HP ProtectTools Security Software,Version 6.0 User Guide
Page 14
... a second computer to have the necessary encryption keys to log in, Credential Manager presents the credentials automatically. Embedded Security for HP ProtectTools Embedded Security for HP ProtectTools provides the ability to select what web or network asset they can also encrypt the entire drive and e-mail. The... is an issue. Example 1: A Purchasing Agent for a large manufacturer makes most often used to restrict access to the data on the motherboard. The Purchasing Agent has decided to use the same password on the computer. The user can access any data on the PC that they...
... a second computer to have the necessary encryption keys to log in, Credential Manager presents the credentials automatically. Embedded Security for HP ProtectTools Embedded Security for HP ProtectTools provides the ability to select what web or network asset they can also encrypt the entire drive and e-mail. The... is an issue. Example 1: A Purchasing Agent for a large manufacturer makes most often used to restrict access to the data on the motherboard. The Purchasing Agent has decided to use the same password on the computer. The user can access any data on the PC that they...
HP ProtectTools Security Software,Version 6.0 User Guide
Page 15
... be copied or stolen. Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools can only be able to copy the data to a USB drive. Even though the USB ports are both bound to the original motherboard. The IT Manager uses Device Access Manager to ...enable access for some employees while blocking external access to shred deleted data, temporary files, browser activity, etc. File Sanitizer for HP ProtectTools File Sanitizer for HP ProtectTools is written over, it is...
... be copied or stolen. Device Access Manager for HP ProtectTools Device Access Manager for HP ProtectTools can only be able to copy the data to a USB drive. Even though the USB ports are both bound to the original motherboard. The IT Manager uses Device Access Manager to ...enable access for some employees while blocking external access to shred deleted data, temporary files, browser activity, etc. File Sanitizer for HP ProtectTools File Sanitizer for HP ProtectTools is written over, it is...
Safety and Regulatory Information
Page 28
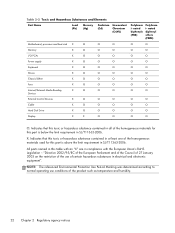
... with the European Union's RoHS Legislation - Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...
... with the European Union's RoHS Legislation - Table 2-2 Toxic and Hazardous Substances and Elements Part Name Lead (Pb) Mercury (Hg) Cadmium (Cd) Hexavalent Chromium (Cr(VI)) Motherboard, processor and heat sink X O O O Memory X O O O I/O PCAs X O O O Power supply X O O O Keyboard X O O O Mouse X O O O Chassis/Other X O O O Fans X O O O Internal/External Media Reading X O O O Devices External Control Devices X O O O Cable X O O O Hard Disk Drive...