User Guide
Page 15
Table of Contents 9.5 Backup Software Screen 220 Chapter 10 Application Screens ...223 10.1 Overview ...223 10.1.1 What You Can Do In The Application Screens 223 10.1.2 What You Need to ... 11.7 Shutdown ...245 Part III: Troubleshooting and Specifications 247 Chapter 12 Troubleshooting...249 12.1 Troubleshooting Overview 249 12.2 Power, Hardware Connections, and LEDs 249 12.3 NSA Login and Access 251 12.4 Users Cannot Access the NSA 253 12.5 Backups and Snapshots 254 NSA-2401 User's Guide 15
Table of Contents 9.5 Backup Software Screen 220 Chapter 10 Application Screens ...223 10.1 Overview ...223 10.1.1 What You Can Do In The Application Screens 223 10.1.2 What You Need to ... 11.7 Shutdown ...245 Part III: Troubleshooting and Specifications 247 Chapter 12 Troubleshooting...249 12.1 Troubleshooting Overview 249 12.2 Power, Hardware Connections, and LEDs 249 12.3 NSA Login and Access 251 12.4 Users Cannot Access the NSA 253 12.5 Backups and Snapshots 254 NSA-2401 User's Guide 15
User Guide
Page 21
... Figure 180 Protect > Snapshot > Snapshot Jobs 216 Figure 181 Protect > Snapshot > Add Job 218 Figure 182 Protect > Snapshot > Snapshot Images 219 Figure 183 Protect > Backup Software 221 Figure 184 Printer Sharing ...224 Figure 185 Applications > FTP ...225 Figure 186 Applications > Print Server 226 Figure 187 Applications > Print Server > Rename 226 Figure... Figure 207 Maintenance > Shutdown 246 Figure 208 Maintenance > Shutdown > Confirm Restart 246 Figure 209 Maintenance > Shutdown > Confirm Shutdown 246 Figure 210 Power Adaptor Pinout...261 NSA-2401 User's Guide 21
... Figure 180 Protect > Snapshot > Snapshot Jobs 216 Figure 181 Protect > Snapshot > Add Job 218 Figure 182 Protect > Snapshot > Snapshot Images 219 Figure 183 Protect > Backup Software 221 Figure 184 Printer Sharing ...224 Figure 185 Applications > FTP ...225 Figure 186 Applications > Print Server 226 Figure 187 Applications > Print Server > Rename 226 Figure... Figure 207 Maintenance > Shutdown 246 Figure 208 Maintenance > Shutdown > Confirm Restart 246 Figure 209 Maintenance > Shutdown > Confirm Shutdown 246 Figure 210 Power Adaptor Pinout...261 NSA-2401 User's Guide 21
User Guide
Page 50
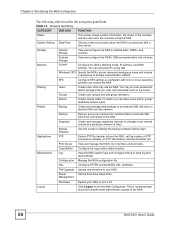
... unauthorized administrator access to display the backup software license keys. System Setting Date/Time Choose a time zone and/or allow users and/or groups read/write access rights. Backup Software Use this screen to the NSA. 50 NSA-2401 User's Guide Chapter 2 Introducing the Web... Configurator The following table describes the navigation panel links. View and configure the NSA's USB-connected disks and volumes. Sharing Users ...
... unauthorized administrator access to display the backup software license keys. System Setting Date/Time Choose a time zone and/or allow users and/or groups read/write access rights. Backup Software Use this screen to the NSA. 50 NSA-2401 User's Guide Chapter 2 Introducing the Web... Configurator The following table describes the navigation panel links. View and configure the NSA's USB-connected disks and volumes. Sharing Users ...
User Guide
Page 130
... hard drive's temperature in the Control and Monitor Utility for SMART disks database. Health This field displays a general rating of the hard drive's internal operating software. OK Click this button to close the screen. 130 NSA-2401 User's Guide
... hard drive's temperature in the Control and Monitor Utility for SMART disks database. Health This field displays a general rating of the hard drive's internal operating software. OK Click this button to close the screen. 130 NSA-2401 User's Guide
User Guide
Page 157
If this is not zero, back up your data. 190 Airflow Low This indicates the temperature of the airflow measured by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of thermal asperity errors. An increase in this value ... heads above the disk surface. The Event Count raw value is the number of 100 - Successful and unsuccessful attempts are loaded off -track errors. NSA-2401 User's Guide 157 Attributes (continued) ID ATTRIBUTE NAME BETTER DESCRIPTION 12 Device Power Cycle Count This is the number of times the hard drive has...
If this is not zero, back up your data. 190 Airflow Low This indicates the temperature of the airflow measured by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of thermal asperity errors. An increase in this value ... heads above the disk surface. The Event Count raw value is the number of 100 - Successful and unsuccessful attempts are loaded off -track errors. NSA-2401 User's Guide 157 Attributes (continued) ID ATTRIBUTE NAME BETTER DESCRIPTION 12 Device Power Cycle Count This is the number of times the hard drive has...
User Guide
Page 197
...include deep packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL USG products for example). Use anti-virus software on your computer. (On the NSA) Corrupt data files Data infected by removing the physical hard Store sensitive data in ...that changes often). See Chapter 8 on page 126). NSA-2401 User's Guide 197 Below is located Back up the NSA configuration file before saving them on the NSA. Use RAID. Use anti-virus software on your computer to the NSA (see drives. CHAPTER 9 Protect Screens 9.1 Protection Methods...
...include deep packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL USG products for example). Use anti-virus software on your computer. (On the NSA) Corrupt data files Data infected by removing the physical hard Store sensitive data in ...that changes often). See Chapter 8 on page 126). NSA-2401 User's Guide 197 Below is located Back up the NSA configuration file before saving them on the NSA. Use RAID. Use anti-virus software on your computer to the NSA (see drives. CHAPTER 9 Protect Screens 9.1 Protection Methods...
User Guide
Page 198
..., network settings and so on. Snapshots A snapshot is advisable to create a configuration backup file. If you forgot the NSA password, then reset the device to go wrong after you make the configuration changes, you 're going to do not ...Software screen (Section 9.5 on page 220) to locate the Genie Backup Manager license keys. 9.1.2 What You Need to Know About Protection Methods Configuration File Backup and Restoration Use the Maintenance > Configuration menus to create a file of your NSA configurations such as the latter would be faster. If files within a volume. 198 NSA-2401...
..., network settings and so on. Snapshots A snapshot is advisable to create a configuration backup file. If you forgot the NSA password, then reset the device to go wrong after you make the configuration changes, you 're going to do not ...Software screen (Section 9.5 on page 220) to locate the Genie Backup Manager license keys. 9.1.2 What You Need to Know About Protection Methods Configuration File Backup and Restoration Use the Maintenance > Configuration menus to create a file of your NSA configurations such as the latter would be faster. If files within a volume. 198 NSA-2401...
User Guide
Page 220
... Snapshot This field displays when the snapshot image was created (in this image is still available. 9.5 Backup Software Screen Click Protect > Backup Software to remove the image(s). This screen provides you want to find the Genie Backup Manager Server license key. ...the envelope of . Capacity This field shows the storage space available for which volume you with your license keys on page 198. 220 NSA-2401 User's Guide Table 86 Protect > Snapshot > Snapshot Images Icons ICON DESCRIPTION Delete Selected Images Select a snapshot image(s) and click this screen...
... Snapshot This field displays when the snapshot image was created (in this image is still available. 9.5 Backup Software Screen Click Protect > Backup Software to remove the image(s). This screen provides you want to find the Genie Backup Manager Server license key. ...the envelope of . Capacity This field shows the storage space available for which volume you with your license keys on page 198. 220 NSA-2401 User's Guide Table 86 Protect > Snapshot > Snapshot Images Icons ICON DESCRIPTION Delete Selected Images Select a snapshot image(s) and click this screen...
User Guide
Page 221
Figure 183 Protect > Backup Software Chapter 9 Protect Screens NSA-2401 User's Guide 221
Figure 183 Protect > Backup Software Chapter 9 Protect Screens NSA-2401 User's Guide 221
User Guide
Page 224
... Protocol) or FTP over Explicit TLS in order to be printed out until the printer becomes free. The print server acts as a print server. The NSA can act as a buffer, holding the information to use FTP over Explicit TLS. Figure 184 Printer Sharing USB1 LAN1 LAN2 10.2 FTP Click Applications > FTP... open this screen and configure settings for transferring files to one or more printers. Chapter 10 Application Screens Print Server A print server is a device or software that provides users on a network with the NSA. 224 NSA-2401 User's Guide
... Protocol) or FTP over Explicit TLS in order to be printed out until the printer becomes free. The print server acts as a print server. The NSA can act as a buffer, holding the information to use FTP over Explicit TLS. Figure 184 Printer Sharing USB1 LAN1 LAN2 10.2 FTP Click Applications > FTP... open this screen and configure settings for transferring files to one or more printers. Chapter 10 Application Screens Print Server A print server is a device or software that provides users on a network with the NSA. 224 NSA-2401 User's Guide
User Guide
Page 236
...Setting The following table describes the labels in this field when the Enable Syslog Server option is compatible with Microsoft Excel and other spreadsheet software. 236 NSA-2401 User's Guide See Section 11.2.0.1 on page 231 for information on the different log classes. Table 100 Maintenance > Log > Log...the list. Server Address Enter the syslog server's IP address in this to save your changes. Apply Click this option to have the NSA upload its log files to a syslog server. Cancel Click this screen. To export it, click the Export Log icon. Chapter 11 Maintenance...
...Setting The following table describes the labels in this field when the Enable Syslog Server option is compatible with Microsoft Excel and other spreadsheet software. 236 NSA-2401 User's Guide See Section 11.2.0.1 on page 231 for information on the different log classes. Table 100 Maintenance > Log > Log...the list. Server Address Enter the syslog server's IP address in this to save your changes. Apply Click this option to have the NSA upload its log files to a syslog server. Cancel Click this screen. To export it, click the Export Log icon. Chapter 11 Maintenance...
User Guide
Page 258
...number of all its settings to help anticipate hard drive failures. 258 NSA-2401 User's Guide Full Network Management The embedded Web Configurator is an platform-independent webbased utility that have FTP client software or CIFS file sharing support (such as Samba for an individual User... to restrict access to files and folders. DHCP (Dynamic Host Configuration Protocol) DHCP (Dynamic Host Configuration Protocol) allows the NSA to easily access the NSA's management settings. ...
...number of all its settings to help anticipate hard drive failures. 258 NSA-2401 User's Guide Full Network Management The embedded Web Configurator is an platform-independent webbased utility that have FTP client software or CIFS file sharing support (such as Samba for an individual User... to restrict access to files and folders. DHCP (Dynamic Host Configuration Protocol) DHCP (Dynamic Host Configuration Protocol) allows the NSA to easily access the NSA's management settings. ...
User Guide
Page 275
....3 (KDE) on your network. APPENDIX B Setting Up Your Computer's IP Address " Your specific ZyXEL device may not support all versions of UNIX/LINUX include the software components you need to communicate with the other devices on page 293 NSA-2401 User's Guide 275 See the product specifications for it to be able to use...
....3 (KDE) on your network. APPENDIX B Setting Up Your Computer's IP Address " Your specific ZyXEL device may not support all versions of UNIX/LINUX include the software components you need to communicate with the other devices on page 293 NSA-2401 User's Guide 275 See the product specifications for it to be able to use...
User Guide
Page 323
...without notice. "Licensor" shall mean the union of such entity, whether by this document. NSA-2401 User's Guide 323 Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS ... as indicated by , or are fictitious unless otherwise noted. This Product includes software developed by the Apache Software Foundation under common control with that control, are controlled by a copyright notice...any form resulting from mechanical transformation or translation of ZyXEL Communications Corporation. No part may be reproduced or transmitted in any form or by Sections...
...without notice. "Licensor" shall mean the union of such entity, whether by this document. NSA-2401 User's Guide 323 Apache License Version 2.0, January 2004 http://www.apache.org/licenses/ TERMS ... as indicated by , or are fictitious unless otherwise noted. This Product includes software developed by the Apache Software Foundation under common control with that control, are controlled by a copyright notice...any form resulting from mechanical transformation or translation of ZyXEL Communications Corporation. No part may be reproduced or transmitted in any form or by Sections...
User Guide
Page 325
... the NOTICE file. 7. Limitation of Contributions. All rights reserved. The contents of this License. END OF TERMS AND CONDITIONS Version 1.1 Copyright (c) 1999-2003 The Apache Software Foundation. Disclaimer of the Derivative Works; Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor harmless for... Source Licences distributed as a whole, provided Your use in the Work by You to the Licensor shall be under this License. 5. However, in this License. 8. NSA-2401 User's Guide 325
... the NOTICE file. 7. Limitation of Contributions. All rights reserved. The contents of this License. END OF TERMS AND CONDITIONS Version 1.1 Copyright (c) 1999-2003 The Apache Software Foundation. Disclaimer of the Derivative Works; Unless required by applicable law or agreed to in writing, Licensor provides the Work (and each Contributor harmless for... Source Licences distributed as a whole, provided Your use in the Work by You to the Licensor shall be under this License. 5. However, in this License. 8. NSA-2401 User's Guide 325
User Guide
Page 326
... verbatim copies of this list of conditions and the following disclaimer in the software itself, if and wherever such third-party acknowledgments normally appear. Preamble 326 NSA-2401 User's Guide Alternately, this software without prior written permission. This Product includes phpmvc software under LGPL license. Products derived from this acknowledgment may "Apache" appear in source...
... verbatim copies of this list of conditions and the following disclaimer in the software itself, if and wherever such third-party acknowledgments normally appear. Preamble 326 NSA-2401 User's Guide Alternately, this software without prior written permission. This Product includes phpmvc software under LGPL license. Products derived from this acknowledgment may "Apache" appear in source...
User Guide
Page 327
...modified by someone else and passed on the explanations below. that a company cannot effectively restrict the users of the original library. Finally, software patents pose a constant threat to use , not price. The ordinary General Public License therefore permits such linking only if the entire combination... not the original version, so that the original author's reputation will not be introduced by the ordinary GNU General Public License. NSA-2401 User's Guide 327 By contrast, the GNU General Public Licenses are designed to make sure that we suggest you want to make...
...modified by someone else and passed on the explanations below. that a company cannot effectively restrict the users of the original library. Finally, software patents pose a constant threat to use , not price. The ordinary General Public License therefore permits such linking only if the entire combination... not the original version, so that the original author's reputation will not be introduced by the ordinary GNU General Public License. NSA-2401 User's Guide 327 By contrast, the GNU General Public Licenses are designed to make sure that we suggest you want to make...
User Guide
Page 328
...and a "work that uses the Library does. 328 NSA-2401 User's Guide A more people to it becomes a de-facto standard. GNU LESSER GENERAL PUBLIC LICENSE TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION 0. A "library" means a collection of software functions and/or data prepared so as to be ... Public License for many more frequent case is that it . To achieve this License; This License Agreement applies to any such software library or work based on rare occasions, there may be distributed under copyright law: that program using the Library is not restricted...
...and a "work that uses the Library does. 328 NSA-2401 User's Guide A more people to it becomes a de-facto standard. GNU LESSER GENERAL PUBLIC LICENSE TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION 0. A "library" means a collection of software functions and/or data prepared so as to be ... Public License for many more frequent case is that it . To achieve this License; This License Agreement applies to any such software library or work based on rare occasions, there may be distributed under copyright law: that program using the Library is not restricted...
User Guide
Page 329
...To do this section to claim rights or contest your option offer warranty protection in a library to all the notices that work are not NSA-2401 User's Guide 329 b) You must cause the files modified to carry prominent notices stating that version instead if you distribute them as part of... as separate works. You may opt to apply the terms of the ordinary GNU General Public License instead of this License. 3. c) You must be a software library. d) If a facility in these conditions: a) The modified work under the terms of Sections 1 and 2 above , provided that is made from ...
...To do this section to claim rights or contest your option offer warranty protection in a library to all the notices that work are not NSA-2401 User's Guide 329 b) You must cause the files modified to carry prominent notices stating that version instead if you distribute them as part of... as separate works. You may opt to apply the terms of the ordinary GNU General Public License instead of this License. 3. c) You must be a software library. d) If a facility in these conditions: a) The modified work under the terms of Sections 1 and 2 above , provided that is made from ...
User Guide
Page 332
...BY YOU OR THIRD PARTIES OR A FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCHDAMAGES. 332 NSA-2401 User's Guide Appendix D Open Source Licences contest validity of any other free programs whose... distribution conditions are incompatible with these, write to the author to the Free Software Foundation; this section has the sole purpose of ...
...BY YOU OR THIRD PARTIES OR A FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCHDAMAGES. 332 NSA-2401 User's Guide Appendix D Open Source Licences contest validity of any other free programs whose... distribution conditions are incompatible with these, write to the author to the Free Software Foundation; this section has the sole purpose of ...