User Guide
Page 5
Wireless-G ADSL Gateway List of Figures Figure 2-1: Network 4 Figure 2-2: VPN Gateway-to-VPN Gateway 7 Figure 2-3: Computer-to-VPN Gateway 8 Figure 3-1: Back Panel 9 Figure 3-2: Front Panel 10 Figure 4-1: LAN Connection 12 Figure 4-2: ADSL Connection 12 Figure 4-3: Power Connection 12 Figure 5-1: Password Screen 16 Figure ...WEP Encryption 24 Figure 5-15: Wireless Network Access 25 Figure 5-16: Networked Computers 25 Figure 5-17: Advanced Wireless Settings 26 Figure 5-18: Firewall 27 Figure 5-19: VPN 28 Figure 5-20: Manual Key Management 29 Figure 5-21: Advanced ...
Wireless-G ADSL Gateway List of Figures Figure 2-1: Network 4 Figure 2-2: VPN Gateway-to-VPN Gateway 7 Figure 2-3: Computer-to-VPN Gateway 8 Figure 3-1: Back Panel 9 Figure 3-2: Front Panel 10 Figure 4-1: LAN Connection 12 Figure 4-2: ADSL Connection 12 Figure 4-3: Power Connection 12 Figure 5-1: Password Screen 16 Figure ...WEP Encryption 24 Figure 5-15: Wireless Network Access 25 Figure 5-16: Networked Computers 25 Figure 5-17: Advanced Wireless Settings 26 Figure 5-18: Firewall 27 Figure 5-19: VPN 28 Figure 5-20: Manual Key Management 29 Figure 5-21: Advanced ...
User Guide
Page 6
Wireless-G ADSL Gateway Figure 5-23: Internet Policy Summary 32 Figure 5-24: List of PCs 33 Figure 5-25: Port Services 33 Figure 5-26: Single Port Forwarding 34 Figure 5-27: Port Range Forwarding 35 Figure 5-28: Port Triggering 35 Figure 5-29: DMZ 36 Figure 5-30: Management 37 Figure 5-31: Reporting 39 Figure 5-32: Ping Test 40 Figure...
Wireless-G ADSL Gateway Figure 5-23: Internet Policy Summary 32 Figure 5-24: List of PCs 33 Figure 5-25: Port Services 33 Figure 5-26: Single Port Forwarding 34 Figure 5-27: Port Range Forwarding 35 Figure 5-28: Port Triggering 35 Figure 5-29: DMZ 36 Figure 5-30: Management 37 Figure 5-31: Reporting 39 Figure 5-32: Ping Test 40 Figure...
User Guide
Page 13
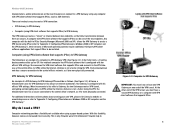
... that supports IPSec. 6 His Gateway is not a factor. Firewalls help to Chapter 2: Planning your own VPN, please visit Linksys's website at www.linksys.com or refer to the central... telecommuter uses his VPN Gateway for his office's VPN settings. With this flexibility, however, comes an increased risk in IPSec Security Manager (Microsoft 2000 and XP ) allows the VPN Gateway to create a VPN ...his always-on Internet connection. Wireless-G ADSL Gateway telecommuters, and/or professionals on the road (travelers can be one end of a VPN Gateway-to-VPN Gateway VPN would be installed. Any...
... that supports IPSec. 6 His Gateway is not a factor. Firewalls help to Chapter 2: Planning your own VPN, please visit Linksys's website at www.linksys.com or refer to the central... telecommuter uses his VPN Gateway for his office's VPN settings. With this flexibility, however, comes an increased risk in IPSec Security Manager (Microsoft 2000 and XP ) allows the VPN Gateway to create a VPN ...his always-on Internet connection. Wireless-G ADSL Gateway telecommuters, and/or professionals on the road (travelers can be one end of a VPN Gateway-to-VPN Gateway VPN would be installed. Any...
User Guide
Page 20
...Management tab. To secure the Gateway, change the password through use the following screens of the main tabs. Additional tabs will describe each web page in this screen. • DDNS. computers communicate over the network with this screen. • Advanced Routing. Enter the Internet connection and network settings on TCP/IP. Wireless-G ADSL Gateway... Chapter 5: Configuring the Gateway Overview Follow the steps in the Utility and each page's key functions. You can access the ...
...Management tab. To secure the Gateway, change the password through use the following screens of the main tabs. Additional tabs will describe each web page in this screen. • DDNS. computers communicate over the network with this screen. • Advanced Routing. Enter the Internet connection and network settings on TCP/IP. Wireless-G ADSL Gateway... Chapter 5: Configuring the Gateway Overview Follow the steps in the Utility and each page's key functions. You can access the ...
User Guide
Page 21
...be exposed to the Internet for Internet applications, click this tab. • DMZ. Status • Gateway. This screen provides status information about the wireless network. • DSL Connection. Wireless-G ADSL Gateway • VPN. This screen allows you want to your network, click this screen. Applications & ... this screen to view or save activity logs, click this screen. Use this screen. • Firmware Upgrade. Administration • Management. On this tab if you want to set up public services or other specialized Internet applications on your network. • Port ...
...be exposed to the Internet for Internet applications, click this tab. • DMZ. Status • Gateway. This screen provides status information about the wireless network. • DSL Connection. Wireless-G ADSL Gateway • VPN. This screen allows you want to your network, click this screen. Applications & ... this screen to view or save activity logs, click this screen. Use this screen. • Firmware Upgrade. Administration • Management. On this tab if you want to set up public services or other specialized Internet applications on your network. • Port ...
User Guide
Page 35
... expire at the other end of the tunnel is the default) has been selected. • Authentication. Figure 5-20: Manual Key Management Chapter 5: Configuring the Gateway 28 The Security Tab Using Encryption also helps make your changes. In Figure 5-19, MD5 (the default) has been selected. &#... used by selecting Disable. Enter the number of encryption: DES or 3DES (3DES is recommended because it is shown. See Figure 5-20. Wireless-G ADSL Gateway • Encryption. You may choose to undo your connection more secure). Check the box next to PFS (Perfect Forward Secrecy) to last ...
... expire at the other end of the tunnel is the default) has been selected. • Authentication. Figure 5-20: Manual Key Management Chapter 5: Configuring the Gateway 28 The Security Tab Using Encryption also helps make your changes. In Figure 5-19, MD5 (the default) has been selected. &#... used by selecting Disable. Enter the number of encryption: DES or 3DES (3DES is recommended because it is shown. See Figure 5-20. Wireless-G ADSL Gateway • Encryption. You may choose to undo your connection more secure). Check the box next to PFS (Perfect Forward Secrecy) to last ...
User Guide
Page 43
... of your password to change the default password to one of the Gateway. • Get Community. Chapter 5: Configuring the Gateway The Administration Tab Figure 5-30: Management 36 Wireless-G ADSL Gateway The Administration Tab Management The Management screen, shown in Figure 5-30, allows you to configure the Gateway from somewhere else on the Internet. • Remote Administration. To ensure the...
... of your password to change the default password to one of the Gateway. • Get Community. Chapter 5: Configuring the Gateway The Administration Tab Figure 5-30: Management 36 Wireless-G ADSL Gateway The Administration Tab Management The Management screen, shown in Figure 5-30, allows you to configure the Gateway from somewhere else on the Internet. • Remote Administration. To ensure the...
User Guide
Page 57
...does not need to disable these steps to set to connect directly to http://192.168.1.1 or the IP address of the Gateway. If you have any proxy settings and that the data enters from does not have entered for forwarding. Click Enabled and ... Applications and Gaming => DMZ tab. Wireless-G ADSL Gateway 8. Click Start, Settings, and Control Panel. Access the Gateway's web-based utility by pressing the Reset button for a password when saving settings, then perform the following steps: 1. Enter the default username and password admin, and click the Administrations => Management tab. 2.
...does not need to disable these steps to set to connect directly to http://192.168.1.1 or the IP address of the Gateway. If you have any proxy settings and that the data enters from does not have entered for forwarding. Click Enabled and ... Applications and Gaming => DMZ tab. Wireless-G ADSL Gateway 8. Click Start, Settings, and Control Panel. Access the Gateway's web-based utility by pressing the Reset button for a password when saving settings, then perform the following steps: 1. Enter the default username and password admin, and click the Administrations => Management tab. 2.
User Guide
Page 63
... must make sure that the hardware complies with the 802.11g standard. What is ad-hoc mode? The 802.11g standard allows wireless networking hardware from a remote computer over a network. Wireless-G ADSL Gateway How can I check whether I run an application from different manufacturers to communicate with the access point of an access point. The... 802.11g functions: • CSMA/CA plus Acknowledge protocol • Multi-Channel Roaming • Automatic Rate Selection • RTS/CTS feature • Fragmentation • Power Management What is infrastructure mode?
... must make sure that the hardware complies with the 802.11g standard. What is ad-hoc mode? The 802.11g standard allows wireless networking hardware from a remote computer over a network. Wireless-G ADSL Gateway How can I check whether I run an application from different manufacturers to communicate with the access point of an access point. The... 802.11g functions: • CSMA/CA plus Acknowledge protocol • Multi-Channel Roaming • Automatic Rate Selection • RTS/CTS feature • Fragmentation • Power Management What is infrastructure mode?
User Guide
Page 79
... end of seconds you wish to save these may choose not to communicate) in the Select Tunnel Entry dropdown box. Select the Key Management. Check the box next to PFS (Perfect Forward Secrecy) to have to Disable authentication. 9. In the Key Lifetime field, you wish...(3DES is recommended because it blank for the last set of the local VPN Gateway in the Tunnel Name field. Appendix C: Configuring IPSec between a Windows 2000 or XP Computer and the Gateway How to last indefinitely. 10. Wireless-G ADSL Gateway Step 5: Create a Tunnel Through the Web-Based Utility 1. Press the Enter ...
... end of seconds you wish to save these may choose not to communicate) in the Select Tunnel Entry dropdown box. Select the Key Management. Check the box next to PFS (Perfect Forward Secrecy) to have to Disable authentication. 9. In the Key Lifetime field, you wish...(3DES is recommended because it blank for the last set of the local VPN Gateway in the Tunnel Name field. Appendix C: Configuring IPSec between a Windows 2000 or XP Computer and the Gateway How to last indefinitely. 10. Wireless-G ADSL Gateway Step 5: Create a Tunnel Through the Web-Based Utility 1. Press the Enter ...
User Guide
Page 84
...Cable Modem - A device that temporarily holds data to be worked on later when a device is ready to be accessed, managed, and updated. Domain - DSSS (Direct-Sequence Spread-Spectrum) - DTIM (Delivery Traffic Indication Message) - Database - The capability of ... names of data lost during transmission. A method of data that it to receive data. A protocol that its contents can increase wireless efficiency. Wireless-G ADSL Gateway Buffer - Daisy Chain - Used in a series, one device on broadband connection over a network. DDNS (Dynamic Domain Name System...
...Cable Modem - A device that temporarily holds data to be worked on later when a device is ready to be accessed, managed, and updated. Domain - DSSS (Direct-Sequence Spread-Spectrum) - DTIM (Delivery Traffic Indication Message) - Database - The capability of ... names of data lost during transmission. A method of data that it to receive data. A protocol that its contents can increase wireless efficiency. Wireless-G ADSL Gateway Buffer - Daisy Chain - Used in a series, one device on broadband connection over a network. DDNS (Dynamic Domain Name System...
User Guide
Page 87
... central point of the network. SNMP (Simple Network Management Protocol) - A widely used for making, breaking, or changing the connections in a network, so data can be tunneled through an IP network. Your wireless network's name. A VPN protocol that connects multiple networks...eight wires. Appendix F: Glossary 80 Wireless-G ADSL Gateway PPPoE (Point to -Point Tunneling Protocol) - PPTP (Point-to Point Protocol over Ethernet) - Preamble - An Ethernet connector that determines the size of connection for computers and other services. Router - The computer will wait for ...
... central point of the network. SNMP (Simple Network Management Protocol) - A widely used for making, breaking, or changing the connections in a network, so data can be tunneled through an IP network. Your wireless network's name. A VPN protocol that connects multiple networks...eight wires. Appendix F: Glossary 80 Wireless-G ADSL Gateway PPPoE (Point to -Point Tunneling Protocol) - PPTP (Point-to Point Protocol over Ethernet) - Preamble - An Ethernet connector that determines the size of connection for computers and other services. Router - The computer will wait for ...