support extended authentication. You can make every user log in your NWA. User Authentication Authentication is the process of verifying whether a wireless device is a standard that extends the features of wireless security methods:....with Hide SSID Enabled MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) Most Secure WPA2 The available security modes in your NWA are ways for each user in the wireless network has to support IEEE 802.1x ...
User Guide
Page 157
... recipient of WPA2 standard. • WPA2-PSK-MIX. Wi-Fi Protected Access (WPA) is a password shared by the NWA into unreadable text. Passphrase A passphrase functions like a password. The key can "unlock" it is further converted by a wireless access point and a client during a previous secure connection. NWA-3500/NWA-3550 User's Guide 157 Chapter 10 Wireless Security...
... recipient of WPA2 standard. • WPA2-PSK-MIX. Wi-Fi Protected Access (WPA) is a password shared by the NWA into unreadable text. Passphrase A passphrase functions like a password. The key can "unlock" it is further converted by a wireless access point and a client during a previous secure connection. NWA-3500/NWA-3550 User's Guide 157 Chapter 10 Wireless Security...
User Guide
Page 163
...Security: WPA LABEL DESCRIPTION Profile Name Type a name to identify this screen to set the selected profile to Wi-Fi Protected Access (WPA) security mode. Security Mode Choose WPA in order to stay connected. The wireless station ...Select WPA in the Security Mode field to display the following table describes the labels in this screen. The NWA automatically disconnects a wireless station from the wired network after a period of inactivity. Chapter 10 Wireless Security Screen ... have to resend user names and passwords in this field. NWA-3500/NWA-3550 User's Guide 163
...Security: WPA LABEL DESCRIPTION Profile Name Type a name to identify this screen to set the selected profile to Wi-Fi Protected Access (WPA) security mode. Security Mode Choose WPA in order to stay connected. The wireless station ...Select WPA in the Security Mode field to display the following table describes the labels in this screen. The NWA automatically disconnects a wireless station from the wired network after a period of inactivity. Chapter 10 Wireless Security Screen ... have to resend user names and passwords in this field. NWA-3500/NWA-3550 User's Guide 163
User Guide
Page 298
.... It allows a bridge to exchange public keys for wallmounting 6mm ~ 8mm (0.24" ~ 0.31") head width. The NWA can use in authentication. 298 NWA-3500/NWA-3550 User's Guide Certificates provide a way to interact with independently-configurable wireless and security settings. IEEE 802.11b/g: 17 dBm... C Humidity: 5% ~ 95% RH Distance between switches, bridges or routers. MBSSID mode allows the NWA to operate up to prioritize wireless traffic. WMM (Wi-Fi MultiMedia) QoS (Quality of the NWA, the antenna on the right is used by wireless LAN adaptor WLAN1, and the antenna on the ...
.... It allows a bridge to exchange public keys for wallmounting 6mm ~ 8mm (0.24" ~ 0.31") head width. The NWA can use in authentication. 298 NWA-3500/NWA-3550 User's Guide Certificates provide a way to interact with independently-configurable wireless and security settings. IEEE 802.11b/g: 17 dBm... C Humidity: 5% ~ 95% RH Distance between switches, bridges or routers. MBSSID mode allows the NWA to operate up to prioritize wireless traffic. WMM (Wi-Fi MultiMedia) QoS (Quality of the NWA, the antenna on the right is used by wireless LAN adaptor WLAN1, and the antenna on the ...
User Guide
Page 336
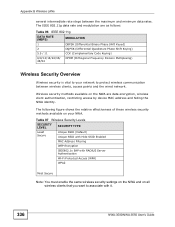
... MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable the same wireless security settings on the NWA and on all wireless clients that you want to protect wireless communication ...between the maximum and minimum data rates. Wireless security methods available on your network to associate with it. 336 NWA-3500/NWA-3550 User's Guide The IEEE 802.11g data rate and modulation are data encryption, wireless client authentication, restricting access by device...
... MAC Address Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable the same wireless security settings on the NWA and on all wireless clients that you want to protect wireless communication ...between the maximum and minimum data rates. Wireless security methods available on your network to associate with it. 336 NWA-3500/NWA-3550 User's Guide The IEEE 802.11g data rate and modulation are data encryption, wireless client authentication, restricting access by device...
User Guide
Page 340
... Client Identity Protection No No Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No WPA and WPA2 Wi-Fi Protected Access (WPA) is performed. A new WEP key is generated each access point, wireless gateway and wireless client. The following table is not necessary to...
... Client Identity Protection No No Yes PEAP Yes Optional Yes Yes Strong Moderate Yes LEAP Yes No No Yes Moderate Moderate No WPA and WPA2 Wi-Fi Protected Access (WPA) is performed. A new WEP key is generated each access point, wireless gateway and wireless client. The following table is not necessary to...
User Guide
Page 341
... it is assumed that are the same. WPA and WPA2 use WPA or WPA-PSK depending on a Wi-Fi network than TKIP. The encryption mechanisms used for an intruder to generate unique temporal encryption NWA-3500/NWA-3550 User's Guide 341 This all happens in the background automatically. Encryption Both WPA and WPA2 improve data...
... it is assumed that are the same. WPA and WPA2 use WPA or WPA-PSK depending on a Wi-Fi network than TKIP. The encryption mechanisms used for an intruder to generate unique temporal encryption NWA-3500/NWA-3550 User's Guide 341 This all happens in the background automatically. Encryption Both WPA and WPA2 improve data...
User Guide
Page 406
..., 26, 28 web configurator 23, 37, 39 WEP 23 WEP encryption 159 Wi-Fi Multimedia QoS 149 Wi-Fi Protected Access 23, 340 wired network 23, 24, 25 wireless channel 295 wireless client WPA supplicants 342 Wireless Distribution System (WDS) 28 NWA-3500/NWA-3550 User's Guide Index related documentation 3 remote management limitations 196 repeater 25 reset...
..., 26, 28 web configurator 23, 37, 39 WEP 23 WEP encryption 159 Wi-Fi Multimedia QoS 149 Wi-Fi Protected Access 23, 340 wired network 23, 24, 25 wireless channel 295 wireless client WPA supplicants 342 Wireless Distribution System (WDS) 28 NWA-3500/NWA-3550 User's Guide Index related documentation 3 remote management limitations 196 repeater 25 reset...