User Manual
Page 6
...1. Check your Windows CD to the Network dialog box. If TCP/IP is in the same subnet with the Access Point. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Click the Start button and select Settings, then click Control Panel....installed, click the Add button to start installing the TCP/IP protocol. Your PC will now have the IP Address you to do not setup 192.168.2.1) 9 Subnet Mask: 255.255.255.0 8. In the Select Network Protocol dialog box, select Microsoft and TCP/IP and ...
...1. Check your Windows CD to the Network dialog box. If TCP/IP is in the same subnet with the Access Point. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Click the Start button and select Settings, then click Control Panel....installed, click the Add button to start installing the TCP/IP protocol. Your PC will now have the IP Address you to do not setup 192.168.2.1) 9 Subnet Mask: 255.255.255.0 8. In the Select Network Protocol dialog box, select Microsoft and TCP/IP and ...
User Manual
Page 8
... and Subnet mask as following example. 9 IP Address: 192.168.2.3 (any IP address within 192.168.2.2~192.168.2.254 is available, do not setup 192.168.2.1) 9 Subnet Mask: 255.255.255.0 6. Click OK to confirm the setting. Double-click Network icon. Check each of the tabs ... Network Protocols. Check your list. In the Select Network Protocol window, select the TCP/IP Protocol and click the Ok button to get into the Access Point's configuration page. Select TCP/IP from the Network window. 3. 1c) Windows 2000 1. Your PC will appear. 2. The Control Panel window will...
... and Subnet mask as following example. 9 IP Address: 192.168.2.3 (any IP address within 192.168.2.2~192.168.2.254 is available, do not setup 192.168.2.1) 9 Subnet Mask: 255.255.255.0 6. Click OK to confirm the setting. Double-click Network icon. Check each of the tabs ... Network Protocols. Check your list. In the Select Network Protocol window, select the TCP/IP Protocol and click the Ok button to get into the Access Point's configuration page. Select TCP/IP from the Network window. 3. 1c) Windows 2000 1. Your PC will appear. 2. The Control Panel window will...
User Manual
Page 15
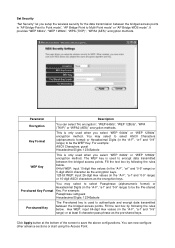
...-shared key is only used to authenticate and encrypt data transmitted between the bridged access points in the "A-F", "a-f" and "0-9" range) to encrypt data transmitted between the bridged access points. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used... method. Set Security "Set Security" let you setup the wireless security for the data transmission between the bridged access points. Parameter Description Encryption You can now configure other advance sections or start using the Access Point. The WEP key is only used to be ...
...-shared key is only used to authenticate and encrypt data transmitted between the bridged access points in the "A-F", "a-f" and "0-9" range) to encrypt data transmitted between the bridged access points. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used... method. Set Security "Set Security" let you setup the wireless security for the data transmission between the bridged access points. Parameter Description Encryption You can now configure other advance sections or start using the Access Point. The WEP key is only used to be ...
User Manual
Page 18
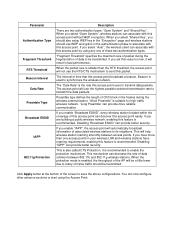
...of the AP will not use WEP encryption in bad performance. "Fragment Threshold" specifies the maximum size of this access point can associate with this access point without WEP encryption. "Long Preamble" can provide better security. It is the rate this packet. If you ...Preamble Type Broadcast ESSID IAPP 802.11g Protection Description There are building a public wireless network, enabling this access point by using the Access Point. When you should also setup WEP key in the "Encryption" page and wireless stations should be transmitted. When you select "Shared Key...
...of the AP will not use WEP encryption in bad performance. "Fragment Threshold" specifies the maximum size of this access point can associate with this access point without WEP encryption. "Long Preamble" can provide better security. It is the rate this packet. If you ...Preamble Type Broadcast ESSID IAPP 802.11g Protection Description There are building a public wireless network, enabling this access point by using the Access Point. When you should also setup WEP key in the "Encryption" page and wireless stations should be transmitted. When you select "Shared Key...