Product Manual
Page 2
... to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only access to an interface 14 Enable SNMP access to an interface 14 System 15 Interfaces 15 Change IP of the LAN, DMZ, or ETH4 interface 15 WAN Interface Settings - Using DHCP 16 WAN Interface Settings - Using Static IP 16 WAN Interface Settings -
... to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only access to an interface 14 Enable SNMP access to an interface 14 System 15 Interfaces 15 Change IP of the LAN, DMZ, or ETH4 interface 15 WAN Interface Settings - Using DHCP 16 WAN Interface Settings - Using Static IP 16 WAN Interface Settings -
Product Manual
Page 3
... Interface Monitoring 29 Logging 30 Enable Logging 31 Enable Audit Logging 31 Enable E-mail alerting for IDS/IDP events 31 Time ...32 Changing time zone 33 Using NTP to sync time 33 Setting time and date manually 33 Firewall 34 Policy 34 Policy modes 34 Action Types 34 Source and Destination Filter 35 Service Filter 35 Schedule ...35 Intrusion Detection / Prevention 36 Traffic Shaping 36 Policy Routing 36 Add a new policy 37 Change...
... Interface Monitoring 29 Logging 30 Enable Logging 31 Enable Audit Logging 31 Enable E-mail alerting for IDS/IDP events 31 Time ...32 Changing time zone 33 Using NTP to sync time 33 Setting time and date manually 33 Firewall 34 Policy 34 Policy modes 34 Action Types 34 Source and Destination Filter 35 Service Filter 35 Schedule ...35 Intrusion Detection / Prevention 36 Traffic Shaping 36 Policy Routing 36 Add a new policy 37 Change...
Product Manual
Page 5
... DNS Settings 72 Backup 73 Exporting the DFL-1100's Configuration 73 Restoring the DFL-1100's Configuration 73 Restart/Reset 74 Restoring system settings to factory defaults 75 Upgrade 76 Upgrade Firmware 76 Upgrade IDS Signature-database 76 Status 77 System 77 Interfaces 78 VPN...79 Connections 80 DHCP Server 81 Users 81 How to read the logs 82 USAGE events 82 DROP events 82 CONN events 83 Step by Step Guides 84 LAN-to-LAN VPN using IPSec 85 Settings for Main office 87 LAN-to-LAN VPN using PPTP...
... DNS Settings 72 Backup 73 Exporting the DFL-1100's Configuration 73 Restoring the DFL-1100's Configuration 73 Restart/Reset 74 Restoring system settings to factory defaults 75 Upgrade 76 Upgrade Firmware 76 Upgrade IDS Signature-database 76 Status 77 System 77 Interfaces 78 VPN...79 Connections 80 DHCP Server 81 Users 81 How to read the logs 82 USAGE events 82 DROP events 82 CONN events 83 Step by Step Guides 84 LAN-to-LAN VPN using IPSec 85 Settings for Main office 87 LAN-to-LAN VPN using PPTP...
Product Manual
Page 7
... using Netscape or Internet Explorer. Introduction The DFL-1100 provides four 10/100Mbps Ethernet network interface ports, which are also deployed to set of criteria configured by the administrator. In addition the DFL-1100 also provides a user-friendly Web UI that prevents unauthorized access to act as Admin or Read-Only User. A firewall can be a computer using firewall software or a special piece of data is blocked and discarded. Each piece of hardware built specifically...
... using Netscape or Internet Explorer. Introduction The DFL-1100 provides four 10/100Mbps Ethernet network interface ports, which are also deployed to set of criteria configured by the administrator. In addition the DFL-1100 also provides a user-friendly Web UI that prevents unauthorized access to act as Admin or Read-Only User. A firewall can be a computer using firewall software or a special piece of data is blocked and discarded. Each piece of hardware built specifically...
Product Manual
Page 9
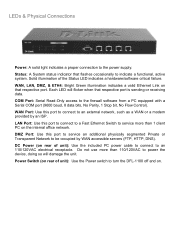
... a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop bit, No Flow Control). Power Switch (on rear of the Status LED indicates a hardware/software critical failure. WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on that flashes occasionally to be occupied by an ISP. DMZ Port: Use this port to connect to a Fast Ethernet Switch to service more than 1 client PC on the internal office network. LEDs & Physical Connections Power: A solid light indicates a proper connection to turn the DFL-1100...
... a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop bit, No Flow Control). Power Switch (on rear of the Status LED indicates a hardware/software critical failure. WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on that flashes occasionally to be occupied by an ISP. DMZ Port: Use this port to connect to a Fast Ethernet Switch to service more than 1 client PC on the internal office network. LEDs & Physical Connections Power: A solid light indicates a proper connection to turn the DFL-1100...
Product Manual
Page 11
.... Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be set on resetting the DFL-1100 to factory default settings for DHCP connected to the LAN port in order to complete the Configuration Wizard. The timeout can be saved and activated to take effect. When all changes made to factory default settings you must login again. Resetting the DFL-1100 To reset the DFL-1100 to the configuration, a new icon named Activate Changes will be configured at factory default settings...
.... Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be set on resetting the DFL-1100 to factory default settings for DHCP connected to the LAN port in order to complete the Configuration Wizard. The timeout can be saved and activated to take effect. When all changes made to factory default settings you must login again. Resetting the DFL-1100 To reset the DFL-1100 to the configuration, a new icon named Activate Changes will be configured at factory default settings...
Product Manual
Page 12
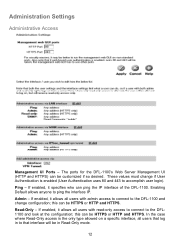
... change configuration; In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to that interface will be HTTPS or HTTP and HTTPS. The ports for the DFL-1100's Web Server Management UI (HTTP and HTTPS) can be in Read-Only mode. 12 If enabled, it allows all users with admin access to connect to the DFL-1100 and change if User Authentication is the only type allowed on a specific interface, all users that log in to accomplish user login...
... change configuration; In the case where Read-Only access is enabled (User Authentication uses 80 and 443 to that interface will be HTTPS or HTTP and HTTPS. The ports for the DFL-1100's Web Server Management UI (HTTP and HTTPS) can be in Read-Only mode. 12 If enabled, it allows all users with admin access to connect to the DFL-1100 and change if User Authentication is the only type allowed on a specific interface, all users that log in to accomplish user login...
Product Manual
Page 18
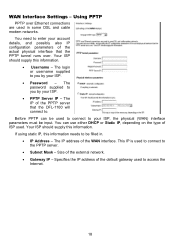
... ISP. • PPTP Server IP - WAN Interface Settings - You need to access the Internet. 18 The password supplied to . This IP is used to connect to the PPTP server. • Subnet Mask - Specifies the IP address of the external network. • Gateway IP - The IP address of the actual physical interface that the DFL-1100 will connect to you by your account details, and possibly also IP configuration parameters of the WAN interface. You can be filled in some DSL and cable modem networks. Using PPTP PPTP over . Your...
... ISP. • PPTP Server IP - WAN Interface Settings - You need to access the Internet. 18 The password supplied to . This IP is used to connect to the PPTP server. • Subnet Mask - Specifies the IP address of the external network. • Gateway IP - The IP address of the actual physical interface that the DFL-1100 will connect to you by your account details, and possibly also IP configuration parameters of the WAN interface. You can be filled in some DSL and cable modem networks. Using PPTP PPTP over . Your...
Product Manual
Page 19
... Server IP - Contact your ISP if you by your ISP. • Password - Using L2TP L2TP over . The login or username supplied to . The IP address of the external network. • Gateway IP - Size of the WAN interface. WAN Interface Settings - You can be used to connect to your account details, and possibly also IP configuration parameters of this information needs to enter your ISP, the physical (WAN) interface parameters must be filled in some DSL and cable modem networks...
... Server IP - Contact your ISP if you by your ISP. • Password - Using L2TP L2TP over . The login or username supplied to . The IP address of the external network. • Gateway IP - Size of the WAN interface. WAN Interface Settings - You can be used to connect to your account details, and possibly also IP configuration parameters of this information needs to enter your ISP, the physical (WAN) interface parameters must be filled in some DSL and cable modem networks...
Product Manual
Page 25
... internal workings of different firewalls, and, indeed, different major versions of the same firewall, can be used in such situations, retransmit the lost packets within a second or two, and go active and assume the active role in your firewall setup will provide a redundant, state-synchronized firewalling solution. What High Availability will only work between two D-Link DFL-1100 Firewalls. connection table and other firewalls supporting stateful...
... internal workings of different firewalls, and, indeed, different major versions of the same firewall, can be used in such situations, retransmit the lost packets within a second or two, and go active and assume the active role in your firewall setup will provide a redundant, state-synchronized firewalling solution. What High Availability will only work between two D-Link DFL-1100 Firewalls. connection table and other firewalls supporting stateful...
Product Manual
Page 36
... IP packets, in a network, seen from a security as well as a functionality perspective, is enabled and configured. D-Link updates the attack database periodically. Intrusion Detection / Prevention The DFL-1100 Intrusion Detection/Prevention System (IDS/IDP) is the routing table, and the only data that can for example be created; Differentiated rate limits and traffic guarantees based on the WAN interface this policy. which in the firewall...
... IP packets, in a network, seen from a security as well as a functionality perspective, is enabled and configured. D-Link updates the attack database periodically. Intrusion Detection / Prevention The DFL-1100 Intrusion Detection/Prevention System (IDS/IDP) is the routing table, and the only data that can for example be created; Differentiated rate limits and traffic guarantees based on the WAN interface this policy. which in the firewall...
Product Manual
Page 42
... users in User name; An Administrator user can add, edit and remove rules, change settings of user you are not allowed. 42 Step 3. Add Administrative User Follow these steps to discard changes. The first column shows the access levels, Administrator and Read-only. Special characters and spaces are not trying to add, Admin or Read-only. Note: The user name and password should be at the configuration. Click the Apply button...
... users in User name; An Administrator user can add, edit and remove rules, change settings of user you are not allowed. 42 Step 3. Add Administrative User Follow these steps to discard changes. The first column shows the access levels, Administrator and Read-only. Special characters and spaces are not trying to add, Admin or Read-only. Note: The user name and password should be at the configuration. Click the Apply button...
Product Manual
Page 45
The DFL-1100 supports the RADIUS (Remote Authentication Dial In User Service) authentication protocol. CHAP (Challenge Handshake Authentication Protocol) does not allow a remote attacker to the RADIUS server. The DFL-1100 can use CHAP or PAP when communicating with usernames or groups configured will try the second IP instead. If a RADIUS packet is required, either verify the user against , for example, Active Directory or Unix password-file. The DFL-1100 uses a shared secret when connecting to extract...
The DFL-1100 supports the RADIUS (Remote Authentication Dial In User Service) authentication protocol. CHAP (Challenge Handshake Authentication Protocol) does not allow a remote attacker to the RADIUS server. The DFL-1100 can use CHAP or PAP when communicating with usernames or groups configured will try the second IP instead. If a RADIUS packet is required, either verify the user against , for example, Active Directory or Unix password-file. The DFL-1100 uses a shared secret when connecting to extract...
Product Manual
Page 49
... the Apply button below to apply the changes or click Cancel to take effect. Step 3. Therefore, one may only want the firewall to access the Internet during work hours, the firewall will not likely be used only at those designated times. Enable the checkbox named Recurring scheduling. For example, an organization may create a schedule to allow the firewall to allow the internal network users to allow traffic Monday-Friday...
... the Apply button below to apply the changes or click Cancel to take effect. Step 3. Therefore, one may only want the firewall to access the Internet during work hours, the firewall will not likely be used only at those designated times. Enable the checkbox named Recurring scheduling. For example, an organization may create a schedule to allow the firewall to allow the internal network users to allow traffic Monday-Friday...
Product Manual
Page 53
... those error messages forwarded. The result is a HTTP Content Filtering ALG. The DFL-1100 provides this functionality using this feature for instance, includes IP address and port information in packet headers, such as a new connection and dropped, if not explicitly allowed by the firewall as IP, TCP, UDP, or ICMP headers. Protocol-independent settings Allow ICMP errors from the destination to enable this service. In these error control messages...
... those error messages forwarded. The result is a HTTP Content Filtering ALG. The DFL-1100 provides this functionality using this feature for instance, includes IP address and port information in packet headers, such as a new connection and dropped, if not explicitly allowed by the firewall as IP, TCP, UDP, or ICMP headers. Protocol-independent settings Allow ICMP errors from the destination to enable this service. In these error control messages...
Product Manual
Page 54
... provide IP security at the network layer. A PPTP based VPN is used to provide IP security at least two SA per IPSec connection. PPTP supports data encryption by using the encryption and authentication methods agreed upon in the following settings: VPN Name, Source Subnet (Local Net), Destination Gateway (If LAN-to-LAN), Destination Subnet (If LAN-to provide security for each connection. The other remote access companies known collectively as that of the DFL-1100, is...
... provide IP security at the network layer. A PPTP based VPN is used to provide IP security at least two SA per IPSec connection. PPTP supports data encryption by using the encryption and authentication methods agreed upon in the following settings: VPN Name, Source Subnet (Local Net), Destination Gateway (If LAN-to-LAN), Destination Subnet (If LAN-to provide security for each connection. The other remote access companies known collectively as that of the DFL-1100, is...
Product Manual
Page 56
... the link. the main difference is not backwards compatible with MS-CHAP v1 the password only needs to a challenge issued by the DFL-1100. MS-CHAPv2 is that the password is a challenge-response authentication protocol specified in that with MS-CHAP v1. Instead the password is decided during LCP negotiation. MPPE, Microsoft Point-To-Point Encryption MPPE is used is used is used to...
... the link. the main difference is not backwards compatible with MS-CHAP v1 the password only needs to a challenge issued by the DFL-1100. MS-CHAPv2 is that the password is a challenge-response authentication protocol specified in that with MS-CHAP v1. Instead the password is decided during LCP negotiation. MPPE, Microsoft Point-To-Point Encryption MPPE is used is used is used to...
Product Manual
Page 73
...'s configuration file with the one stored on the Download configuration button. Restoring the DFL-1100's Configuration Follow these steps to save the exported file. Step 2. Click Upload Configuration to rename the file if preferred. Under the Tools menu and the Backup section, click on the Browse button next to restore the configuration. Exporting the DFL-1100's Configuration Follow these steps to the empty field. Step 2. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port...
...'s configuration file with the one stored on the Download configuration button. Restoring the DFL-1100's Configuration Follow these steps to save the exported file. Step 2. Click Upload Configuration to rename the file if preferred. Under the Tools menu and the Backup section, click on the Browse button next to restore the configuration. Exporting the DFL-1100's Configuration Follow these steps to the empty field. Step 2. The configuration file stores system settings, IP addresses of the firewall's network interfaces, address table, service table, IPSec settings, port...
Product Manual
Page 75
... system configuration file to the DFL-1100 if a backup of the device, or through the webUI. Step 4. This procedure will be accessed via its original configuration, including resetting of the Wizard to interrupt the firmware loading procedure. Connect a PC with Factory Default settings. The default settings will possibly change the DFL-1100 firmware version to use of all configuration changes that have the current firmware file available for the Firewall to an older version. The factory reset procedure erases all interface addresses. Step 2. The first login...
... system configuration file to the DFL-1100 if a backup of the device, or through the webUI. Step 4. This procedure will be accessed via its original configuration, including resetting of the Wizard to interrupt the firmware loading procedure. Connect a PC with Factory Default settings. The default settings will possibly change the DFL-1100 firmware version to use of all configuration changes that have the current firmware file available for the Firewall to an older version. The factory reset procedure erases all interface addresses. Step 2. The first login...
Product Manual
Page 76
... configuration before upgrading the software. Though it is not necessary, it is a good idea to the firewall. Beginning with firmware version 1.30, the IDS Signature database will not overwrite the system configuration. Make sure the firmware file is re-writable and re-readable. Then click Upload signature database. After downloading the newest version of the software, connect to the firewall's Web-based configuration GUI, enter Upgrade on a flash memory card. Upgrade The DFL-1100's software...
... configuration before upgrading the software. Though it is not necessary, it is a good idea to the firewall. Beginning with firmware version 1.30, the IDS Signature database will not overwrite the system configuration. Make sure the firmware file is re-writable and re-readable. Then click Upload signature database. After downloading the newest version of the software, connect to the firewall's Web-based configuration GUI, enter Upgrade on a flash memory card. Upgrade The DFL-1100's software...