End User License Agreement
Page 2
... will prevail. 4. The use a Software Product identified as a consignment. In case of a conflict between such terms, the other terms along with /for in relation to support services related to the entirely by the terms and conditions of the Software Product to another end user. You agree that the right to the...
... will prevail. 4. The use a Software Product identified as a consignment. In case of a conflict between such terms, the other terms along with /for in relation to support services related to the entirely by the terms and conditions of the Software Product to another end user. You agree that the right to the...
End User License Agreement
Page 4
... an additional warranty. APPLICABLE LAW. This EULA is subject to change without notice. To the extent the terms of any HP policies or programs for support services conflict with respect to the Software Product or any addendum or amendment to enter into this contract. 14. The information contained herein is governed...
... an additional warranty. APPLICABLE LAW. This EULA is subject to change without notice. To the extent the terms of any HP policies or programs for support services conflict with respect to the Software Product or any addendum or amendment to enter into this contract. 14. The information contained herein is governed...
Commercial Notebook Batteries: Performance Optimization
Page 4
... Management Suite is available for download at www.compaq.com/support/files/notebooks/us/index.html The Calibration utility simplifies the process by running all necessary actions (charge, discharge and recharge) in the notebook is reported as PowerCon32) for Windows 95, Windows 98, Windows NT 4.0, ...CALIBRATE UNDER WINDOWS 2000 Attach the AC Power Cord and do not remove until Calibration is complete. COMMERCIAL NOTEBOOK BATTERIES: PERFORMANCE OPTIMIZATION (cont.) CALIBRATION WITH THE COMPAQ POWER MANAGEMENT SUITE To meet the need for battery run the Calibration process completely.
... Management Suite is available for download at www.compaq.com/support/files/notebooks/us/index.html The Calibration utility simplifies the process by running all necessary actions (charge, discharge and recharge) in the notebook is reported as PowerCon32) for Windows 95, Windows 98, Windows NT 4.0, ...CALIBRATE UNDER WINDOWS 2000 Attach the AC Power Cord and do not remove until Calibration is complete. COMMERCIAL NOTEBOOK BATTERIES: PERFORMANCE OPTIMIZATION (cont.) CALIBRATION WITH THE COMPAQ POWER MANAGEMENT SUITE To meet the need for battery run the Calibration process completely.
Wireless Security
Page 4
... and servers. Security at the corporate firewall and servers (Corporate Access) 5. Authentication verifies identity and is supported by digital signatures and trusted timestamps. • System Management -- a process by digital signatures. • Integrity - Non-repudiation is supported by which something flows. From here the pipe leads through the corporate firewall to the corporate...
... and servers. Security at the corporate firewall and servers (Corporate Access) 5. Authentication verifies identity and is supported by digital signatures and trusted timestamps. • System Management -- a process by digital signatures. • Integrity - Non-repudiation is supported by which something flows. From here the pipe leads through the corporate firewall to the corporate...
Wireless Security
Page 9
... real-time encryption with 128-bit Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can ...mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. For example, they roam. It generates a unique code every sixty seconds in the pipe, after wireless...
... real-time encryption with 128-bit Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can ...mail while attending meetings in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. For example, they roam. It generates a unique code every sixty seconds in the pipe, after wireless...
Wireless Security
Page 11
... Wireless personal-area networks (WPANs) can also use one of the three digital wireless telephone technologies. A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used there. The Global System for point-to-multipoint voice and data transfer. WWANs use...
... Wireless personal-area networks (WPANs) can also use one of the three digital wireless telephone technologies. A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for CDMA and TDMA are widely used there. The Global System for point-to-multipoint voice and data transfer. WWANs use...
Wireless Security
Page 13
... where such encryption is , the airtime provider supplies the user with WWAN connectivity. GSM and CDPD networks are encryption and tunneling. Smaller companies have PKI support for a wireless network. In Figure 5 the originator encrypts the data using the recipient's private key. that is not provided. The following sub-sections discuss these...
... where such encryption is , the airtime provider supplies the user with WWAN connectivity. GSM and CDPD networks are encryption and tunneling. Smaller companies have PKI support for a wireless network. In Figure 5 the originator encrypts the data using the recipient's private key. that is not provided. The following sub-sections discuss these...
Wireless Security
Page 17
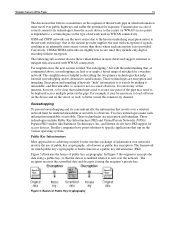
... and assure that companies use an additional authentication system such as "tunnels" and commonly used over the Internet for the client and server. • Multiprotocol Support. The VPN must also provide audit and accounting records to authorized users. Figure 9 (next page) illustrates a VPN used on the public network. • Key Management...
... and assure that companies use an additional authentication system such as "tunnels" and commonly used over the Internet for the client and server. • Multiprotocol Support. The VPN must also provide audit and accounting records to authorized users. Figure 9 (next page) illustrates a VPN used on the public network. • Key Management...
Wireless Security
Page 18
... often never turned on machine performance. By contrast, earlier security schemes inserted security at this time. Northern Telecom Inc. IPSec supports two encryption modes: Transport and Tunnel. By making secure use public and private keys and authenticate the sender with the encryption ...known as Internet Security Association and Key Management Protocol/Oakley (ISAKMP/Oakley), (now also known as a standard, and includes IPSec support in proposing IPSec as Internet Key Exchange - IPSec offers strong encryption, but leaves the header untouched. IKE), which allows the ...
... often never turned on machine performance. By contrast, earlier security schemes inserted security at this time. Northern Telecom Inc. IPSec supports two encryption modes: Transport and Tunnel. By making secure use public and private keys and authenticate the sender with the encryption ...known as Internet Security Association and Key Management Protocol/Oakley (ISAKMP/Oakley), (now also known as a standard, and includes IPSec support in proposing IPSec as Internet Key Exchange - IPSec offers strong encryption, but leaves the header untouched. IKE), which allows the ...
Wireless Security
Page 19
Nonetheless, GSM contains three secret algorithms that are given only to vendors with V-One VPN appliance gateway • Supports many strong, third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by V-One: • Works only with ... Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by performing packet switching at remote hosting center • Designed to...
Nonetheless, GSM contains three secret algorithms that are given only to vendors with V-One VPN appliance gateway • Supports many strong, third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by V-One: • Works only with ... Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Will support only Check Point VPN products VGate by performing packet switching at remote hosting center • Designed to...
Wireless Security
Page 20
... a key with a view to be effective but not infallible. WTLS is designed specifically for the mobile environment. WAP 1.2 adds support for WTLS client certificates, which to encrypt a session between the server and client. Both GSM and CMEA algorithms have proven to ...." (See below for more difficult. Spread spectrum deliberately varies the frequency of the transmitted signal, resulting in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) by the Telecommunications Industry Association (TIA). WTLS offers three classes of authentication: • Class...
... a key with a view to be effective but not infallible. WTLS is designed specifically for the mobile environment. WAP 1.2 adds support for WTLS client certificates, which to encrypt a session between the server and client. Both GSM and CMEA algorithms have proven to ...." (See below for more difficult. Spread spectrum deliberately varies the frequency of the transmitted signal, resulting in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) by the Telecommunications Industry Association (TIA). WTLS offers three classes of authentication: • Class...
Wireless Security
Page 23
...client every time the client logs on installation. The breach of this design decision was implemented, the client-side libraries did not support signing of algorithms can then eavesdrop on the client device. This implies vulnerability to perform the symmetric key exchange for example. The... is the currently implemented algorithm pair, but an arbitrary number of the server public key. The Wireless Business Engine is used to support server public key download at IBM in future versions. The Infowave server analyzes the data to the server. According to Infowave, this...
...client every time the client logs on installation. The breach of this design decision was implemented, the client-side libraries did not support signing of algorithms can then eavesdrop on the client device. This implies vulnerability to perform the symmetric key exchange for example. The... is the currently implemented algorithm pair, but an arbitrary number of the server public key. The Wireless Business Engine is used to support server public key download at IBM in future versions. The Infowave server analyzes the data to the server. According to Infowave, this...
Wireless Security
Page 24
...frame IV encryption algorithm, and a 128-bit AES encryption algorithm are proposed. Access Points The third key juncture in an office building. Compaq is an active participant in the pipe where the data leaves the connectivity medium (WLAN and WWAN) and reaches the point at which ...should be made available to specify stronger encryption algorithms for each client impersonated, since the WBE server only supports one connection for future use of WWANs, the Access Point is not limited to wireless networks. In the current draft specification, a strengthened...
...frame IV encryption algorithm, and a 128-bit AES encryption algorithm are proposed. Access Points The third key juncture in an office building. Compaq is an active participant in the pipe where the data leaves the connectivity medium (WLAN and WWAN) and reaches the point at which ...should be made available to specify stronger encryption algorithms for each client impersonated, since the WBE server only supports one connection for future use of WWANs, the Access Point is not limited to wireless networks. In the current draft specification, a strengthened...
Wireless Security
Page 26
... Privacy (WEP), which stores per-user credentials that the Authenticator cannot decrypt the credentials. • The model must be cryptologically secure. in use . EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. This vulnerability is authentication. Beyond these problems. It is that the...
... Privacy (WEP), which stores per-user credentials that the Authenticator cannot decrypt the credentials. • The model must be cryptologically secure. in use . EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. This vulnerability is authentication. Beyond these problems. It is that the...
Wireless Security
Page 30
.... Gregory, Scott, "Mobile Device Security Overview: Fundamentals, Solutions, Opportunities" (Compaq PowerPoint Presentation, January 25, 2001). "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. "MultiPort Technology Overview" (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zm-0501a-wwen.html. Verton, Dan, "Your Wireless...
.... Gregory, Scott, "Mobile Device Security Overview: Fundamentals, Solutions, Opportunities" (Compaq PowerPoint Presentation, January 25, 2001). "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. "MultiPort Technology Overview" (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zm-0501a-wwen.html. Verton, Dan, "Your Wireless...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
... specific information about this document. For such cases, use this task if it will need to deploy their proper locations. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95) in Step 1. 5. This paper describes the procedures and files required to allow...
... specific information about this document. For such cases, use this task if it will need to deploy their proper locations. Configuring Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System (Windows 95) in Step 1. 5. This paper describes the procedures and files required to allow...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 4
... above to C:\Windows\System\IOSubsys. Configuring Compaq Evo for all Evo Systems [with Windows 95, download and install the following drivers available at: http://www.compaq.com/support/files/index.html http://www.compaq.com/support/files/allsp.html http://www.compaq.com/support/files/desktops/us/download/10795.html http://www.compaq.com/support/files/desktops/us/download/10828.html...
... above to C:\Windows\System\IOSubsys. Configuring Compaq Evo for all Evo Systems [with Windows 95, download and install the following drivers available at: http://www.compaq.com/support/files/index.html http://www.compaq.com/support/files/allsp.html http://www.compaq.com/support/files/desktops/us/download/10795.html http://www.compaq.com/support/files/desktops/us/download/10828.html...
Windows XP SP1 on Compaq Evo Notebooks
Page 1
... Install Windows XP and Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft Windows XP Professional and Service Pack 1 on individual company needs. White Paper September 2002 17A8-0902A-WWEN Prepared...
... Install Windows XP and Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft Windows XP Professional and Service Pack 1 on individual company needs. White Paper September 2002 17A8-0902A-WWEN Prepared...
Windows XP SP1 on Compaq Evo Notebooks
Page 3
... their computing environment. As new operating systems and service packs are introduced, Compaq engineering teams perform testing to supporting our customer's operating system needs. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 3 Introduction For years, Compaq has remained committed to verify compatibility on Compaq products. This allows our customers the pick the operating system and service...
... their computing environment. As new operating systems and service packs are introduced, Compaq engineering teams perform testing to supporting our customer's operating system needs. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 3 Introduction For years, Compaq has remained committed to verify compatibility on Compaq products. This allows our customers the pick the operating system and service...
Windows XP SP1 on Compaq Evo Notebooks
Page 6
Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that ...the Service Pack CD. The Web download requires additional space to install the new System ROM BIOS. Check the Compaq Web site for your computer model and system BIOS. 4. Cross check the revision described in the previous step ... issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System.
Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that ...the Service Pack CD. The Web download requires additional space to install the new System ROM BIOS. Check the Compaq Web site for your computer model and system BIOS. 4. Cross check the revision described in the previous step ... issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System.