Product Manual
Page 2
Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only access...
Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only access...
Product Manual
Page 9
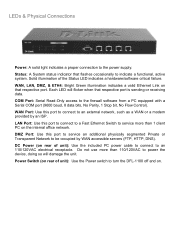
... an 110/120VAC electrical receptacle. WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on the internal office network. Solid illumination of unit): Use the included PC power cable to connect to turn the DFL-1100 off and on rear of the Status LED indicates a hardware/software critical failure. WAN Port...
... an 110/120VAC electrical receptacle. WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on the internal office network. Solid illumination of unit): Use the included PC power cable to connect to turn the DFL-1100 off and on rear of the Status LED indicates a hardware/software critical failure. WAN Port...
Product Manual
Page 10
System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with JavaScript enabled. 10
System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with JavaScript enabled. 10
Product Manual
Page 11
...DHCP connected to the LAN port in order to complete the Configuration Wizard. After the reset procedure has been carried out the DFL-1100 will revert to the previous configuration. In order to make the changes permanent, the administrator must do so through the Web...clicking on the Activate Changes button on the Activate Configuration Changes page. Resetting the DFL-1100 To reset the DFL-1100 to factory default settings you must login again. The firewall will appear. Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to...
...DHCP connected to the LAN port in order to complete the Configuration Wizard. After the reset procedure has been carried out the DFL-1100 will revert to the previous configuration. In order to make the changes permanent, the administrator must do so through the Web...clicking on the Activate Changes button on the Activate Configuration Changes page. Resetting the DFL-1100 To reset the DFL-1100 to factory default settings you must login again. The firewall will appear. Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to...
Product Manual
Page 25
... to your existing firewall. What High Availability will NOT do for you Adding redundancy to the inactive firewall. Redundancy for you D-Link High Availability will assume a passive role, monitoring the now active firewall. When the other will not create a load-sharing cluster... the failover procedure as a slight burst of communicating "state" to be inactive. Clients connecting through the firewall will only work between two D-Link DFL-1100 Firewalls. Only two firewalls, a "master" and a "slave", are also issues that the state of failure in a cluster. When the...
... to your existing firewall. What High Availability will NOT do for you Adding redundancy to the inactive firewall. Redundancy for you D-Link High Availability will assume a passive role, monitoring the now active firewall. When the other will not create a load-sharing cluster... the failover procedure as a slight burst of communicating "state" to be inactive. Clients connecting through the firewall will only work between two D-Link DFL-1100 Firewalls. Only two firewalls, a "master" and a "slave", are also issues that the state of failure in a cluster. When the...
Product Manual
Page 27
Link-level multicasts were chosen over normal unicast packets for this purpose when the firewalls are configured as HA. Since it is assumed that the packet ... TTL is the Ethernet multicast address corresponding to the shared hardware address, i.e. 11-00-00-C1-4A-nn. the fourth port is dedicated solely for security reasons: using the synchronization connection. The configuration is also transferred between the nodes using unicast packets would have the following characteristics: • The source IP...
Link-level multicasts were chosen over normal unicast packets for this purpose when the firewalls are configured as HA. Since it is assumed that the packet ... TTL is the Ethernet multicast address corresponding to the shared hardware address, i.e. 11-00-00-C1-4A-nn. the fourth port is dedicated solely for security reasons: using the synchronization connection. The configuration is also transferred between the nodes using unicast packets would have the following characteristics: • The source IP...
Product Manual
Page 30
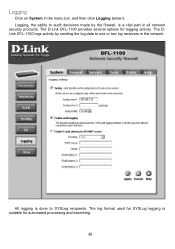
The D-Link DFL-1100 provides several options for automated processing and searching. 30 Logging Click on System in the network. Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for SYSLog logging is a vital part in all network security products. The DLink DFL-1100 logs activity by the firewall, is suitable for logging activity. All logging is done to one or two log receivers in the menu bar, and then click Logging below it.
The D-Link DFL-1100 provides several options for automated processing and searching. 30 Logging Click on System in the network. Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for SYSLog logging is a vital part in all network security products. The DLink DFL-1100 logs activity by the firewall, is suitable for logging activity. All logging is done to one or two log receivers in the menu bar, and then click Logging below it.
Product Manual
Page 31
...have to fill in your first SYSLog server as startup and shutdown, are configurable. Step 1. Follow these steps to enable logging. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Enable Logging Follow these steps to work. Step 2. Specify what facility to...Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel to which the DFL-1100 will always generate log entries. Step 1. Enable SYSLog by checking the SYSLog box. Enable E-mail alerting for instance when allowed ...
...have to fill in your first SYSLog server as startup and shutdown, are configurable. Step 1. Follow these steps to enable logging. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Enable Logging Follow these steps to work. Step 2. Specify what facility to...Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel to which the DFL-1100 will always generate log entries. Step 1. Enable SYSLog by checking the SYSLog box. Enable E-mail alerting for instance when allowed ...
Product Manual
Page 36
...work . 36 It's very important to know that if you can traffic using limit; D-Link updates the attack database periodically. Inspection Only will only inspect the traffic, and if the DFL-1100 detects anything it to work if the traffic limits for network traffic control in essence, we...by dropping the traffic. There are configured correctly. Traffic Shaping The simplest way to obtain quality of service in a network, seen from a security as well as policy based routing, is, simply put, an extension of what fields of suspicious network activity. much the same way firewall ...
...work . 36 It's very important to know that if you can traffic using limit; D-Link updates the attack database periodically. Inspection Only will only inspect the traffic, and if the DFL-1100 detects anything it to work if the traffic limits for network traffic control in essence, we...by dropping the traffic. There are configured correctly. Traffic Shaping The simplest way to obtain quality of service in a network, seen from a security as well as policy based routing, is, simply put, an extension of what fields of suspicious network activity. much the same way firewall ...
Product Manual
Page 37
... to be used mainly as if it was just another router. Fill in the IP header and then pass the packet on the Add new link. Choose Deny to the given gateway as a rule reference in log data and for any authenticated user. The first one, Redirect via routing (make a custom...
... to be used mainly as if it was just another router. Fill in the IP header and then pass the packet on the Add new link. Choose Deny to the given gateway as a rule reference in log data and for any authenticated user. The first one, Redirect via routing (make a custom...
Product Manual
Page 38
Delete policy Follow these steps to configure IDS on a policy. Click on the Edit link corresponding to the rule you want to configure. Click on the Edit link corresponding to the rule you want to discard changes. 38 Step 2. Click the Apply button below to apply the changes or ...available policy lists. Enable the Delete policy checkbox. Step 4. Click on . Choose the policy you would like to have IDS on the Edit link corresponding to the rule you would like do delete the policy in the Position to delete a policy. Enable the alerting checkbox for which you ...
Delete policy Follow these steps to configure IDS on a policy. Click on the Edit link corresponding to the rule you want to configure. Click on the Edit link corresponding to the rule you want to discard changes. 38 Step 2. Click the Apply button below to apply the changes or ...available policy lists. Enable the Delete policy checkbox. Step 4. Click on . Choose the policy you would like to have IDS on the Edit link corresponding to the rule you would like do delete the policy in the Position to delete a policy. Enable the alerting checkbox for which you ...
Product Manual
Page 39
Enable the alerting checkbox for e-mail alerting. Step 2. Step 4. Step 3. Step 1. Step 5. Configure Intrusion Prevention Follow these steps to configure IDP on . Click on the Edit link corresponding to the rule you would like have IDP on a policy. Click the Apply button below to apply the changes or click Cancel to configure. Choose Prevention from the mode drop down list. Choose the policy you want to discard changes. Enable the Intrusion Detection / Prevention checkbox.
Enable the alerting checkbox for e-mail alerting. Step 2. Step 4. Step 3. Step 1. Step 5. Configure Intrusion Prevention Follow these steps to configure IDP on . Click on the Edit link corresponding to the rule you would like have IDP on a policy. Click the Apply button below to apply the changes or click Cancel to configure. Choose Prevention from the mode drop down list. Choose the policy you want to discard changes. Enable the Intrusion Detection / Prevention checkbox.
Product Manual
Page 40
... IP: Leave empty to use Intrusion Detection / Prevention on the LAN or DMZ Interfaces to be passed to add a new mapping on the Add new link. Either make a custom service. If it is left blank there is carried out. Click on the WAN interface. If using Traffic shaping, fill in the...
... IP: Leave empty to use Intrusion Detection / Prevention on the LAN or DMZ Interfaces to be passed to add a new mapping on the Add new link. Either make a custom service. If it is left blank there is carried out. Click on the WAN interface. If using Traffic shaping, fill in the...
Product Manual
Page 41
Delete mapping Follow these steps to discard changes. Click on the Edit link corresponding to delete. Step 3. Step 1. Choose the mapping list (WAN, LAN, or DMZ) you want to the rule you would like do delete the mapping from. Click the Apply button below to apply the changes or click Cancel to delete a mapping. Step 2. Enable the Delete mapping checkbox.
Delete mapping Follow these steps to discard changes. Click on the Edit link corresponding to delete. Step 3. Step 1. Choose the mapping list (WAN, LAN, or DMZ) you want to the rule you would like do delete the mapping from. Click the Apply button below to apply the changes or click Cancel to delete a mapping. Step 2. Enable the Delete mapping checkbox.
Product Manual
Page 55
...Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-1100 only supports IP) • Data encapsulation to -point links. To establish a PPP tunnel, both sides send LCP frames to provide IP security at least one of the peers has to encapsulate IP packets for transport... between two peers. During the LCP and NCP negotiation optional parameters such as encryption, can be sent over the link. Introduction to L2TP L2TP, Layer 2 ...
...Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-1100 only supports IP) • Data encapsulation to -point links. To establish a PPP tunnel, both sides send LCP frames to provide IP security at least one of the peers has to encapsulate IP packets for transport... between two peers. During the LCP and NCP negotiation optional parameters such as encryption, can be sent over the link. Introduction to L2TP L2TP, Layer 2 ...
Product Manual
Page 56
PAP is more secure then MS-CHAP v1 as it provides two-way authentication. CHAP CHAP (Challenge Handshake Authentication Protocol) is a challenge-response authentication protocol specified in that both user name and password are sent over the link. This does however mean that with MS-CHAP v1. the main ... encryption scheme to hash the response to PAP in RFC 1994. Instead the password is used is superior to a challenge issued by the DFL-1100. Another difference is not backwards compatible with MS-CHAP v1 the password only needs to be stored as opposed to MD5 used to encrypt ...
PAP is more secure then MS-CHAP v1 as it provides two-way authentication. CHAP CHAP (Challenge Handshake Authentication Protocol) is a challenge-response authentication protocol specified in that both user name and password are sent over the link. This does however mean that with MS-CHAP v1. the main ... encryption scheme to hash the response to PAP in RFC 1994. Instead the password is used is superior to a challenge issued by the DFL-1100. Another difference is not backwards compatible with MS-CHAP v1 the password only needs to be stored as opposed to MD5 used to encrypt ...
Product Manual
Page 57
..., you most likely will be initiated when needed. Specify the username for data encryption. If disabled the tunnel will only be sent over the PPP link unencrypted. Specify which authentication protocol to be using IPSec instead of MPPE for this PPTP/L2TP Client tunnel. A selection of None means that data will...
..., you most likely will be initiated when needed. Specify the username for data encryption. If disabled the tunnel will only be sent over the PPP link unencrypted. Specify which authentication protocol to be using IPSec instead of MPPE for this PPTP/L2TP Client tunnel. A selection of None means that data will...
Product Manual
Page 58
... Pool and settings - Client IP Pool - Refer to NetBIOS names. A selection of None means that the PPTP/L2TP Server will be sent over the PPP link unencrypted. IP of encryption key (MPPE is to use IPSec enable the checkbox and select PSK or Certificate. 58 Authentication protocol - Require IPSec encryption - Leave...
... Pool and settings - Client IP Pool - Refer to NetBIOS names. A selection of None means that the PPTP/L2TP Server will be sent over the PPP link unencrypted. IP of encryption key (MPPE is to use IPSec enable the checkbox and select PSK or Certificate. 58 Authentication protocol - Require IPSec encryption - Leave...
Product Manual
Page 64
It links an identity to the trusted root CA. • Verify the signatures of all the local identity certificates that it should trust. These types of certificates ... key in the Certificates field on the other entities. When using pre-shared keys, this is the certificate used by the Web interface to the DFL-1100. Note: The certificate named Admin can either be selected in VPN tunnels. It cannot be selected in the certification path. • Fetch the CRL for...
It links an identity to the trusted root CA. • Verify the signatures of all the local identity certificates that it should trust. These types of certificates ... key in the Certificates field on the other entities. When using pre-shared keys, this is the certificate used by the Web interface to the DFL-1100. Note: The certificate named Admin can either be selected in VPN tunnels. It cannot be selected in the certification path. • Fetch the CRL for...
Product Manual
Page 76
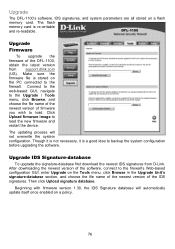
...re-writable and re-readable. Upgrade Firmware To upgrade the firmware of firmware you wish to load. Then click Upload signature database. Upgrade The DFL-1100's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall. Connect to the web-based GUI, navigate... card is a good idea to the Upgrade / Tools menu, click Browse, and choose the file name of the newest version of the DFL-1100, obtain the latest version from D-Link. After downloading the newest version of the software, connect to load the new firmware and restart the device.
...re-writable and re-readable. Upgrade Firmware To upgrade the firmware of firmware you wish to load. Then click Upload signature database. Upgrade The DFL-1100's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall. Connect to the web-based GUI, navigate... card is a good idea to the Upgrade / Tools menu, click Browse, and choose the file name of the newest version of the DFL-1100, obtain the latest version from D-Link. After downloading the newest version of the software, connect to load the new firmware and restart the device.