Installation Guide
Page 4
... Configuration 33 Using a Console Connection 34 Connecting Power and Turning the Power On 34 Performing the Initial Configuration 36 Connecting Network Interfaces 37 Using Check Point Network Voyager 38 Viewing Check Point IPSO Documentation by Using Check Point Network Voyager ... Features 48 Ethernet NIC Connectors and Cables 49 Two-Port and Four-Port Copper Gigabit Ethernet NIC 50 Copper Gigabit Ethernet NIC Features in the IP690 50 Copper Gigabit Ethernet NIC Connectors and Cables 51 Two-Port Fiber-Optic Gigabit Ethernet NICs 53 Fiber-Optic Gigabit Ethernet NIC Features 53 Fiber...
... Configuration 33 Using a Console Connection 34 Connecting Power and Turning the Power On 34 Performing the Initial Configuration 36 Connecting Network Interfaces 37 Using Check Point Network Voyager 38 Viewing Check Point IPSO Documentation by Using Check Point Network Voyager ... Features 48 Ethernet NIC Connectors and Cables 49 Two-Port and Four-Port Copper Gigabit Ethernet NIC 50 Copper Gigabit Ethernet NIC Features in the IP690 50 Copper Gigabit Ethernet NIC Connectors and Cables 51 Two-Port Fiber-Optic Gigabit Ethernet NICs 53 Fiber-Optic Gigabit Ethernet NIC Features 53 Fiber...
Installation Guide
Page 11
...) Services Modules" describes how to install or replace memory, hard-disk drives, the fan unit, power supplies, battery, compact flash memory card, PC card, and the Check Point encryption accelerator card. „ Chapter 8, "Troubleshooting" discusses problems you might ...a general overview of the Check Point IP690 security platform. „ Chapter 2, "Installing the Check Point IP690 Appliance" describes how to rack-mount the appliance. „ Chapter 3, "Performing the Initial Configuration" describes how to physically connect the Check Point IP690 security platform to a network and to ...
...) Services Modules" describes how to install or replace memory, hard-disk drives, the fan unit, power supplies, battery, compact flash memory card, PC card, and the Check Point encryption accelerator card. „ Chapter 8, "Troubleshooting" discusses problems you might ...a general overview of the Check Point IP690 security platform. „ Chapter 2, "Installing the Check Point IP690 Appliance" describes how to rack-mount the appliance. „ Chapter 3, "Performing the Initial Configuration" describes how to physically connect the Check Point IP690 security platform to a network and to ...
Installation Guide
Page 12
... one or more of service. It might occur because of the variable. For example: delete interface nic1 12 Check Point IP690 Security Platform Installation Guide Note Notes provide information of commands that you must spell a command exactly as a room or equipment...compiler or preprocessor script for a compiled Check Point product. Caution Cautions indicate potential equipment damage, equipment malfunction, loss of performance, loss of data, or interruption of the following sections describe the conventions this guide uses, including notices, text conventions, and command-line...
... one or more of service. It might occur because of the variable. For example: delete interface nic1 12 Check Point IP690 Security Platform Installation Guide Note Notes provide information of commands that you must spell a command exactly as a room or equipment...compiler or preprocessor script for a compiled Check Point product. Caution Cautions indicate potential equipment damage, equipment malfunction, loss of performance, loss of data, or interruption of the following sections describe the conventions this guide uses, including notices, text conventions, and command-line...
Installation Guide
Page 15
...is a one rack-unit appliance that incorporates a serviceable slide-out tray into the chassis design. In its base configuration, the IP690 consists of: „ Solid state IDE compact flash storage, which stores the Check Point IPSO operating system „ 2-GB system RAM „ Redundant hot...-swappable AC power supplies „ Fan unit „ Encryption accelerator card to further enhance VPN performance The front panel of the IP690 security platform contains: &#...
...is a one rack-unit appliance that incorporates a serviceable slide-out tray into the chassis design. In its base configuration, the IP690 consists of: „ Solid state IDE compact flash storage, which stores the Check Point IPSO operating system „ 2-GB system RAM „ Redundant hot...-swappable AC power supplies „ Fan unit „ Encryption accelerator card to further enhance VPN performance The front panel of the IP690 security platform contains: &#...
Installation Guide
Page 16
... can manage, monitor, and configure the IP690 security platform from the command line. You can perform installations and upgrades on the IP690 security platform and enabled through the Check Point IPSO operating system. Use one of the four Ethernet ports to use for IP appliances-a secure GUI-based software image management application. With Horizon...
... can manage, monitor, and configure the IP690 security platform from the command line. You can perform installations and upgrades on the IP690 security platform and enabled through the Check Point IPSO operating system. Use one of the four Ethernet ports to use for IP appliances-a secure GUI-based software image management application. With Horizon...
Installation Guide
Page 24
...battery is not provided, use a power cord rated at http:// support.checkpoint.com/. 24 Check Point IP690 Security Platform Installation Guide Do not use telephone equipment, follow procedures that are not described in Appendix A,...can occur if you use . 1 Overview Site Requirements, Warnings, and Cautions Before you install a Check Point IP690 security platform, ensure that your computer room or wiring closet conforms to the environmental specifications listed in this document....type. Dispose of end use controls, make performance adjustments, or follow basic safety precautions.
...battery is not provided, use a power cord rated at http:// support.checkpoint.com/. 24 Check Point IP690 Security Platform Installation Guide Do not use telephone equipment, follow procedures that are not described in Appendix A,...can occur if you use . 1 Overview Site Requirements, Warnings, and Cautions Before you install a Check Point IP690 security platform, ensure that your computer room or wiring closet conforms to the environmental specifications listed in this document....type. Dispose of end use controls, make performance adjustments, or follow basic safety precautions.
Installation Guide
Page 33
... time you to configure the network settings and provides access to the admin account. This process enables you turn on power to a Check Point IP690 appliance, the initial configuration process begins. Check Point IP690 Security Platform Installation Guide 33 Note Check Point recommends that you perform the initial configuration procedure this chapter describes.
... time you to configure the network settings and provides access to the admin account. This process enables you turn on power to a Check Point IP690 appliance, the initial configuration process begins. Check Point IP690 Security Platform Installation Guide 33 Note Check Point recommends that you perform the initial configuration procedure this chapter describes.
Installation Guide
Page 34
.... You can use a straight-through cable. 3 Performing the Initial Configuration Using a Console Connection If you do not use DHCP to perform the initial configuration of the appliance as shown in Figure 9. 34 Check Point IP690 Security Platform Installation Guide Use only the RJ-45 ...the supplied null-modem cable (console cable) to the console port on the back of your Check Point IP690 security platform, you no longer need the console connection. After you perform the initial configuration, you must use a serial console connection (cable included). SLOT 1 SLOT 2 CONSOLE ...
.... You can use a straight-through cable. 3 Performing the Initial Configuration Using a Console Connection If you do not use DHCP to perform the initial configuration of the appliance as shown in Figure 9. 34 Check Point IP690 Security Platform Installation Guide Use only the RJ-45 ...the supplied null-modem cable (console cable) to the console port on the back of your Check Point IP690 security platform, you no longer need the console connection. After you perform the initial configuration, you must use a serial console connection (cable included). SLOT 1 SLOT 2 CONSOLE ...
Installation Guide
Page 36
... settings are running after you verify the console connections and still do not use DHCP to perform the initial configuration of your Check Point IP690 security platform, you no longer need the console connection. 3 Performing the Initial Configuration Performing the Initial Configuration If you do not see the Check Point Support Center at http...
... settings are running after you verify the console connections and still do not use DHCP to perform the initial configuration of your Check Point IP690 security platform, you no longer need the console connection. 3 Performing the Initial Configuration Performing the Initial Configuration If you do not see the Check Point Support Center at http...
Installation Guide
Page 38
... entered during the initial configuration and check that all cables are prompted to enter the admin username and the password you entered when you performed the initial configuration. 3 Performing the Initial Configuration Using Check Point Network Voyager Use Check Point Network Voyager to configure and monitor your appliance. To access this source... of the initial interface you plan to configure or monitor your appliance, or you are viewing, click Help. To open , you view. 38 Check Point IP690 Security Platform Installation Guide
... entered during the initial configuration and check that all cables are prompted to enter the admin username and the password you entered when you performed the initial configuration. 3 Performing the Initial Configuration Using Check Point Network Voyager Use Check Point Network Voyager to configure and monitor your appliance. To access this source... of the initial interface you plan to configure or monitor your appliance, or you are viewing, click Help. To open , you view. 38 Check Point IP690 Security Platform Installation Guide
Installation Guide
Page 40
....checkpoint.com. 40 Check Point IP690 Security Platform Installation Guide For more . Using Check Point Horizon Manager, a network security professional can obtain configuration information, upgrade (or downgrade) the operating system, perform application installations, and distribute necessary licensing...of Check Point IP security platforms. Using Check Point Horizon Manager, an administrator can manage multiple devices simultaneously, perform parallel software upgrades, device verifications, device configuration, file backups, and more information about the Check Point Horizon...
....checkpoint.com. 40 Check Point IP690 Security Platform Installation Guide For more . Using Check Point Horizon Manager, a network security professional can obtain configuration information, upgrade (or downgrade) the operating system, perform application installations, and distribute necessary licensing...of Check Point IP security platforms. Using Check Point Horizon Manager, an administrator can manage multiple devices simultaneously, perform parallel software upgrades, device verifications, device configuration, file backups, and more information about the Check Point Horizon...
Installation Guide
Page 42
...Voyager. If the power supply switches at the rear of the appliance are not applicable to deactivate its logical and physical interfaces in the IP690. For information about how to each procedure. The instructions point out steps appropriate to access Network Voyager, see "Using Check Point Network Voyager...Begin To install a NIC, you may have to reinstall the NIC to all of the IP690 appliance. Turn off the power to manually disconnect power for this procedure. Some steps are difficult to perform an orderly shutdown of the physical interfaces on page 38. 2. If you do not ...
...Voyager. If the power supply switches at the rear of the appliance are not applicable to deactivate its logical and physical interfaces in the IP690. For information about how to each procedure. The instructions point out steps appropriate to access Network Voyager, see "Using Check Point Network Voyager...Begin To install a NIC, you may have to reinstall the NIC to all of the IP690 appliance. Turn off the power to manually disconnect power for this procedure. Some steps are difficult to perform an orderly shutdown of the physical interfaces on page 38. 2. If you do not ...
Installation Guide
Page 59
... the IPSO software to use an ADP module rather than a NIC. Use Network Voyager or the command-line interface (CLI) to the IP690 appliance. 5. Turn off the power to perform an orderly shutdown of IPSO you use Network Voyager or the CLI, see the Network Voyager Reference Guide or CLI Reference Guide...
... the IPSO software to use an ADP module rather than a NIC. Use Network Voyager or the command-line interface (CLI) to the IP690 appliance. 5. Turn off the power to perform an orderly shutdown of IPSO you use Network Voyager or the CLI, see the Network Voyager Reference Guide or CLI Reference Guide...
Installation Guide
Page 67
... use the ADP interfaces. Effect on a Check Point ADP module. Check Point IP690 Security Platform Installation Guide 67 To help you understand the implications of installing an ADP module, it provides an example of the steps you might perform to the ADP interfaces as explained below: „ If you install ADP modules...
... use the ADP interfaces. Effect on a Check Point ADP module. Check Point IP690 Security Platform Installation Guide 67 To help you understand the implications of installing an ADP module, it provides an example of the steps you might perform to the ADP interfaces as explained below: „ If you install ADP modules...
Installation Guide
Page 68
When you install an ADP module in an IP690 appliance, Check Point recommends that you install an ADP module in an IP690 appliance, the network processor in the module performs all VPN encryption and decryption, even for PMC NICs. IP690 appliances support one ADP module which occupies both slots... 1 and 2. Configuring Network Topology with PMC NICs. Using a configuration of this performance loss. 68 Check Point IP690 Security Platform Installation Guide The built-in the ADP module. If VPN traffic ingresses or egresses through PMC NIC interfaces....
When you install an ADP module in an IP690 appliance, Check Point recommends that you install an ADP module in an IP690 appliance, the network processor in the module performs all VPN encryption and decryption, even for PMC NICs. IP690 appliances support one ADP module which occupies both slots... 1 and 2. Configuring Network Topology with PMC NICs. Using a configuration of this performance loss. 68 Check Point IP690 Security Platform Installation Guide The built-in the ADP module. If VPN traffic ingresses or egresses through PMC NIC interfaces....
Installation Guide
Page 71
Check Point IP690 Security Platform Installation Guide 71 To reconfigure interfaces for these interfaces is complete, the upgraded system can become the new master while you need to ... the installation is unchanged as described below. Reconfiguring Interfaces After you install the ADP module, you upgrade the original master. Configuring Check Point IPSO with IP690 ADP Interfaces Note It is best to perform the procedures in slot 2 have not changed.
Check Point IP690 Security Platform Installation Guide 71 To reconfigure interfaces for these interfaces is complete, the upgraded system can become the new master while you need to ... the installation is unchanged as described below. Reconfiguring Interfaces After you install the ADP module, you upgrade the original master. Configuring Check Point IPSO with IP690 ADP Interfaces Note It is best to perform the procedures in slot 2 have not changed.
Installation Guide
Page 78
You must perform an orderly shutdown of the hard-disk drive (slot B). Use the internal compact flash to boot the system and install the IPSO operating system on the motherboard in a slot in front of the appliance and turn the ... not use the following procedure when you replace the compact flash memory. 78 Check Point IP690 Security Platform Installation Guide Caution You risk damage to service internal components. The compact flash memory card is located on the compact flash memory card. Figure 20 Compact Flash Memory Card Slot SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 1 2 3 ...
You must perform an orderly shutdown of the hard-disk drive (slot B). Use the internal compact flash to boot the system and install the IPSO operating system on the motherboard in a slot in front of the appliance and turn the ... not use the following procedure when you replace the compact flash memory. 78 Check Point IP690 Security Platform Installation Guide Caution You risk damage to service internal components. The compact flash memory card is located on the compact flash memory card. Figure 20 Compact Flash Memory Card Slot SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 1 2 3 ...
Installation Guide
Page 79
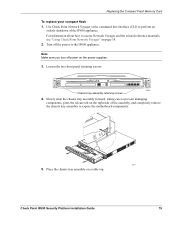
... components. Turn off power on the right side of the IP690 appliance. Loosen the two front panel retaining screws. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the assembly, and completely remove the ...SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 4. Place the chassis tray assembly on page 38. 2. For information about how to the IP690 appliance. Replacing the Compact Flash Memory Card To replace your compact flash 1. Note Make sure you turn off the power to access Network Voyager ...
... components. Turn off power on the right side of the IP690 appliance. Loosen the two front panel retaining screws. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the assembly, and completely remove the ...SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 4. Place the chassis tray assembly on page 38. 2. For information about how to the IP690 appliance. Replacing the Compact Flash Memory Card To replace your compact flash 1. Note Make sure you turn off the power to access Network Voyager ...
Installation Guide
Page 81
... eject button to the left of the slot should be flush with the IP690, you do not need to remove a PC card that was configured as an optional disk, you must turn off as an optional disk and then perform an orderly system shutdown before removing a PC card that some files in... to configure system logging options. Insert the PC card into the PC card slot until it snaps in the Voyager Reference Guide. You do not perform this procedure before you would any PMC NIC. For more information, see Chapter 4, "Installing and Replacing Network Interface Cards." Note To use the PC ...
... eject button to the left of the slot should be flush with the IP690, you do not need to remove a PC card that was configured as an optional disk, you must turn off as an optional disk and then perform an orderly system shutdown before removing a PC card that some files in... to configure system logging options. Insert the PC card into the PC card slot until it snaps in the Voyager Reference Guide. You do not perform this procedure before you would any PMC NIC. For more information, see Chapter 4, "Installing and Replacing Network Interface Cards." Note To use the PC ...
Installation Guide
Page 82
Caution To prevent the card from shock. When you purchase your IP690, you push the eject button. 4. You can be used in an IP690 1. Note A second hard-disk drive, which can use a single hard-disk drive for the flash-based IP690. Perform one or two optional hard-disk drives that also supports one of storage space. Reboot...
Caution To prevent the card from shock. When you purchase your IP690, you push the eject button. 4. You can be used in an IP690 1. Note A second hard-disk drive, which can use a single hard-disk drive for the flash-based IP690. Perform one or two optional hard-disk drives that also supports one of storage space. Reboot...