FVS338 Reference Manual
Page 17
... accommodate either a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. The firewall incorporates Auto UplinkTM technology. FVS338 ProSafe VPN Firewall 50 Reference Manual Security The VPN firewall is equipped with several networked PCs to share an Internet account using only a single IP address...correct configuration. Each Ethernet port will then configure itself to either type of ports. • Exposed Host (Software DMZ). The VPN firewall allows several features designed to maintain security, as to make the right connection. NAT opens a temporary path to ...
... accommodate either a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. The firewall incorporates Auto UplinkTM technology. FVS338 ProSafe VPN Firewall 50 Reference Manual Security The VPN firewall is equipped with several networked PCs to share an Internet account using only a single IP address...correct configuration. Each Ethernet port will then configure itself to either type of ports. • Exposed Host (Software DMZ). The VPN firewall allows several features designed to maintain security, as to make the right connection. NAT opens a temporary path to ...
FVS338 Reference Manual
Page 41
...3-6 • "Configuring Static Routes" on your network will function as the firewall's LAN IP address. For most applications, the default DHCP and TCP/IP settings of the firewall are available for both the LAN and DMZ settings. Otherwise, leave it to assign IP, DNS server, WINS Server,... and default gateway addresses to all of your network. Chapter 3 LAN Configuration This chapter describes how to configure LAN Setup, LAN Groups and Routing (Static IP) features of your ProSafe VPN Firewall 50, including the...
...3-6 • "Configuring Static Routes" on your network will function as the firewall's LAN IP address. For most applications, the default DHCP and TCP/IP settings of the firewall are available for both the LAN and DMZ settings. Otherwise, leave it to assign IP, DNS server, WINS Server,... and default gateway addresses to all of your network. Chapter 3 LAN Configuration This chapter describes how to configure LAN Setup, LAN Groups and Routing (Static IP) features of your ProSafe VPN Firewall 50, including the...
FVS338 Reference Manual
Page 43
...screen will manually configure all computers connected to the router's LAN. The subnet mask specifies the network number portion of the router (this is optional). By default, the router will function as the subnet mask (computed by the router). 4. Check the Enable DHCP Server radio button... mask based on your router (factory default: 192.168.1.1). (Always make sure that you will display. Unless you are in different subnets.) 3. FVS338 ProSafe VPN Firewall 50 Reference Manual 1. If another device on the IP address that the LAN Port IP address and DMZ port IP address are ...
...screen will manually configure all computers connected to the router's LAN. The subnet mask specifies the network number portion of the router (this is optional). By default, the router will function as the subnet mask (computed by the router). 4. Check the Enable DHCP Server radio button... mask based on your router (factory default: 192.168.1.1). (Always make sure that you will display. Unless you are in different subnets.) 3. FVS338 ProSafe VPN Firewall 50 Reference Manual 1. If another device on the IP address that the LAN Port IP address and DMZ port IP address are ...
FVS338 Reference Manual
Page 46
... any other network devices. Example: WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0 WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0 DMZ IP address: 192.168.10.1 with subnet 255.255.255.0 LAN IP address: 192.168.1.1 with subnet 255.255.255.0 Secondary LAN IP...IPs table. Warning: Make sure the secondary IP addresses are assigned dynamic IP addresses by this router. The router's DHCP server will be added to the Network Database in two ways: • Using the DHCP Server. FVS338 ProSafe VPN Firewall 50 Reference Manual • Subnet Mask: IPv4 Subnet Mask. • Action/Edit: Click to ...
... any other network devices. Example: WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0 WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0 DMZ IP address: 192.168.10.1 with subnet 255.255.255.0 LAN IP address: 192.168.1.1 with subnet 255.255.255.0 Secondary LAN IP...IPs table. Warning: Make sure the secondary IP addresses are assigned dynamic IP addresses by this router. The router's DHCP server will be added to the Network Database in two ways: • Using the DHCP Server. FVS338 ProSafe VPN Firewall 50 Reference Manual • Subnet Mask: IPv4 Subnet Mask. • Action/Edit: Click to ...
FVS338 Reference Manual
Page 82
... preventing the LAN users from consuming all the bandwidth on the Port Triggering screen.. The Port Triggering Rule will be added to the DMZ interface. 4-28 Firewall Protection and Content Filtering v1.0, March 2009 FVS338 ProSafe VPN Firewall 50 Reference Manual b. Click Edit in the Port Triggering Rules table. Click Add. Enter the End Port range (1 - 65534). 6.
... preventing the LAN users from consuming all the bandwidth on the Port Triggering screen.. The Port Triggering Rule will be added to the DMZ interface. 4-28 Firewall Protection and Content Filtering v1.0, March 2009 FVS338 ProSafe VPN Firewall 50 Reference Manual b. Click Edit in the Port Triggering Rules table. Click Add. Enter the End Port range (1 - 65534). 6.
FVS338 Reference Manual
Page 87
...4-3. The type of the initiating device for more information about log entry messages. The IP address of event and what action was recorded. Firewall Protection and Content Filtering v1.0, March 2009 4-33 Refer to Appendix B, "System Logs and Error Messages" for this log entry. Log ..., and whether it 's on the View Log icon opposite the Firewall Logs & E-mail tab. The service port number of the destination device, and whether it originated from the LAN, WAN or DMZ. The name or IP address of the log by clicking send log. 3. FVS338 ProSafe VPN Firewall 50 Reference Manual 1.
...4-3. The type of the initiating device for more information about log entry messages. The IP address of event and what action was recorded. Firewall Protection and Content Filtering v1.0, March 2009 4-33 Refer to Appendix B, "System Logs and Error Messages" for this log entry. Log ..., and whether it 's on the View Log icon opposite the Firewall Logs & E-mail tab. The service port number of the destination device, and whether it originated from the LAN, WAN or DMZ. The name or IP address of the log by clicking send log. 3. FVS338 ProSafe VPN Firewall 50 Reference Manual 1.
FVS338 Reference Manual
Page 132
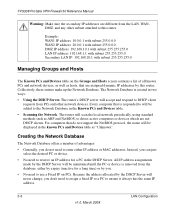
...Allow • ALLOW always 6-4 Router and Network Management v1.0, March 2009 VPN Firewall Features That Increase Traffic Features that are as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of ... blocks all existing rules for inbound traffic. Warning: This feature is for the procedure on how to use this feature. FVS338 ProSafe VPN Firewall 50 Reference Manual See "Setting Block Sites (Content Filtering)" on page 4-20 for the procedure on how to use this feature...
...Allow • ALLOW always 6-4 Router and Network Management v1.0, March 2009 VPN Firewall Features That Increase Traffic Features that are as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of ... blocks all existing rules for inbound traffic. Warning: This feature is for the procedure on how to use this feature. FVS338 ProSafe VPN Firewall 50 Reference Manual See "Setting Block Sites (Content Filtering)" on page 4-20 for the procedure on how to use this feature...
FVS338 Reference Manual
Page 12
Routing Logs ...B-14 LAN to WAN Logs B-15 LAN to DMZ Logs B-15 DMZ to WAN Logs B-15 WAN to LAN Logs B-15 DMZ to LAN Logs B-16 WAN to DMZ Logs B-16 Appendix C Related Documents Index xii Contents v1.0, March 2008
Routing Logs ...B-14 LAN to WAN Logs B-15 LAN to DMZ Logs B-15 DMZ to WAN Logs B-15 WAN to LAN Logs B-15 DMZ to LAN Logs B-16 WAN to DMZ Logs B-16 Appendix C Related Documents Index xii Contents v1.0, March 2008
FVS338 Reference Manual
Page 19
... on the service port number of PCs on your network. FVS338 ProSafe VPN Firewall 50 Reference Manual • Port Forwarding with Auto Uplink With its own address as a DNS server to the attached PCs. The VPN firewall allows several networked PCs to one computer on your PC....are autosensing and capable of ports. • Exposed Host (Software DMZ). That port will automatically sense whether the Ethernet cable plugged into the port should have configured an inbound rule. The VPN firewall dynamically assigns network configuration information, including IP, gateway, and domain ...
... on the service port number of PCs on your network. FVS338 ProSafe VPN Firewall 50 Reference Manual • Port Forwarding with Auto Uplink With its own address as a DNS server to the attached PCs. The VPN firewall allows several networked PCs to one computer on your PC....are autosensing and capable of ports. • Exposed Host (Software DMZ). That port will automatically sense whether the Ethernet cable plugged into the port should have configured an inbound rule. The VPN firewall dynamically assigns network configuration information, including IP, gateway, and domain ...
FVS338 Reference Manual
Page 44
The LAN Setup screen will display. Figure 3-1 2. Enter the IP Address of your LAN setup: 1. FVS338 ProSafe VPN Firewall 50 Reference Manual To modify your router (factory default: 192.168.1.1). The IP address provided is the router's LAN IP address. (Always make sure that the LAN Port IP address and DMZ port IP address are in different subnets.) 3-2 LAN Configuration v1.0, March 2008 Select Network Configuration from the main menu and LAN Setup from the submenu.
The LAN Setup screen will display. Figure 3-1 2. Enter the IP Address of your LAN setup: 1. FVS338 ProSafe VPN Firewall 50 Reference Manual To modify your router (factory default: 192.168.1.1). The IP address provided is the router's LAN IP address. (Always make sure that the LAN Port IP address and DMZ port IP address are in different subnets.) 3-2 LAN Configuration v1.0, March 2008 Select Network Configuration from the main menu and LAN Setup from the submenu.
FVS338 Reference Manual
Page 48
...by this router. Collectively, these entries make up the Network Database. Every computer that are assigned dynamic IP addresses by the DHCP Server will accept and respond to DHCP client requests from the database, either IP address or MAC addresses. FVS338 ProSafe VPN Firewall 50 Reference ...Manual Warning: Make sure the secondary IP addresses are not DHCP clients. Example: WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0 WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0 DMZ IP address: 192.168.10.1 with...
...by this router. Collectively, these entries make up the Network Database. Every computer that are assigned dynamic IP addresses by the DHCP Server will accept and respond to DHCP client requests from the database, either IP address or MAC addresses. FVS338 ProSafe VPN Firewall 50 Reference ...Manual Warning: Make sure the secondary IP addresses are not DHCP clients. Example: WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0 WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0 DMZ IP address: 192.168.10.1 with...
FVS338 Reference Manual
Page 87
... connections using the class expire. Example: When a new connection is established by a device, the device will locate the firewall rule corresponding to the DMZ interface. The source IP is deleted when all WAN modes. Figure 4-20 The Bandwidth Profile table lists the currently defined...to the following connections. • If the rule has a bandwidth profile specification, then the device will share the same class. FVS338 ProSafe VPN Firewall 50 Reference Manual • Bandwidth limiting for outbound traffic is done on the available WAN interface in the case of an individual type ...
... connections using the class expire. Example: When a new connection is established by a device, the device will locate the firewall rule corresponding to the DMZ interface. The source IP is deleted when all WAN modes. Figure 4-20 The Bandwidth Profile table lists the currently defined...to the following connections. • If the rule has a bandwidth profile specification, then the device will share the same class. FVS338 ProSafe VPN Firewall 50 Reference Manual • Bandwidth limiting for outbound traffic is done on the available WAN interface in the case of an individual type ...
FVS338 Reference Manual
Page 92
... of the initiating device, and whether it 's on the LAN, WAN or DMZ. Although setting firewall rules (see "Setting a Schedule to manage distant sites from the LAN, WAN or DMZ. Block sites (see "Managing Groups and Hosts" on page 4-1) is the...- Services (see "Enabling Remote Management Access" on page 4-28) 4-36 Firewall Protection and Content Filtering v1.0, March 2008 Source MAC filtering (see "Setting Up Port Triggering" on page 6-9). 2. FVS338 ProSafe VPN Firewall 50 Reference Manual Table 4-3. Log Entry Descriptions Field Date and Time Description or Action...
... of the initiating device, and whether it 's on the LAN, WAN or DMZ. Although setting firewall rules (see "Setting a Schedule to manage distant sites from the LAN, WAN or DMZ. Block sites (see "Managing Groups and Hosts" on page 4-1) is the...- Services (see "Enabling Remote Management Access" on page 4-28) 4-36 Firewall Protection and Content Filtering v1.0, March 2008 Source MAC filtering (see "Setting Up Port Triggering" on page 6-9). 2. FVS338 ProSafe VPN Firewall 50 Reference Manual Table 4-3. Log Entry Descriptions Field Date and Time Description or Action...
FVS338 Reference Manual
Page 136
...blocking. • Web Component Blocking - FVS338 ProSafe VPN Firewall 50 Reference Manual You can bypass keyword blocking for trusted domains by PCs even in the groups for which keyword blocking has been enabled will cause serious problems. 6-4 Router and Network Management v1.0, March 2008 ... as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of Service) attacks. VPN Firewall Features That Increase Traffic Features that are still subject to use it (i.e.,...
...blocking. • Web Component Blocking - FVS338 ProSafe VPN Firewall 50 Reference Manual You can bypass keyword blocking for trusted domains by PCs even in the groups for which keyword blocking has been enabled will cause serious problems. 6-4 Router and Network Management v1.0, March 2008 ... as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of Service) attacks. VPN Firewall Features That Increase Traffic Features that are still subject to use it (i.e.,...
FVS338 Reference Manual
Page 137
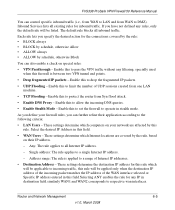
...range: The rule is between two VPN tunnel end points. • Drop fragmented IP packets - These settings determine which computers on your firewall rules, you specify the desired action for inbound traffic. Router and Network Management 6-5 v1.0, March 2008 FVS338 ProSafe VPN Firewall 50 Reference Manual You can control specific... locations are affected by this to protect the router from Syn flood attack. • Enable DNS Proxy - Enable this to allow the incoming DNS queries. • Enable Stealth Mode - Enable this to DMZ). Enable this rule. As you define your network...
...range: The rule is between two VPN tunnel end points. • Drop fragmented IP packets - These settings determine which computers on your firewall rules, you specify the desired action for inbound traffic. Router and Network Management 6-5 v1.0, March 2008 FVS338 ProSafe VPN Firewall 50 Reference Manual You can control specific... locations are affected by this to protect the router from Syn flood attack. • Enable DNS Proxy - Enable this to allow the incoming DNS queries. • Enable Stealth Mode - Enable this to DMZ). Enable this rule. As you define your network...
FVS338 Reference Manual
Page 169
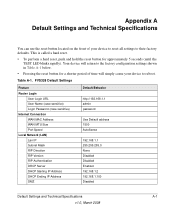
Table A-1. FVS338 Default Settings Feature Router Login User Login URL User Name (case sensitive) Login Password (case sensitive) Internet Connection WAN MAC Address WAN MTU Size Port Speed Local Network (LAN) Lan IP Subnet Mask RIP Direction RIP Version RIP Authentication DHCP Server DHCP Starting IP Address DHCP Ending IP Address DMZ Default Behavior...
Table A-1. FVS338 Default Settings Feature Router Login User Login URL User Name (case sensitive) Login Password (case sensitive) Internet Connection WAN MAC Address WAN MTU Size Port Speed Local Network (LAN) Lan IP Subnet Mask RIP Direction RIP Version RIP Authentication DHCP Server DHCP Starting IP Address DHCP Ending IP Address DMZ Default Behavior...
FVS338 Reference Manual
Page 187
FVS338 ProSafe VPN Firewall 50 Reference Manual LAN to WAN Logs Table B-21. None DMZ to WAN Logs Table B-19. None WAN to DMZ Logs Table B-20. None System Logs and Error Messages v1.0, March 2008 B-15 None LAN to LAN Logs Table B-22. Routing Logs: LAN to WAN ....99 PROTO=ICMP TYPE=8 CODE=0 • This packet from DMZ to WAN has been dropped by the firewall. • For other parameters, refer to Table B-1. Routing Logs: DMZ to WAN Message Explanation Recommended Action Nov 29 09:19:43 [FVS338] [kernel] DMZ2WAN[DROP] IN=DMZ OUT=WAN SRC=192.168.20.10 DST=72.14...
FVS338 ProSafe VPN Firewall 50 Reference Manual LAN to WAN Logs Table B-21. None DMZ to WAN Logs Table B-19. None WAN to DMZ Logs Table B-20. None System Logs and Error Messages v1.0, March 2008 B-15 None LAN to LAN Logs Table B-22. Routing Logs: LAN to WAN ....99 PROTO=ICMP TYPE=8 CODE=0 • This packet from DMZ to WAN has been dropped by the firewall. • For other parameters, refer to Table B-1. Routing Logs: DMZ to WAN Message Explanation Recommended Action Nov 29 09:19:43 [FVS338] [kernel] DMZ2WAN[DROP] IN=DMZ OUT=WAN SRC=192.168.20.10 DST=72.14...
FVS338 Reference Manual
Page 188
....10 PROTO=ICMP TYPE=8 CODE=0 • This packet from DMZ to LAN has been dropped by the firewall. • For other parameters, refer to Table B-1. FVS338 ProSafe VPN Firewall 50 Reference Manual DMZ to DMZ Logs Table B-24. None B-16 v1.0, March 2008 System Logs and Error Messages Routing Logs: DMZ to WAN Message Explanation Recommended Action Nov 29 09...
....10 PROTO=ICMP TYPE=8 CODE=0 • This packet from DMZ to LAN has been dropped by the firewall. • For other parameters, refer to Table B-1. FVS338 ProSafe VPN Firewall 50 Reference Manual DMZ to DMZ Logs Table B-24. None B-16 v1.0, March 2008 System Logs and Error Messages Routing Logs: DMZ to WAN Message Explanation Recommended Action Nov 29 09...