Installation Guide
Page 3
... Guide 11 In this Guide 11 Conventions this Guide Uses 12 Notices 12 Command-Line Conventions 12 Text Conventions 14 1 Overview 15 About the Check Point IP690 Security Platform 15 Managing the Check Point IP690 Security Platform 16 Check Point IP690 Security Platform Overview 17 Four-Port 10/100/1000 Ethernet NIC 17 PMC... Fan Unit 22 Power Supplies 22 Fan Unit 23 Site Requirements, Warnings, and Cautions 24 Software Requirements 24 Product Disposal 25 2 Installing the Check Point IP690 Appliance 27 Before You Begin 27 Rack-Mounting the Appliance 27 Check Point...
... Guide 11 In this Guide 11 Conventions this Guide Uses 12 Notices 12 Command-Line Conventions 12 Text Conventions 14 1 Overview 15 About the Check Point IP690 Security Platform 15 Managing the Check Point IP690 Security Platform 16 Check Point IP690 Security Platform Overview 17 Four-Port 10/100/1000 Ethernet NIC 17 PMC... Fan Unit 22 Power Supplies 22 Fan Unit 23 Site Requirements, Warnings, and Cautions 24 Software Requirements 24 Product Disposal 25 2 Installing the Check Point IP690 Appliance 27 Before You Begin 27 Rack-Mounting the Appliance 27 Check Point...
Installation Guide
Page 4
... Network Interfaces 37 Using Check Point Network Voyager 38 Viewing Check Point IPSO Documentation by Using Check Point Network Voyager 38 Using the Command-Line Interface 39 Using Check Point Horizon Manager 40 4 Installing and Replacing Network Interface Cards 41 Deactivating Configured Interfaces 41 Installing NICs... NIC Connectors and Cables 49 Two-Port and Four-Port Copper Gigabit Ethernet NIC 50 Copper Gigabit Ethernet NIC Features in the IP690 50 Copper Gigabit Ethernet NIC Connectors and Cables 51 Two-Port Fiber-Optic Gigabit Ethernet NICs 53 Fiber-Optic Gigabit Ethernet NIC ...
... Network Interfaces 37 Using Check Point Network Voyager 38 Viewing Check Point IPSO Documentation by Using Check Point Network Voyager 38 Using the Command-Line Interface 39 Using Check Point Horizon Manager 40 4 Installing and Replacing Network Interface Cards 41 Deactivating Configured Interfaces 41 Installing NICs... NIC Connectors and Cables 49 Two-Port and Four-Port Copper Gigabit Ethernet NIC 50 Copper Gigabit Ethernet NIC Features in the IP690 50 Copper Gigabit Ethernet NIC Connectors and Cables 51 Two-Port Fiber-Optic Gigabit Ethernet NICs 53 Fiber-Optic Gigabit Ethernet NIC ...
Installation Guide
Page 9
Tables Table 1 Command-Line Conventions 12 Table 2 Text Conventions 14 Table 3 Pin Assignments for Console Connector and Console Cable 18 Table 4 System Status LEDs 20 Table 5 Power Supply Status LEDs 23 Table 6 NIC PCI Frequency 47 Check Point IP690 Security Platform Installation Guide 9
Tables Table 1 Command-Line Conventions 12 Table 2 Text Conventions 14 Table 3 Pin Assignments for Console Connector and Console Cable 18 Table 4 System Status LEDs 20 Table 5 Power Supply Status LEDs 23 Table 6 NIC PCI Frequency 47 Check Point IP690 Security Platform Installation Guide 9
Installation Guide
Page 12
...this Guide Uses The following elements on a command-line path. For example: delete interface if_name Supply an interface name in Check Point business security products. For example: delete interface nic1 12 Check Point IP690 Security Platform Installation Guide Conventions this guide uses..., including notices, text conventions, and command-line conventions. You must supply. You might appear alone or precede one or ...
...this Guide Uses The following elements on a command-line path. For example: delete interface if_name Supply an interface name in Check Point business security products. For example: delete interface nic1 12 Check Point IP690 Security Platform Installation Guide Conventions this guide uses..., including notices, text conventions, and command-line conventions. You must supply. You might appear alone or precede one or ...
Installation Guide
Page 13
... You must supply a value: retry-limit Square brackets [ ] Supply a value. Check Point IP690 Security Platform Installation Guide 13 Type this Guide Uses Table 1 Command-Line Conventions (continued) Convention Description angle brackets < > Indicates arguments for a compiler or preprocessor ...argument. For example: retry-limit 60 Indicates optional arguments. pipe (|) framing -flag .ext To complete the command, supply the value. The extension might follow a variable that you must enter exactly as shown. Punctuation and mathematical notations...
... You must supply a value: retry-limit Square brackets [ ] Supply a value. Check Point IP690 Security Platform Installation Guide 13 Type this Guide Uses Table 1 Command-Line Conventions (continued) Convention Description angle brackets < > Indicates arguments for a compiler or preprocessor ...argument. For example: retry-limit 60 Indicates optional arguments. pipe (|) framing -flag .ext To complete the command, supply the value. The extension might follow a variable that you must enter exactly as shown. Punctuation and mathematical notations...
Installation Guide
Page 14
... Italics Enter indicates you press simultaneously are defined in the text. • Indicates an external book title reference. • Indicates a variable in a command: delete interface if_name 14 Check Point IP690 Security Platform Installation Guide 1 Text Conventions Table 2 describes the text conventions this guide uses. Table 2 Text Conventions Convention Description monospace font Indicates...
... Italics Enter indicates you press simultaneously are defined in the text. • Indicates an external book title reference. • Indicates a variable in a command: delete interface if_name 14 Check Point IP690 Security Platform Installation Guide 1 Text Conventions Table 2 describes the text conventions this guide uses. Table 2 Text Conventions Convention Description monospace font Indicates...
Installation Guide
Page 16
...supports a comprehensive suite of the four Ethernet ports to use for IP appliances-a secure GUI-based software image management application. Managing the Check Point IP690 Security Platform You can manage the IP690 security platform by using a standard Web browser. For information about how to access Network ... platform is designed to Check Point NG. With Network Voyager, you can manage, monitor, and configure the IP690 security platform from the command line. Horizon Manager can perform installations and upgrades on up to 2,500 Check Point IP security platforms, offering ...
...supports a comprehensive suite of the four Ethernet ports to use for IP appliances-a secure GUI-based software image management application. Managing the Check Point IP690 Security Platform You can manage the IP690 security platform by using a standard Web browser. For information about how to access Network ... platform is designed to Check Point NG. With Network Voyager, you can manage, monitor, and configure the IP690 security platform from the command line. Horizon Manager can perform installations and upgrades on up to 2,500 Check Point IP security platforms, offering ...
Installation Guide
Page 33
... Interfaces „ Using Check Point Network Voyager „ Using the Command-Line Interface „ Using Check Point Horizon Manager For information about how to the admin account. Check Point IP690 Security Platform Installation Guide 33 Note Check Point recommends that you physically install... Other than Network Interface Cards (NICs) and Accelerated Data Path (ADP) Services Modules." For information about how to a Check Point IP690 appliance, the initial configuration process begins. You can perform the initial configuration in two ways: „ Configure a DHCP server to perform...
... Interfaces „ Using Check Point Network Voyager „ Using the Command-Line Interface „ Using Check Point Horizon Manager For information about how to the admin account. Check Point IP690 Security Platform Installation Guide 33 Note Check Point recommends that you physically install... Other than Network Interface Cards (NICs) and Accelerated Data Path (ADP) Services Modules." For information about how to a Check Point IP690 appliance, the initial configuration process begins. You can perform the initial configuration in two ways: „ Configure a DHCP server to perform...
Installation Guide
Page 39
... Voyager Reference Access Points Link to complete user documentation Link to online help (context sensitive help) Using the Command-Line Interface You can also use the Check Point IPSO command-line interface (CLI) to manage and configure Check Point IP security appliances from the CLI shell and the ...settings on to the appliance. The Check Point IPSO shell is , you can view configuration settings, but you can change them. Check Point IP690 Security Platform Installation Guide 39 Nearly everything that you can also do with the CLI. Log on to administer a cluster, see when you can...
... Voyager Reference Access Points Link to complete user documentation Link to online help (context sensitive help) Using the Command-Line Interface You can also use the Check Point IPSO command-line interface (CLI) to manage and configure Check Point IP security appliances from the CLI shell and the ...settings on to the appliance. The Check Point IPSO shell is , you can view configuration settings, but you can change them. Check Point IP690 Security Platform Installation Guide 39 Nearly everything that you can also do with the CLI. Log on to administer a cluster, see when you can...
Installation Guide
Page 40
...about how to access and use the CLI, see the Check Point Web site at www.checkpoint.com. 40 Check Point IP690 Security Platform Installation Guide You must be the name of a regular file. While Check Point Network Voyager provides the device ... the operating system, perform application installations, and distribute necessary licensing to learn more . Check Point Enter IPSO command clish -c line "cli-command" Execute a single CLI command. For information about how to obtain Check Point Horizon Manager or to multiple platforms simultaneously, thereby reducing potential human...
...about how to access and use the CLI, see the Check Point Web site at www.checkpoint.com. 40 Check Point IP690 Security Platform Installation Guide You must be the name of a regular file. While Check Point Network Voyager provides the device ... the operating system, perform application installations, and distribute necessary licensing to learn more . Check Point Enter IPSO command clish -c line "cli-command" Execute a single CLI command. For information about how to obtain Check Point Horizon Manager or to multiple platforms simultaneously, thereby reducing potential human...
Installation Guide
Page 42
... Begin To install a NIC, you must deactivate the NIC by using Check Point Network Voyager. Use Check Point Network Voyager or command-line interface (CLI) to each procedure. Installing NICs Note Before removing a configured network interface card with the chassis tray assembly fully... procedure. To install a network interface card 1. Any servicing of the appliance are not applicable to deactivate its logical and physical interfaces in the IP690. Use these instructions, you need to install a NIC in Network Voyager. If you do not need the following: „ A Phillips-head...
... Begin To install a NIC, you must deactivate the NIC by using Check Point Network Voyager. Use Check Point Network Voyager or command-line interface (CLI) to each procedure. Installing NICs Note Before removing a configured network interface card with the chassis tray assembly fully... procedure. To install a network interface card 1. Any servicing of the appliance are not applicable to deactivate its logical and physical interfaces in the IP690. Use these instructions, you need to install a NIC in Network Voyager. If you do not need the following: „ A Phillips-head...
Installation Guide
Page 46
... page 38. For information about how to configure and activate the logical and physical interfaces on a specific port. 46 Check Point IP690 Security Platform Installation Guide You can asses the general operating condition of the NIC in Chapter 5, "Connecting PMC Network Interface Cards." ...Monitoring Network Interface Cards You can also use the tcpdump command to access detailed port information. Turn the power on page 38. For information about accessing Network Voyager, see "Using Check Point Network...
... page 38. For information about how to configure and activate the logical and physical interfaces on a specific port. 46 Check Point IP690 Security Platform Installation Guide You can asses the general operating condition of the NIC in Chapter 5, "Connecting PMC Network Interface Cards." ...Monitoring Network Interface Cards You can also use the tcpdump command to access detailed port information. Turn the power on page 38. For information about accessing Network Voyager, see "Using Check Point Network...
Installation Guide
Page 59
... 6. Therefore, you need to the required version as the naming conventions for the first 4 ports for IP690 Appliances" on page 68. 2. Use Network Voyager or the command-line interface (CLI) to expose the motherboard. Upgrade the IPSO software to delete the slot 1 configuration for the ...the Network Voyager Reference Guide or CLI Reference Guide for the version of the IP690 appliance. Slide the chassis tray assembly forward, pressing the release tab on a table top. Check Point IP690 Security Platform Installation Guide 00597 59 Loosen the two front panel retaining screws....
... 6. Therefore, you need to the required version as the naming conventions for the first 4 ports for IP690 Appliances" on page 68. 2. Use Network Voyager or the command-line interface (CLI) to expose the motherboard. Upgrade the IPSO software to delete the slot 1 configuration for the ...the Network Voyager Reference Guide or CLI Reference Guide for the version of the IP690 appliance. Slide the chassis tray assembly forward, pressing the release tab on a table top. Check Point IP690 Security Platform Installation Guide 00597 59 Loosen the two front panel retaining screws....
Installation Guide
Page 79
... components. SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 4. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the assembly, and completely remove the chassis tray assembly to access ...Network Voyager and the related reference materials, see "Using Check Point Network Voyager" on the power supplies. 3. Replacing the Compact Flash ...
... components. SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 4. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the assembly, and completely remove the chassis tray assembly to access ...Network Voyager and the related reference materials, see "Using Check Point Network Voyager" on the power supplies. 3. Replacing the Compact Flash ...
Installation Guide
Page 82
... with care. 82 Check Point IP690 Security Platform Installation Guide Perform a system shutdown by used in a flash-based IP690 for logging in an IP690 1. Installing a Hard-Disk Drive The IP690 is an option only for the flash-based IP690. When you purchase your IP690, you push the eject button.... 4. Caution To prevent the card from shock. Before You Begin Caution Hard-disk drives are not included in this chapter. Note A second hard-disk drive, which can by using Network Voyager or the CLI halt command...
... with care. 82 Check Point IP690 Security Platform Installation Guide Perform a system shutdown by used in a flash-based IP690 for logging in an IP690 1. Installing a Hard-Disk Drive The IP690 is an option only for the flash-based IP690. When you purchase your IP690, you push the eject button.... 4. Caution To prevent the card from shock. Before You Begin Caution Hard-disk drives are not included in this chapter. Note A second hard-disk drive, which can by using Network Voyager or the CLI halt command...
Installation Guide
Page 83
...the chassis tray assembly from the chassis. To install or replace a hard-disk drive, you perform an orderly shut down of the IP690 appliance. Turn off the power to the appliance „ Check Point hard-disk drive kit „ A Phillips-head screwdriver The ... 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 Check Point IP690 Security Platform Installation Guide 83 Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the system before attempting to access Network Voyager and...
...the chassis tray assembly from the chassis. To install or replace a hard-disk drive, you perform an orderly shut down of the IP690 appliance. Turn off the power to the appliance „ Check Point hard-disk drive kit „ A Phillips-head screwdriver The ... 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 Check Point IP690 Security Platform Installation Guide 83 Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of the system before attempting to access Network Voyager and...
Installation Guide
Page 87
... components or open the appliance. Any servicing of the appliance. SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 Check Point IP690 Security Platform Installation Guide 87 For information about how to manually disconnect power for this procedure. To replace the encryption accelerator card 1. Note You...appliance should be completed with the wrist strap before you remove the chassis tray assembly from the appliance. Use Check Point Network Voyager or the command-line interface (CLI) to the IP690 appliance. 3.
... components or open the appliance. Any servicing of the appliance. SLOT 1 SLOT 2 CONSOLE RESET AUX SLOT 3 SLOT 4 1 2 3 4 Chassis tray assembly retaining screws IP690 00581 Check Point IP690 Security Platform Installation Guide 87 For information about how to manually disconnect power for this procedure. To replace the encryption accelerator card 1. Note You...appliance should be completed with the wrist strap before you remove the chassis tray assembly from the appliance. Use Check Point Network Voyager or the command-line interface (CLI) to the IP690 appliance. 3.
Installation Guide
Page 91
... register the module, you must completely remove power to maintain a proper operating temperature. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of time. For information about how to perform IKE acceleration. The fan ... with the Check Point software on page 38. 2. Replacing a Fan Unit To enable IKE acceleration 1. For information about how to the IP690 appliance „ Replacement fan unit kit „ A Phillips-head screwdriver Caution Components inside the appliance can provide proper airflow for the encryption...
... register the module, you must completely remove power to maintain a proper operating temperature. Use Check Point Network Voyager or the command-line interface (CLI) to perform an orderly shutdown of time. For information about how to perform IKE acceleration. The fan ... with the Check Point software on page 38. 2. Replacing a Fan Unit To enable IKE acceleration 1. For information about how to the IP690 appliance „ Replacement fan unit kit „ A Phillips-head screwdriver Caution Components inside the appliance can provide proper airflow for the encryption...
Installation Guide
Page 93
... Check Point Network Voyager on the back of the appliance. 3. Use Check Point Network Voyager or command-line interface (CLI) to service an appliance. Remove the grounding cable if one is in this document. Check Point IP690 Security Platform Installation Guide 93 Locate the power supply on page 38. 2. Caution Protect your... OVER PWER OK Power supplies 00580 Caution You should have working knowledge of networking equipment before you attempt to perform an orderly shutdown of the IP690 appliance. Limit service to the procedures described in use.
... Check Point Network Voyager on the back of the appliance. 3. Use Check Point Network Voyager or command-line interface (CLI) to service an appliance. Remove the grounding cable if one is in this document. Check Point IP690 Security Platform Installation Guide 93 Locate the power supply on page 38. 2. Caution Protect your... OVER PWER OK Power supplies 00580 Caution You should have working knowledge of networking equipment before you attempt to perform an orderly shutdown of the IP690 appliance. Limit service to the procedures described in use.
Installation Guide
Page 94
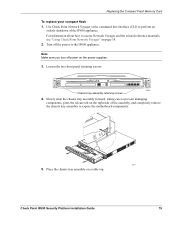
... Power Supply You can also use the handle to firmly pull the power supply out of the IP690 appliance power supplies with Check Point Network Voyager. 7 Installing and Replacing Components Other than Network Interface... if being used. 9. Similarly, you can monitor the status of the chassis. 00588 7. For information about 94 Check Point IP690 Security Platform Installation Guide Turn on the power. Plug the power cord into the empty bay until the release lever latches. 00598...Grasp the handle and release lever as shown in the following figure, and use the command-line interface (CLI).
... Power Supply You can also use the handle to firmly pull the power supply out of the IP690 appliance power supplies with Check Point Network Voyager. 7 Installing and Replacing Components Other than Network Interface... if being used. 9. Similarly, you can monitor the status of the chassis. 00588 7. For information about 94 Check Point IP690 Security Platform Installation Guide Turn on the power. Plug the power cord into the empty bay until the release lever latches. 00598...Grasp the handle and release lever as shown in the following figure, and use the command-line interface (CLI).