Configuration Guide
Page 4
Contents Configuring Enhanced IGRP 14 Configuration Example 15 Verifying Your Configuration 15 2 P A R T Configuring Your Router for Ethernet and DSL Access 2 C H A P T E R Sample Network Deployments 1 3 C H A P T E R Configuring PPP over Ethernet with NAT 1 Configure ... Example 4 Verify Your DHCP Configuration 4 Configure VLANs 5 Assign a Switch Port to a VLAN 6 Verify Your VLAN Configuration 6 6 C H A P T E R Configuring a VPN Using Easy VPN and an IPSec Tunnel 1 Configure the IKE Policy 4 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 4 OL-5332-01
Contents Configuring Enhanced IGRP 14 Configuration Example 15 Verifying Your Configuration 15 2 P A R T Configuring Your Router for Ethernet and DSL Access 2 C H A P T E R Sample Network Deployments 1 3 C H A P T E R Configuring PPP over Ethernet with NAT 1 Configure ... Example 4 Verify Your DHCP Configuration 4 Configure VLANs 5 Assign a Switch Port to a VLAN 6 Verify Your VLAN Configuration 6 6 C H A P T E R Configuring a VPN Using Easy VPN and an IPSec Tunnel 1 Configure the IKE Policy 4 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 4 OL-5332-01
Configuration Guide
Page 5
...Parameters 8 Apply the Crypto Map to the Physical Interface 9 Create an Easy VPN Remote Configuration 10 Verifying Your Easy VPN Configuration 11 Configuration Example 11 Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation 1 Configure a VPN 2 Configure the IKE Policy 3 Configure Group Policy Information 4 Enable Policy ... Bridging on VLANs 4 Configure Radio Station Subinterfaces 6 Configuration Example 7 Sample Configuration 1 Configuring Additional Features and Troubleshooting OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 5
...Parameters 8 Apply the Crypto Map to the Physical Interface 9 Create an Easy VPN Remote Configuration 10 Verifying Your Easy VPN Configuration 11 Configuration Example 11 Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation 1 Configure a VPN 2 Configure the IKE Policy 3 Configure Group Policy Information 4 Enable Policy ... Bridging on VLANs 4 Configure Radio Station Subinterfaces 6 Configuration Example 7 Sample Configuration 1 Configuring Additional Features and Troubleshooting OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 5
Configuration Guide
Page 6
...T E R 14 C H A P T E R Additional Configuration Options 1 Configuring Security Features 1 Authentication, Authorization, and Accounting 1 Configuring AutoSecure 2 Configuring Access Lists 2 Access Groups 3 Guidelines for Creating Access Groups 3 Configuring a CBAC Firewall 3 Configuring Cisco IOS Firewall IDS 4 Configuring VPNs 4 Configuring Dial Backup and Remote Management 1 Dial Backup Feature Activation Methods 1 Backup Interfaces... the Aggregator and ISDN Peer Router 20 Troubleshooting 1 Getting Started 1 Before Contacting Cisco or Your Reseller 1 ADSL Troubleshooting 2 SHDSL Troubleshooting 2 ATM...
...T E R 14 C H A P T E R Additional Configuration Options 1 Configuring Security Features 1 Authentication, Authorization, and Accounting 1 Configuring AutoSecure 2 Configuring Access Lists 2 Access Groups 3 Guidelines for Creating Access Groups 3 Configuring a CBAC Firewall 3 Configuring Cisco IOS Firewall IDS 4 Configuring VPNs 4 Configuring Dial Backup and Remote Management 1 Dial Backup Feature Activation Methods 1 Backup Interfaces... the Aggregator and ISDN Peer Router 20 Troubleshooting 1 Getting Started 1 Before Contacting Cisco or Your Reseller 1 ADSL Troubleshooting 2 SHDSL Troubleshooting 2 ATM...
Configuration Guide
Page 11
...Cisco 857 DSL Access Router • Cisco 870 Series Routers - OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 11 Cisco 871 Ethernet Access Router - To obtain the SDM release notes and other features on your router. Cisco 876, Cisco 877, and Cisco 878 DSL Access Routers... the software using only the CLI. Cisco 851 Ethernet Access Router - You can use the Cisco Router and Security Device Manager (SDM)-a web-based configuration tool that network administrators with minimal familiarity with Cisco routers use this guide, and the text ...
...Cisco 857 DSL Access Router • Cisco 870 Series Routers - OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 11 Cisco 871 Ethernet Access Router - To obtain the SDM release notes and other features on your router. Cisco 876, Cisco 877, and Cisco 878 DSL Access Routers... the software using only the CLI. Cisco 851 Ethernet Access Router - You can use the Cisco Router and Security Device Manager (SDM)-a web-based configuration tool that network administrators with minimal familiarity with Cisco routers use this guide, and the text ...
Configuration Guide
Page 12
... Configuration Options"-Provides a road map for Part 3. • Chapter 12, "Configuring Security Features"-Explains basic configuration of Cisco IOS security features, including firewall and VPN configuration. • Chapter 13, "Configuring Dial Backup and Remote Management"-Provides instructions on how to configure your Cisco router for Part 2. • Chapter 3, "Configuring PPP over Ethernet with NAT"-Provides instructions...
... Configuration Options"-Provides a road map for Part 3. • Chapter 12, "Configuring Security Features"-Explains basic configuration of Cisco IOS security features, including firewall and VPN configuration. • Chapter 13, "Configuring Dial Backup and Remote Management"-Provides instructions on how to configure your Cisco router for Part 2. • Chapter 3, "Configuring PPP over Ethernet with NAT"-Provides instructions...
Configuration Guide
Page 35
... topology, a step-by configuring another key feature. The Cisco 851 and Cisco 871 router models can be used in the Ethernet-based scenarios and the Cisco 857, Cisco 876, Cisco 877, and Cisco 878 router models can pattern your router for DSL-based networks. • Chapter 4, "Configuring ...with NAT" • Chapter 5, "Configuring a LAN with DHCP and VLANs" • Chapter 6, "Configuring a VPN Using Easy VPN and an IPSec Tunnel" • Chapter 7, "Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation" • Chapter 8, "Configuring a Simple Firewall" For DSL-Based ...
... topology, a step-by configuring another key feature. The Cisco 851 and Cisco 871 router models can be used in the Ethernet-based scenarios and the Cisco 857, Cisco 876, Cisco 877, and Cisco 878 router models can pattern your router for DSL-based networks. • Chapter 4, "Configuring ...with NAT" • Chapter 5, "Configuring a LAN with DHCP and VLANs" • Chapter 6, "Configuring a VPN Using Easy VPN and an IPSec Tunnel" • Chapter 7, "Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation" • Chapter 8, "Configuring a Simple Firewall" For DSL-Based ...
Configuration Guide
Page 36
Chapter 2 Sample Network Deployments • Chapter 7, "Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation" • Chapter 8, "Configuring a Simple Firewall" Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 2-2 OL-5332-01
Chapter 2 Sample Network Deployments • Chapter 7, "Configuring VPNs Using an IPSec Tunnel and Generic Routing Encapsulation" • Chapter 8, "Configuring a Simple Firewall" Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 2-2 OL-5332-01
Configuration Guide
Page 67
... secure the connection between two particular endpoints. The example in this chapter does not apply to a corporate network. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-1 CH A P T E R 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel The Cisco 870 series routers support the creation of a remote access VPN that uses the Cisco Easy VPN...
... secure the connection between two particular endpoints. The example in this chapter does not apply to a corporate network. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-1 CH A P T E R 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel The Cisco 870 series routers support the creation of a remote access VPN that uses the Cisco Easy VPN...
Configuration Guide
Page 68
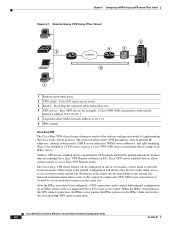
... split-tunneling flags, to access resources at the client site are running Cisco Easy VPN Remote software on an IPSec client, such as Easy VPN Remote nodes. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-2 OL-5332-01 for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 5 Corporate office with...
... split-tunneling flags, to access resources at the client site are running Cisco Easy VPN Remote software on an IPSec client, such as Easy VPN Remote nodes. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-2 OL-5332-01 for example, a Cisco VPN 3000 concentrator with outside interface address 210.110.101.1 5 Corporate office with...
Configuration Guide
Page 69
Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Note The Cisco Easy VPN client feature supports configuration of these configurations tasks, see Chapter 1, "Basic Router Configuration," Chapter 3, "Configuring PPP over Ethernet with NAT," Chapter 4, "Configuring PPP over ATM with NAT,"... shown in this chapter assume that you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on the Cisco 870 series router. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-3
Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Note The Cisco Easy VPN client feature supports configuration of these configurations tasks, see Chapter 1, "Basic Router Configuration," Chapter 3, "Configuring PPP over Ethernet with NAT," Chapter 4, "Configuring PPP over ATM with NAT,"... shown in this chapter assume that you must manually configure the IPSec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on the Cisco 870 series router. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-3
Configuration Guide
Page 70
...VPN Using Easy VPN and an IPSec Tunnel Configure the IKE Policy Perform these steps to configure the Internet Key Exchange (IKE) policy, beginning in the IKE policy. The priority is Secure Hash standard (SHA-1). authentication {rsa-sig | rsa-encr | pre-share} Example: Router...standard (DES). The example specifies the Message Digest 5 (MD5) algorithm. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-4 OL-5332-01 Also enters the Internet Security Association Key and Management Protocol (ISAKMP) policy configuration mode. The example ...
...VPN Using Easy VPN and an IPSec Tunnel Configure the IKE Policy Perform these steps to configure the Internet Key Exchange (IKE) policy, beginning in the IKE policy. The priority is Secure Hash standard (SHA-1). authentication {rsa-sig | rsa-encr | pre-share} Example: Router...standard (DES). The example specifies the Message Digest 5 (MD5) algorithm. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-4 OL-5332-01 Also enters the Internet Security Association Key and Management Protocol (ISAKMP) policy configuration mode. The example ...
Configuration Guide
Page 71
...IKE group policy configuration mode, and enters global configuration mode. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-5 Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Configure Group Policy Information Configure Group Policy Information Perform ... local pool dynpool 30.30.30.20 30.30.30.30 Router(config)# Specifies a local address pool for the group. domain name Specifies group domain membership. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) group policy configuration mode...
...IKE group policy configuration mode, and enters global configuration mode. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-5 Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Configure Group Policy Information Configure Group Policy Information Perform ... local pool dynpool 30.30.30.20 30.30.30.30 Router(config)# Specifies a local address pool for the group. domain name Specifies group domain membership. Also enters the Internet Security Association Key and Management Protocol (ISAKMP) group policy configuration mode...
Configuration Guide
Page 72
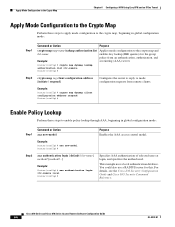
.... Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-6 OL-5332-01 For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. This example uses a local authentication database. Router(config...Router(config)# Enable Policy Lookup Perform these steps to apply mode configuration to the crypto map, beginning in global configuration mode: Step 1 Command or Action aaa new-model Purpose Enables the AAA access control model. Apply Mode Configuration to the Crypto Map Chapter 6 Configuring a VPN Using Easy VPN...
.... Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-6 OL-5332-01 For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. This example uses a local authentication database. Router(config...Router(config)# Enable Policy Lookup Perform these steps to apply mode configuration to the crypto map, beginning in global configuration mode: Step 1 Command or Action aaa new-model Purpose Enables the AAA access control model. Apply Mode Configuration to the Crypto Map Chapter 6 Configuring a VPN Using Easy VPN...
Configuration Guide
Page 73
... encryption-type encrypted-password} Example: Router(config)# username Cisco password 0 Cisco Router(config)# Establishes a username-based authentication system. When such a transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to the protected traffic as a part of both peers. Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Configure IPSec...
... encryption-type encrypted-password} Example: Router(config)# username Cisco password 0 Cisco Router(config)# Establishes a username-based authentication system. When such a transform set represents a certain combination of security protocols and algorithms. During IKE negotiation, the peers agree to the protected traffic as a part of both peers. Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel Configure IPSec...
Configuration Guide
Page 74
...)# crypto dynamic-map dynmap 1 Router(config-crypto-map)# See the Cisco IOS Security Command Reference for detail about this command. Example: Router(config)# crypto ipsec security-association lifetime seconds 86400 Router(config)# See the Cisco IOS Security Command Reference for example, IP address). Configure the IPSec Crypto Method and Parameters Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel...
...)# crypto dynamic-map dynmap 1 Router(config-crypto-map)# See the Cisco IOS Security Command Reference for detail about this command. Example: Router(config)# crypto ipsec security-association lifetime seconds 86400 Router(config)# See the Cisco IOS Security Command Reference for example, IP address). Configure the IPSec Crypto Method and Parameters Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel...
Configuration Guide
Page 75
...provides connectivity to evaluate all the traffic against the security associations database. See the Cisco IOS Security Command Reference for the crypto map entry. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-9 Applying the crypto map ...to the physical interface instructs the router to the Internet. Chapter 6 Configuring a VPN Using Easy VPN ...
...provides connectivity to evaluate all the traffic against the security associations database. See the Cisco IOS Security Command Reference for the crypto map entry. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-9 Applying the crypto map ...to the physical interface instructs the router to the Internet. Chapter 6 Configuring a VPN Using Easy VPN ...
Configuration Guide
Page 76
... mode. Note A hostname can be specified only when the router has a DNS server available for the VPN connection. Specifies the VPN mode of operation. 6-10 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01 See the Cisco IOS Security Command Reference for the VPN connection. Specifies the IPSec group and IPSec key value...
... mode. Note A hostname can be specified only when the router has a DNS server available for the VPN connection. Specifies the VPN mode of operation. 6-10 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01 See the Cisco IOS Security Command Reference for the VPN connection. Specifies the IPSec group and IPSec key value...
Configuration Guide
Page 77
... ezvpn name [outside | inside] Example: Router(config-if)# crypto ipsec client ezvpn ezvpnclient outside Router(config-if)# Assigns the Cisco Easy VPN remote configuration to the WAN interface, causing the router to which you want the Cisco Easy VPN remote configuration applied. Example: Router(config-crypto-ezvpn)# exit Router(config)# Verifying Your Easy VPN Configuration Router# show crypto ipsec client ezvpn...
... ezvpn name [outside | inside] Example: Router(config-if)# crypto ipsec client ezvpn ezvpnclient outside Router(config-if)# Assigns the Cisco Easy VPN remote configuration to the WAN interface, causing the router to which you want the Cisco Easy VPN remote configuration applied. Example: Router(config-crypto-ezvpn)# exit Router(config)# Verifying Your Easy VPN Configuration Router# show crypto ipsec client ezvpn...
Configuration Guide
Page 78
interface vlan 1 crypto ipsec client ezvpn ezvpnclient inside ! 6-12 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01 crypto ipsec transform-set vpn1 reverse-route ! crypto map static-map 1 ...1 set transform-set vpn1 esp-3des esp-sha-hmac ! crypto ipsec security-association lifetime seconds 86400 ! interface fastethernet 4 crypto ipsec client ezvpn ezvpnclient outside crypto map static-map ! Configuration Example Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel ! crypto isakmp policy 1 encryption 3des authentication pre...
interface vlan 1 crypto ipsec client ezvpn ezvpnclient inside ! 6-12 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01 crypto ipsec transform-set vpn1 reverse-route ! crypto map static-map 1 ...1 set transform-set vpn1 esp-3des esp-sha-hmac ! crypto ipsec security-association lifetime seconds 86400 ! interface fastethernet 4 crypto ipsec client ezvpn ezvpnclient outside crypto map static-map ! Configuration Example Chapter 6 Configuring a VPN Using Easy VPN and an IPSec Tunnel ! crypto isakmp policy 1 encryption 3des authentication pre...
Configuration Guide
Page 79
... for NAT) 5 LAN interface-Connects to the corporate network, with GRE Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 7-1 Cisco routers and other broadband devices provide high-performance connections to the Internet, but many applications also require the security of VPN connections which perform a high level of authentication and which controls access to...
... for NAT) 5 LAN interface-Connects to the corporate network, with GRE Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 7-1 Cisco routers and other broadband devices provide high-performance connections to the Internet, but many applications also require the security of VPN connections which perform a high level of authentication and which controls access to...