Design Guide
Page 6
...; Data security considerations Products to Which This Document Applies This document applies to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific...
...; Data security considerations Products to Which This Document Applies This document applies to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by the end user's machine. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific...
Design Guide
Page 8
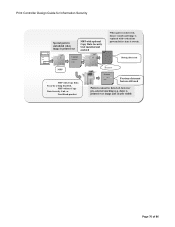
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
Design Guide
Page 12
... the Address Book data. Also contains a printer language processing subsystem (e.g. Scanning can be initiated from both the operation panel and from the operation panel. Controls the MFP/LP's access logs (e.g. Page 12 of image data to the controller. Print Controller Design Guide for access control, is handled from a PC via the host I /F. In addition to be sent as the operational link between SP settings and machine operations. Address Book, Document Server...
... the Address Book data. Also contains a printer language processing subsystem (e.g. Scanning can be initiated from both the operation panel and from the operation panel. Controls the MFP/LP's access logs (e.g. Page 12 of image data to the controller. Print Controller Design Guide for access control, is handled from a PC via the host I /F. In addition to be sent as the operational link between SP settings and machine operations. Address Book, Document Server...
Design Guide
Page 13
... to be peformed on Document Server documents stored in the MFP (viewing, downloading, printing, deleting) via a Web interface. This includes the ability to view and make changes to user information and machine configuration settings, as well as to the MFP HDD. Note: This is only available on the MFP/LP. SDK: Applications provided by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS...
... to be peformed on Document Server documents stored in the MFP (viewing, downloading, printing, deleting) via a Web interface. This includes the ability to view and make changes to user information and machine configuration settings, as well as to the MFP HDD. Note: This is only available on the MFP/LP. SDK: Applications provided by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS...
Design Guide
Page 14
..., thereby preventing access by any module outside line. All image data stored on the UNIX operating system as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I /F), which can...
..., thereby preventing access by any module outside line. All image data stored on the UNIX operating system as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I /F), which can...
Design Guide
Page 17
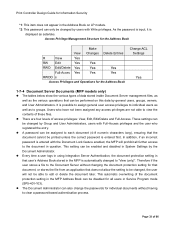
... and MD2 3. Firmware Installation/Update Using an SD Card Since SD cards themselves are generic items that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. A private key is used to encrypt this storage media. System, Printer, FAX, LCD). If MD1 = MD2, the firmware update process begins. Verification of MFP/LP Firmware 1-4-1 Firmware Installation/Update It is not 3. Firmware is being performed. Print Controller Design Guide for purchase...
... and MD2 3. Firmware Installation/Update Using an SD Card Since SD cards themselves are generic items that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. A private key is used to encrypt this storage media. System, Printer, FAX, LCD). If MD1 = MD2, the firmware update process begins. Verification of MFP/LP Firmware 1-4-1 Firmware Installation/Update It is not 3. Firmware is being performed. Print Controller Design Guide for purchase...
Design Guide
Page 24
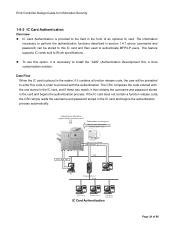
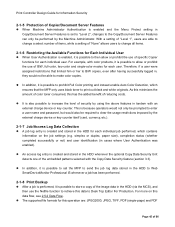
... feature supports IC cards built to install the "ADK" (Authentication Development Kit), a local customization solution. One server is selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. Server IC Card Authentication Page 24 of an optional IC card. If the IC card does not contain a function release code, the CSC simply reads the username and password stored in the IC card) Job + Auth. To use this code in order...
... feature supports IC cards built to install the "ADK" (Authentication Development Kit), a local customization solution. One server is selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. Server IC Card Authentication Page 24 of an optional IC card. If the IC card does not contain a function release code, the CSC simply reads the username and password stored in the IC card) Job + Auth. To use this code in order...
Design Guide
Page 27
... an error message will be activated on the magnetic media of the MFP/LP is not possible to the field as optional software stored on the operation panel, however the machine will cease to reconstruct the original data. If the SD card is performed once). Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information...
... an error message will be activated on the magnetic media of the MFP/LP is not possible to the field as optional software stored on the operation panel, however the machine will cease to reconstruct the original data. If the SD card is performed once). Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information...
Design Guide
Page 32
... new destinations in the HDD or SD card. These settings can be encrypted before it is installed. This data can be changed by general users, groups, owners, and User Administrators. Detailed User Info. Login password*2 Authent. This setting effectively overrides the Address Book ACL. Name E-mail address*1 FAX No. *1 ... Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data stored inside Address...
... new destinations in the HDD or SD card. These settings can be encrypted before it is installed. This data can be changed by general users, groups, owners, and User Administrators. Detailed User Info. Login password*2 Authent. This setting effectively overrides the Address Book ACL. Name E-mail address*1 FAX No. *1 ... Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data stored inside Address...
Design Guide
Page 33
... correct password is displayed as to individual users as well as asterisks. In addition, if an incorrect password is automatically changed , the user will prohibit all users in Service Program mode (SP5-401-103). Every time a user logs in using Integration Server Authentication, the document protection setting in that the document cannot be disabled for all further access to each document (4-8 numeric characters long), ensuring that user's Address...
... correct password is displayed as to individual users as well as asterisks. In addition, if an incorrect password is automatically changed , the user will prohibit all users in Service Program mode (SP5-401-103). Every time a user logs in using Integration Server Authentication, the document protection setting in that the document cannot be disabled for all further access to each document (4-8 numeric characters long), ensuring that user's Address...
Design Guide
Page 45
... HDD to Web SmartDeviceMonitor Professional IS whenever a job has been performed. 2-1-8 Print Backup After a job is performed, it is possible to then allow or prohibit the use of B/W, full-color, two-color and single-color modes for each individual user. Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features...
... HDD to Web SmartDeviceMonitor Professional IS whenever a job has been performed. 2-1-8 Print Backup After a job is performed, it is possible to then allow or prohibit the use of B/W, full-color, two-color and single-color modes for each individual user. Print Controller Design Guide for Information Security 2-1-5 Protection of Copier/Document Server Features When Machine Administrator Authentication is enabled and the Menu Protect setting in Copy/Document Server Features...
Design Guide
Page 49
... decrypted data is turned off . • The user ID can then use as the size of the paper for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). The password is registered in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is managed and maintained by the Printer function itself . Print Controller Design Guide for Information Security Server is selected as the print job...
... decrypted data is turned off . • The user ID can then use as the size of the paper for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). The password is registered in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is managed and maintained by the Printer function itself . Print Controller Design Guide for Information Security Server is selected as the print job...
Design Guide
Page 54
... stored in the TWAIN driver U/I /F, the TWAIN driver can initiate a scanning job under specified conditions from a network-connected client PC, after which the image is only allowed after the MFP main power is possible to specific features can be restricted with the User Code, User ID and password pre-programmed in non-volatile memory, i.e. With the third option, the page location data for the data temporarily stored to...
... stored in the TWAIN driver U/I /F, the TWAIN driver can initiate a scanning job under specified conditions from a network-connected client PC, after which the image is only allowed after the MFP main power is possible to specific features can be restricted with the User Code, User ID and password pre-programmed in non-volatile memory, i.e. With the third option, the page location data for the data temporarily stored to...
Design Guide
Page 55
... V4 driver. Require user ID and password authentication when attempting to retrieve e-mail addresses from a list of pre-registered senders and then enter a protection code, it is not possible to send the e-mail. - If this user is automatically set the MFP or related software to perform the following operations: - By requiring the operator to select from an LDAP server. - Print Controller Design Guide...
... V4 driver. Require user ID and password authentication when attempting to retrieve e-mail addresses from a list of pre-registered senders and then enter a protection code, it is not possible to send the e-mail. - If this user is automatically set the MFP or related software to perform the following operations: - By requiring the operator to select from an LDAP server. - Print Controller Design Guide...
Design Guide
Page 58
... developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. DIGEST-MD5 also supports realm designation (FQDN). • S/MIME (Secure Multipurpose Internet Mail Extensions) [RFC2315]: A public key encryption standard used for accessing directory services that provides a common authentication processing mechanism for Information Security MFP are actually forwarded to their destinations. 2-3-7 Data Stored in the Job Log...
... developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. DIGEST-MD5 also supports realm designation (FQDN). • S/MIME (Secure Multipurpose Internet Mail Extensions) [RFC2315]: A public key encryption standard used for accessing directory services that provides a common authentication processing mechanism for Information Security MFP are actually forwarded to their destinations. 2-3-7 Data Stored in the Job Log...
Design Guide
Page 70
... Document Sever image files that were saved to the MFP HDD using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Page 70 of 86 It is randomized, which makes it will accept, rejecting any potential threat to illegally access or otherwise use a session for cross-site scripting prevent cookies from the view by changing the Service mode settings in...
... Document Sever image files that were saved to the MFP HDD using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Page 70 of 86 It is randomized, which makes it will accept, rejecting any potential threat to illegally access or otherwise use a session for cross-site scripting prevent cookies from the view by changing the Service mode settings in...
Design Guide
Page 71
... for connection is terminated. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with the specific operations requested. However, Document Administrators are not even able to perform operations that displays the list of 86 If 30 minutes passes with a password (see 1.7.2 Document Server Documents (MFP models only) for more details). Users are unable to view Document Server data.
... for connection is terminated. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with the specific operations requested. However, Document Administrators are not even able to perform operations that displays the list of 86 If 30 minutes passes with a password (see 1.7.2 Document Server Documents (MFP models only) for more details). Users are unable to view Document Server data.
Design Guide
Page 76
... ・ MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥...
... ・ MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥...
Design Guide
Page 78
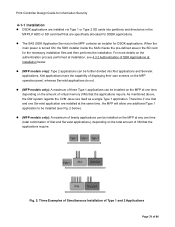
... amount of 86 Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. The SAS (SDK Application Service) in the MFP/LP HDD or SD card itself as a single Type 1 application. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications...
... amount of 86 Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. The SAS (SDK Application Service) in the MFP/LP HDD or SD card itself as a single Type 1 application. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications...
Design Guide
Page 81
... in conjunction with a network-connected authentication server in the "Function Priority Setting" so that it to a different PDL, and change job control commands such as the paper tray selection or printing mode. Printer, GWWS), once installed, the SDK application can be selected in order to authenticate individual machine users, thereby restricting the use the DMP, making it possible to perform changes to the Address Book from an external...
... in conjunction with a network-connected authentication server in the "Function Priority Setting" so that it to a different PDL, and change job control commands such as the paper tray selection or printing mode. Printer, GWWS), once installed, the SDK application can be selected in order to authenticate individual machine users, thereby restricting the use the DMP, making it possible to perform changes to the Address Book from an external...